Introduction
With Windows XP well into deployment and more manufacturers starting to beat the drum on how wonderful life is with a UPnP enabled router, I thought I’d see whether UPnP is something that you just won’t want to live without in your Internet sharing device. If you’re the impatient type and just want the bottom line on what I found, just skip to the last page.
![]() Notes, Caveats, Warnings!
Notes, Caveats, Warnings!![]()
- This is my first time doing any serious playing with both WinXP networking and UPnP. Therefore some of my observations may be old news to many readers. I apologize if I repeat what may be common knowledge, or if I’ve missed something or gotten it wrong. I’ll be happy, of course, to update this article with any corrections I receive.
- I checked with Microsoft, D-Link, and Linksys to see if there were any descriptions of what I should look for during my testing. I received responses from all, but the information was at a marketing “features” and “benefits” level and not at the detailed “User Manual” level that I was hoping for.
- I also searched through the Windows XP help (which turned out to be more helpful than I thought it would be… once I learned where to look), and hit Google in hopes of finding someone who had already been down this path and could give me some guidance. I didn’t have much luck with these sources either.
After checking with my vendor contacts, I found the only UPnP-enabled routers that I could get my hands on right now (“now” being April 2002) were the the Linksys BEFSR41 (with firmware 1.42.3 or higher) and the D-Link DI-804 (with firmware V4.67 or higher). So with routers in hand and Windows XP Home installed on one of my test machines, I set out to see what I could see.
Update 8/2/02 Additional routers that support UPnP are: MultiTech RF550VPN and D-Link’s DI-604 [reviewed here] (with 2.0f firmware update).
Grab your Partner!
Since I’d heard so much about how a WinXP computer and a UPnP enabled router were supposed to find each other no matter how the XP client was set up and without requiring any reboots, I thought I’d poke at that first.
I took my trusty, but aging, Compaq 1650 laptop, that I’d recently loaded with WinXP Home and that was happily connected to my SMC7008 main router (and the Internet) via a Linksys PCM100H1 HomeLink Phoneline + 10/100 Network PC card (yes, that’s a strange choice, but my trusty generic 10Mbps PC card Ethernet NIC died during my experiments). WinXP had installed the NIC, using the latest drivers downloaded from Linksys, and configured it with the default assortment of services as shown in Figure 1 below.

Figure 1
XP had set the NIC to “Obtain an IP address automatically”, and the adapter had successfully leased IP address information from the SMC router in the 192.168.3.XXX subnet and was added to the the Network Connections window as shown in Figure 2 below.
Figure 2
Tip: You must have the TCP/IP protocol installed, set to “Obtain an IP address automatically”, and no Gateway or DNS information entered in the TCP/IP properties. This is the default setting for WinXP, but not for earlier OSes.
If you manually set your IP address or other TCP/IP properties, UPnP will not override those settings and may not automatically connect to your UPnP-enabled router.
So far, though, no UPnP magic had been invoked because the SMC7008 is not UPnP enabled. So I left the Network Connections window open, unplugged the Compaq’s Ethernet cable from the SMC, plugged it into the D-Link DI-804, and waited to be amazed. After about 10 seconds or so, the Network Connections window began morphing and after about half a minute had changed to what you see in Figure 3.
The Linksys was slower to appear in the Network Connections window, taking about a minute to finish its configuration.
Figure 3
Hmmm… a new icon. Let’s go check it out!
The Internet Connection
This Internet Connection icon’s appearance in the Network Connections window is the first indication that you get of being connected to a UPnP enabled router or Internet Gateway Device (IGD). It’s also the way that you access some of the router information and properties that UPnP makes available to you.
Tip: If you’ve used XP’s Internet Connection Sharing feature, you’ve probably already seen this icon and are familiar with what is does. XP uses essentially the same interface elements for UPnP enabled routers.
Double clicking on the Internet Connection icon (or right-clicking and selecting Status) brings up its Status window, which is a little more interesting. Most of what you see in this window is described in the XP Help topic “Internet Connection Sharing Discovery and Control overview“, so I’ll just focus on my “discoveries”.
First, the Internet Connection speed reported by the Linksys router is incorrect (3.2Mbps when it should be 10Mbps). The D-Link correctly reports 10Mbps, which according to XP Home’s Help is “…the speed in megabits per second (Mbps) at which the adapter with Internet Connection Sharing enabled is capable of operating”, not the actual speed of data flowing to/from the Internet.
Moving on, clicking the Properties button on the Status screen brings up the Internet Connection Properties window shown in Figure 4. Not much here, except for the checkbox that allows you to have an icon appear in the system notification area (that’s the System Tray to Win98 folks…) when the connection is active, and the button that brings you to the more interesting Advanced Settings windows.
Figure 4: Internet Connection Properties
Tip: System notifications are off by default, so be sure to check the “Show icon in notification area when connected” box if you want to be alerted to changes in networking connections.
Before we move on to look at what’s behind the “Settings” button, though, let’s first spend a moment on UPnP’s NAT Traversal feature.
Come Transverse my NAT
When I first heard about the feature, it made me very nervous (and still does). Could I trust something that automatically opened holes in my router’s firewall? Would it work? How reliable would it be? Would it tell me what it was doing? Could I control it?
I found that I was pretty much on my own in answering these questions and had to rely on net searching with Google and poking around in the XP Help documentation to piece together a picture of what NAT Traversal is supposed to do. Let me summarize the key points of what you should know:
- The present Version 1 NAT Traversal API (Application Programming Interface) provides the following functions:
- Determine if a NAT is present
- Get the external IP address of the NAT, i.e. the router
- Get the static port mapping information for a specific external port, if it is mapped.
- Add a static port mapping, unless the external port is previously assigned.
- Enable or disable a specific port mapping without deleting it
- Edit the user-friendly description of a static port mapping
- Delete a static port mapping.
-
Obtain a list of static port mappings for the local network.
-
Applications do the “heavy lifting” in managing port mappings, using the API functions listed in Point 1. The router is more a “slave” than a “master”, so UPnP doesn’t add much value to a router without applications that know how to use UPnP features.
- UPnP enabled Internet Gateway Devices or IGD‘s (Microsoft’s UPnP term for routers and similar devices) currently support port mappings of infinite duration only. This means the mappings can’t be set with a router-controlled time-out. It also means that IGD’s are not smart enough to detect “zombie” mappings, i.e. ports left opened by abnormally terminated applications. If the application that used UPnP NAT Traversal to open ports in an IGD crashes, the ports will stay open until the next time that application is used.
It was pretty clear that I needed to find some NAT Traversal savvy applications to test with. But when I asked D-Link, Linksys, and Microsoft for a list of applications that supported NAT Traversal, I didn’t really get one and couldn’t find one anywhere on the web. I did learn that XP’s Windows Messenger, Remote Desktop Connection, and Remote Assistance features supported it, and that various Microsoft games were in the process of adding support for it, too. But I couldn’t get reliable information on UPnP support in applications from any vendor other than Microsoft. So since XP insists on launching Messenger every time it starts up, I used it to check out NAT Traversal. Let’s get to it!
This is “Advanced”?!
The Advanced Settings window is where you really get to see whether UPnP delivers the promised goods in making Internet sharing easy. From what I saw in these two products, UPnP has a long way to go to reach that goal. But let me save the editorial comments for later and focus on what I found.
The Linksys BEFSR41 was loaded with firmware 1.42.6 Mar 11, 2002 and the D-Link DI-804 with firmware V4.67(2001/12/20).
Figures 5 and 6 once again show the D-Link and Linksys “Advanced Settings” windows, and you can see that the two products are very different in what they provide.
Figure 5 – D-Link DI-804
Figure 6- Linksys BEFSR41
The DI-804’s screen (cryptically) shows that Windows Messenger had automatically opened two Services (Microsoft’s term for ports) and enabled them. I ran a port scan for the listed ports against the 804’s WAN port and found, indeed, that the ports were open. When I quit Messenger, the port mappings were not just disabled (which would have been indicated by removing the check marks in the boxes), but removed, i.e. no Services were listed in the Advances Settings window. So that’s what NAT Traversal looks like in action!
Figure 7: D-Link Service Setting info
Selecting the first service and clicking “Edit” brought up the window shown above in Figure 7. Note the use of different internal and external port numbers (common for some applications) and the use of the computer’s name instead of IP address.
The Linksys results, however, were disappointing. First, the router and Windows Messenger appeared to not pay any attention to each other, with no Messenger related Services appearing (refer to Figure 8 above). Under the same test conditions, the Linksys instead offered a menu of common Internet Services that could be enabled (note that all are disabled by default). But when I enabled the FTP (Port 21) service, then ran a port scan against it (with an FTP server running on the target machine), the port wasn’t found to be open! I also tried enabling the HTTP (Port 80) service (again, with a Webserver running on the target machine) with the same result.
Probing further, I edited the FTP service and found that the IP address wasn’t even set to the XP computer’s IP address! Instead, it was set to 192.168.5.0 (it should have been set to 192.168.5.100… at least they got the correct subnet). In all, a very disappointing result for the Linksys.
Updated 9/9/02 A few readers have commented on my criticism of the Linksys’ UPnP capabilities, and especially my criticism of its failure to enter a working IP address for the pre-configured Services in the Advanced Services window. Since the original paragraph was unclear on a few points, I hope this update (and the edits I’ve made to the few paragraphs above, clears things up.
First, the inability of UPnP routers to enter a working IP address for any pre-configured UPnP Services that they offer in the Advanced Settings screen is not unique to the LInksys, but seen on all UPnP routers to date. (The Linksys’ failure to produce a working Service (port mapping) via UPnP, is however, a Linksys problem.)
The reason for my criticism is that I think it’s reasonable (and logical) that UPnP would default to providing the IP address of the machine that the UPnP Advanced Settings window is opened on, for any of the services that is shows a checkbox for. Why? XP/UPnP goes to all the trouble of offering pre-configured services (ports), and one of UPnP’s primary goals is to make it easy for users to get applications working through “Internet Gateway Devices”, i.e. routers.
An inexperienced user would reasonably assume that they just need to check a Service box and have the service added for the computer that they have opened the UPnP interface on, since that’s the computer that they are probably trying to get to work through their router. Since XP knows the computer’s IP address, why require the user to edit the Service, just to get it running? At minimum, the Advanced Settings window should make it obvious that the user not only needs to check the desired service, but also enter the IP address via the Edit button in order to get a working service. Better yet, a Wizard should be invoked to guide the user through the process, or the network could be searched for the service that is being enabled, and the IP address of that computer automatically entered.
Right now, the user is left on their own to figure things out, and I don’t think that’s acceptable.
The Battle of the Services!
Updated 8/2/02 While gathering data for this article’s update, I decided to check out how well changes in Service settings (manual port mappings) were coodinated between UPnP and a router’s normal admin interface. Since I’d found the D-Link DI-804 to have the best UPnP implementation so far, I chose it as my guinea pig.
Tip: I first upgraded the 804 with 4.68 firmware, which turned it into the DI-804U, according to the new admin screen! I also found out that you’ll need to check that your version of Windows Messenger is 4.6.X. I found this out when my new Dell 4100 laptop didn’t appear to be activating NAT Traversal for Messenger. Turned out that the Dell had come with the older 4.0 version of Messenger, which apparently doesn’t have the NAT Traversal feature baked in.
I found that a service added via the DI-804’s UPnP interface did not show up on the 804’s internal browser-based admin interface Virtual Server Settings page. The 804 did, however, properly establish the requested service and open the required ports, which I confirmed by port scanning the router. It also properly closed the ports when I removed the service via the UPnP Services interface. Another pleasant surprise was that the 804 didn’t have to be rebooted to add or delete the service, as it does when you change a Virtual Server setting via its normal Admin interface.
Similarly, a virtual server programmed on the 804’s admin interface did not show up in the UPnP Advanced Settings > Services. The required ports were again properly opened, however.
I next tried to add the same service via both methods. I found that I was able to add the same exact port mapping on both interfaces (same ports, same LAN IP) and did not get any warnings or complaints from UPnP or the 804. I was also able to remove or disable the port mapping from each interface, but the ports were not closed on the router until the mapping (service) was removed via both interfaces.
The bottom line is that, at least for the DI-804, UPnP and the 804’s browser admin interface don’t communicate with each other about port forwarding (services).
Tip: My advice here is pick an interface, either the UPNP Advanced Settings > Services interface, or your router’s admin screens if you’re going to open ports in your router’s firewall. Although it’s nice that you can open ports using both methods, the ports won’t be closed until you close or delete the mapping from the interface you used to open them with! If you forget that you opened a port with one interface, and then open it with the other, you’ll need to remember to go back and remove the mappings with both interfaces to close the ports.
But wait…there’s more!
Updated 8/2/02
A helpful reader let me know that I missed a second UPnP-related feature because I hadn’t really enabled WinXP’s UPnP features. The next screen shots show how to turn on this very exciting feature.
1) Open the Network Connections screen, and select the Advanced > Optional Networking Components… menu item. The window shown in Figure 8 will open.

Figure 8: Optional Networking Components
2) Select Networking Services and click the Details button. The window shown in Figure 9 will open.
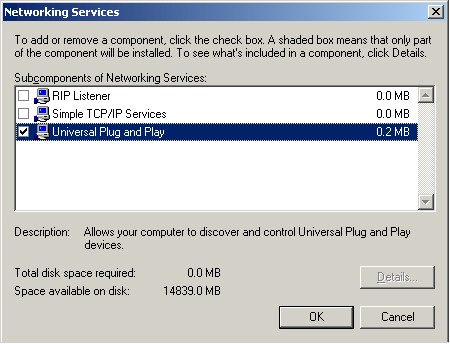
Figure 9: Networking Services
3) Check Universal Plug and Play, click OK to close this window, then Next in the Optional Networking Components Wizard. The files will then install and the Wizard will go away.
Shortly after the Wizard completes, you will see a new icon in the System Notification area (the right hand side of the Taskbar at the bottom of your screen). For some reason, this icon appears only the first time you connect to a particular UPnP-enabled IGD. Its properties doesn’t have a “Show icon in notification area when connected” checkbox, either. But if you open My Network Places, you’ll see a new icon, as shown in Figure 10.

Figure 10: My Network Places with UPnp IGD
Double-click on this icon (or right-click and select Invoke (?!)), and lo and behold, a browser window will open to the IGD’s main admin interface. Yes, it’s nice that the user won’t have to know the IP address of the admin interface to get to it, but why Microsoft, in its infinite wisdom, didn’t just put another button on the Internet Connection Properties window is a mystery to me. Right-clicking on the icon and selecting Properties will bring up a Window similar to that in Figure 11.

Figure 11: UPnP Router properties
So, contrary to my conclusion from the first version of this article, it looks like UPnP does give the user a simple way to access the IGD’s real admin features… if you know where to look, and if you figure out how to enable UPnP.
A peek at the D-Link DI-604
Updated 8/2/02
As I was updating this article, D-Link issued a firmware update for their new ultra-cheap DI-604. In addition to some needed bugfixes, version 2.0f firmware adds UPnP features, making the DI-604 the most inexpensive UPnP-enabled router available. But it looks like D-Link still has some work to do.
The My Network Places icon properties screen contains information about who really makes the DI-604, as shown in Figure 12.

Figure 12: UPnP Router properties – D-Link DI-604
Figure 13 shows that the DI-604 has added some pre-made services to its automatically generated NAT-Traversal selections.

Figure 13: UPnP services – D-Link DI-604
But when I tried to use the pre-made services, I kept getting a pop-up that said that the router wouldn’t accept the changes. You should also note that unlike the NAT-Traversal services, the pre-sets don’t have the IP address filled in. So if you just checked the box for the service you want (which you’d expect that you could do since this interface is supposed to be the port-opening-for-Dummies one), you probably wouldn’t get the service… if this feature worked.
Summary, Conclusions, Recommendations
Updated 8/2/02
Basically, I’m still not very impressed with UPnP’s tricks at this point in its development. Let me sum up what I’ve learned:
|
Summary of UPnP enabled Internet Gateway Device (IGD) capabilities
|
|
|
What it does
|
What it doesn’t do
|
|
1) Allows a UPnP enabled client to find and connect to an IGD if the client is set to “Obtain an IP address automatically”. 2) Automatically opens needed ports in the IGD firewall for applications that support UPnP NAT Traversal 3) Allows a user to define Services (open ports in the IGD firewall) without directly accessing an IGD’s admin interface. 4) Provides access to the IGD’s main admin interface via a My Network Places icon that has an obvious name. |
1) Let the user automatically know that ports have been opened in the IGD’s firewall and that security could be compromised. 2) Ask the user for permission before enabling NAT Traversal services. 3) Coordinate service addition, removal, and display between the UPnP and normal IGD admin interfaces 4) For non NAT-Traversal services, automatically determine the IP address for the service based on the computer that is establishing the service, or prompt the user to enter it. 5) Allow you to disable NAT Traversal separately from other UPnP services. 6) Automatically configure the IGD’s WAN connection properties, i.e. get connected to the Internet. 7) Guide the user in configuring the IGD’s WAN connection properties 8) Provide information about the IGD’s WAN IP information (IP address, DNS, Gateway) |
Since I didn’t check to see what happens when multiple UPnP enabled clients request the same Service (port mapping), I can’t offer any insight into what happens. But from reading Microsoft’s UPnP papers, I will say that it looks like its an issue that applications need to deal with, since Microsoft says that port conflict resolution isn’t the IGD’s problem.
Note that many of the items in the “doesn’t do” list above are not deficiencies in UPnP’s fundamental design, i.e. things it could never do, but are things that are caused by limitations in the present implementations of UPnP, UPnP-enabled IGDs, UPnP-enabled applications, or combinations of the three. But no matter what the reason, the [in my opinion] deficiencies are still there.
READ THIS! READ THIS! READ THIS! READ THIS! READ THIS! READ THIS!
I highlighted “Doesn’t do” Points 1, 2 and 3, because I think Microsoft has set a very bad precedent that I think they need to fix ASAP. I realize that Microsoft is trying to make things easier for the consumer and to help their customers get around some of the frustrations of dealing with the problems that NAT-based routers can cause with many applications (not to mention the time and $ spent in the Tech Support calls related to those problems). But even your common Web-browser warns you when you are changing from a secure to a non-secure web page and can be set to block (or at least warn about) cookies, Java applets and other things that can cause security problems. Shouldn’t a user be warned and allowed to confirm an event that could potentially be even more damaging than a cookie?! Especially when many users take the time to ensure that their routers are configured so that they are as invisible as possible to port scans?
It’s simply unacceptable (and especially in light of Microsoft’s alleged new company-wide focus on “trusted computing”) that NAT Traversal doesn’t provide warning and allow confirmation of opening holes in an IGD’s firewall or allow the user to disable that capability independent of disabling UPnP entirely. Given the capabilities of the UPnP API, Microsoft could even go further and have UPnP provide indications of opened ports whether or not they were set by NAT Traversal.
So c’mon Redmond, let’s get this fixed!
READ THIS! READ THIS! READ THIS! READ THIS! READ THIS! READ THIS!
Recommendations? I have two.
-
Don’t make a router or other networking equipment purchase decision based on whether or not UPnP is supported. The technology needs time to mature, doesn’t provide a lot of value added due to the relatively few applications that support NAT Traversal, doesn’t provide enough user feedback and control of holes it opens in a IGD’s firewall, and implementations are buggy. It also seems that manufacturers are not knocking each over in a race to make their routers UPnP-enabled, so it looks like UPnP feature improvements will be slow in coming.
-
If you must have a UPnP enabled router that properly handles NAT Traversal, your only choice is still the D-Link DI-804.
