
| At a glance | |
|---|---|
| Product | TP-LINK SafeStream Gigabit Dual-WAN VPN Router (TL-ER6020) [Website] |
| Summary | Dual-WAN Gigabit PPTP / L2TP / IPSec VPN router |
| Pros | • High routing throughput • High VPN throughput |
| Cons | • No IPv6 • VLANs don’t support 802.1q tags • No wizards to help with VPN configuration |
Typical Price: $0 Buy From Amazon
Introduction
I recently had the opportunity to look at the TP-LINK TL-SG2216 switch. As I mentioned in that review, TP-LINK is trying to grow its market share in the U.S. as a network device manufacturer. My experience with the TL-SG2216 left me interested to look at additional products from TP-LINK.
My wish was granted! In this review, I’m going to look at TP-LINK’s TL-ER6020, a dual WAN VPN Router with Gigabit ports. This router has two Gigabit Ethernet WAN ports and three Gigabit Ethernet LAN ports. The third LAN port can alternatively be configured as a dedicated DMZ port.
The TL-ER6020 is enclosed in a gray metal case measuring 11.6”W x 7.1”D x 1.7”H. Brackets and screws are included for mounting in a standard 19” rack. WAN and LAN Ethernet ports, a console port, indicator lights, and the reset button are located on the front of the device as shown below.
TP-LINK TL-ER6020 front
| Interface | Port | Description |
|---|---|---|
| WAN | 1-2 | The WAN port is for connecting the Router to a DSL/Cable modem or Ethernet by the RJ45 cable |
| LAN | 1-3 | The LAN port is for connecting the Router to the local PCs or switches by the RJ45 cable |
| DMZ | 3 | The DMZ port is for connecting the Router to the servers |
| Console | N/A | The Console port is for connecting with the serial port of a computer or terminal to monitor and configure the Router |
Table 1: Front panel port summary
The back of the TL-ER6020, shown below, has a Kensington security slot, grounding terminal and power socket. The grounding terminal can be used for an additional ground if needed. According to the TP-LINK data sheet, the TL-ER6020 is “designed to (withstand) lightning up to 4Kv in well-grounded connection conditions.”
TP-LINK TL-ER6020 rear
The power supply of the TL-ER6020 is internal. It comes with adhesive backed rubber feet for desktop use and has no internal cooling fan so it runs silently.
Inside
The TL-ER6020 runs on a Cavium CNS3411 600 MHz CPU, hidden under the heat sink in the shot of the main board below. Memory and storage are 128 MB of DDR2 RAM and 16 MB of flash. The Ethernet ports are managed by a Realtek RTL8367RB Ethernet Switch. The switch device spec says it supports up to 9216 Byte jumbo packets. But there is no mention of jumbo frame support in any of the TP-LINK documentation. I did not test for jumbo frame support.

TP-LINK TL-ER6020 board
Configuration
The TL-ER6020 can be configured via a browser, as well as via CLI with the included console cable or telnet (but not ssh). The user manual has a full chapter devoted to CLI configuration options.
I found the web configuration GUI logical and easy to use. Menus are responsive and quick to apply. I suspect the 600MHz CPU contributes to the fast configuration performance.
Menu options are listed along the left of the web page, with sub options available once expanded. Within each sub menu, multiple tabs provide access to additional configuration pages. The table below provides a summary of the TL-ER6020’s configuration options.
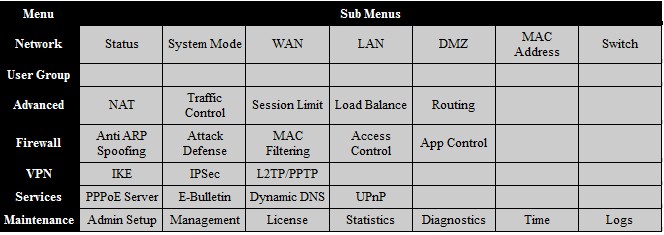
TP-LINK TL-ER6020 menu summary
The configuration pages in the web GUI have a help section that provides definitions for each of the fields. The 168 page user manual is also useful. Missing are configuration wizards in the web GUI, however. If you search through TP-LINK’s support site, there are some useful configuration examples, which I’ll mention shortly.
Feature Summary
The feature list below is based on the TP-LINK’s TL-ER6020 specification listing.
- Up to 50 IPsec VPN Tunnels, 50Mbps IPsec VPN Throughput
- IPsec, PPTP, L2TP, L2TP over IPsec
- IPsec NAT Traversal (NAT-T)
- DES, 3DES, AES128, AES192, AES256 Encryption
- MD5, SHA1 Authentication
- Manual, IKE Key Management Mode
- LAN-to-LAN, Client-to-LAN IPsec VPN
- PPTP/L2TP VPN Server/Client
- Hardware DMZ port
- One-to-One NAT
- FTP/H.323/SIP/IPsec/PPTP ALG
- IM/P2P Application Blocking
- URL/Keywords Filtering
- Web Content Filtering (Java, ActiveX, Cookies)
- ARP Inspection
- DoS/DDoS Defense
- Intelligent Load Balance
- Policy Routing
- Link Backup (Timing, Failover)
- IP-based Bandwidth Control
- Guarantee & Limited Bandwidth
- IP-based Session Limit
- Port VLAN, Port Mirror
- Static Routing, RIP v1/v2
- PPPoE Server
- E-Bulletin
VPN Configuration
The TL-ER6020 supports up to 16 L2TP tunnels, 16 PPTP tunnels and 50 IPsec tunnels. It can function as a server or client for L2TP and PPTP. As a server, remote clients can connect via L2TP and PPTP tunnels. As a client, the TL-ER6020 can connect to other L2TP or PPTP servers.
IPsec functionality includes support for remote access and site to site tunnels. TP-LINK doesn’t provide IPsec client software, but recommends Shrew Soft‘s free VPN client or GreenBow‘s VPN client.
I successfully set up L2TP, PPTP, and IPsec tunnels to the TL-ER6020. VPN tunnel configuration on the TL-ER6020 is relatively straightforward, although you won’t find configuration wizards to help.
For L2TP and PPTP tunnels, you enable the L2TP or PPTP server, create a user name and password, select whether encryption is enabled and create an IP address pool for the remote clients.
Using a Windows 7 PC and the native VPN “connect to a work network” utility, I was able to remotely connect to the TL-ER6020 via L2TP and PPTP. I was also able to remotely connect to the TL-ER6020 via a PPTP tunnel from an iPhone. In the screenshot from the TL-ER6020 below, my iPhone is connected via PPTP and my laptop via L2TP.
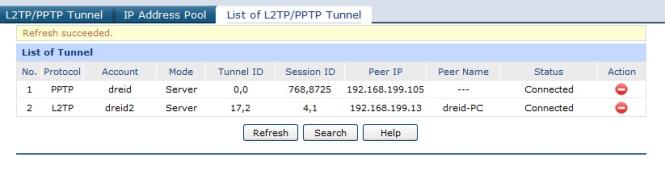
PPTP / L2TP tunnel status
I set up IPsec tunnels with a remote Windows 7 PC running Shrew Soft’s IPsec VPN client software as well as a site-to-site tunnel to a NETGEAR SRX5308 VPN router. In the screenshot from the TL-ER6020 below, you can see I have a remote and site-to-site IPsec tunnel connected.
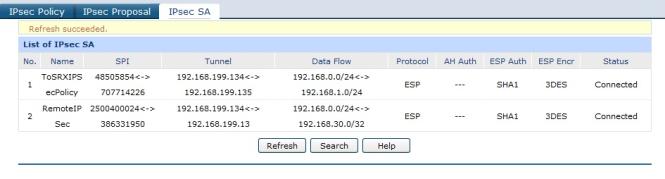
IPsec tunnel status
IPsec configuration on the TL-ER6020 requires creating an IKE profile and policy as well as an IPsec profile and policy. All typical IPsec options are available, including MD5 and SHA-1 authentication and 3DES and AES encryption.
To set up a site-to-site tunnel, the NETGEAR SRX5308 VPN configuration wizard selects SHA1, 3DES, and DH2 for IKE/Phase 1, and ESP, SHA1, 3DES and PFS = DH2 for IPsec/Phase 2. Once I manually applied the same options on the TL-ER6020, the tunnel between the two routers came right up.
To set up remote IPsec tunnel support, I had to configure the options on both the TP-LINK and Shrew Soft client software, which took a bit of trial and error. After I got a remote IPsec tunnel working as shown in the screenshots below, I stumbled across a nice step by step on how to configure a TP-LINK VPN router with the Shrew Soft VPN Client on TP-LINK’s website. You’ll find other configuration examples located in TP-LINK’s FAQ section.
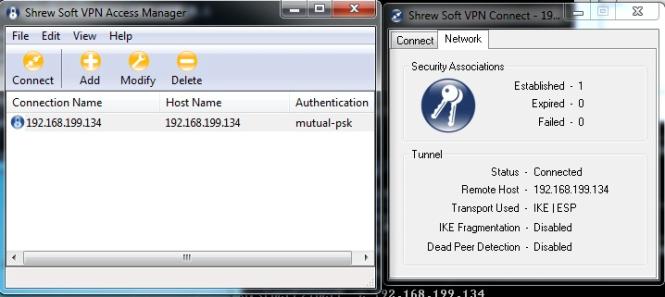
Working IPsec tunnel using Shrew Soft client
VPN Performance
I tested the TL-ER6020’s VPN performance with iperf using default TCP settings, with a TCP window size of 8KB and no other options. I used iperf on two PCs running 64-bit Windows 7 with their software firewall disabled. (Running a simple iperf throughput test between two PCs uses the command iperf -s on one PC and iperf -c (ip) on the other PC.)
Table 1 shows my VPN throughput measurements over the four tunnel types on the TL-ER6020.
| Tunnel Type | Client – Gateway (Mbps) | Gateway – Client (Mbps) |
|---|---|---|
| PPTP | 30.0 | 34.6 |
| L2TP | 26.0 | 20.0 |
| Client IPsec | 41.9 | 40.0 |
| Site-to-site IPsec | 45.9 | 37.9 |
Table 1: VPN throughput summary
For the site to site test, I used my standard NETGEAR SRX5308 to terminate the other end of the tunnel. NETGEAR specs the SRX5308 site-to-site tunnel throughput at 180 Mbps. But the best I was able to do testing with a 64 bit Win 7 client running TheGreenBox IPsec client was 43 Mbps with traffic flowing from Gateway to client. So the site-to-site test results above might be slightly limited by the SRX5308.
Table 2 shows a VPN throughput table comparing the TL-ER6020 to several VPN routers I’ve reviewed in recent years. Note, you can click on the model listed in the table to go to the review for each device.
| IPsec Throughput (Mbps) | PPTP Throughput (Mbps) | |||
|---|---|---|---|---|
| Product | Client-Gateway | Gateway-Client | Client-Gateway | Gateway-Client |
| TL-ER6020 | 41.9 | 40.0 | 30.0 | 34.6 |
| Cisco RV180 | 39.7 | 50.9 | 5.98 | 6.49 |
| Cisco RV120W | 23.1 | 21.2 | N.A. | N.A. |
| Cisco RV220W | 38.3 | 49.3 | 16.3 | 14.1 |
| Cisco RV042 | 37.1 | 47.5 | 10.8 | 9.7 |
| Draytek 2920 | 17.8 | 17.8 | 19.9 | 19.9 |
| Netgear SRX5308 | 31.8 | 42.6 | N.A. | N.A. |
| Netgear FVS318N | 33.1 | 45.8 | N.A. | N.A. |
| Zyxel VFG6005 | 5.9 | 5.6 | 10.8 | 6.54 |
| TrendNET TW100-BRV214 | 3.32 | 2.85 | 8.95 | 7.61 |
Table 2: VPN throughput competitive comparison
TP-LINK rates the TL-ER6020 capable of 80 Mbps for IPsec VPN throughput with 3DES encryption. As you can see, I measured IPsec 3DES throughput on the TL-ER6020 at ~40 Mbps in both directions. TP-LINK addresses throughput testing in their FAQ section, stating varying results are based on test tool and protocol (TCP vs. UDP) differences. Nevertheless, iperf based TCP testing for IPsec throughput is a pretty good indicator of real world performance.
The TL-ER6020 stacks up well against the other devices in the chart. More specifically, the TL-ER6020’s IPsec throughput is more symmetrical than most of the other devices.
PPTP throughput on the TL-ER6020 is head and shoulders above the other routers in the chart at 30 Mbps+. PPTP tunnels have a lot of utility since the client software is easy to set up and is included with all Windows versions as well as most smart phones including the iPhone and Android devices.
Dual WAN
The TL-ER6020 has three router modes, NAT, Non-NAT and Classic. NAT, or network address translation mode, is the default and is used to translate public to private IP addresses between the WAN and LAN interfaces. Non-NAT mode disables NAT functionality and requires the configuration of static routes and/or utilization of the RIP routing protocol to establish routing rules. Classic mode is “a combined mode of NAT and Non-NAT”.
I could see classic mode as useful if it allowed configuration of NAT on one WAN interface and Non-NAT on the other WAN interface, but it didn’t seem to work that way for me. Documentation of this mode is vague, so I’ve reached out to TP-LINK for clarity and will post an update when I hear back.
The TL-ER6020 automatically performs load balancing between active WAN ports using TP-LINK’s “Intelligent Load Balancing”. Using the default configuration for load balancing, it looks to me like the TL-ER6020 distributes traffic equally between WAN interfaces based on sessions.
To test default load balancing on the TL-ER6020, I set up two continuous pings to two different websites, with each ping representing a different session. I then disconnected the WAN1 interface. As you can see in the screenshot below on the left, only one of the ping sessions was interrupted, the other ping session continued without interruption. Moreover, the ping session that was interrupted only lost one packet. I repeated the test multiple times with similar results.
Load balance ping test
Based on my simple tests, the TL-ER6020 can fail over to the other WAN connection quite quickly. I like the fact that it automatically uses both connections by default, instead of leaving one connection as an idle backup.
The TL-ER6020 dual-WAN default mode assumes equal ISP connection bandwidth. If your ISP connections have different bandwidth capabilities or if one is usage sensitive or if one is more reliable than the other or if you have a requirement to send specific traffic out a specific connection, you may want to adjust the load balancing scheme. Load balancing on the TL-ER6020 can be customized based on bandwidth, source or destination IP address, TCP or UDP, tine of day/week schedule and primary/backup designation.
Firewall and Security
There are five main options on the TL-ER6020 firewall: Anti ARP Spoofing, Attack Defense, MAC Filtering, Access Control, and App Control.
Anti ARP Spoofing is a feature more commonly found on switches, but is useful on a router, too. With this feature, you can bind IP addresses to specific MAC addresses and permit only traffic that matches those bindings.
The Attack Defense feature allows for blocking excessive or potentially fraudulent traffic flows. Traffic floods can be blocked based on six types of traffic flows and configurable packet per second thresholds. Anomalous packets can also be blocked. Below is a screenshot of the Attack Defense options.
Firewall attack defense options
MAC filtering provides both allow / deny options for listed MAC addresses. For a small network (less than 10 users), MAC filtering based on a list of permitted devices can be an effective way to control access to the network, although somewhat resource intensive.
Access Control options on the TL-ER6020 are basic. The URL filtering option filters Internet traffic based on keywords or URLs, while the Web filtering option filters Internet traffic based on the presence of Java, ActiveX, or Cookies. The Access Rules option allows for creating rules to block or allow traffic based on ten predefined services (ICMP, FTP, SSH, TELNET, SMTP, DNS, HTTP, POP3, SNTP, H.323), source and destination IP address, and schedule. Additional services can be defined by protocol and port.
App Control allows for blocking various well-known Internet traffic types including Instant Messaging, Social Networking, Peer to Peer, Media, and other Internet sites. The list of applications are defined by a database file provided by TP-LINK. I tested this feature with a basic rule to block all traffic to all of the apps shown below and could no longer access YouTube once my basic rule was applied.
App control traffic types
Other Features
The TL-ER6020 has numerous options for managing traffic on a network. In addition to dual WAN options and a configurable dedicated DMZ interface, the TL-ER6020 supports VLANs, bandwidth controls, port mirroring, functions as an Application Layer Gateway (ALG), as well as several other networking features. Lacking, however, is support for IPv6.
The TL-ER6020 supports port-based VLANs, but not 802.1q based VLANs. With port-based VLANs, each physical LAN port can be assigned to one of three VLANs. Devices connected to LAN ports assigned to different VLANs are not able to pass traffic to/from each other. This provides a simple way to segregate traffic.
Bandwidth utilization by device can be controlled with port-based rate controls or by IP address. I found the port-based rate controls effective and easy to set up.
In the screenshot below, I set up a 1 Mbps ingress and egress rate limit on port 3, which is LAN port 1. As you can see in the screenshot, before I set up the rate limit, my bandwidth was 129 and 117 Mbps. After I set up the rate limit, my bandwidth was 989 and 977 kbps.
Bandwidth limit test
Another feature of note on the TL-ER6020 is the ability to perform ingress and egress port mirroring between all the ports on the router. For troubleshooting purposes, I find the ability to run a packet capture on all interfaces useful.
The TL-ER6020 enables ALG functionality by default for FTP, H.323, SIP, IPsec, but each can be easily disabled. ALGs typically modify Layer 5 headers to match Layer 3 headers as packets are translated from private to public IP addresses. In some circumstances, ALGs can improve functionality for these applications.
An interesting feature for a network administrator is the E-Bulletin feature. This allows posting a message to internal users on an ad hoc basis, continuous interval or during a specific time frame. I created the sample message shown below to test this feature. The message is presented when users try to surf or access the Internet. Users simple click “Continue” once they’ve read the message and they then go to their desired website.
E-Bulletin example message
Routing Performance
Routing throughput was measured running 1.0.0 Build 20120807 Rel.34348 firmware, using our router test process. The TL-ER6020’s throughput numbers come pretty close to TP-LINK’s product ratings of 180 Mbps NAT throughput and 30,000 concurrent sessions.
We measured WAN-LAN throughput at 162 Mbps, LAN-WAN throughput at 157 Mbps, total throughput at 162 Mbps and maximum connections at 29,990. These numbers put the TL-ER6020 above most of the other VPN routers I’ve tested, shown in Table 3 below, but behind the Cisco RV180 and RV220W, which both produce throughput numbers north of 700 Mbps.
| Product | WAN – LAN Throughput (Mbps) | LAN – WAN Throughput (Mbps) | Total Simultaneous Throughput (Mbps) | Maximum Simultaneous Connections |
|---|---|---|---|---|
| TL-ER6020 | 162 | 157 | 163 | 29,990 |
| Cisco RV180 | 798 | 811 | 1,192 | 10,000 |
| Cisco RV120W | 87 | 87 | 136 | 12,086 |
| Cisco RV220W | 720 | 728 | 1,113 | 34,925 |
| Cisco RV042 | 91 | 90 | 91 | 34,925 |
| Draytek 2920 | 146 | 137 | 147 | 34,925 |
| NETGEAR FVS318N | 62 | 60 | 61 | 5,004 |
| Zyxel VFG6005 | 636 | 150 | 304 | 34,925 |
| TrendNET TW100-BRV214 | 93 | 92 | 140 | 34,925 |
Table 3: Routing throughput summary and comparison
The composite IxChariot plot of our three routing tests below (WAN-LAN, LAN-WAN, Total) shows very low throughput variation.
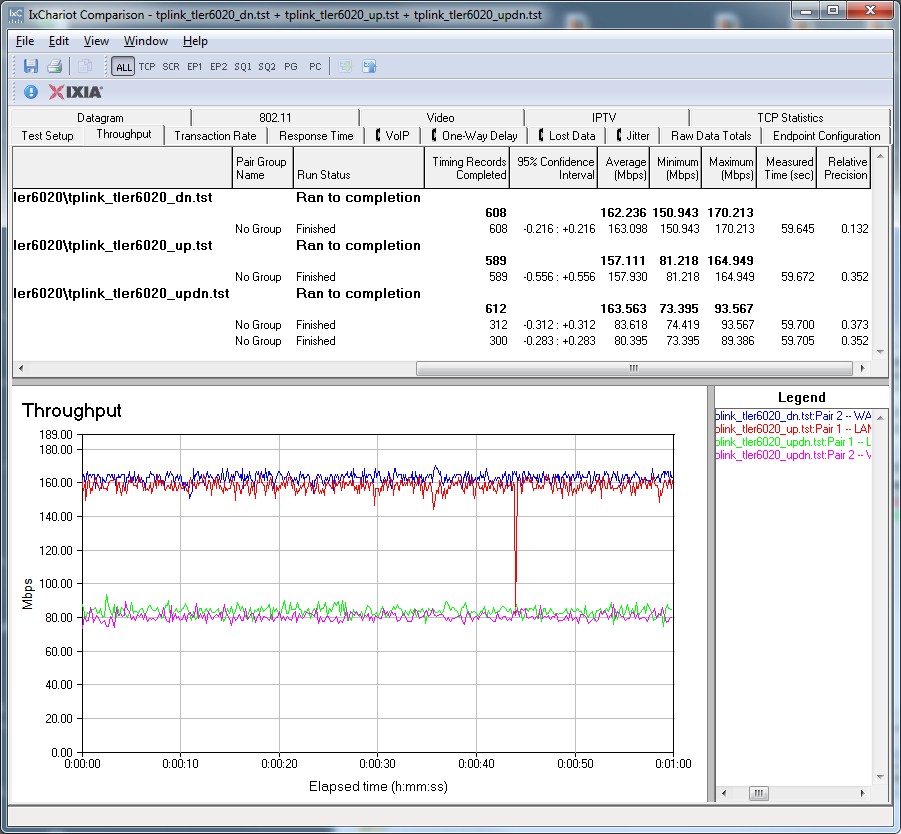
IxChariot routing throughput summary
I also used iperf to get another measure of TCP router throughput and got WAN-LAN throughput at 127 Mbps and LAN-WAN throughput at 110 Mbps.
If you’re connecting the WAN port(s) on the TL-ER6020 to an ISP connection of 100 Mbps or less, your Internet throughput will be limited by your ISP, not the router. So, for a gateway router, the TL-ER6020’s throughput capability should be more than sufficient.
Closing Thoughts
I was intrigued to discover the TL-ER6020 has a 600 MHz CPU. As mentioned previously, I observed the menus and application of configurations on the devices to be quite fast. I went back and looked at the CPU speeds, as well as a few key details on previously tested VPN routers and included that data in the Table 4 below.
| Product | CPU | IPsec tunnels | WAN ports | VLANS | WLAN | Price* |
|---|---|---|---|---|---|---|
| TL-ER6020 | Cavium 600 MHz | 50 | 2 | 3 (port based) | N | $127 |
| Cisco RV180 | Cavium 300 MHz | 10 | 1 | 4 | N | $114 |
| Cisco RV120W | Cavium 300 MHz | 10 | 1 | 4 | Y | $122 |
| Cisco RV220W | Cavium 400 MHz | 25 | 1 | 16 | Y | $227 |
| Cisco RV042 | Cavium 300 MHz | 50 | 2 | 0 | N | $116 |
| Draytek 2920 | Infineon 266 MHz | 32 | 2 | 0 | N | $207 |
| NETGEAR SRX5308 | Cavium 700 MHz | 125 | 4 | 254 | N | $358 |
| NETGEAR FVS318N | Cavium 300 MHz | 12 | 1 | 64 | Y | $140 |
| Zyxel VFG6005 | MIPS 348 MHz | 32 | 1 | 0 | N | $98 |
| TrendNET TW100-BRV214 | Realtek RTL8196 (? MHz) | 80 | 1 | 0 | N | $69 |
Table 4: VPN router comparison
*Prices from PriceGrabber as of 1/2/13.
As you can see in Table 4, only the much more expensive NETGEAR SRX5308 has a more powerful CPU. Now, the CPU is only one element in a router and other components can also contribute to performance. Still, it’s nice the TL-ER6020 has the horsepower under the hood.
The first of the two beefs I have with the TL-ER6020 is its lack of IPv6 support. IPv6 isn’t an issue for me now and more of a future-proofing concern. But with wider deployment of IPv6 finally happening in the U.S. and already common elsewhere, it’s a surprising omission for an otherwise very capable small business router.
My second concern is the lack of 802.1q VLAN tag support. I prefer 802.1q VLANs over port-based VLANs because VLAN tagging allows greater flexibility to extend VLANs to other switches as a network grows.
Even with these two issues, I came away impressed with the TP-LINK TL-ER6020. The Cisco RV042 is the closest dual WAN VPN router in price, coming in a little lower at $116 compared to $127 for the TL-ER6020. Yet the RV042 has only 10/100 ports compared the TL-ER6020’s 10/100/1000 ports. (For more money, you can opt for the RV042G with Gigabit ports for $182.)
I’ve tested TP-LINK’s TL-SG2216 switch and now its TL-ER6020 Dual WAN VPN router. I found both devices performed well and are reasonably priced. Watch your back, Cisco and NETGEAR! TP-LINK looks like it’s coming for you in the small business networking market.
