Introduction
There are many different types of devices and mechanisms within the security environment to provide a layered approach of defense. If an attacker is able to bypass one layer, another layer should stand in the way to protect the network. Two of the most popular and significant tools used to secure networks are firewalls and intrusion detection systems.
In this article, we will examine the various types of firewalls and understand the architecture behind them. We will also discuss attack indications and the countermeasures that should be applied in order to secure the network from breach.
What is a Firewall?
A firewall is a device installed between the internal network of an organization and the rest of the network. It is designed to forward some packets and filter others.
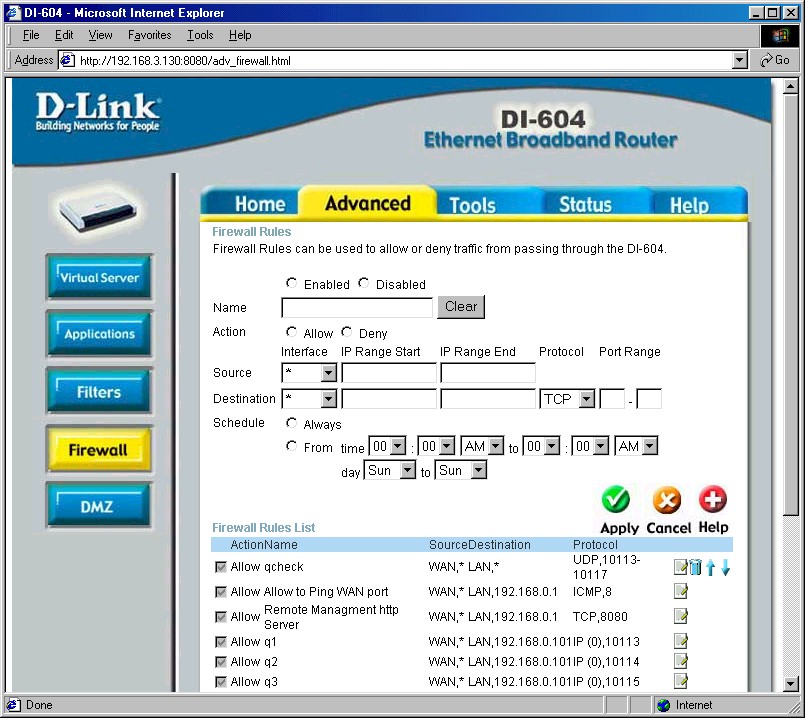
The rudimentary functionality of a firewall is to screen network traffic for the purpose of preventing unauthorized access between computer networks. For example, a firewall may filter all incoming packets destined for a specific host or a specific server such as HTTP or it can be used to deny access to a specific host or a service in the organization. The following image depicts a firewall installation in the network.
Firewalls are a set of tools that monitors the flow of traffic between networks. Placed at the network level and working closely with a router, it filters all network packets to determine whether or not to forward them towards their destinations.
A firewall is often installed away from the rest of the network so that no incoming requests get directly to the private network resource. If it is configured properly, systems on one side of the firewall are protected from systems on the other side. Firewalls generally filter traffic based on two methodologies:
- A firewall can allow any traffic except what is specified as restricted. It relies on the type of firewall used, the source, the destination addresses, and the ports.
- A firewall can deny any traffic that does not meet the specific criteria based on the network layer on which the firewall operates.
The type of criteria used to determine whether traffic should be allowed through varies from one type of firewall to another. A firewall may be concerned with the type of traffic or with source or destination addresses and ports. A firewall may also use complex rules based on analyzing the application data to determine if the traffic should be allowed through.
Every security device has advantages and disadvantages and firewalls are no different. If we applied strict defensive mechanisms into our network to protect it from breach, then it might be possible that even our legitimate communication could malfunction. On the other hand, if we allow entire protocol communications into our network, then it can be easily hacked by malicious users. So, we should maintain a balance between strictly-coupled and loosely-coupled functionalities.
Firewalls also can’t do everything. There are some things that they are good at and others that they aren’t. Here are some examples of things that firewalls excel at:
- Firewalls can be configured to bar incoming traffic to POP and SNMP and to enable email access
- Firewalls can also block email services to secure against spam.
- Firewalls can be used to restrict access to specific services. For example, the firewall can grant public access to the web server but prevent access to telnet and the other non-public daemons.
- Firewalls verify incoming and outgoing traffic against firewall rules, ensuring that only traffic that meets the rule requirements gets through
- Firewalls are excellent auditors. Given plenty of disk or remote logging capabilities, they can log any and all traffic that passes through.
And on the minus side:
- A firewall can’t prevent revealing sensitive information through social engineering.
- Firewalls can’t protect against what has been authorized. Firewalls permit normal communications of approved applications. If those applications themselves have flaws, a firewall will not stop the attack, because to the firewall, the communication is authorized.
- Firewalls are only as effective as the rules they are configured to enforce.
- Firewalls can’t stop attacks if the traffic does not pass through them.
- Firewalls also can’t secure against tunneling attempts. Applications that are secure can be Trojaned (compromised). Tunneling bad things over HTTP, SMTP and other protocols is quite simple and easily demonstrated.
Firewall Types
The way a firewall provides greater protection relies on the firewall itself, and on the policies that are configured on it. The main firewall technologies available today are:
- Hardware Firewall
- Software Firewall
- Packet-Filter Firewall
- Proxy Firewall
- Application Gateways
- Circuit-Level Gateways
- Stateful Packet-Inspection (SPI)
Let’s briefly look at each of these types.
A hardware firewall is preferred when a firewall is required on more than one device or when it is preferred to have centralized protection. The disadvantage of this approach is that if the firewall is compromised, all the devices that it serves are vulnerable.
A software firewall is usually considered a second layer of security. It is run on a device to protect it from malware, worms, viruses and poisoned email attachments. It looks like any other program and can be customized based on network requirements. Software firewalls can be customized to include antivirus programs and also to block sites and images.
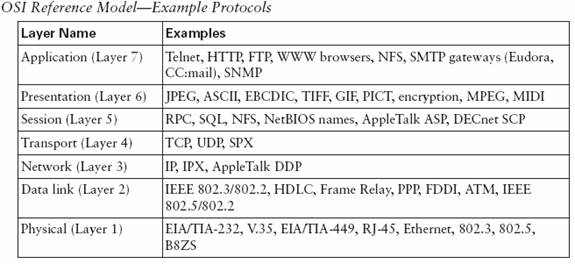
A packet-filtering firewall filters at the network or transport layer. It provides network security by filtering network communications based on the information contained in the TCP/IP header of each packet. The firewall examines these headers and uses the information to decide whether to accept and route the packets along to their destinations or deny the packet by dropping them. A Packet-Filter firewall is a router that uses a filtering table to decide which packets must be discarded.
Packet-Filtering makes decisions based upon the following header information:
- The Source IP address
- The Destination IP address
- The Network protocol in use (TCP ,ICMP or UDP)
- The TCP or UDP source port
- The TCP or UDP destination port
- If the protocol is ICMP, then its message type
The packet-filter firewall uses information available in the network and transport layer header. However, sometimes we need to filter a message based on the information available in the message itself (at the application layer). For example, assume that an organization only allows access to users who have previously established business relations with the company. In this case, a packet-filter firewall is not feasible, because it can’t distinguish between the different packets arriving at TCP port 80.
Proxy firewalls can help in this situation by providing a trusted intermediary. Customer traffic would be directed to the proxy where the proxy firewall runs a server process to receive the request. The server opens the packet at the application level and confirms whether the request is legitimate or not. If it is, the server initiates a new network connection based on the original request and sends the message to the intended server, otherwise the message is dropped. Proxy firewalls can also cache and log requests in addition to their filtering and control functions.
Like proxy servers, application gateways also analyze application-level information to make decisions about whether or not to transmit packets. Application gateways act as an intermediary for applications such as email, FTP, Telnet, HTTP, etc. An application gateway verifies communication by asking for authentication to pass the packets. It can also perform data conversion if necessary.
For example, an application gateway can be configured to restrict FTP commands to allow only get commands and deny put commands. Application gateways can also be used to protect vulnerable services on protected systems by disallowing direct communication between the end user and a destination service.
Common disadvantages when implementing application gateways include slower performance and lack of transparency. Each application the gateway handles must be programmed into the device. So there are limits to what the gateway can handle.
A key difference between proxy firewalls and application gateways is that the latter does not require applications to be configured to use it. Proxy firewalls require that applications be explicitly configured to connect to them.
Circuit-level gateways work at the sessions layer (5) of the OSI model or the TCP layer of the TCP/IP (Layer 4). Their primary job is to monitor the TCP handshake between packets to determine whether a requested session is legitimate. Circuit-level gateways operate by relaying TCP connections from the trusted network to the untrusted network. This means that a direct connection between the client and server never occurs.
The main advantage of circuit-level gateway is that it provides services for many different protocols and can be adapted to serve an even greater variety of communications. A SOCKS proxy is a typical implementation of circuit-level gateway.
A stateful packet-inspection (SPI) firewall permits and denies packets based on a set of rules very similar to that of a packet filter. However, when a firewall is state-aware, it makes access decisions not only on IP addresses and ports but also on the SYN, ACK, sequence numbers and other data contained in the TCP header. Whereas packet filters can pass or deny individual packets and require permissive rules to permit two-way TCP communications, SPI firewalls track the state of each session and can dynamically open and close ports as specific sessions require.
Firewall Identification
Normally, firewalls can be identified for offensive purposes. Because firewalls are usually a first line of defense in the virtual perimeter, an attacker usually needs to identify the firewall technology in use and how it is configured before mounting an effective attack.
Port scanning is typically employed to investigate the ports in use by a target. If an application’s standard ports have not been redirected to less obvious ones, their use can help an attacker quickly narrow his or her focus. Nmap is probably the most famous port-scanning tool available.
Banner grabbing is also a tell-tale for sloppy network security. It can enable an attacker to easily obtain very helpful details about the services in use, including versions used. Services most vulnerable to banner grabbing are HTTP, FTP and SMTP. Banner grabbing can easily pass through firewalls by using what looks like legitimate connections.
Finally, "firewalking" uses traceroute-like IP packet analysis in order to verify if a data packet will be passed through a firewall.
Conclusion
Though some have predicted the end of the firewall, its strategic location in the network makes it an indispensable tool for protecting assets. Good security practices continue to dictate that firewalls should be deployed between any two networks of differing security requirements.
Ajay Yadav is a security researcher for the InfoSec Institute with a Masters Degree in Computer Science. He has attained numerous premier certifications in Information Security, Software and Database domain.
