Introduction
| BuffaloTech AirStation 54Mbps Broadband Router (WBR-G54) | |
|---|---|
| Summary | Broadcom-based draft-802.11g router. Supports multipoint bridging and repeating |
| Update | 1/3/2003 – Buffalo adds guarantee for interoperability with 802.11g released spec. |
| Pros | • It really works! 20+Mbps speed with 11b compatibility • Includes wireless repeating • Attractive pricing |
| Cons | • One active 11b client kills 11g throughput boost • High variation in throughput • “Turbo” mode doesn’t work • User Interface needs work |

In the race to be the first to market with a draft-standard 802.11g product, Buffalo Technology made it to at least the SmallNetBuilder labs before Linksys did. They sent both their WBR-G54 router and WLI-CB-G54 CardBus client card for evaluation, and evaluate them I did. This review will cover primarily the router, and a RapidReview of the client card will follow later.
I’ll cut right to the chase with the answer that you’re most interested in. Yes, the products really did produce “11a” level speeds of about 20+Mbps and had the range I expected from a 11b product (although you don’t get both at the same time, of course!). There were some rough spots in the product, however, and I found a pretty significant bug (or is it a “feature”?) in the radio section. There’s a lot to cover, so let’s get started…
Basic Features
The G54 retains Buffalo’s distinctive vertical ovoid cylinder styling of the previous members of the AirStation product line and stands about 7in. high, 6 in. deep, and 2 in. wide. Indicator LEDs are located on both the front panel (Power, WAN Link/Activity, Wireless Activity, and Diag) and one of the sides (Link/Activity for each of the four LAN ports, and a duplicated Diag). I don’t care for this arrangement, because it makes it difficult to see all the LEDs at once,but it seems to be what Buffalo has settled on for the AirStation line. Note that the G54 has no wall-mounting features.
The rear panel holds the four 10/100 auto MDI / MDI-X LAN ports, which willl figure out how to connect to whatever you plug in, and whether you use a Normal or Crossover cable. (This also means that any port can be used as either a normal or “Uplink” port.) There’s also a 10/100 WAN port, power connector, Reset-to-Factory-Defaults Init switch, and an external antenna connector hidden behind a little flip-up cover.
It’s interesting to note that the WAN port is also auto MDI / MDI-X, and can have its speed and mode set via the Admin interface. The external antenna connector is the custom “Lucent” type found on both Buffalo and ORiNOCO’s 802.11b client cards, and Buffalo offers both Indoor and Outdoor antennas in case you need a little range extension. Buffalo includes a normal UTP cable, printed Quick Setup poster, and AirNavigator CD with the 54G.
A Peek Inside
Given all the brouhaha created by Broadcom during last month’s Comdex, I don’t think I’ll be giving away any trade secrets by telling you what makes up the innards of the WBRG54. As expected, it’s pretty much an all-Broadcom implementation, but manufactured by Buffalo.
The heart is a Broadcom BCM4702 Wireless Network Processor coupled with a Broadcom BCM5325 5 port switch. The processor is a pretty zippy little number and has plenty of power for the G54’s needs as you’ll see later. It’s also used in Linksys’ WAP51AB Dual-Band Access Point [reviewed here], and I’d wouldn’t be surprised to see it at the heart of Linksys’ “54G” efforts, the WAP54G Access Point and WRT54G Wireless Router.
The radio is a Broadcom BCM94306MP, which is their OEM reference design in mini-PCI format. The radio connects to a small PC board that runs front-to-back at the top of the cabinet and contains a dual-dipole diversity antenna assembly. This arrangement puts the antennas in a fixed, horizontally polarized orientation, with the external antenna jack connected in parallel with the antenna closest to the rear panel.
Setup
Buffalo ships an AirNavigator CD that contains a number of Windows-based applications, drivers for their client cards, and documentation for their products. Since the printed Quick Setup Guide poster included with the router suggested running the AirNavigator setup wizard, I dutifully did. Everything seemed to be going peachy until the process ended with a window from the AirNavigator that “Congratulations! Setup is complete”, but an Internet Explorer window that was unsuccessfully trying to reach http://0.0.0.0/cgi-bin/index.cgi.
At that point, I put aside the Quick Setup Guide since my client machine that was Ethernet connected and running XP Home told me that my Ethernet connection was up and running. I just opened the Network Connection Status window, clicked on the Support tab and saw that I had leased a 192.168.11.X address. That meant that I should be able to connect to the router admin screen at 192.168.11.1.
But I also noticed that an Internet Connection Status icon had appeared in my System (Tray) Notification area, which told me that the G54 was UPnP-enabled. So I decided to how Buffalo had done with their UPnP implementation. I opened My Network Places, found an icon for Buffalo WBR Series, double clicked on it, entered the login info (conveniently found in the Quick Setup Guide) and was greeted with the Top level screen shown in Figure 1.
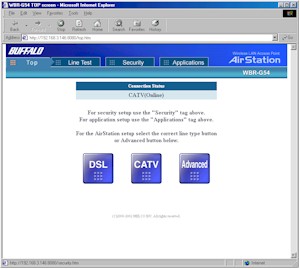
Figure 1: Top screen
Tip: As you can see, you don’t really need to run a Windows machine to setup the AirStation, and I recommend you do your router setup from a wired client, not a wireless client as Buffalo suggests. Even if you are not running WinXP as your OS, just make sure your client machine is set to an IP address from 192.168.11.2 to 192.168.11.254, subnet mask 255.255.255.0 and point your web browser to 192.168.11.1.
NOTE: The G54 ships with a default username, but no password. Make sure you set a password, especially if you enable Remote Administration.
Since I started out via UPnP, I did a quick check to see if UPnP NAT Traversal was working by firing up Windows Messenger. I then opened the Internet Connection Properties, clicked on the Settings button and verified that Messenger had successfully opened ports as shown in Figure 2.
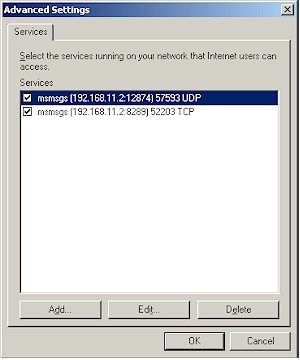
Figure 2: MS Messenger ports opened via UPnP
NOTE: The ports that Messenger opens on your machine may be different and that’s OK.
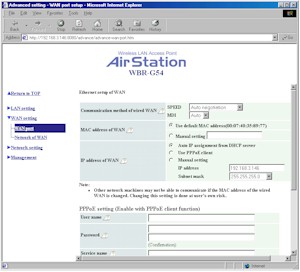
Going back to the screen in Figure 1, the “DSL” and “CATV” buttons launch auto-setup sequences that attempt to get the router WAN connection and local DHCP server set up and running. I didn’t spend much time with them, since I don’t have access to either type of connection. Instead, I clicked on the “Advanced” button and went right to the WAN Port screen shown in Figure 3.
Figure 3: WAN Port settings
(click on the image for a full-sized view)
The G54 handles all the main WAN authentication types, although you have to go to the “Network of WAN” page to fill in Host Name or DNS server entries if your ISP’s authentication scheme requires them. That screen also is where you can control whether the router will respond to WAN pings (disabled by default) and set a port number for remote administration. Note that as soon as you enter the port number, Remote administration is enabled, with no ability to limit access to a particular IP address or range of addresses. If you enable Remote Admin, make sure you set an administration password (found on the Management > Unit Information screen), since no password is set by default.
The G54 allows multiple administrator logins at a time and doesn’t provide any warning when a second administrator logs in. There’s also no way to log out of the admin interface, other than quitting your browser.
In general, I think that Buffalo has some work to do on the Admin Interface if they want to reach the mainstream consumer. A survey of the admin interfaces of the major consumer network product manufacturers should provide better screen organization models to emulate.
One plus that Buffalo has is their on-line Help. Virtually each setting has a little “help balloon” that you can click on and get reasonably useful information from. However, there is definitely a need to have a native English speaker review and re-write some of the screens, since I ran into at least a few instances where the wording was misleading or inaccurate.
My other major complaint is that you must endure a 10 second mini-reboot for changes in each section of each Admin page. This was very frustrating, not to mention time-consuming, when I was testing out the NAT Table (port forwarding) features of the firewall, which I’ll cover next.
Firewall
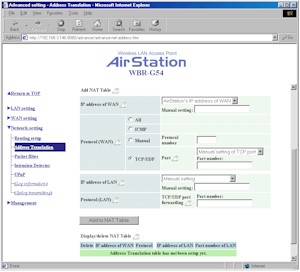
Buffalo says that the G54 has a NAT-based firewall, but given its “Intrusion Detection” function, I think there’s at least a little Stateful Packet Inspection (SPI) mixed in. The firewall features are found under the “Network Setting” link, and I’ll start with the Address Translation page shown in Figure 4.
Figure 4: Address Translation settings
(click on the image for a full-sized view)
The screenshot actually shows the lower half of the page and doesn’t include the DMZ and Address Translation Enable settings. Yup, that’s right, you can shut off the NAT function and use the G54 as a normal LAN-LAN router, including the ability to handle RIP1 and 2 dynamic routing protocols and set static routes via the Routing setting screen.
If you’re like me, you’ll have to stare at this screen for awhile and do some experimenting to figure out how to map ports, due to the many options not normally found in port forwarding interfaces. You’ll also bump into some not-so-helpful error messages if you do something wrong, which again, could use some translation help.
I eventually figured things out, though, and once programmed, the port forwarding seemed to work fine. Note that you can’t edit or temporarily disable port mappings, and “loopback” is not supported for forwarded ports.
Tip: If you’re forwarding port ranges, don’t enter any port numbers in the Protocol LAN box, and just enter the IP address of the computer that you want the ports to be forwarded to. Otherwise you’ll get an error.
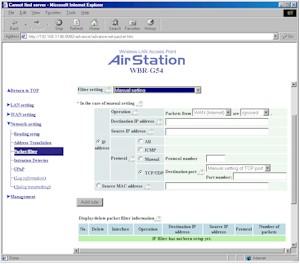
The main part of the Packet Filter (access control) screen is shown in Figure 5. Also on the page, but not shown in the screenshot is a checkbox that controls whether packet filtering actions are logged and an area at the bottom of the page that displays and allows deleting (but not editing or disabling) of programmed filters.
Figure 5: Packet filter screen
(click on the image for a full-sized view)
Filters that prevent IDENT requests and Microsoft Networking broadcast packets come programmed by default. Note that you can reject all Internet access for LAN machines by entering each one’s MAC address in the Source MAC address box.
Two things that are missing from the G54’s firewall features are scheduled port mappings and packet filtering and content filtering of any sort. So if you need to open ports or control access during specific times, or want to be able to control which websites your LAN users visit, the router won’t help you.
VPN
The VPN features of the G54 are very basic. You get support for only one PPTP or IPsec pass through client each, and the router can handle port forwarding for one PPTP or IPsec LAN-based server.
Logging and Other Features
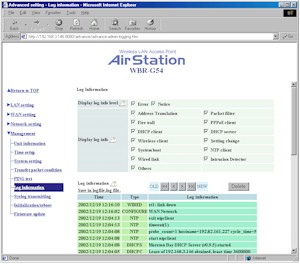
The G54 has many logging features, including support for logging to a syslog daemon. But, like many other products, it doesn’t log normal web or other Internet access traffic.
Figure 6: Logging setup screen
(click on the image for a full-sized view)
Figure 6 shows what the G54 does log, which is quite extensive. The lower part of the page shows part of the 10 pages of log info that can be viewed via the admin interface. A nice touch is the ability to click on the Save in logfile.log file link to save the logfile right to your local machine. The Syslog transmitting page provides basically the same set of checkboxes to control what it sent to the syslog stream, and includes a syslog enable button and entry box for the IP address of the computer that’s running the syslog server/daemon.
Although it’s located in the Network setting section, I tend to think of the Intrusion Detector as another of the G54’s logging features. Its job is to “Watch for and prevent unauthorized access from WAN side devices” according to its help balloon. The Intrusion Detector Information ballon says that the following “attacks” are detected: Incorrect packets; TCP SYN FLOOD attack; Port scan; SMURF attack; IP SPOOFING attack; LAND attack; UDP port loopback attack.
But I port-scanned the crap out of it an never got a peep out of the detector. A check with Buffalo revealed that port scans really are not on the detector’s list (mainly because they’re so common that they produce a “cry wolf” effect) and they’ll be correcting the help file in an upcoming firmware update. If you do get attacked, the router can either email you an alert, or pop-up a screen on a wireless client that’s running Buffalo’s client application to alert you.
To wrap up the feature review, I’ll just list some of the other miscellaneous functions that the G54 has:
- Can set its internal clock from an NTP server. But this is disabled by default and requires that you input the URL or IP address of an NTP server (you can find a list of NTP servers here)
- Receive / Transmit packet statistics for WAN, LAN and Wireless interfaces
- Built-in ping utility
- Ability to reboot the router or reset it to factory defaults via the admin interface
An interesting feature omission, however, is the ability to save / load the router’s configuration to / from a file.
Routing Performance
Testing Notes:
• WAN to LAN tests are all run with LAN endpoint in DMZ
• LAN to WAN tests are run with LAN endpoint not in DMZ, except UDP Stream
The numbers in the chart pretty much tell the story. The Broadcom processor provides plenty of routing power. Especially impressive is the fact that the UDP streaming results show no degradation in speed and no packet loss.
I also ran 10 second IxChariot tests in both directions which looked pretty good and are shown in Figure 7.

Figure 7: Routing throughput
(click on the image for a full-sized view)
Routing Performance Test Results
| Test Description | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
|---|---|---|---|---|
| Throughput (kbps) | Lost data (%) | |||
| WAN – LAN | 20.4 | 1 (avg) 2 (max) |
499 | 0 |
| LAN – WAN | 22.6 | 1 (avg) 2 (max) |
499 | 0 |
| Firmware Version | 1.10 (1.14) | |||
See details of how we test.
Wireless Features
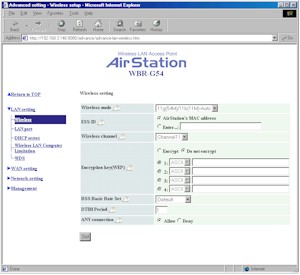
Most of the G54’s wireless setup is accessed through the LAN Setting > Wireless page shown in Figure 8.
Figure 8: Wireless setup
(click on the image for a full-sized view)
Most of the settings are pretty standard stuff, with the exception of the Wireless Mode and BSS Basic Rate Set parameters.The Wireless Mode lets you choose between 11g(54M)/11b(11M)-Auto and 11g(54M)-Turbo modes, but does not include an 11b-only mode. The BSS Basic Rate Set choices are explained this way in the setting’s help balloon:
- Default –
Communicate by 1, 2, 5.5 or 11Mbps. In the case of 11g(54M)-Only, the rate is 6, 12 or 24Mbps.
- Default(11b)
communicate by 1 or 2Mbps. - All –
Communicate 1, 2, 5.5, 6, 11, 12, 18, 24, 36, 48, or 54Mbps.
For my testing, I just left this setting at Default and the Wireless Mode in the Auto setting and didn’t have any trouble communicating with the router with either the Buffalo WLI-CB-G54 Draft-802.11g card or the 802.11b cards I tried. From my conversations with Buffalo, however, I suspect that these settings may evolve and include an 11b only mode in addition to the above choices.
I should mention that there are only 64 and 128 bit WEP settings available. You can enter the keys as either ASCII text or Hexadecimal strings, but you need to enter the proper number of characters for the WEP mode you desire (the lengths are described in the on-line help). The keys are also not stored in cleartext and can’t be saved to a file, so you better write down your key so that it can be properly entered in your client machines.
By the way, kudos to Buffalo for including the Deny Any setting, which I think should be standard on all Access Points. I also think that the ability to block (E)SSID broadcast should be standard, but it’s not included in the G54.
The other wireless security feature that the G54 does have is MAC Address-based association control for wireless clients (called Wireless LAN Computer Limitation). This feature lets you control the wireless clients that can associate (or connect) to the router by entering MAC addresses manually, or picking from a list of presently-associated MAC addresses. I would have liked to see the ability to create both a deny and allow list, and the ability to read and save the MAC address list from / to a file, however.
There are some missing items, however, such as the ability to monitor in-range wireless clients and various status info such as mode, WEP status, MAC address, etc. If the wireless clients are set to be DHCP clients, you’ll be able to see them in the listing on the LAN Setting > DHCP server page, but there’s no indication of which clients are wireless.
I also didn’t see the ability to shut off the radio, or limit its transmit power. The first is handy for situations where you just want to limit the router to wired operation for security reasons, such as when you leave it for the day. The second is a feature that has been offered on 802.11a equipment to allow control of an AP’s “cell” or zone size in multiple Access Point installations. I mention it mainly because I saw it in the Buffalo Client card’s Advanced Properties and saw no sign of it in the router’s wireless interface.
A Pleasant Surprise
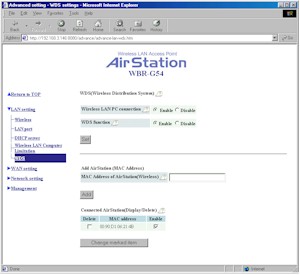
Clicking on the LAN Setting > WDS link brings up the settings shown in Figure 9, which control the G54’s wireless repeating capability.
Figure 9: WDS settings
(click on the image for a full-sized view)
I didn’t get to try this, since Buffalo sent me only one WBR-G54, and they said that their WDS (Wireless Distribution System) implementation is incompatible with the WDS feature on their Agere Systems (Lucent) 802.11b based products.
But it appears from the interface that you can set two (or more) G54’s so that they repeat (allow clients to connect and also connect wirelessly to each other), or just form a wireless bridge (i.e. with no clients allowed to connect). This will have to be an experiment left for another time, unfortunately!
And now, what you’ve really been waiting for… the wireless performance results!
Wireless Performance
NOTES:
• “Signal Quality” readings are actually the Buffalo Tech Client Manager “Condition” readings
• Testing was done with a Buffalo Tech WLI-CB-G54 Cardbus client card in a WinXP Home Dell Inspiron 4100 laptop
Since the WBR-G54 is a first-of-kind product to the SNB test bench, and since Broadcom is trying to set a de-facto standard with their “54g” draft 802.11g implementation, I gave the product a pretty thorough going over. But before I get into the results, let me climb onto my soapbox for a little speech.
The 802.11g standard has not yet been approved, but is expected to be in the April-May 2003 timeframe. Broadcom – the maker of the chipset in the Buffalo Tech and Linksys 11g products – is making an aggressive bid to gain market share in the wireless networking market with the early introduction of wireless networking products based on the draft 802.11g standard. By doing so, Broadcom hopes to get the “first mover” market share advantage and make up for the time (and money) lost by not having participated in the previous 802.11b explosion.
Anyone who buys a draft 802.11g product should be prepared to deal with not only the usual “early adopter” bugs, but also recognize that this technology is a work in progress. You are going to pay for the privilege of helping Broadcom debug their chipset, firmware, and drivers, and also come up the learning curve on wireless networking in general.
However, you won’t be working directly with Broadcom, but with whichever vendor you purchase your product from. The interesting thing to watch (and perhaps an important factor in your purchase decision) will be how Buffalo Tech and Linksys each handle the tech support burden that they are taking on. There are pros and cons for both companies, but in the end, it will come down to which one delivers superior support. I hope you use the SmallNetBuilder Opinion feature to share your experiences with others.
Follow the Bouncing Throughput…
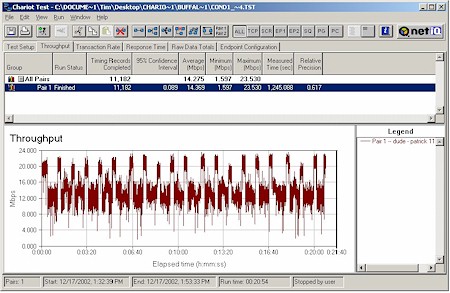
That being said, let’s turn to the first issue that I found. While I was running some of my early tests, I kept seeing a noticeable difference in maximum throughput. At first I thought it was due to some of the interference tests that I was running, but then I decided to do a special test. I made sure that the only wireless equipment powered up was the WBR-G54 and Buffalo WLI-CB-G54 client. I then ran the NetIQ Chariot throughput.scr script for about 20 minutes, modifying only the file_size parameter to use a 200,000 Byte file size, instead of the default 100,000 Bytes for each transfer. Figure 10 shows the result.
Figure 10: Long throughput test
(click on the image for a full-sized view)
This proved that I wasn’t imagining the max throughput difference, and further showed a definite cyclical pattern. A similar pattern can also be seen with a cycle time of somewhere between 30 and 60 seconds. So Issue #1 is that there is work needed, probably in the transmit-rate auto ranging routine. When I presented my findings to Buffalo Tech, they confirmed the issue, and a few days later sent the plot shown in Figure 11.
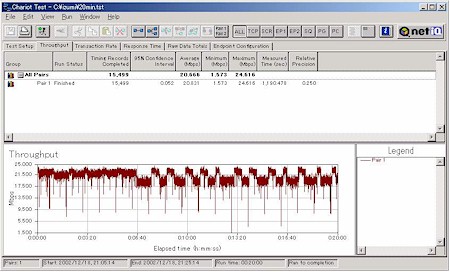
Figure 11: Long throughput test – new firmware
(click on the image for a full-sized view)
The plot was generated with tweaked, unreleased firmware and although still shows a cyclical throughput variation, the variation has been reduced. So Buffalo (and presumably Broadcom) is on the problem, and says they’ll be issuing a firmware update in mid-January. However, all the following results should be viewed with this issue in mind, because it can be seen in pretty much every test.
“Dual-ing” Standards
The next thing I did was see how the router handled simultaneous normal 802.11b and draft 11g traffic. Again using Chariot, I set up a test using two client pairs. The reference draft 802.11g test pair for each test was a WinXP Home Dell Laptop with BuffaloTech WLI-CB-G54 Cardbus card to Win98SE Ethernet client. The second pair used a WinXP Home Compaq Laptop with various 802.11b cards to a Win98SE Ethernet client.
In an attempt to hit the major chipset types, I tested the following cards:
- NETGEAR MA401 (Original Intersil PRISM II based card)
- ORiNOCO Gold (Agere Systems chipset)
- D-Link DWL-650+ (TI ACX100 chipset)
- NETGEAR WAB501 (Atheros 5100X dual-band chipset)
![]() Testing Notes:
Testing Notes:
- Two separate Ethernet client machines were used to avoid overloading any single CPU,
- All clients were on the LAN side of the router, so the routing portion of the product is not involved in the test.
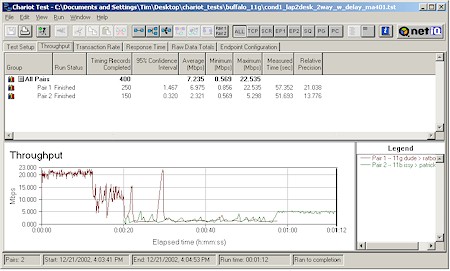
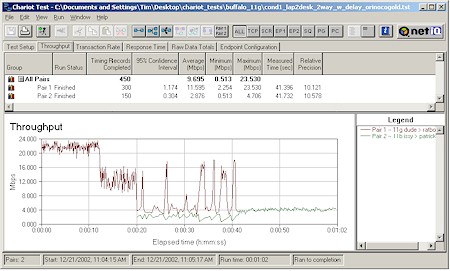
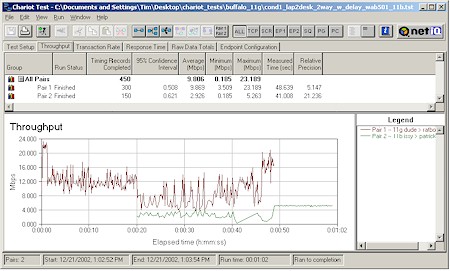
In each test, I started the BuffaloTech card first, then kicked in the 802.11b card. Both cards then run simultaneously for awhile, then the BuffaloTech card stops and lets the 11b card finish by itself. As you can see from the plots below, all 11b cards performed similarly.
Figure 12: Two pair test – NETGEAR MA401
(click on the image for a full-sized view)
Figure 13: Two pair test – ORiNOCO Gold
(click on the image for a full-sized view)
Figure 14: Two pair test – D-Link DWL-650+
(click on the image for a full-sized view)
Figure 15: Two pair test – NETGEAR WAB501
(click on the image for a full-sized view)
Remember that the variation in the BuffaloTech card when it’s running by itself is a known issue, and not due to any effect from the 802.11b card. The one card that seemed to be a little more 11g-friendly was the NETGEAR Atheros-based card. Figure 15 seems to show that the BuffaloTech card was able to achieve a higher average throughput when running simultaneously, but it could just be my imagination!
The 11b testing confirms what I was told during my Comdex meetings, i.e. that as soon as an 802.11b client starts sending data through an 802.11g Access Point, all the 802.11g throughput advantage is lost. The good news that the plots also show is that as long as the 11b client isn’t sending data, the 11g stations will communicate at the higher rate, i.e. the association of an 802.11b client with an AP doesn’t do any throughput harm.
“Dual-ing” Standards, continued
Of course, if you’re running more than one 11g card, you’d expect them to share the available bandwidth nicely. The Chariot plot in Figure 16 essentially confirms this.
Figure 16: Two pair test – Two Buffalo Tech WLI-CB-G54
(click on the image for a full-sized view)
This plot just happened to do the sharing during the downward throughput hop. It’s interesting to note that whatever the mechanism is that’s causing the hopping throughput, it didn’t cut the throughput yet again in half when the second draft-11g client kicked in.
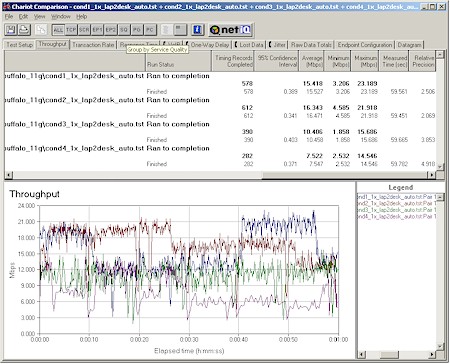
I, of course, ran my usual four-location throughput test, the results of which are shown in the chart at the top of this section. I also did Chariot runs, which are shown in Figure 17.
Figure 17: Four condition throughput
(click on the image for a full-sized view)
The hopping throughput problem makes the plots not very useful, but I included the screenshot so that you can see the Max, Avg, and Min throughput numbers for each run.
I also ran tests with 128bit WEP enabled, and didn’t see any throughput degradation, at least none that I could separate out from the normally varying throughput.
Finally, I tried running some Turbo-mode tests, but couldn’t find a Turbo setting in the Buffalo Client application. After some back-and-forth, Buffalo told me that Turbo mode is presently implemented in the AP (router) side only. The client is supposed to auto-detect the Access Point’s mode, and adjust itself accordingly.
After following Buffalo’s instructions and setting the router into Turbo mode, I did a Chariot run and found that, once again, I couldn’t accurately see any Turbo effect due to the normal throughput variation. So the question of how much boost Turbo mode gives you, and whether it lowers effective throughput under weaker signal conditions as 802.11a’s Turbo does, will have to wait for a future firmware release.
802.11g Wireless Performance Test Results
| Test Conditions
– WEP encryption: DISABLED |
Firmware/Driver Versions
AP f/w: |
||||
|---|---|---|---|---|---|
| Test Description | Signal Quality (%) | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
| Throughput (kbps) | Lost data (%) | ||||
| Client to AP – Condition 1 | 100 | 15.5 [No WEP] 15.9 [w/ WEP] |
1 (avg) 1 (max) |
499 | 0 |
| Client to AP – Condition 2 | 75 | 16.5 | 1 (avg) 1 (max) |
499 | 0 |
| Client to AP – Condition 3 | 30 | 10.5 | 1 (avg) 1 (max) |
499 | 0 |
| Client to AP – Condition 4 | 45 | 6.9 | 1 (avg) 2 (max) |
497 | 0 |
See details of how we test.
Adding it all up
So what does all of this mean? Should you buy or not? Here are my take-aways from my first 802.11g experience:
-
802.11g is a pretty impressive technical feat, and is currently capable of producing maximum usable throughput of around 20Mbps. But it appears that this first implementation has a “throughput hopping” “feature”, that cyclically moves the maximum throughput down to 12Mbps – a 40% drop. I suspect that this “feature” will be common to all Broadcom-based products, but since I haven’t yet seen the Linksys products, I can’t say for sure.
-
The first bullet reinforces my point that there will be a number of firmware releases between now and a stable, standards-compatible product. Anyone buying now should be prepared to deal with debugging and performing multiple firmware upgrades.
- Although there is no guarantee that any draft 802.11g product will conform to the 802.11g spec when it is finally released toward the beginning of Q2 2003, it’s a reasonably sure bet that you won’t end up having to junk your draft-11g products and buy new stuff when the standard is released. But I’d like to see draft-11g manufacturers provide the missing guarantee, so that consumers don’t get stuck holding products that don’t work, come mid 2003.
Update 1/3/2003 – I guess someone at Buffalo was listening. Shortly after this review, BuffaloTech stepped up to the plate and added this statement at the bottom of their webpages for the WBR-G54 and WLI-CB-G54:
-
NOTE TO OUR CUSTOMERS:
As you may know, IEEE802.11g is slated to be certified by the Wi-Fi Alliance in mid 2003. We understand this could affect current 802.11g technology. We are dedicated to ensuring that our customers have the most current and reliable products available on the market today. If the certification materially changes the principal operating features of our pre-standard 802.11g products, we will replace or upgrade any of those products at no charge and provide toll-free technical support. We thank you for your loyalty and confidence in our products. - Although Buffalo Tech isn’t as well-known as the more popular consumer-networking companies, they’re not newbies to the industry. They are actually a subsidiary of Melco, Inc, a $650M Japanese manufacturer of memory, storage, and networking products, and one of the first companies to introduce a consumer-priced 802.11b Access Point a few years ago when the whole consumer 802.11b industry started to take off. But with a narrower distribution, and low brand-recognition, they’ll have their work cut out for them.
If it were my money, I’d wait a month or so (Jan 2003) and let someone else find the other bugs and give Broadcom some time to get rid of their throughput-hopping “feature”.