Introduction
| At a Glance | |
|---|---|
| Product | NETGEAR ProSafe SSL VPN Concentrator (SSL312) |
| Summary | “Price-busting” SSL VPN appliance (based on ActiveX controls) |
| Pros | – Easy to install and set up – Requires only one port exposed to the internet (https TCP port 443) – Supports up to 25 simultaneous users – Provides a true network connection like a traditional IPsec client – Can be purchased for under $400 |
| Cons | – Requires Internet Explorer for many of its features |
In a previous article, I wrote about a software-based open-source SSL VPN solution called SSL-Explorer, which can turn a PC on your network into a very nice full-featured VPN gateway. This time we will take a look at the ProSafe SSL VPN Concentrator 25 SSL312, a newly-available hardware-based remote access SSL VPN solution from the folks at Netgear. Figure 1 below shows the front of the device where the Ethernet ports, power light, test light, and LEDs are located.

Figure 1: Netgear SSL312
As I began to work with the SSL312, I thought to myself, “Is it really possible that Netgear could offer an enterprise-quality SSL VPN for under $400? An enterprise-quality SSL VPN such as the Juniper Netscreen SA700 costs roughly $1500.” To see what the SSL312 has to offer us, let’s dive in and take a closer look.
The key features of the SSL312 are:
- Hardware support of up to 25 simultaneous VPN tunnels
- No concurrent user restrictions
- Ability to browse Windows file systems using VPN portal
- WebCIFS, Telnet, FTP, SSH, WebFTP access support
- Built-in database, MS Active Directory, LDAP, and RADIUS authentication support
- Remote access of desktop using Terminal Services and VNC
- Access using zero-footprint VPN client (ActiveX control)
- Automatic cache cleanup after session termination support (ActiveX control)
- Port forwarding support (ActiveX control)
- Session inactivity timeouts
A web browser that supports Microsoft ActiveX (i.e. Internet Explorer) is required since much of the tunneling/port forwarding features of the SSL312 are based on ActiveX components. Netgear recommends using Internet Explorer 6.5.1 or above. I should mention that because the ActiveX controls aren’t used in the web management interface for configuring the SSL312, you can use other web browsers such as Mozilla Firefox to set up the SSL312. It is also important to note that Netgear is working diligently to convert the ActiveX components over to pure JAVA so that any modern browser that supports JAVA may be used.
A Quick Peek Inside
The SSL312 is built on a 200MHz Cavium NITROX Soho CN22X MIPS32 CPU. The VPN acceleration capabilities of the Cavium chip come in handy since 256-bit AES encryption is used to secure the connection to the SSL312. The specifications table on the Cavium Web site shows that the 200MHz Cavium NITROX Soho CN22X MIPS32 CPU is capable of about 20Mbps of SSL VPN throughput.
Our own throughput tests using the Qcheck reported a little over 6Mbps of throughput (both up and down) through an active VPN tunnel. The SSL312 also provided 16MB of FLASH memory and 128MB of SDRAM. Using port scanning tools on the unit, I discovered that the device runs Linux for an OS. According to Netgear, the hardware combination enables it to simultaneously support up to 25 user VPN tunnels. I, like many of my geeky friends, want to know what makes this kind of equipment tick; so, let’s open it up, and take a quick peek inside.
Figure 2 shows the SSL312 with the cover opened.
Figure 3 shows its system board in greater detail. You can see the Cavium CPU (large chip in the middle with a heat sink on it), the FLASH/SDRAM chips, the Ethernet controllers, and various other components.
Installation/Configuration
I was very impressed with how quick and easy it was to configure the SSL312. It only took about 15-20 minutes to get everything plugged in and to set a few basic network/VPN configuration parameters before I was ready to start using it. First, I took the SSL312 out of its box. I connected the AC power cord to the unit and plugged it to a power outlet. Then, I plugged the network cable into Ethernet Port 1 on the front of the SSL312. I plugged the other end of the network cable into the Ethernet port of my PC. I turned on my PC, and turned the power switch on the back of the SSL312 to On.
In order to access the SSL312 and change its settings, you must configure your PC with an IP address so that it is on the same subnet as the unit. Since the SSL312 comes “out-of-box” with a default IP address of 192.168.1.1, Netgear recommends setting up a PC that is already on your network with an IP address of 192.168.1.10 and a subnet mask of 255.255.255.0.
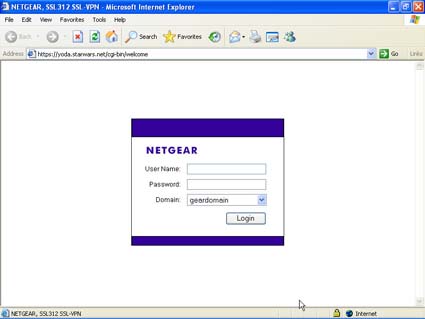
Once your PC is configured on the same network as the SSL312, open a browser and type the URL, https://192.168.1.1, into the address field. If you were successful in connecting the SSL312 to your PC, a login screen appears. Refer to Figure 4.
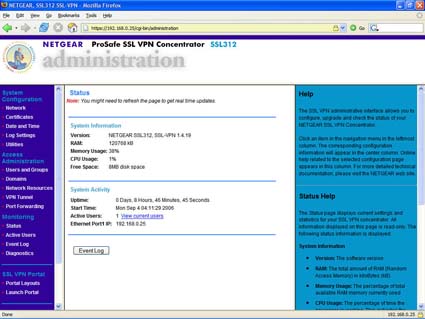
Enter admin for the user name and password for the password. An administrator account with a default user name and password was configured for the SSL312 at the factory. NOTE: Remember to change the password to one that is more secure before connecting to the internet. If it isn’t selected, choose geardomain for the Domain. Once you are successfully logged in, you will be presented with a status screen (Figure 5).
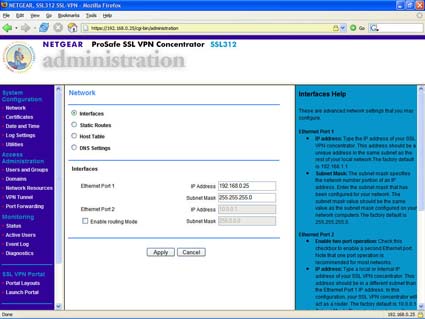
To start configuring the network settings, click the Network link underneath the System Configuration heading. When the Network screen appears, select Interfaces.
Installation/Configuration – more
Now, change the SSL312’s IP address to an open IP address on your local network and set the subnet mask so that the device is added to your existing home network. To do this, enter the open IP address in the IP Address field and the subnet mask in the Subnet Mask field in the Ethernet Port 1 area under the Interfaces section. Refer to Figure 6. For my device, I changed the IP address to 192.168.0.25 and set the subnet mask to 255.255.255.0.
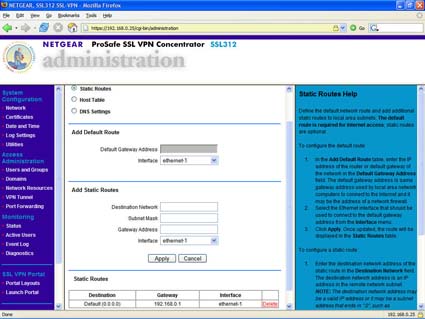
To define the default network route, select Static Routes. In the Default Gateway Address field, enter the gateway address used by your local network to access the internet. Refer to Figure 7. For my device, I entered the default gateway as 192.168.0.1.
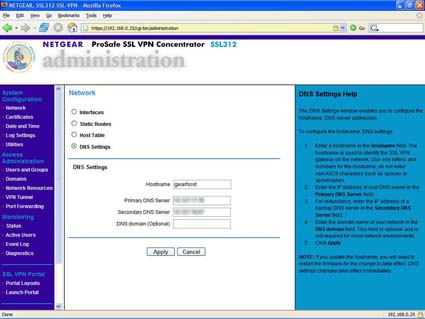
To configure the DNS server addresses, select DNS Settings. In the Network screen, enter the IP addresses of the primary and secondary DNS servers in the appropriate fields. Refer to Figure 8.
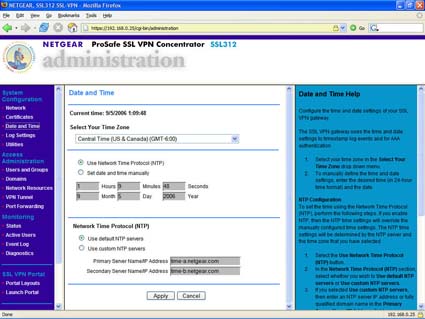
To set the time zone, date, and time, click the Date and Time link underneath the System Configuration heading. It is important that the time and date are correct since they will appear in the log files. When the Date and Time screen appears, select your time zone. Refer to Figure 9. Then, click Use Network Time Protocol (NTP) to ensure that the device uses the NTP server and the time zone you selected to set the time and date; thereby, overriding any manual time setting configurations.
Installation/Configuration – more
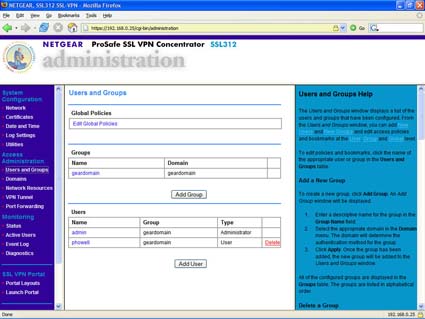
Now we’re ready to add a user to the SSL312. Click the Users and Groups link underneath the Access Administration heading. In the Users and Groups screen, click Add User. Refer to Figure 10. Fill in the information for any new users you may want to add at this point. You will use one of the user accounts to login in to the VPN portal later.
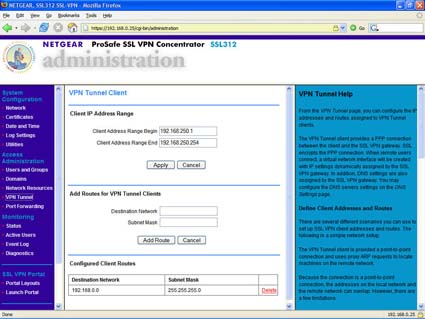
To specify how the SSL312 connects to the network, click the VPN Tunnel link underneath the Access Administration heading. The VPN Tunnel Client screen appears.
Notice the client address range start and client address range end. Those addresses represent the pool of addresses that will be available for assignment for the PPP connection that are made when we start the VPN tunnel. The range of numbers must not overlap with the network that we wish to connect to.
For example, if our network starts at 192.168.1.1, we would need to choose another unused subnet like 192.168.250.1 – 192.168.250.254. We will also need to add the route for the VPN tunnel client. Refer to Figure 11, which shows that I added the 192.168.0.x network so that the 192.168.250.x network could communicate with it.
VERY IMPORTANT: You will also need a static route set up in the firewall/router for the 192.168.250.x network (or the client network range you have configured) that points to the IP address of the SSL312. In my case, I needed a static route set up in such a way that any 192.168.250.x traffic is routed to the SSL312 gateway at 192.168.0.25. Without the static route back to the SSL312 from our firewall/router, packets may become lost and cause the VPN tunnel not to work correctly.
Also, be sure and take the time to confirm that port 443 (HTTPS) can be reached externally from the internet to the SSL312. Most firewalls/routers will need a rule set up to allow traffic from the outside (i.e. internet) to come inside the network to the SSL312. The procedure for doing this varies greatly depending on the kind of firewall/router and the design of your network. Save yourself some headaches and frustration by taking the time now to ensure that this level of connectivity is functioning correctly.
In Use – VPN Tunnel
Okay, let’s open a browser on a remote PC and take a look at the VPN portal. From a remote PC, open a browser window using Internet Explorer and enter the portal URL we recorded from the Portal Layout page: https://192.168.0.25/portal/SSL-VPN.
If all goes well, you are presented with a login page similar to the one below.
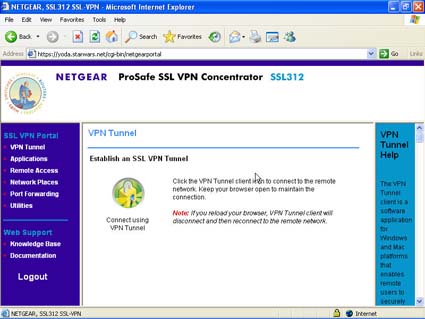
Login with the new user you created using the User and Groups screen earlier. After logging in, the VPN Tunnel screen appears. Refer to Figure 13 below.
The VPN Tunnel screen or “portal” represents the starting point for any users logging into the SSL312. Click the lock graphic to establish a VPN tunnel. NOTE: Be sure and install any ActiveX components that you were asked to install or the connection will not work. Once the connection is established, a new unfamiliar icon appears in your system tray. If you double-click the icon, a VPN Tunnel Connection Status window appears, showing the connection details for your VPN tunnel connection.
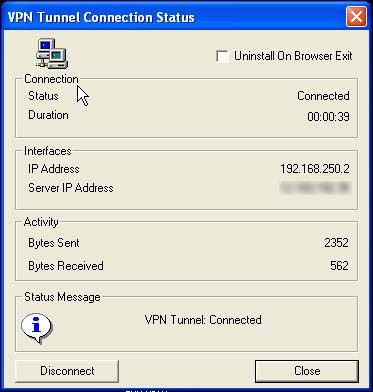
Figure 14: SSL312 – ActiveX Control – VPN Tunnel
I normally run TightVNC on all my machines to make them easy to control when I’m out of town on business. So naturally one of the very first tests I wanted to try was to see how well the SSL312 VPN tunnel handled my remote desktop tasks using VNC. I was pleasantly surprised that the VPN tunnel was rock solid. I didn’t experience any problems remotely controlling my PCs. Performance was on par with what I normally receive without a VPN connection. In fact, it was hard to tell that I was running over a VPN at all since it felt more like a direct connection.
I’ve used TightVNC on various IPsec clients from the “big guys” (Cisco, Juniper, Sonicwall, and Checkpoint) and while all have improved since their early incarnations, I still occasionally run into small issues such as losing my internet access while using an application over the tunnel or not being able to connect at all from a hotel because of network address translation (NAT) traversal issues.
In Use – VPN Tunnel – more
Another annoyance that many IPsec clients seem to suffer from is the fact that they make such radical changes to your networking settings that often times if you have the need to connect to different facilities that use different IPsec clients, you will find that you must uninstall one client before you can use another. Put simply, they seem to have real trouble coexisting on your PC.
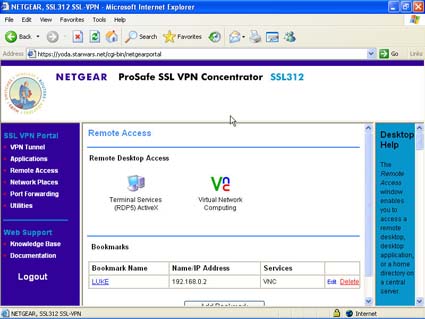
Fortunately, the SSL312 does not inherit any of these annoying traits. As I stated previously, the connection was very smooth and unobtrusive. Although I chose to use my TightVNC client on my desktop PC over the VPN tunnel, the SSL312 offers a built-in VNC client on the main portal page, which appears when you login. It works just as well. This built-in client can be handy as you can set up a couple of bookmarks so that users can make quick-and-easy connections to various boxes without having to deal with a VNC client application or without knowing the connection specifics of a particular machine.
For those who have Windows 2000 Server, 2003 Server or XP Pro boxes (The Windows XP Home does not support RDP connections itself although you can RDP into other Windows boxes which do support RDP) in their networks, the SSL312 offers excellent support for Terminal Services and the Remote Desktop Protocol (RDP). RDP is a Microsoft proprietary protocol which allows for remote desktop control (much like VNC). Terminal Services allows a single machine to host individual remote desktop sessions, each with their own unique environment.
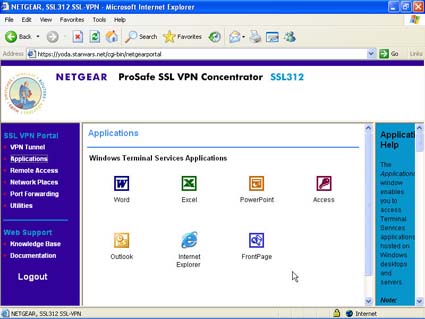
You can also host applications for users when you set up Terminal Services for application mode. Bookmarks to those applications can then be placed prominently on the SSL312 VPN portal page; thereby providing easy access to frequently-used applications for remote users. I did not have a Windows server with which I could thoroughly test the RDP functionality. However, you can consult the SSL312 resources section at the conclusion of this article to obtain documentation describing additional Terminal Services/RDP functionality and configuration. Figure 15 shows the Terminal Services Applications screen from the portal.
Figure 16 shows the Remote Access screen which has information on the built-in remote access clients (RDP and VNC).
Network Browsing, Port Forwarding
Next, I decided that I wanted to see how well the WebCIFS functionality, i.e. network browsing, worked over the VPN tunnel. I have a Linksys NSLU2 NAS on my network; so, I tried to connect to it through the tunnel. From the SSL VPN portal page you can click the Network Places link and start browsing your network domain for shares. I experienced very little trouble gaining access to my files. I could upload files, delete files, and create new folders. I uploaded several different files ranging in sizes from 250kb all the way up to 50MB.
One minor annoyance was that after an upload operation had completed, the SSL312 would take you back to the root of your share instead of leaving you in the directory to which you had just uploaded a file. One nice feature of the WebCIFS interface was the ability to create bookmarks. You can create bookmarks for any machine shares and have them show up at the machine level when you click Network Places instead of having to navigate down through layers of subdirectories.
All in all, the WebCIFS functionality worked very well. There were times when it seemed a bit slow in downloading and uploading operations, but I suspect that this may have been more of a reflection on my internet connection than the SSL312 itself. It would have been nice if the interface had a “progress bar” for uploads and downloads so that you could occasionally check the status of the file transfers and not worry about whether or not the transfers were successful. Figure 17 shows an example of the WebCIFS GUI.
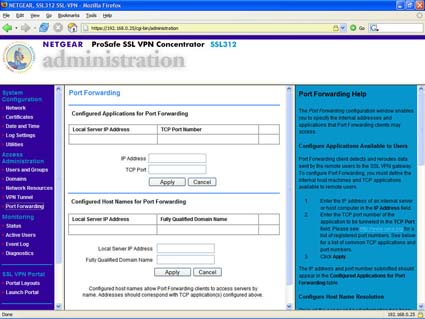
Another nice feature of the SSL312 is the ability to perform port forwarding. The port forwarding feature in the SSL312 only works with applications that use TCP connections. The functionality is currently implemented in the form of an ActiveX control much like the full VPN tunnel feature. According to Netgear, if you do not need a “full-blown” VPN tunnel and only want to forward TCP connections, you may want to consider the port forwarding functionality since it does not create as much overhead as a full tunnel connection.
I decided to use the port forwarding functionality to forward IMAP (TCP 143) connections from Mozilla Thunderbird to my Linux mail server and to forward MySQL (TCP 3306) database connections to my Linux database server. You configure the port forwarding selections that will be available for users from the management side of the SSL312. Refer to Figure 18.
In this manner, the users do not have the ability to arbitrarily forward anything. Users must select from the ones that the Administrator has set up and made available to them. Once you are logged into the portal, click the Port Forwarding link to load the ActiveX control and activate the port forwarding feature. It will place a small icon in your system tray. If you double-click the icon, a Port Forwarding window appears, which displays your current port forwarding details.
My testing with Mozilla Thunderbird and MySQL seemed to indicate that the SSL312 was handling the port forwarding duties seamlessly with flying colors. I was able to retrieve my mail and perform all other mail-oriented daily tasks without a single hiccup. I was also able to run several complicated queries on a large MySQL database without any issues. Databases in particular are generally very sensitive to network hiccups, especially when performing lengthy complicated transactions. Again, it all worked seamlessly.
One thing that I did wish existed was a way to grant “privileges” to specific users so that they are able to forward ports arbitrarily without having to have the SSL312 Administrator set up every scenario. This feature would give a little more flexibility to software developers who work remotely and are constantly working with servers and applications which run on a plethora of different ports. It’s possible that this can be accomplished by setting up Groups using the User and Groups feature, but I didn’t try it.
Other Notes
In addition to the basic functionality that we have described so far, there are some other options/settings available on the SSL312 that I want to take a minute to mention since they offer a variety of configuration options, utilities, and information on the status of the SSL312. In the management side of the SSL312 under the System Configuration link, you will find options that allow you to work with SSL certificates, to change logging settings, to back up your SSL312 configuration, and to upgrade the firmware.
The SSL312 comes with a default certificate already installed; however, you can import your own certificate should you have one. Syslog logging is also supported by the SSL312 for logging if you have a syslog server. You can also set up the SSL312 to email log files to you every so often based on criteria that you specify. Under the Access Administration link, you can administer users, groups, and domains. You can also configure global settings for the VPN tunnel and port forwarding functionality.
The SSL312 has quite a bit of policy control designed to help restrict the operations users can perform. This area is also where you would configure an Active Directory domain if you want to use it as your user authentication source. The Monitoring link allows you to check up on the current status of the SSL312, see the active users, and check the event log. You can also remotely reboot the SSL312 from this area if necessary. And finally, the SSL VPN Portal link allows you to control the layout of what functionality is available for users when they login. It also allows you to have some limited control over how the portal will look by allowing you to do things such as uploading a custom banner graphic for the portal.
So how does the SSL312 compare to a free SSL VPN implemented with SSL-Explorer? One of the things that I liked a little better in SSL-Explorer was the overall look and feel of the GUI. It did not feel as polished as the SSL-Explorer GUI. There were times when I felt that some of the terms used to describe the various settings might confuse users. Both the user portal and the management components were similar in this regard. The port forwarding features were very much like SSL-Explorer and it performed similarly.
However, the VPN tunnel feature does not exist in SSL-Explorer unless you buy their Enterprise version, or recently-announced $99 home/academic version. In SSL-Explorer, the VPN tunnel functionality is currently implemented by a small JAVA client. Netgear appears to be moving in the same direction in order to “open up” usage by other popular browsers that do not support Microsoft’s ActiveX technology. Another thing that is available in SSL-Explorer but that does not exist in the SSL312 is the ability to package custom applications (like TightVNC or WinSCP) for distribution through the VPN connection.
Closing Thoughts
The SSL312 has much in common, feature-for-feature, with many of its more expensive pedigreed brethren such as the Juniper Netscreen SA700 and the Cisco ASA 5500. The SA700 costs roughly $1500 and the 5500 can easily cost several thousand dollars depending on the configuration.
I did not find too many features that would make the other products stand out and justify their significant differences in price over the SSL312. The more expensive units do offer some interesting features such as failover redundancy and load balancing, but realistically speaking, those are some rather esoteric features that are only going to appeal to a select crowd.
Netgear has attempted to build a cost-effective plug-and-play device that would service a majority of the needs of the small business community. To that end goal, the SSL312 has more than succeeded. Similar devices from the big name networking firms can run into the thousands of dollars and configuring/maintaining them often requires a well-trained in-house IT staff or costly service contract. Quality business-class products at this price point have so far been nonexistent.
In fact, I believe that the Netgear SSL312 would feel right at home in the data centers of many larger businesses (usually the hallowed domain of big name networking firms only). Kudos to Netgear for providing such an economical feature-packed product. If you are looking for an easy-to-use, plug-and-play SSL VPN gateway for your small business or home network I would strongly suggest that you give some serious thought to the SSL312.
Other Resources
You can find additional information regarding the SSL312 on the Netgear website. A series of FAQs and other technical notes for the SSL312 can be found on the product’s support pages.