Introduction

| SMC7004VBR Barricade Cable/DSL Broadband Router | |
|---|---|
| Summary | -New version of popular Barricade router with SPI based firewall, but no printserver or dial-up WAN support |
| Update | 7/31/2003 – Address mapping / Multi NAT feature removed. |
| Pros | • Schedulable firewall rules and URL keyword blocking, with different time periods per day |
| Cons | • No Web traffic logging • No static inbound port range mapping |
It sure has taken a long time, but SMC’s next-generation Barricade has finally hit the shelves. Although the little guy still won’t win any beauty contests, it might win a place in your SOHO network…
Basic Features
The VBR’s plastic package maintains SMC’s dark grey color scheme, and has about the same thickness, but slightly smaller footprint than your average Tom Clancy page-turner. All indicators are on the front panel and include Link/Activity, and Speed for each of the four LAN ports, Link/Activity for the WAN, and Power. All LED’s were bright and viewable from a wide angle. The four switched 10/100 LAN ports are on the rear panel, along with the 10/100 WAN port, power socket, Reset/Reset to Defaults button. Note there’s no support for uplink capability, so you’ll need to depend on whatever you use to expand the number of ports (if four aren’t enough), or use a crossover cable.
The 10/100 WAN port is a give-away that the VBR joins the ranks of D-Link’s DI-604 [reviewed here] and NETGEAR’s FR114P [reviewed here] as a next-generation router based on the ADMtek 5106 Home Gateway Controller. To answer the question that at least some of you are asking, no, it’s not a clone of either the D-Link or NETGEAR, although the designs are similar. So any experimentation involving flashing the router with something other than SMC’s firmware is at your own risk. One difference that I need to point out is that the VBR is the only one of the three to not have a heatsink on the ADMtek chip. All three routers run warm to the touch, so time will tell if SMC has made a wise choice here.
SMC includes a printed “EZ 3-Click Installation Guide”, Installation CD, and normal CAT5 patch cable. The CD contains:
- a PDF copy of the User Guide
- a copy of a Windows-executable for the 3-Click setup wizard
- a copy of the Adobe Acrobat Reader installer
SMC has changed the graphic design of their product packaging and Installation Guide, giving them an updated look. The User Guide design remains unchanged, and although there are plenty of screen shots in it, I would have liked more information on some of the VBR’s unique features such as the NAT Address Mapping and Firewall Intrusion Detection screens.
Setup
SMC has done a complete makeover of their browser-based admin interface for the VBR. It uses the blue-toned scheme that’s used on their 2755W 802.11a Access Point, and has its good and not-so-good points.
Pointing your browser to the default address of 192.168.2.1 brings up a login screen that you just need to click on the LOGIN button to get past, since the VBR ships without a password and doesn’t force you to set one.
Although having a well-known (and easy to guess) password, as many routers have, doesn’t provide the best security, I’m uncomfortable with SMC’s choice of shipping with no password at all. My objection is reinforced by the fact that the “EZ 3-Click” setup doesn’t include a step for setting a password. I suggest you go to the System > Password Settings page and set up a strong password ASAP.
The first screen lets you choose between the Setup Wizard and Advanced Setup methods. The Setup Wizard has three steps:
1) Set Timezone to adjust the time that’s automatically picked up from an NTP server
2) Select the Broadband Type (Cable, Fixed-IP xDSL, PPPoE xDSL)
3) Enter IP address info. The title really doesn’t properly describe the third step, which has you enter information that is specific to the type of connection you chose in Step 2. For Cable, you can enter Host Name and WAN Mac Address. Choosing “Fixed-IP xDSL” lets you enter IP address, Subnet mask, and Gateway and DNS server information. The final choice of “PPPoE xDSL” allows entry of Username, Password, and Service name. You can also set the MTU, Maximum Idle time, and whether you want to auto-reconnect.
Although this wizard appropriately narrows the configuration choices according to the user’s connection type, the user still has to correctly decide what kind of connection they have. I’d like to see SMC offer something more like NETGEAR’s Install Wizard that auto-detects the connection type, freeing the networking newbie from that often-confusing choice.
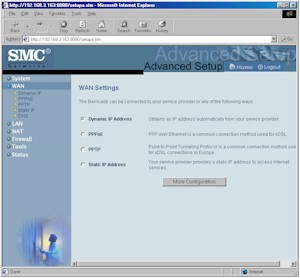
Selecting the Advanced Setup path gives you full access to all the VBR’s wonders, and shows a PPTP WAN setting option in addition to the previous three types. (PPTP is used by some US, and many European xDSL providers instead of PPPoE).
Figure 1: Advanced Setup
(click on the image for a full-sized view)
A quick review of each of the WAN connection type screens showed that everything that you’ll need to get properly authenticated is in place, and you shouldn’t have any problems connecting to your ISP.
LAN-side setup is straightforward, with the DHCP server enabled and ready to go. A nice touch is that you can set the DHCP Lease time in programmed increments from 30 minutes to 2 weeks, or have the lease never expire.
The overall responsiveness was pretty good with quick navigation from screen to screen. You’ll slow down a bit when saving settings though, with most changes taking a few seconds, but some requiring a 30 second -or-so reboot cycle. You get a “Your Data is being saved” screen for the longer saves, however, and the screen does auto-refresh when the save is done.
Remote administration can be enabled (it’s off by default), and you can restrict access to a single IP address if you like.
Tip: Remote admin is directed to Port 8080 (this is not documented). So if your WAN IP is 222.22.22.2, then you would enter http://222.22.22.2:8080 into your browser to connect from the WAN side of the router.
You can also reboot the router, or force it to reload factory defaults (although these functions are on two different screens) via the admin interface, and save and restore router configuration to / from a local file. The VBR does not allow multiple administrator logins at a time and tells you the IP address of the current administrator if there is one, when you try to log in. I didn’t find any holes in the login authentication, although the router does not automatically log you out when you quit your browser. You can also set the time for the idle admin auto-logout (Password Settings screen).
Firewall, Port Mapping, Filters
I first thought that the VBR’s firewall features were going to be pretty much the same old same-old, but it turned out that SMC had a few tricks up its sleeve to try to set the VBR apart from the pack.
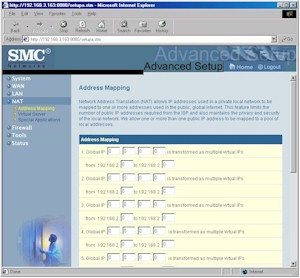
First in the “unique feature” department is the VBR’s Multi-NAT capability. SMC calls this “Address Mapping”, and as Figure 2 below shows, with it, you can take multiple WAN IP addresses and assign them to ranges of private LAN IP addresses. This lets you, for example, put more than one LAN client in DMZ (one for each WAN IP address you have), and also lets you have multiple virtual (mapped) servers of the same type (FTP servers for example) operating on the same port.
NOTE! This feature is useable only if you have multiple WAN IP addresses assigned from your ISP!
Figure 2: Address Mapping
(click on the image for a full-sized view)
SMC let you define up to 10 Address Mappings and 8 DMZ machines, but again, you need an ISP-assigned IP address for each Mapping or DMZ assignment.
The second unique feature is the control that you get over the Stateful Packet Inspection (SPI) features of the VBR’s firewall. Figures 3 and 4 show some of the “knobs” that you can tweak on the firewall.
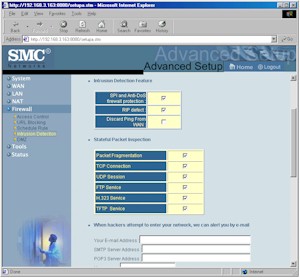
Figure 3: Intrusion Detection
(click on the image for a full-sized view)
The Intrusion Detection and Stateful Packet Inspection sections are fairly straightforward. The SPI and Anti-DoS firewall protection checkbox allows you to turn most of the SPI features on and off. If you leave SPI on, the checkboxes in the Stateful Packet Inspection section allow you to turn off SPI features for specific types of traffic.
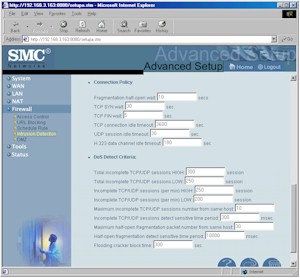
Figure 4: More Intrusion Detection
(click on the image for a full-sized view)
The settings in the Connection Policy and DoS Detect Criteria sections are harder to decipher. Unfortunately, you’ll need to go elsewhere to understand when and how to change most of the settings, since SMC’s User Guide offers no useful information. This page is also where you set up the Email hack alert feature, which is supposed to send an email when a hack attempt is detected. I say supposed, because although I port-scanned the crap out of the VBR, it never sent a single email alert. I asked SMC about this and will cover their response in the Logging section later on.
Moving on to the more typically found firewall features, you’ll find both static single port (Virtual Servers) and triggered port range (Special Applications) mapping capabilities, but you won’t find static port range mappings. SMC says, however, that this will be added in a future firmware update. Note that server “loopback” is not supported for Virtual servers, and the port mappings are not schedulable.
The VBR’s Access Controls (Port Filters), allow you to pick from a built-in list of common services, and add a custom rule (not shown on the screen shot) that can contain up to 5 single ports or port ranges, in either UDP or TCP protocols (but not both at once) to apply to a range of LAN IP addresses.
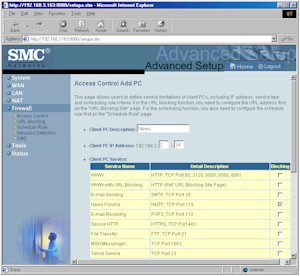
Figure 5: Access Controls
(click on the image for a full-sized view)
You can only create rules that block the specified ports… not the sometimes handier allow type rules. You can disable all rules and leave them programmed, but can’t disable rules on an individual basis.
The VBR’s Scheduling Features are the most flexible that I’ve found in recent routers. For each Access Control rule, you can apply one of 10 schedules that you set up, or have the rule always in force.
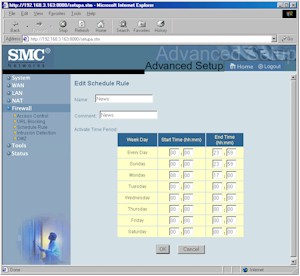
Figure 6: Rule Schedule
(click on the image for a full-sized view)
Figure 6 shows that each day has its own time period, a flexibility that you don’t often find among rule-schedulable routers. Schedules also can be applied to the URL Keyword blocking feature, which is treated just like an Access Control port filter rule for scheduling purposes. Note that although you can set different times for keyword blocking for different groups of LAN clients, you get only one set of URL keywords.
In all, I thought the VBR had a pretty good set of Firewall related features, except for the missing static port range mapping.
VPN
The VBR supports pass-through VPN connections, and can handle multiple sessions for PPTP, IPsec, and L2TP protocols. Mapping of LAN based VPN servers for all three VPN protocols is handled, too, as long as you establish the proper Inbound services and rules.
Logging
The VBR’s logging features are unfortunately, not among its better features.
Figure 7: Status
(click on the image for a full-sized view)
The cramped, unsizable Security Log window is your only view into what the VBR is logging. But as I reported in the Firewall section, my test port scans never registered in the log, nor did they cause email alerts to be sent. I asked SMC about this, thinking that maybe I missed an enable setting somewhere. SMC replied that what I was seeing was by design, i.e. the VBR does not log or email alerts when probed (port scanned), but only when “serious attacks” (snork, smurf, etc.) are attempted. Their reasoning is that port scans are so common that logging them or emailing an alert creates a “cry wolf” type of situation, masking the times when a “real” attack is detected. They also said they plan to add syslog capability in a future firmware update, and will enable port scan logging at that point.
This choice is certainly SMC’s to make, but I’d like to see this clarified in the User documentation. Right now the User Guide says that the Status screen shows “illegal attempts to access your network”, and the Admin interface title over the Security Log box says “View any attempts that have been made to gain access to your network”.
For the items that are logged (mostly router admin events) you can clear, refresh, and save the log to a local file. Although it might be obvious, I’ll point out that the VBR doesn’t log traffic (website visits) either.
Routing Performance
Testing Notes:
• WAN to LAN tests are all run with LAN endpoint in DMZ
• LAN to WAN tests are run with LAN endpoint not in DMZ, except UDP Stream
The truth be known, I’ve been having a hell of a time with my normal testing tool, Qcheck, since I’ve started testing these ADMtek-based routers. Although routers have claimed to be using SPI (Stateful Packet Inspection) before, it seems that the ADMtek-based boxes really are using SPI, or at least doing something different in their implementation.
At any rate, these routers sent me off on a few weeks of experimentation with Qcheck and Chariot, the two NetIQ testing tools that I rely on for my most of my testing. After a lot of back-and-forth with NetIQ Tech Support, experimentation with various Endpoint versions (an Endpoint is a little application that runs in the background of your machine, waiting for test instructions from the Qcheck or Chariot console), and a nice new flat spot on my forehead from banging it against the wall, I finally think I’ve come up with a new test method for SPI+NAT routers… and I have the VBR to thank.
Turns out that the VBR’s ability to fine-tune its NAT settings (Intrusion Detection section) allowed me to finally decide that the reduced throughput that I was seeing on LAN-WAN tests when I put the LAN machine in DMZ really could be attributed to the interaction between Qcheck / Chariot and the SPI in the router. The VBR allowed me to leave the LAN endpoint in DMZ, and disable SPI, therefore separating the DMZ and SPI effects. With other products all I could do was move the LAN endpoint in and out of DMZ.
So that my test results are as apples-to-apples as I can get them for SPI+NAT routers and given Chariot’s “can’t handle SPI+NAT” warning, I went back and retested the D-Link DI-604 [reviewed here] and NETGEAR FR114P [reviewed here] using the same settings. I strongly suggest you read the new test method info, so that you don’t misinterpret the results from my new test method.
As I said, the SPI-tuning features allowed me to explore the VBR a little more, so I’ll present my findings in another handy chart:
|
Case Number
|
Test Description |
Intrusion Detection Settings | DMZ |
Transfer Rate (Mbps) |
Response Time (msec) |
|
1
|
WAN-LAN |
SPI enabled (defaults) | on |
1.22 |
652 (avg) |
|
2
|
WAN-LAN |
SPI disabled | on |
6.75 |
118 (avg) |
|
3
|
LAN-WAN |
SPI enabled (defaults) | off |
10.7 |
74 (avg) |
|
4
|
LAN-WAN | SPI enabled (defaults) | on | 2.4 | 74 (avg) |
|
5
|
LAN-WAN |
SPI disabled | on |
9.0 |
88 (avg) |
|
6
|
LAN-WAN | SPI disabled | off | 13.6 | 58 (avg) |
Since WAN-LAN tests won’t work unless the LAN endpoint is in DMZ, I could only compare results with SPI enabled and disabled, but the results in Cases 1 and 2 show a 5X throughput improvement with SPI disabled. Comparing Cases 3 and 6 shows an almost 30% throughput improvement from disabling SPI with the LAN endpoint not in DMZ, and an almost 4X improvement with the endpoint in DMZ (Cases 4 and 5). The last point to note is that the UDP LAN-WAN test would run, but would not report back results.
What’s all this mean for real-world performance? I’d say that either putting a LAN client in DMZ (or forwarding specific ports to a LAN-side server) with SPI enabled will result in the lower throughput performance, although the actual numbers you get may vary from my Chariot-based measurements. But before you turn off SPI in search of higher throughput, consider the typical 1 to 1.5Mbps speed of most broadband connections, and that the “exposed” computer will be protected against nasty stuff like fragmented packet, syn flood, and DoS type attacks, which is protection well-worth the throughput hit.
Routing Performance Test Results
| Test Description | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
|---|---|---|---|---|
| Throughput (kbps) | Lost data (%) | |||
| WAN – LAN | 1.2 | 652 (avg) 675 (max) |
442 | 3 |
| LAN – WAN | 10.7 | 74 (avg) 79 (max) |
||
| Firmware Version | v1.03 Jun 12 2002 22:00: | |||
See details of how we test.
Wrap Up
As I said at the top of the review, the VBR isn’t anybody’s clone. It can handle sharing up to 10 WAN IP addresses, has the most flexible port and URL filter scheduling that I’ve seen, and SPI features that should make it especially attractive if you’re running servers and are looking for an extra edge in protection. And all for a street price under $50, too.
The main things that may hold it back is its limited logging and lack of static port range mapping. Let’s hope that SMC doesn’t take as long birthing those improvements as it took to (finally) get this baby to market!