
| At a glance | |
|---|---|
| Product | Ubiquiti EdgeMAX EdgeRouter Pro (ERPro-8) [Website] |
| Summary | Very fast Gigabit Ethernet router based on Vyatta code running on dual-core Cavium CPU |
| Pros | • Wire-speed Gigabit routing • Highly configurable • Advanced routing features |
| Cons | • Limited GUI configuration. Mostly CLI • Does not come plug-and-play out of box • Documentation requires lots of reading between lines and Forum consultation |
Typical Price: $330 Buy From Amazon
Introduction
Our review of Ubiquiti’s $99 EdgeRouter Lite over a year ago has left fans of the company’s high-performance, but reasonably priced routers hungering for more. So when someone from the Ubiquiti engineering team answering questions about the Lite in the Forums offered to line up an EdgeRouter Pro for review, we said sure.
There are currently four routers in the EdgeMAX lineup: the EdgeRouter Pro; 8-Port EdgeRouter; EdgeRouter PoE; and EdgeRouter Lite.
The Pro and 8-Port routers are high speed routers capable of up to 8 Gbps of throughput. The EdgeRouter Pro and 8-Port EdgeRouter are both rack mountable routers with eight 10/100/1000 Ethernet ports. The EdgeRouter Pro has a faster CPU and two ports on the EdgeRouter Pro are combo RJ45/SFP ports, providing fiber connectivity. The PoE and Lite models are desktop routers, with fewer ports and peak throughput of up to 3 Gbps. This review will cover the EdgeRouter Pro.
Inside
The EdgeRouter Pro is designed to be a data center router. The chassis has permanent rack mount brackets and you probably wouldn’t want to use it as a desktop router as the noise from the two cooling fans is quite audible.
The router measures 19.06″W x 6.46″D x 1.73″H. The front of the device has the indicator lights and network ports. There is also a console port for local admin access, as well as a USB port which is not functional but according to Ubiquiti’s quick start guide, is “reserved for future use.” The power supply is internal, with a power cable connecting to the back side. The fans exhaust hot air out the back of the device. Below is a shot of the front and back views of the EdgeRouter Pro.
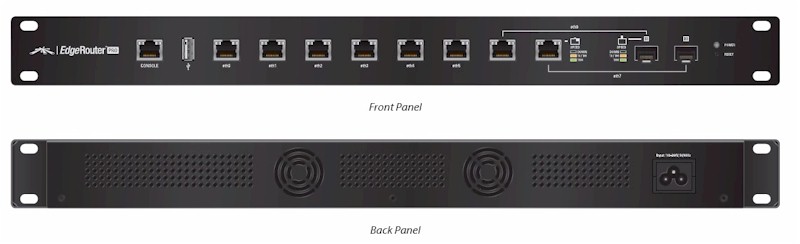
Front and Rear View
Inside the EdgeRouter Pro is a dual core, 64-bit, 1 GHz Cavium Octeon II CPU, 2 GB DDR3 RAM, and 4 GB Flash. A shot of the internal components is below.
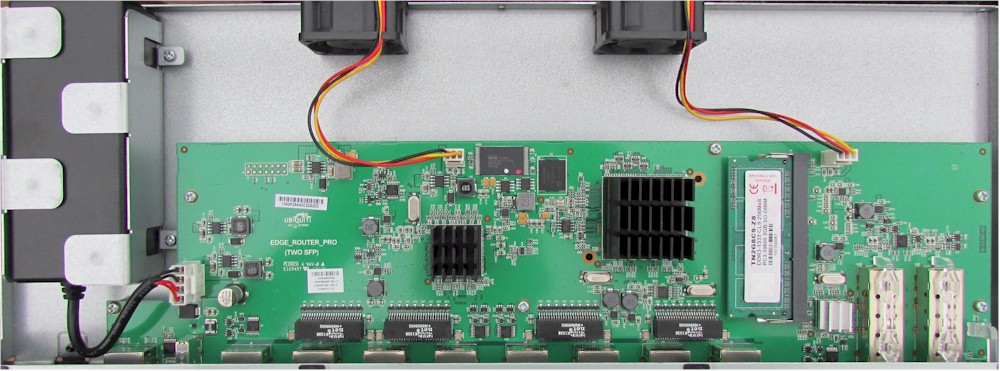
Main Board
Features
Here’s a quick rundown of the ERP’s key features extracted from its data sheet:
- 2,400,000 pps routing throughput (64 Byte packets)
- 8 Gbps routing throughput (512 Byte packets)
System and Services
- Basic: CLI, Configs, Sys Mgt, Connection management (connection tracking and flow accounting), Logging, SNMP
- Services: ssh, telnet, web GUI, DHCP v4/v6, DNS, web cache, LLDP, NTP, UBNT discovery, logging
- NAT: NAT masquerade, NAT rules
Interfaces
- (1) console, (6) 10/100/1000 RJ45, (2) 10/100/1000 RJ45/SFP Combo ports
- LAN = Ethernet, Pseudo Ethernet, Loopback, VLAN (802.1q), Bridging, Bonding (802.3ad)
- Encapsulations = HDLC, FR, iPoA, Bridged Ethernet
- PPP = PPP, PPPoE, PPPoA, multilink
- Tunnels: GRE, IP-in-IP, SIT
Networking
- IPv4, IPv6
- 802.1q VLANs
- DHCP Client and Server
- PPPoE client and server, bridging, bonding, GRE, VRRP
- Dynamic DNS, DNS forwarding, DHCP relay
Routing
- Basic = Forwarding, Static Routing
- Protocols = RIP, RIPng, OSPF, BGP, Policy Based Routing, IGMP Proxy
Security
- Firewall = Packet based IPv4/IPv6 (ACLs), Zone based, NAT
- Other = IPS, web filtering
- VPN = IPsec- S2S and remote client, OpenVPN – SIS and remote client, PPTP server for remote access and client, L2TP server for remote access
QoS
- FIFO, Stochastic Fairness Queuing, Random Early Detection (RED), Token Bucket (Hierarchical and Filter), Deficit Round Robin, Ingress Policing
High Availability
- WAN Load Balancing, VRRP, Clustering, Stateful NAT and Firewall Failover, RAID1, config sync
Operating System
Ubiquiti’s EdgeRouter EdgeOS is based on Vyatta, an open source network operating system. Vyatta is based on Debian Linux. (Note, in November 2012, Brocade announced it was acquiring Vyatta.)
You can familiarize yourself with Vyatta, and thus EdgeOS, by downloading a free Vyatta Virtual Machine (version 6.6) and running it in VMWare’s free VMWare Player software. There are some differences between Vyatta and EdgeOS (Ubiquiti forked Vyatta at version VC6.3), but they are more similar than different. Familiarizing yourself with Vyatta might be a good (and free) means to determine if the EdgeRouter is for you.
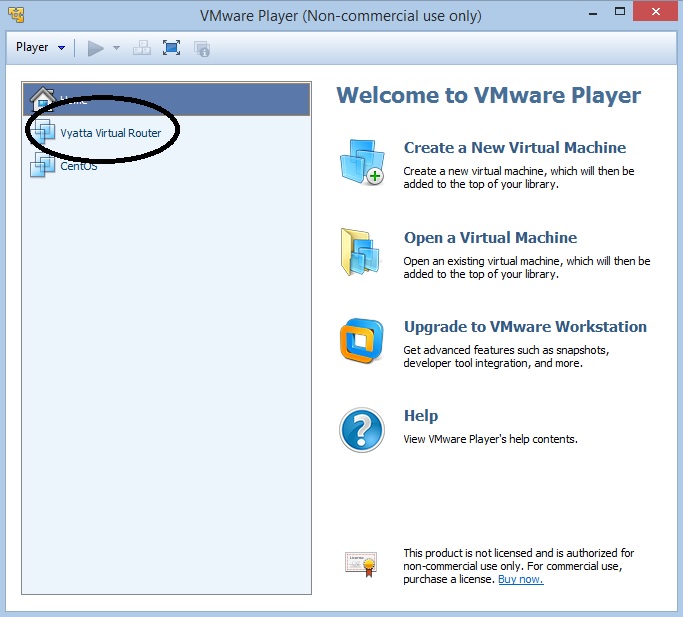
Vyatta Virtual Machine
We tested the EdgeRouter Pro with firmware version 1.4.0. Version 1.4.1 is now available, which Ubiquiti says is a maintenance release to fix some security vulnerabilities and critical bug fixes. Version 1.4.1 has no new features, with the exception of UDP fragmentation.
All functionality of the EdgeOS is configurable via the CLI (Command Line Interface). If you’re familiar with Juniper’s JunOS, the learning curve will probably be shorter. Familiarity with Cisco’s IOS also helps.
The Edge routers are also configurable via a GUI. Not all aspects of the Edge can be configured via GUI, although Ubiquiti is rolling out updated firmware versions with increasing GUI functionality. Presently, the GUI provides a useful dashboard and supports routing, security, services, and user configuration. There are also several wizards, such as the “WAN+2LAN” wizard, which I’ll discuss shortly.
Menu/Configs
When I configure a Cisco router using Cisco’s IOS, I write my configs in a text file, then copy and paste them into the router. This enables me to keep a copy of my configs and it makes it easier to edit them. You can do the same thing with the EdgeRouter, copying configs from Ubiquiti’s support site, editing as needed and pasting them into the router. Once they get the hang of it, many folks think working with a CLI is faster than a GUI.
EdgeOS configuration guides and examples can be found on Ubiquiti’s Community Knowledge Base. There you’ll find 24 FAQs, 50 CLI Basics, and 30 Config Examples to help you get your EdgeRouter up and running.
Resetting the EdgeRouter Pro to factory defaults and applying a wizard provides a good amount of functionality out of the box. The “WAN+2LAN” wizard in the GUI sets up DHCP, two LAN interfaces (eth0 and eth2) and one WAN interface (eth1), with both LAN interfaces NAT-ed out the WAN interface.
Below is a screenshot outlining the various configuration menus. Hitting the question mark (?) at any time in EdgeOS configuration mode provides a list of configuration options available at that level. For example, to see interface configuration options, you can start by typing set interfaces ?.
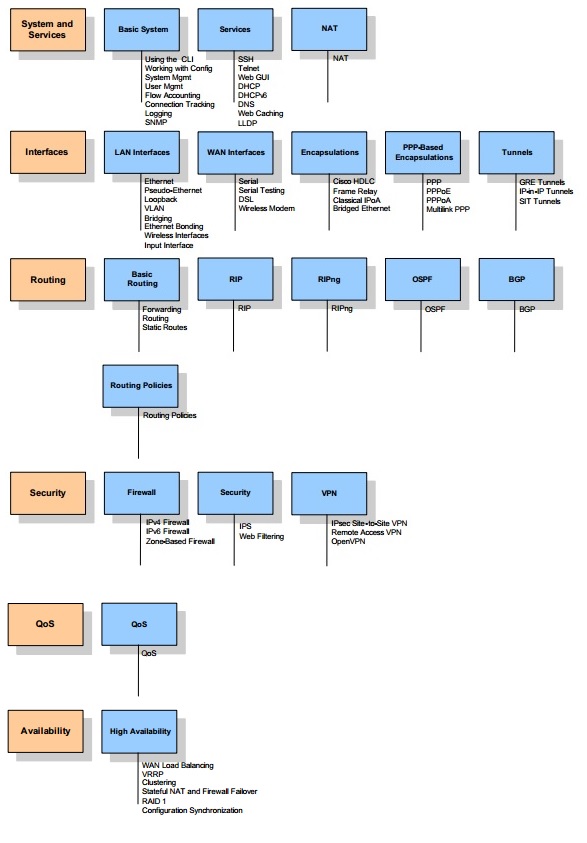
Menu Outline
I found the EdgeOS GUI a useful complement to the CLI. Ubiquiti provides a 57 page user guide for the EdgeOS GUI. I found firewall configurations were easy to apply via the GUI. The EdgeOS GUI also has some useful utilities, such as the dashboard which displays numerous details such as Tx/Rx rates on interfaces, interface stats and IP addresses, shown below.
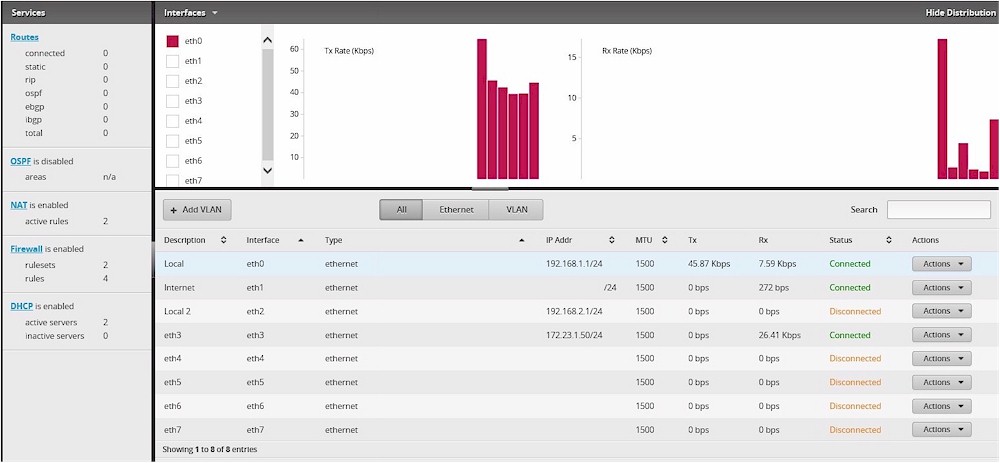
EdgeOS Dashboard
At its core, the EdgeRouter Pro is running on Linux. Thus, standard Linux file commands and tools are available. Further, you can write and run Linux shell scripts from the router. The Internet is a vast resource of Linux instructions and how-to’s if you’re willing to look. In addition, the Vyatta and Ubiquiti community have created quite a few configurations, utilities, and scripts, free to copy and try as you wish.
LAN
There are eight physical interfaces on the EdgeRouter, labeled eth0-eth07. With eight physical interfaces, the Edge Router Pro can physically connect to quite a few networks. All interfaces can be given a static IP address, get an IP address via DHCP and support a DHCP server.
802.1q sub-interfaces can also be created, allowing the Edge Router Pro to connect to a trunk port on an 802.1q switch and route between even more networks. According to the folks at Ubiquiti, the maximum number of VLANs supported on the Edge is 4096, although the real limit is dictated by CPU and memory consumption.
I successfully tested the Edge Router Pro’s VLAN trunking capability by setting up a physical interface with two sub-interfaces corresponding to three different VLANs. I also set up a DHCP server on the Edge for each of these three VLANs. I connected the EdgeRouter Pro physical interface to a trunk port on a Cisco SG200-28 switch configured with the same VLAN IDs I set up on the EdgeRouter Pro. Plugging a PC into access ports on the switch assigned to each of the VLANs got an IP address from the correct DHCP server on the EdgeRouter Pro, validating VLAN tagging was working as expected.
WAN
Any of the eight interfaces on the EdgeRouter Pro can be configured as a WAN interface, but load-balancing is currently limited to two WAN interfaces. I set up my EdgeRouter Pro with the WAN+2LAN wizard and followed the dual WAN load-balancing with failover guide located here.
I followed the instructions to test each WAN interface with the other disconnected before I applied all the configs and connected both interfaces. As you can see from the below screenshot, interfaces eth1 and eth3 are now in a load balancing group called “WAN_FAILOVER.”
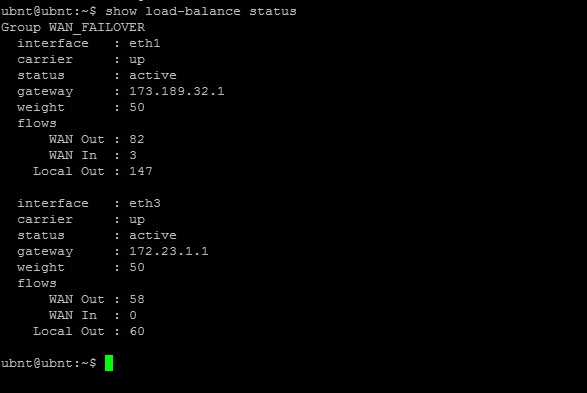
Dual WAN Status
To test WAN failover, I enabled a continuous ping to google.com (ping google.com -t) on my PC (connected to eth0), and disconnected eth1. Only one ping failed before the EdgeRouter Pro failed over to eth3. I then reconnected eth1, allowed it to restore, and disconnected eth3. Only three pings failed before the EdgeRouter Pro failed over to eth1. So far so good, WAN failover worked as expected!
With the config I applied, eth1 and eth3 will failover between each other. They are also configured for 50-50 load balancing. According to the failover guide, “this configuration will also start up a watchdog thread for each WAN interface that pings www.ubnt.com every 10 seconds. If there 3 consecutive failures, all traffic will fail over to the other WAN interface.” These timers and values are all adjustable.
A useful WAN feature, especially if you’re getting your WAN IP address via DHCP is Dynamic DNS. The Edge supports Dynamic DNS to dnspark, dyndns, namecheap, zoneedit, dslreports, easydns, and sitelutions. Dynamic DNS can be configured via the CLI following this guide, and Ubiquiti tells me it will be available in the GUI in an upcoming release. Following the guide, I successfully set up dynamic DNS to dyndns, as shown in the screenshot below. (I deleted my IP address and host name from the status.)
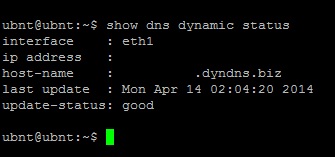
Dynamic DNS Status
VPN
The Edge supports IPsec, PPTP, L2TP, and OpenVPN (SSL) tunnels. All VPN configuration is via CLI. I found some useful guides on the Ubiquiti wiki for configuring the VPN tunnels. I successfully configured IPsec Site-to-Site, as well as remote PPTP, and L2TP tunnels on the Edge using CLI guides available on Ubiquiti’s support site.
I was not able to configure an OpenVPN or remote IPsec tunnels on the Edge. I experienced errors following the OpenVPN server setup using this guide when creating key files. I didn’t attempt a remote IPsec tunnel, as I didn’t find a guide on the Ubiquiti wiki.
I successfully tested IPsec on the EdgeRouter Pro by setting up a site-to-site tunnel to a Zyxel Zywall 110. The Edge supports 3DES and AES encryption as well as MD5 and SHA-1 authentication. The Ubiquiti wiki guide uses AES128 encryption and SHA-1 authentication, so I stuck with those settings. Below is a screenshot of the CLI show command displaying my active IPsec tunnel.
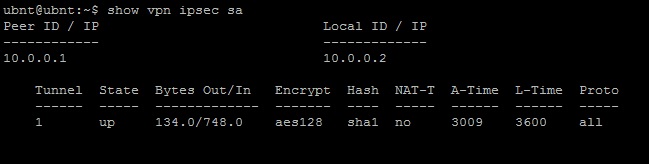
IPsec Status
Further, I successfully tested PPTP and L2TP on the EdgeRouter Pro from a Windows 7 PC and an iPhone. Below is a screenshot of the CLI show command displaying my active PPTP tunnel.
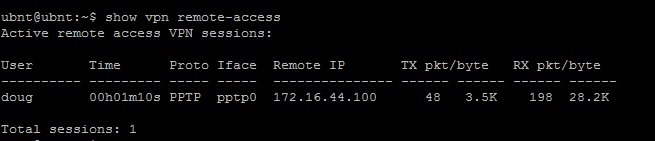
PPTP Status
We’ve been testing VPN throughput for some time using iperf as our real-world throughput test tool. Iperf has its limitations, though. Specifically, iperf measures throughput using a fixed TCP Window size.
After evaluating multiple different throughput test tools, we’ve chosen TotuSoft’s LAN Speed Test as our new real-world VPN throughput test tool. Totusoft’s LAN Speed Test measures TCP data transfer speeds from TotuSoft’s free LAN Speed Test client application to and from a shared folder on another device or to TotuSoft’s LAN Speed Test server application (cost = $6). I used the client and server application and measured throughput using a file size of 100 MB.
To measure VPN throughput, I used two PCs running 64-bit Windows with their software firewall disabled. I benchmarked these two PCs over a Gigabit LAN and measured 349 Mbps. My results for IPsec Site-to-Site, PPTP and L2TP tunnels are in Table 1.
| VPN Tunnel Type | Throughput (Mbps) | |
|---|---|---|
| Gateway-Client | Client-Gateway | |
| IPSec Site2Site | 217.1 | 156.1 |
| PPTP Client | 34.7 | 8.9 |
| L2TP Client | 49.1 | 36.9 |
Table 1: VPN throughput
Ubiquiti doesn’t provide a rating for IPsec throughput on the Edge, although they reported to me they measured throughput “around 220 Mbps” between two EdgeRouter Lite routers, and hoped that two EdgeRouter Pro routers could hit up to 500 Mbps. I didn’t expect to come close to 500 Mbps numbers as I’m testing the EdgeRouter Pro to a Zywall 110, which has an IPsec UDP rating of 300 Mbps.
As you can see, I measured the EdgeRouter Pro could encrypt and send IPsec data at 217.1 Mbps to the Zywall, and could receive and decrypt data at 156.1 Mbps from the Zywall. My guess is the Zywall was the bottleneck in my tests and these numbers would be higher if I was able to test between two EdgeRouter Pros.
For remote PPTP tunnels, I measured the EdgeRouter Pro could encrypt and send data at 34.7 Mbps to the client, and could receive encrypted data at 8.9 Mbps from the client. Finally, for L2TP tunnels, I measured the EdgeRouter Pro could encrypt and send data at 49.1 Mbps to the client, and could receive encrypted data at 36.9 Mbps from the client.
Overall, these speeds are tremendous! An IPsec tunnel between two routers running at over 150 Mbps enables LAN speed between two locations. Based on my tests, you would need WAN/Internet connectivity greater than 150 Mbps to max out the Edge’s VPN throughput.
Remote tunnels are typically constrained by the far end Internet connection. L2TP throughput on the EdgeRouter Pro was the faster of the two remote VPN options I tested with a download speed of 49.1 Mbps and upload of 36.9 Mbps. These speeds easily exceeds the average US ISP download (as reported by Ookla, the technology behind speedtest.net) of 22.9 Mbps and the average upload speed of 7.4 Mbps.
Firewall
The Edge firewall can be configured via ACLs (Access Control Lists) or zone-based. I’m more comfortable with list-based configurations, so I stuck with ACLs. Ubiquiti has a guide on zone-based firewall configurations here.
Edge firewall ACLs are configured with series of rulesets. Firewall rulesets are applied to interfaces to filter inbound, outbound, or “local” traffic “Local” traffic is traffic directed at the router itself.
Each Edge firewall ruleset is a list of rules defining action(s) to take on traffic. Firewall rulesets follow top-down logic and act on the first matching rule. Firewall rules are where you specify the traffic you want to accept, drop, or reject. Dropped packets are simply dropped, whereas rejected packets receive an ICMP message saying destination unreachable.
Firewall rules can be created to filter traffic based on IP address, port, protocol, session, fragment status, TCP flags, and time. There are also pre-built peer-to-peer applications that can be filtered including Applejuice, Bittorrent, Directconnect, Edonkey, Gnutella, and Kazaa.
The WAN+2LAN setup wizard in the GUI creates two firewall rulesets: WAN_IN and WAN_LOCAL. These statefulrulesets permit traffic that is part of an established two-way connection or related to an established connection, while all other traffic blocked. These two rulesets essentially enable a stateful firewall on the WAN interface. The below screenshot shows a snippet of the CLI configs for the WAN_IN and WAN_LOCAL firewall rulesets.
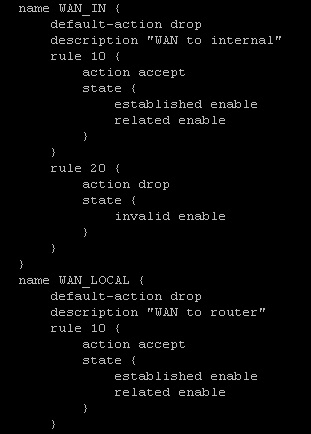
WAN_IN and WAN_LOCAL Firewall Rules
I found using this GUI wizard helpful to get the firewall enabled and to figure out how to create additional firewall rules. You can edit the firewall via the GUI and CLI, and you will have to edit the firewall to get the most out of the Edge. For example, VPN functionality requires editing the firewall rules. Other configurations on the Edge also use rules, such as NAT (Network Address Translations) configurations.
Routing Performance
Let’s preface this section by stating that Ubiquiti’s EdgeRouters and in particular the EdgeRouter Pro have routing performance beyond our capability to accurately measure it.
Routing performance for the EdgeRouter Pro loaded with v1.4.0 firmware and using our standard test method is summarized below. The throughput results listed in Table 2 are obviously not reflective of the router’s actual 8 Gbps spec’d performance. In our review of the EdgeRouter Lite, we measured WAN-LAN at 821 Mbps, LAN-WAN at 772 Mbps and Total Simultaneous Throughput at 1,306 Mbps. After trying different configurations on the EdgeRouter Pro, we’ve concluded the measured routing performance of the EdgeRouter Pro is beyond our ability to accurately test it. (It’s that fast!)
Essentially, these results below are more reflective of our testbed limits instead of the router. (Note, the maximum simultaneous connections result is at the limit of our test process, indicating the EdgeRouter Pro can certainly support enough user sessions.)
| Test Description | EdgeRouter Pro |
|---|---|
| WAN – LAN | 304.1 |
| LAN – WAN | 553.6 |
| Total Simultaneous | 736.6 |
| Maximum Simultaneous Connections | 30,998 |
| Firmware Version | v1.4.0 |
Table 2: Routing Throughput
For completeness, below is a screenshot of our throughput tests for download and upload speeds.
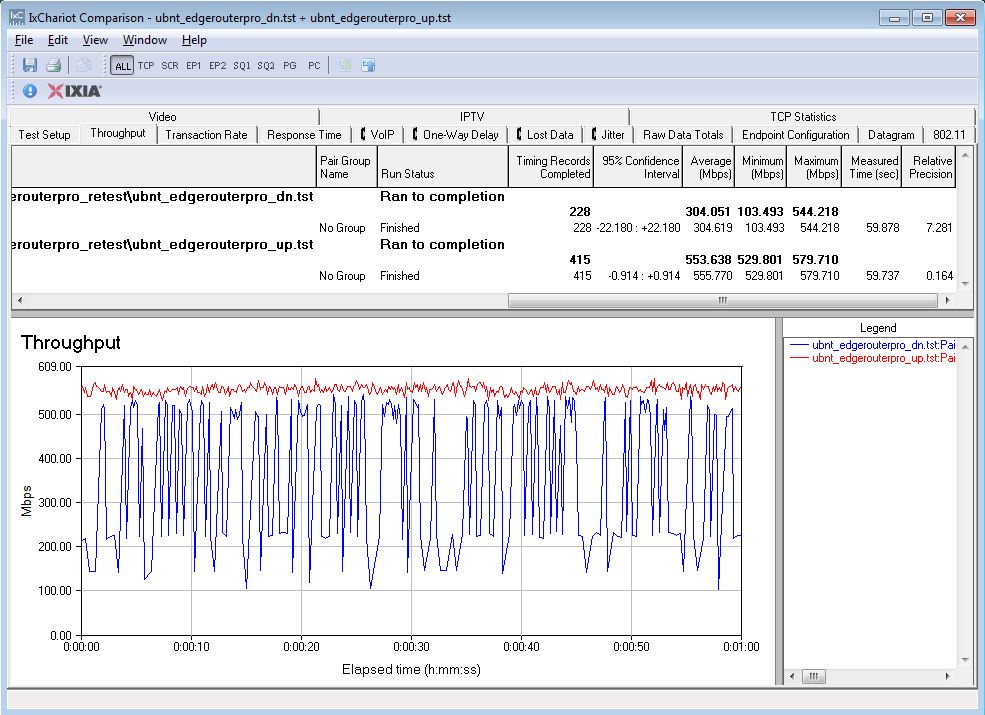
Unidirectional Throughput
Simultaneous up/downlink throughput is shown in the below IxChariot plot.
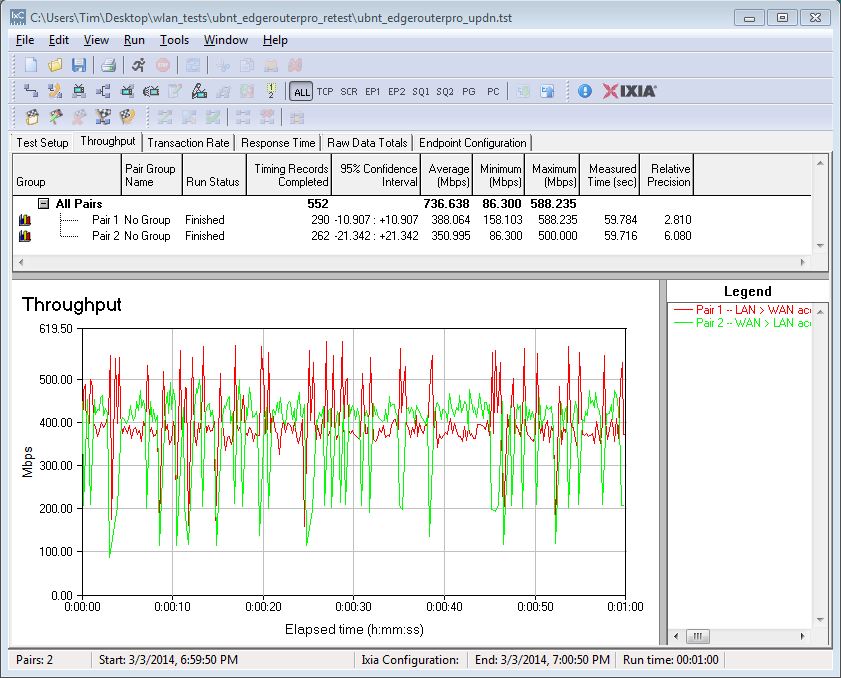
Bidirectional Throughput
Closing Thoughts
The Ubiquiti EdgeRouters are first and foremost, extremely fast routers. The previously reviewed EdgeRouter Lite is near the top of our router charts with Total Simultaneous Throughput of 1,306 Mbps and is available for less than $100. The EdgeRouter Pro is rated over 2.5x faster than the EdgeRouter Lite, its performance exceeds our test tool’s capability and costs only $399!
I only scratched the surface of the EdgeRouter Pro’s capabilities in this review. I successfully tested VPNs, firewall rules, VLANs, dual WAN load-balancing and dynamic DNS following various configuration guides on Ubiquiti’s wiki. Clearly, the EdgeRouter Pro offers significantly more features than I could possibly test in a single review.
Ubiquiti bills the EdgeMAX routers as “Advanced Routing Technology for the Masses.” Certainly, the EdgeMAX routers are priced for “the Masses,” and bring high throughput routing speeds to a very affordable level. However, “the Masses” are more accustomed to GUI-based router configuration and this is where Ubiquiti’s OS and documentation come up short. While Ubiquiti has made progress in expanding GUI-based configuration options, you’ll still need to use the command line for most anything other than basic setup. This is not a router for novice users!
[Editors note from Tim: To reinforce this point, Doug took twice as long for this review vs. other VPN routers. And he is no stranger to CLI-based router configuration.]
I reviewed Ubiquiti’s UniFi Wi-Fi controller software awhile back and complimented Ubiquiti for “pushing the wireless industry to a more economical and flexible solution.” I think Ubiquiti has done it again with the EdgeMAX routers, challenging the wired network industry with an economical, fast and flexible routing solution!
