| At a glance | |
|---|---|
| Product | () |
| Summary | |
| Pros | |
| Cons | |
Typical Price: $
We’ve looked at a lot of VPN routers here at SmallNetBuilder, each with a different combination of features and with a downward trend for pricing. In this review, we’re looking at the TRENDnet TW100-BRV214, which, at around $70, establishes a new low in VPN router pricing.
TRENDnet advertises the TW100 as a “GREENnet” power-saving device. TRENDnet claims the TW100 can provide up to 40% power savings and rates the TW100’s power draw at 4 W. Other VPN routers we’ve reviewed don’t advertise maximum wattage, so it’s difficult to validate or compare TRENDnet’s claim of a 40% power savings. However, the concept of power saving is a good one, and I commend TRENDnet for moving in this direction.
The TW100 is a wired-only router with four 10/100 LAN ports and a single 10/100 WAN port. I prefer Gigabit LAN ports on my routers. But adding a basic 10/100/1000 switch is always a possibility. Figures 1 and 2 show the front and back of the unit, with features called out.
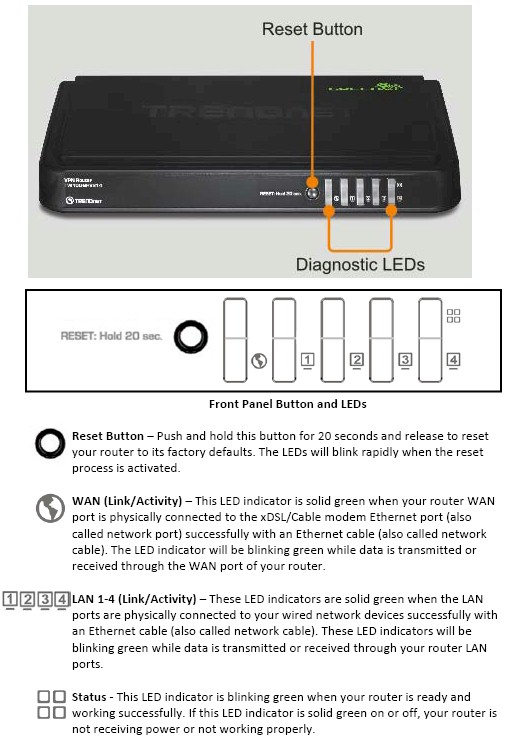
Figure 1: TRENDnet TW100-BRV214 front panel callouts
The TW100 measures 7.4” long by 4.6” deep by 1.3” in height. The case is black plastic, with indicator lights on the front, WAN and LAN ports on the back, as well as the power connector and an on/off button. It has an external power brick at the end of the power cable. The TW100 is passively cooled, thus silent in operation.
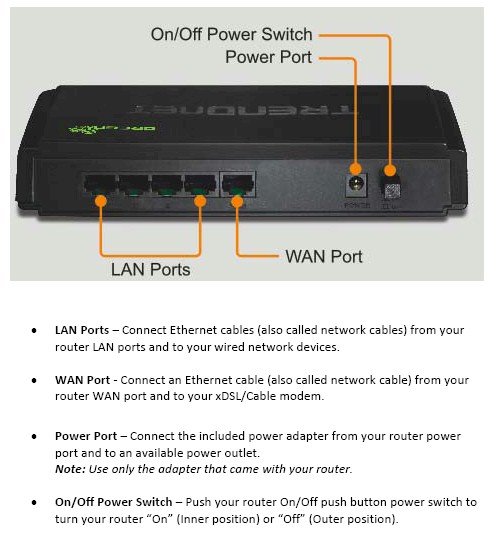
Figure 2: TRENDnet TW100-BRV214 rear panel callouts
Inside
The main board photo, shown in Figure 3, reveals a Realtek RTL8196 AP/router SoC along with 64 MB DRAM. The Realtek chip combines a 32 bit RISC processor and five port 10/100 switch.

Figure 3: TRENDnet TW100-BRV214 board
Features
This is my first TRENDnet product and it was easy to work with. Configuration is all done via web browser and the menus are relatively intuitive and well organized. The user manual is also useful, with decent explanations and examples. However, a glaring omission, particularly for a security router, is that administration via HTTPS is not supported.
There are three high-level options in the TW100 menu, including Status, Wizard, and Configuration. The Status and Wizard screens are basic, providing information about the router’s current status and easy config guidance for the WAN port and device password. Clicking the Configuration link takes you to the Basic Setting page shown in Figure 4.
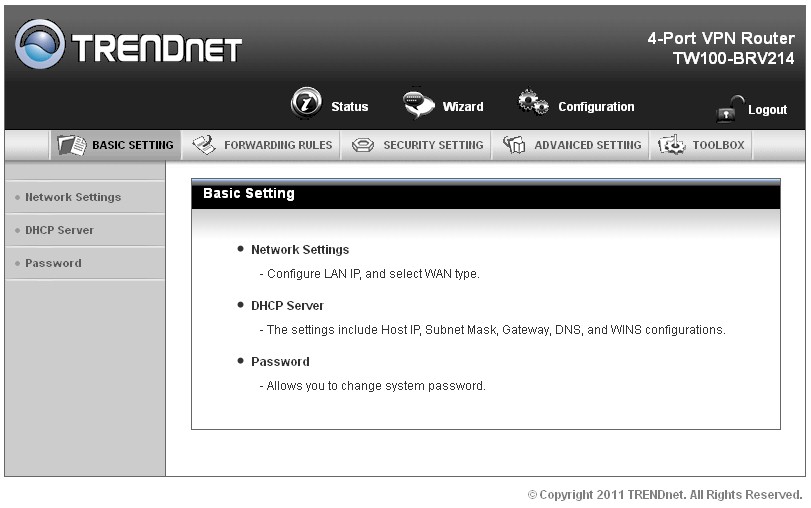
Figure 4: Configuration Basic Setting page
From here, the device is managed via five main menus with 3-10 submenus each. I’ve laid out the configuration options in the table below. There is also an online emulator, which you can use to test drive the interface before buying. (Ignore the Wireless Status portion of the online emulator’s Status page—the TW100 does not support wireless.)
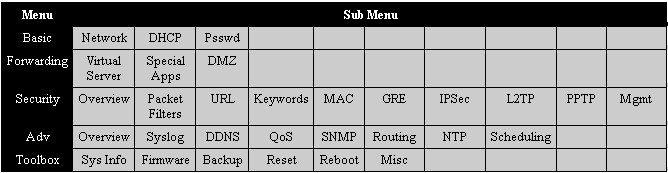
Figure 4: TRENDnet TW100-BRV214 menu summary
Before I dive into detailing some of the TW100’s features, there is a summary in Figure 5 to give you a general feel.
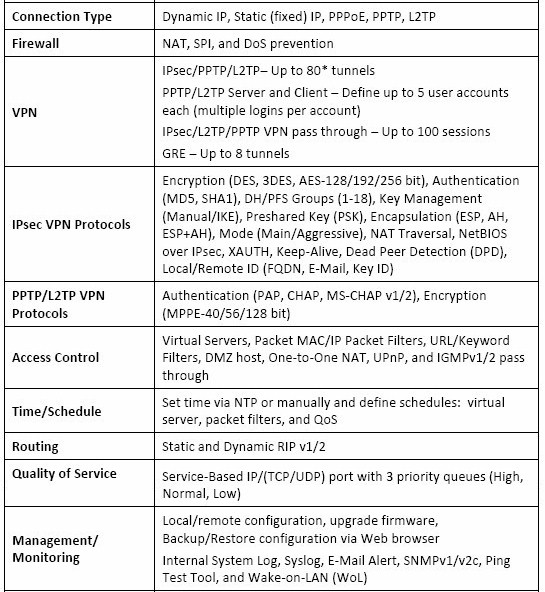
Figure 5: TRENDnet TW100-BRV214 feature summary
Network security on the TW100’s firewall is organized into four functions: Packet Filtering; Content Filtering; MAC Address Control; and Traffic Control.
Packet Filtering on the TW100 can be applied on both inbound and outbound traffic. Rules are constructed based on source IP, destination IP, layer 4 port, and protocol (TCP or UDP). Once constructed, rules can be saved and enabled or disabled with a single click. Up to 8 inbound and outbound rules can be created and schedules (100 user-programmable) can be applied.
I successfully created a basic rule to block outbound traffic to a specific device in my network. The rule worked, but there wasn’t an error message or indication to the user explaining why the website did not come up. Instead, you’ll get your browser’s "can’t reach the Internet" message, like the one in Figure 6 that IE threw to me.
Figure 6: Browser error due to outbound packet filter
Other routers I’ve tested have a simple web page that tells end users why they couldn’t get to a specific site, such as the NETGEAR FVS318G that displays a page “Website blocked by NETGEAR Firewall.” This lack of a message could lead to end users reporting problems.
Content Filtering on the TW100 can be applied to 10 URLs or to 10 keywords found in the URL or web page. Traffic to these URLs can be dropped, logged, or both.
I set up a simple URL blocking rule to block access to smallnetbuilder.com, shown in Figure 7. Setting up the rule was easy and it worked, but again there wasn’t any message displayed explaining the block.
Figure 7: URL filter example
Overall, content filtering on the TW100 works, but is quite basic. If you’re looking to ensure that end users aren’t surfing porn or other undesired websites, you’ll probably want a more robust solution, such as UTM device or a DNS-based service such as opendns.com.
Another security feature on the TW100 is up to 100 MAC addresses can be programmed to control which devices gain access to the TW100’s network. Adding MAC addresses into the MAC table is simplified by selecting devices from the TW100’s DHCP table for entry.
Features – more
Port forwarding on the TW100 has three options: Virtual Server; Special Application and DMZ. The Virtual Server menu is where Port Forwarding rules can be applied. There are nine predefined traffic types, including AUTH, DNS, FTP, ISAKMP, POP3, SMTP, TELNET, and HTTP. Up to 20 forwarding rules can be created to any of the predefined traffic types or a user-defined port and then enabled or disabled with a single click. Figure 8 shows a port forwarding rule to direct FTP traffic to a specific server. Note that separate public and private port numbers can be set and one of 100 schedules can be applied to each rule.
Figure 8: Port forwarding rule for FTP
Special Applications is where triggered port forwarding rules are created. Specify an outbound port and inbound port, and the TW100 firewall will permit inbound traffic triggered by the specified outbound flow. There are six predefined applications, including Battle.net, Dialpad, ICU II, MSN Gaming Zone, PC-to-Phone, and Quick Time 4. Up to eight rules can be created so that any of the predefined applications will “trigger” the opening of the firewall to permit return or incoming traffic. Custom triggering rules can also be created to any of the predefined application or a specified port and then enabled or disabled with a single click.
DMZ is also included in the TW100’s suite of network security options.
An noted earlier, rules for Packet Filtering and Traffic Control can be enabled/disabled based on 100 customizable time schedules, allowing you to automatically enable and disable network management. To facilitate time based schedules, the TW100 synchs with a network time server, ensuring it is running on accurate time, including adjusting for Daylight Savings Time.
Rounding out the TW100’s firewall controls are simple check boxes to allow UPnP and IGMP traffic on the LAN, as well as to permit passthru of PPTP, L2TP, and IPsec traffic. The TW100 can also detect and block DoS attacks including SYN Attacks, WinNuke, Port Scans, Ping of Death, and Land Attacks.
Overall, the TW100 firewall is simple to use, but relatively basic. There are more advanced firewall options out there, but as I’ll cover in the end of this review, not many VPN firewall routers are as cost effective.
In addition to Firewall and VPN capability, the TW100 offers a few other features. These options are configured in the Advanced Settings and Toolbox menus. Advanced Settings provides configuration options for syslog, dynamic DNS support, Quality of Service (QoS) configuration, SNMP capability and basic routing support for static and dynamic (RIP v1 and v2) routes. The Advanced Settings menu is also where schedules are created for use on firewall rules, discussed earlier.
I set up a simple syslog server using the free Kiwi syslog server and configured the TW100 to send its log messages to a PC. I had to open UDP port 514 on the Windows firewall to allow the traffic to hit the syslog server, but then immediately saw messages coming in from the TW100, as shown in Figure 9.
Figure 9: Kiwi syslog server
The TW100 provides priority-based Quality of Service (QoS) for controlling upstream traffic Configuration is done by entering an upstream bandwidth value, then specifying a traffic flow by local IP:port to remote IP:port and selecting priority High, Normal, or Low.
I did a simple functional QoS test using iperf. I set the TW100 upstream bandwidth to 10 Mbps, even though the WAN port was connected to a 100 Mbps port. (In practice, you would set this equal to the maximum upstream bandwidth provided by your ISP.) Without QoS enabled, my LAN-WAN throughput was about 90 Mbps. With QoS enabled and upstream bandwidth set to 10 Mbps, I saw LAN-WAN throughput at 9.65 Mbps, validating the 10 Mbps limit I set. The High, Normal and Low settings would then be used to raise or lower priority for specific traffic flows during periods of high network traffic.
Figure 10: Upstream QoS
The Toolbox menu provides functions for firmware management, configuration backups, resetting the device to default, rebooting the device and a few other miscellaneous functions. A nice feature in the miscellaneous menu is Wake-on-LAN functionality.
Wake-on-LAN with a VPN router is very handy and worked well for me on the TW100. If you have a PC that supports Wake-on-LAN and want to access it remotely, you can save electricity and leave it off except when needed. This is consistent with the "GREENnet" power saving feature mentioned earlier.
To use the Wake-on-LAN feature, save the MAC address of your local PC that you want to access remotely in the Wake-on-LAN menu of the TW100 (Figure 11). Then, VPN into your network, log in to the router, and click “Wake up” in the miscellaneous menu. Your PC will turn on and once it completes its boot cycle, you’ll be able to access it via Remote Desktop Connection or other remote protocols.
Figure 11: Wake On LAN configuration
Missing from the TW100, however, is support for IPv6. Although many of us may not need IPv6 in our small networks today, it’s already here for others and will keep those users from purchasing the product.
Routing Performance
Routing performance for the TW100 using our standard test method and 1.00.02 firmware is summarized in Table 1. The 90 Mbps range speeds are essentially 100 Mbps wire speed, with the 141 Mbps total simultaneous result indicating that the routing section is capable of higher speeds than the 100 Mbps ports will support. And, speaking of simultaneous, the TW100 maxed out our simultaneous connection test at 34,925 sessions.
| Test Description | TW100-BRV214 Throughput – (Mbps) |
|---|---|
| WAN – LAN | 93 |
| LAN – WAN | 92 |
| Total Simultaneous | 141 |
| Maximum Simultaneous Connections | 34,925 (test limit) |
| Firmware Version | 1.00.02 |
Table 1: Routing throughput
The composite IxChariot plot in Figure 12 of the three routing tests below shows upstream routing has a bit higher variation than downlink.
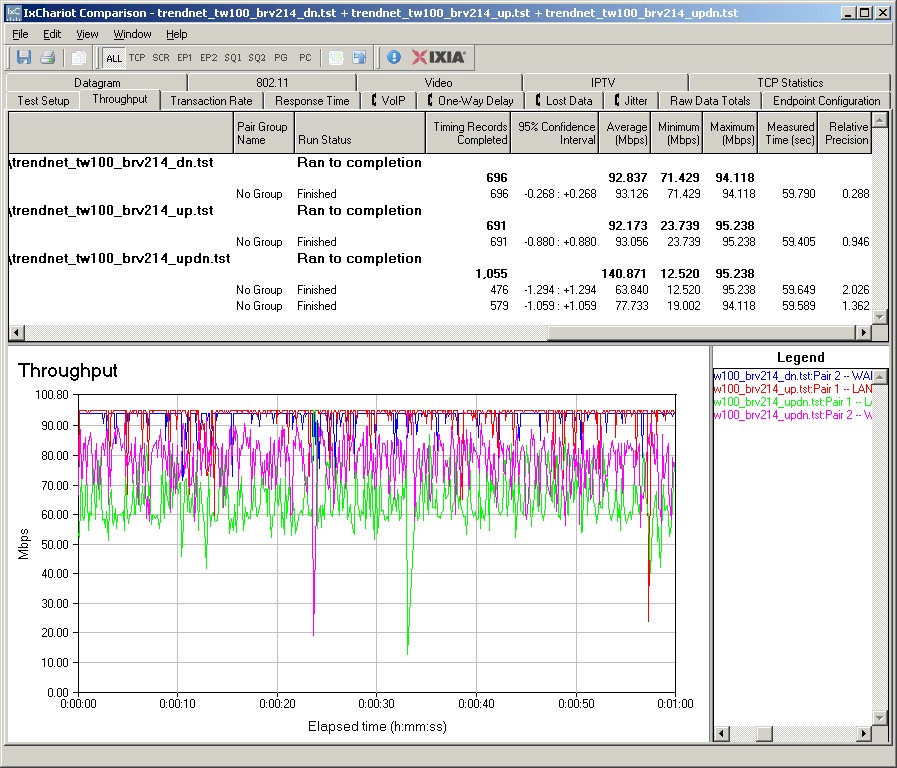
Figure 12: TW100-BRV214 routing throughput
Use the Router Charts for more comparisons.
VPN
TRENDnet lists the TW100 as capable of 8 GRE tunnels and 80 IPsec, L2TP and PPTP tunnels. Interestingly, the TW100 leaves out a popular VPN option, SSL.
GRE and IPsec are supported for site-to-site VPN tunnels on the TW100. It is interesting that TRENDnet chose to support GRE, or Generic Route Encapsulation. Cisco originally developed the GRE protocol, which has since been standardized in RFC 2784. We have reviewed the RV042 v3, RV120W and RV220W, all of which are VPN routers. But none of these Cisco devices support GRE tunnels.
Anyway, GRE is a low overhead tunneling protocol to connect two separate networks over a different network, such as connecting two LANs over the Internet. GRE tunnels by themselves don’t provide encryption or other forms of security, but can be used to encapsulate other connections. Lacking a second GRE capable device, I did not test this feature. However, there is a nicely documented example on how to set up a GRE tunnel between two TW100s in TRENDnet’s user manual.
IPsec is supported for Site-to-Site tunnels only, not remote client access. Typical of most IPsec devices, the TW100 supports 3DES and AES (128, 192, or 256 bit) encryption, with MD5 and SHA-1 authentication. I had no problem configuring an IPsec tunnel using 3DES and SHA-1 between the TW100 and a NETGEAR SRX5308 high performance VPN router. Figure 13 is a screen shot from the TW100, showing the established connection to the NETGEAR.
Figure 13: IPsec configuration
Remote client access to the TW100 LAN can be achieved through either an L2TP or PPTP tunnel. The TW100 can also function as a client to connect to another device using L2TP or PPTP.
For remote client access, a big plus for L2TP and PPTP is that the client software is included in Windows. Of the two protocols, L2TP is probably more secure, but neither is as secure as IPsec. Based on my throughput measurements, which I’ll cover shortly, I recommend using PPTP with the TW100.
I tested remote client access to the TW100 with L2TP and PPTP using a Windows 7 64 bit PC. Configuring the TW100 as a server for L2TP or PPTP involves clicking a few check boxes and entering a user name and password for the remote client. Figure 14 is a screenshot showing my L2TP server configuration on the TW100; notice the status display at the bottom showing the active connection.
Figure 14: L2TP configuration
Configuring the Windows L2TP or PPTP client is point and click. These steps will create the new VPN connection on your PC:
- From the Network and Sharing Center in the Control Panel, select Set up a new connection or network;
- Select Connect to a workplace.
- Select No, create a new connection
- Select Use my Internet connection
- Enter the WAN IP or dynamic DNS name you’ve assigned to the router,
- Select Don’t connect now, just set it up so I can connect later
- At the next screen, enter the user name and password you created on the TW100
Once created, right-click on that connection and select Properties. In the Security tab, select L2TP or PPTP depending on the tunnel type you created on the TW100. Save your changes, right-click the connection again and click Connect.
I successfully tested the TW100 with clients using L2TP and PPTP tunnels. Further, I was able to run L2TP, PPTP, and IPsec tunnels on the TW100 simultaneously. Figure 15 is a screen shot showing my active PPTP connection.
Figure 15: PPTP connection active
I had one problem where the TW100 DHCP server issued the L2TP and PPTP remote clients the same IP addresses. But I was able to resolve it by adjusting the range of IP addresses issued to clients on the PPTP tunnel.
VPN Performance
I tested the TW100’s VPN performance with iperf using default TCP settings, with a TCP window size of 8KB and no other options. I ran iperf on two PCs running 64-bit Windows 7 with their software firewall disabled. (Running a simple iperf throughput test between two PCs uses the command iperf -s on one PC and iperf -c (ip) on the other PC.)
Table 2 shows my VPN throughput measurements over the three tunnel types on the TW100. It also shows my VPN throughput measurements from three other wired VPN routers I’ve reviewed, the Draytek 2920, Netgear FVS318G and the Cisco RV042v3.
| Test Description | Throughput – (Mbps) | |||
|---|---|---|---|---|
| TW100-BRV214 | Draytek 2920 | NETGEAR FVS318G | Cisco RV042v3 | |
| IPsec (3DES) | 3.32 | 17.8 | 2.72 | 37.1 |
| PPTP | 8.95 | 19.9 | N/A | 10.8 |
| L2TP | 5.38 | 12.5 | N/A | N/A |
Table 2: VPN Performanc comparison -client to gateway
| Test Description | Throughput – (Mbps) | |||
|---|---|---|---|---|
| TW100-BRV214 | Draytek 2920 | NETGEAR FVS318G | Cisco RV042v3 | |
| IPsec | 2.85 | 17.8 | 2.72 | 47.5 |
| PPTP | 7.61 | 19.9 | N/A | 9.7 |
| L2TP | 1.1 | 12.5 | N/A | N/A |
Table 3: VPN Performanc comparison -gateway to client
TRENDnet says the TW100 supports up to 80 IPsec, PPTP, and/or L2TP tunnels. However, its VPN throughput numbers imply to me the TW100 would be challenged to support 80 simultaneous VPN tunnels. I think TRENDnet’s 80 tunnel rating may be referencing the fact that you can create 80 IPsec tunnel entries in the TW100 menu. I’d be surprised if the TW100 could support them all simultaneously, even if connected to a WAN circuit with enough bandwidth.
For VPN performance, let’s first discuss IPsec. As shown in Table 2, at about 3 Mbps, the TW100 has similar IPsec throughput to the FVS318G. But it is significantly slower than Draytek’s 17.8 Mbps and Cisco’s 37 Mbps.
Second, you can see PPTP throughput of 8.95 Mbps on the TW100 is lower than Draytek’s 19.9 Mbps and Cisco’s 10.8 Mbps. The FVS318G does not support PPTP, so there are no results posted
Finally, only the TW100 and the Draytek support L2TP. The TW100’s L2TP throughput is quite asymmetric at 5.38 Mbps from client-to-gateway and only 1.1 Mbps from gateway-to-client. Draytek’s 2920 produces higher L2TP throughput at 12.5 Mbps in both directions.
Summing up, the TW100 has quite a few VPN options including GRE, IPsec, L2TP and PPTP. All the ones I tested work and are relatively easy to set up, but throughput is low in comparison to the other devices. As previously stated, I’d use PPTP for remote client connections with the TW100, since you’ll get better performance than L2TP.
Closing Thoughts
In the tables below, I compared the TW100 to the three other routers from the VPN section of this review.
| Product | # IPsec tunnels | GRE | SSL | PPTP | L2TP |
|---|---|---|---|---|---|
| TW100-BRV214 | 80 | Y | N | Y | Y |
| NETGEAR FVS318G | 5 | N | N | N | N |
| Cisco RV042v3 | 50 | N | N | Y | Y |
| Draytek 2920 | 40 | N | N | Y | Y |
Table 4: VPN feature comparison
The key takeaways from Table 4 are the higher number of IPsec tunnels supported by the TW100, as well as the number of VPN options (although I’m skeptical the TW100 can really support 80 simultaneous VPN tunnels). On the other hand, with support for GRE, IPsec, PPTP, and L2TP, the TW100 has the most VPN options of the VPN routers I’ve reviewed.
| Product | WAN ports | LAN ports | Gigabit | WAN-LAN Throughput (Mbps) | LAN-WAN Throughput (Mbps) | Price |
|---|---|---|---|---|---|---|
| TW100-BRV214 | 1 | 4 | N | 94.2 | 92.2 | $67 |
| NETGEAR FVS318G | 1 | 8 | Y | 22.5 | 22.9 | $118 |
| Cisco RV042v3 | 2 | 4 | N | 91.1 | 89.9 | $146 |
| Draytek 2920 | 2 | 4 | Y | 147.5 | 136.5 | $245 |
Table 5: Router summary comparison
The key takeaways from Table 5 are the TW100’s throughput and price. Even though it does not support dual WAN or Gigabit ports, the TW100 has the second highest WAN-LAN and LAN-WAN throughput of these four routers and by far the lowest price.
However, the TW100’s IPsec VPN throughput is disappointing and there are clearly faster options available. And, perhaps more disappointing, you can’t connect a remote client via IPsec, only another router. PPTP throughput, although lower than the others, is reasonable, and probably more than you’ll need for remote access. If you’re looking for remote access to your network while traveling, it is likely you won’t have the bandwidth at a hotel or airport connection to exceed the TW100’s capability anyway. So the TW100’s PPTP throughput would be more than adequate.
You might also say the TW100’s lack of Gigabit ports or wireless support are weaknesses. But while I prefer Gigabit ports, I don’t actually often use that kind of throughput on my network. And adding an inexpensive Gigabit switch is always an option. Likewise, wireless support is solved by using the TW100 as your WAN router and connecting a converted wireless router or access point (here’s a step by step on how to convert a wireless router to an AP).
Bottom line, the TW100 is an inexpensive (and energy efficient) solution for providing secure remote access to your network and a pretty fast non-VPN router, too!
