Introduction
| At a Glance | |
|---|---|
| Product | D-Link MediaLounge DSM-G600 Wireless G Network Storage Enclosure |
| Summary | Wireless enabled BYOD NAS enclosure with Gigabit Ethernet and UPnP AV server |
| Pros | • Gigabit Ethernet support • Functions as 11g AP or client • Includes UPnP AV server |
| Cons | • No print server • No FTP or HTTP file access • Noisy fan • No backup features |
5 April 2006 Editor’s Note: This review describes the RevA version of the product, which was provided for review by D-Link. A more recent RevB version is also available.
There are a lot of consumer-level Network Attached Storage (NAS) devices on the market these days, and over the last year or so I’ve had the chance to try out quite a few. Most of them are designed to be hooked into a 100 Mbps wired network, and are typically used by other computers on the network for sharing and backing up data. However, with 1000 Mbps (Gigabit) networks becoming common, and more and more people having wireless networks in their home, maybe there’s room for some additional network flexibility.
In this review, I’ll be taking a look at an NAS product from D-Link that’s a network “jack of all trades”. The DSM-G600 supports 10, 100 and 1000 Mbps networks, and in addition, it supports wireless networks as either a client or an access point. And to top it all off, it has a built-in multimedia server to dish up music, movies and images to other devices on your network.
The front of the DSM-G600 has a row of status LEDs and a power button. On the back there’s a single antenna, a network port, a fan vent, a reset button and two USB ports (see Figure 1).

Figure 1: DS-G600 Back Plate
Since the G600 is a “bring-your-own-disk” NAS device, a single 3.5″ ATA/IDE drive must be installed before it can be used. Installing the disk is fairly simple, but also a little bit awkward – the power and IDE cable are positioned on the sides of the disk cage rather than on the end where they need to connect to the drive.
The device can operate wirelessly, but the documentation stated that initial configuration needed to be done over a wired network. For this reason, after my drive was in, I connected power and a network cable. When I powered the unit up, the fan immediately came on and was quite loud. I hoped that the fan was thermostatically controlled and thus would eventually turn off, but that was not the case – it runs continuously.
Setup Browser Battles
Both Windows and Mac computers are supported by the G600, so I started configuration using my Apple iBook. The G600 uses network auto-discovery protocols, supporting both Bonjour (the protocol formerly known as Rendezvous) and UPnP. D-Link advertises this as a way to automatically add the network drive to your system, but it’s not quite that easy.
What this feature really means is that the configuration web server on the device is advertised on the network. On my iBook, it showed up as “DSM-G600” under my Bonjour bookmarks; under XP, I got a new UPnP icon in the System Notification (Tray) area. In both cases, the automatic discovery process was just used as a way to get to the web configuration page.
Using Safari – the default web browser on my iBook – I used the Bonjour bookmark to start down the wizard path on the initial configuration page (see Figure 2). It was there that I found standard settings for changing the default administration password and network parameters. But after two configuration pages, I could get no further.

Figure 2: Setup Wizard
The “Next” button here had no effect; even though Safari was listed as being supported, I assumed it was a browser issue so I started up Firefox and went down the same path. This time I got all the way to the end of the wizard, but once again I got hung up, as the final “Restart” button had no effect. I could only quit the wizard; none of my changes could be applied (see Figure 3).

Figure 3: The Setup Wizard and Mac OS X don’t play nicely together
I next tried Internet Explorer on my iBook, but it hung up on the very first page of the Wizard. Sigh. Admitting defeat, I retreated to my Windows XP system, where I found that I could get all the way through the wizard using Internet Explorer. This tells me that D-Link is probably using some questionable JavaScript code in their configuration web pages; while they may be usable under Macintosh, you can only fully configure the device under Windows.
Once I had the basic settings configured using the Wizard, I started exploring the other options.
Feature Configuration
The initial configuration page had options for both wired and wireless settings, but I initially left the wired configuration in place and started exploring the other available options. Under the “Advanced” menu, I found a screen that would allow me to create new network shares and assign them either read-only or read-write privileges (see Figure 4).
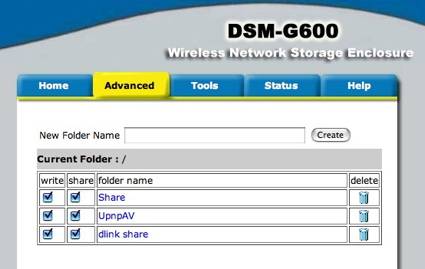
Figure 4: Share Setup
This screen also allowed me to manage external drives plugged into the USB ports (see Figure 5). Drives formatted only with FAT and FAT32 filesystems are recognized. (The internal drive gets formatted with the ext3 filesystem.)
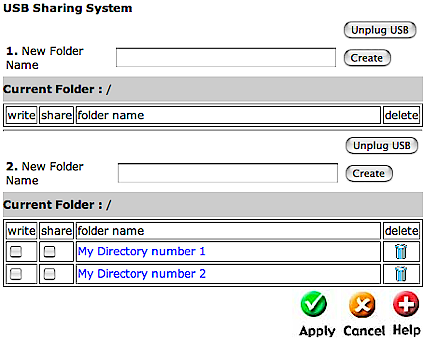
Figure 5: USB Drive Management
The “Tools” menu had a number of options. First was a screen that allowed me to set the time; this had a field to specify an NTP server for automatic time synchronization, but it didn’t seem to take (see Figure 6). Even though I put in a server, the time was never set.
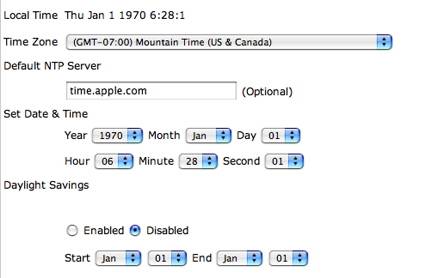
Figure 6: Time Setup
Feature Configuration, Continued
Other capabilities found in this section allowed me to backup and restore my settings, reboot, reset, and “Rescan the Media Server Content”. This last option was the only place in any of the menus where I saw specific mention of the UPnP media serving capabilities of the box. Even the “Help” web page failed to address this option, nor did it have any other mention of media serving.
The Firmware option had menus for updating the firmware, and the “Format” menu allowed the internal drive to be formatted. The top-level “Status” menu had a couple of features. The first screen showed the basic network configuration and the status of the hard drive. The second screen was a “Logging” screen that showed various status messages (see Figure 7).
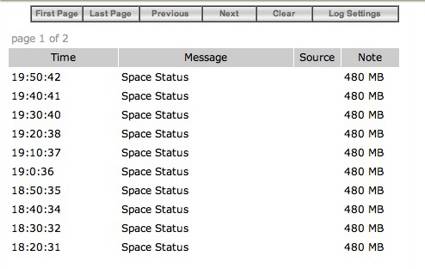
Figure 7: Logging Messages
An option menu allowed the specification of what types of messages would be displayed (see Figure 8).
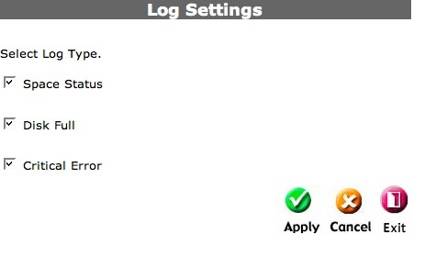
Figure 8: Logging Options
One bug I noticed under the log menu was the “pages” display. Often times, the display indicated that there were two pages of status messages available, when in reality there was only one.
The final top-level menu was “Help”, which allowed me to see short assistance messages regarding the various options found on the previous pages.
One thing I did not find anywhere was an option to set the drive spin-down time. The NAS units on my LAN sit idle most of the time, so it’s nice to have an option to tell them to turn the drive off when idle; this reduces noise, heat and power consumption. Another feature I noticed missing was any sort of automated backup utility. Many consumer NAS devices include software to automatically do backups from other computers on the network, but the G600 had no such capability. If you need this feature, you’ll have to purchase a third-party product. Finally, the G600 does not support file access via FTP or HTTP.
Wireless
After I had explored all of the wired network options, I moved on to the wireless capabilities. The device has the ability to act as either a client to a wireless network or as an access point (see Figure 9).
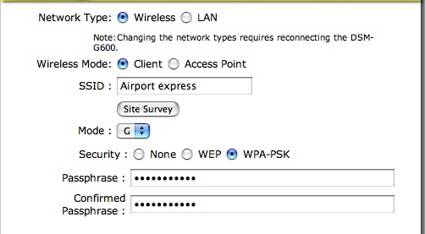
Figure 9: Wireless setup
Both modes have support for either WPA or 128-bit WEP security, but not WPA-2. When I set the device up as an access point, I could connect to it wirelessly and it worked fine, but a number of options you’d normally see in an inexpensive consumer access point were missing. For example, there was no way to set up up a DHCP server, a firewall, MAC filters, etc.
I also tried the device out as a wireless client. In client mode, the device connects wirelessly to an access point on your LAN. To assist in the connection, a “site survey” capability exists, which scans your area and gives you a list of available access points to join. Well, that’s what it is intended to do, but in my case it found none of the three access points that I can normally see. As a result, I had to manually enter the SSID of my access point, followed by my encryption information. Once I had this info entered, the G600 was able to connect to my access point and I could access it wirelessly.
As I experimented with using the unit as a client, I scratched my head a bit to figure out the utility of this mode. Even disregarding the decrease in speed you’d see using a wireless network drive, I couldn’t see a whole lot of need for locating a NAS device far away from my access point and other network equipment, where it could be directly plugged in; perhaps other people have different needs. Maybe if the loud fan gets to be too aggravating, putting the device out in the garage wouldn’t be a bad idea…
UPnP
As mentioned earlier, despite very little information on the subject from D-Link, the G600 has the capability to act as a UPnP based multi-media server. What this means is that you can add content such as music, movies and pictures to the G600, and it will serve them up using the UPnP Audio/Video (AV) protocol. There are a number of devices on the market that support this protocol. For my testing, I used a device that I already have on my network: the Buffalo LinkTheater [reviewed here].
The basic idea is that the G600 will scan its drive to catalog the media available, then send the results to a client device for display and user selection. Upon demand, the G600 will stream the media to a client device such as the LinkTheater for display or playback. Figure 10 shows the main menu of the LinkTheater once it has connected to the G600.
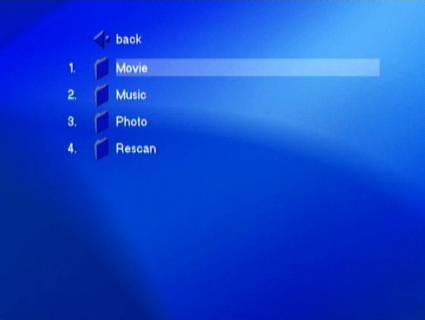
Figure 10: Buffalo LinkTheater connection to the DSM-G600 Media Server
I found that the G600 worked fairly well in this mode; I was able to play LinkTheater-supported music and video from the G600 without issue, though there were a few oddities. For example, all of the album art from my music was shown in the photos section. I guess some people might consider this desirable, but viewing a slide show of album-art isn’t on my list of things to do. Also present was a “Playlist” folder, but there was no documentation on how to create a playlist. Finally, a “Genre” menu was presented, but all of my music was categorized as “Blues”.
NAS Performance – Read
To see how well the G600 performed, I used IOzone to check the G600’s file system performance as described here. The test was run under Windows XP on a Dell Inspiron 1000 laptop with 384 MB of RAM. A Seagate 120 GB Barracuda 7200 RPM with 8MB Cache was the hard drive loaded into the G600.
For my Gigabit network setup, I used a Netgear GA511 Gigabit PC card in my laptop, which was directly connected to the G600 with a network cable. For wireless, the G600 was connected to my WPA encrypted Apple Airport Express access point running in 802.11g mode.
NOTES:
- How fast a computer can read or write data to a drive depends on many factors specific to the system running the test, so this test may not represent the actual performance you’d see on your own system.
- The maximum theoretical data transfer rate possible on a 100 Mbit network is around 12,000 kBps, so any values that exceed that number are as a result of caching behavior, not network speed.
- Wireless performance will vary greatly depending on the speed and reliability of your wireless connection.
For my wireless tests, I didn’t try to optimize wireless signal quality, nor to test the limits of the G600’s wireless range. I just used the device where and how I naturally would in my house. This meant that the G600 was on a different floor, and probably about 20 to 30 feet from the 802.11g Apple Airport Express access point to which it was connected.
I should also mention that when I started running my IOzone tests, I was consistently disconnected from the device; this persisted over reboots of both my test system and the G600 itself. I consulted with engineers at D-Link, but they were unable to replicate my problem using the same IOzone test. After a day or so, I went back to the tests and the disconnects no longer occurred. I had seemingly changed nothing, so it is not clear what made the problem go away.
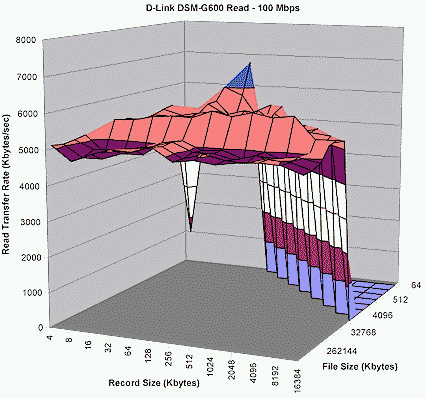
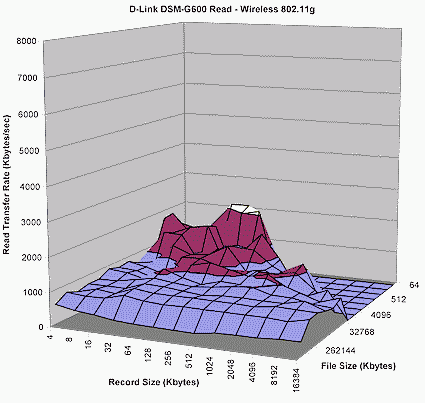
Figures 11 through 13 show read performance for a range of file and record sizes, using 100 Mbps and 1000 Mbps Ethernet connections, as well as the 802.11g wireless connection that I described above.
Figure 11: 100 MBit Read Performance
(click image to enlarge)
100 Mbps read performance was on par with other drives in this class, and Figure 11 shows a slight performance benefit from using a Gigabit Ethernet connection.
Figure 12: 1000 MBit Read performance
(click image to enlarge)
As expected, wireless connection causes a significant throughput hit, so you would probably only want to use that mode as a last resort.
Figure 13: Wireless Read Performance
(click image to enlarge)
NAS Performance – Write
Figures 14 through 16 show write performance for a range of file and record sizes, using 100 Mbps and 1000 Mbps Ethernet connections as well as an 802.11g wireless connection.
Figure 14: 100 Mbit Write Performance
(click image to enlarge)
Due to cached performance dominating Figures 14 and 15, you can’t really see the slight performance boost provided by the Gigabit Ethernet connection with larger file and record sizes.
Figure 15: 1000 MBit Write performance
(click image to enlarge)
The wireless test results in Figure 16 once again show a significant performance hit.
Figure 16: Wireless Write Performance
(click image to enlarge)
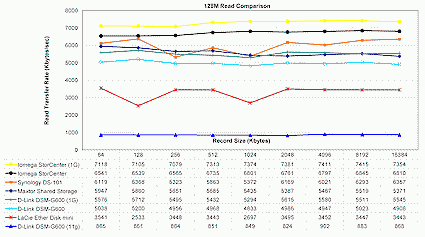
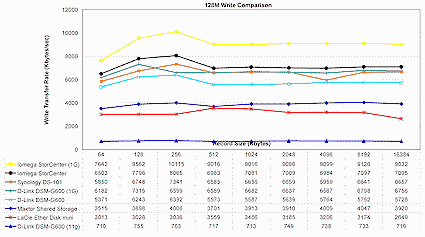
NAS Performance – 128 MB Comparison
To put these results into perspective, the plots shown in Figures 17 and 18 include data taken with the same IOzone configuration from previous reviews of similar-class drives:
To minimize the operating system caching effect, the comparison was done with a 128 MByte file, so it more accurately reflects the real performance of the NAS itself. As you can see, the G600 falls in the center of the pack; the Gigabit run only shows a little performance boost, and as expected, the wireless transfers are far slower than wired ones.
Figure 17: Comparative Read performance
(click image to enlarge)
Figure 18: Comparative Write performance
(click image to enlarge)
Under The Covers
Figure 19 shows the main board of the G600. In the photo, it’s a bit hard to see, but the main processor for the unit is provided by Intel’s IXP420 Network Processor; the IDE controller is provided by Acard; and a VIA Vectro VT6212 provides the USB support and the Gigabit network controller. For the wireless capabilities, a mini-PCI card (shown pulled away from its socket) is used with an Atheros AR5004X chipset.
Figure 19: DSM-G600 Main Board
(click image to enlarge)
It was fairly easy to determine that the G600 was running Linux internally. A network port scan identified it as running a Linux kernel based on either version 2.4 or 2.5. A Telnet connection to the UPnP port revealed the following string:
SERVER: Linux/2.4.27-uc1, UPnP/1.0, Intel SDK for UPnP devices /1.2
Examining a firmware image revealed a “tarred” collection of Linux binaries, including a kernel and a couple of disk images. After untarring the firmware file and then unzipping the root image within, I mounted the root disk image on a Linux box and was able to rummage around.
I found a typical set of embedded ARM architecture Linux executables, including busybox and Samba. Digging a bit deeper, I found the html directory, where I noticed a number of pages, including user creation, group creation and email logging that weren’t available from any of the G600 menus.
When I called up the previously hidden user creation page from my browser, I wasn’t able to successfully create a user, so it didn’t appear to be functional (see Figure 20). However, I was able to make use of the email-logging page and successfully set it up to periodically send me email status messages.

Figure 20: Hidden User Creation page
As I was looking at the firmware image, I noticed a cramfs disk image being used for the “/usr” partition. I didn’t have a cramfs driver handy, but I wanted to see what was in it. I suppose I could have gone out looking for a driver, but I decided to take the lazy man’s approach – don’t try this at home, kids! I created and uploaded a new firmware that gave me a listing of the /usr directory. The approach I took was to find a suitable executable script in the root disk image where I could add my own code.
The file I settled on was the Samba startup script. When this runs, the hard drive should already be mounted, so I could add code to give me a directory listing with the output redirected to the hard drive. Then it was just a matter of adding the command “ls -lR /usr > /home/UpnpAV/log” to the script. Once this was done, I reversed the steps I had previously taken to unpack the firmware, and created my new version. (Manufacturers often add a propriety checksum algorithm to the firmware image, but D-Link had not; it was just a straight tar file.) After I recreated the tar file, it was just a matter of using the standard firmware upgrade steps to load my new image.
As I did the final upgrade reboot, I worried that I had messed something up and I would end up with a destroyed box, but the blinking of the lights looked normal and it came up! I screwed up my command the first time (and the second), putting it in the wrong place, but eventually I got it right and finally found a “log” file in my network directory containing a listing of the “/usr” directory. There was not much new of interest in the directory, however; it was mostly just a standard assortment of embedded busybox commands. I had hoped to find a telnet or ssh daemon, but no such luck.
While I was at it, I changed my approach a bit; instead of executing a single command in the Samba startup script, I added a command to execute a script from the hard drive. Once I had done this, I could easily add my own commands to see which processes were running, look at memory usage, examine the system logs, etc. Every time the box booted, my commands would be executed.
I learned a few things from this approach. The G600 runs NFS, but it is not fully configured, so it can’t be used. The box has 64 MB of RAM, which is a bit more than comparable boxes I’ve worked with. A tftp process is run at boot-time. I didn’t have time to see what it was being used for, but typically tftp is used to upload new firmware. My approach of executing a hard drive script could open up a lot of possibilities for adding functionality to the device. I also noticed that the NSLU2 developers group has taken notice of the G600 as well, so maybe it will get really opened up.
Since the device is running Linux and other GPL licensed software, D-Link should be providing source code for the GPL licensed code. A quick review of D-Link’s GPL ftp download site showed source code for both the Linux kernel and Samba, but not for Busybox. Hopefully this is just an oversight that will be corrected soon.
Conclusion
The G600 has some nice features. Its wireless capabilities give it flexibility, as does its support for Gigabit networks. The UPnP serving support was a nice addition to the box, as was the ability to add external USB disks.
But I found a number of drawbacks as well. From the start, the fan noise was an aggravation, and the inability to configure the device from my iBook was an annoyance as well. The performance boost of Gigabit mode was minimal, and although it was nice to have wireless capabilities, the feature set of the device in access point mode was limited enough that you’d probably be better off using a cheap full-featured device for your wireless needs.
Comparing the G600 to similar “BYOD” products in its class, I’d rate it lower than the Buffalo Kuro Box, Maxtor Shared Storage Drive or Synology DS101. The G600 has fewer NAS features, is noisier, and has lower filesystem performance. But on the plus side, the G600 has media serving capabilities that the others lack.
As far as cost/performance, you can pick up a 200GB Maxtor Shared storage on-line for around $240 including shipping, while the G600 will run you about $150 without a drive. Add a new 200GB 7200RPM IDE drive for $70 and you’re just about even. Of course the Maxtor has no wireless, but a cheap access point can be had for $20-$30.
Put another way, the G600 isn’t the most flexible or speediest NAS available, but its unique combination of wired and wireless connectivity, UPnP media serving and BYOD format just might fit your requirements.