| At a Glance | |
|---|---|
| Product | ZyXEL GS1900-8HP 8-port GbE Smart Managed PoE Switch [Website |
| Summary | 8-port GbE Smart Switch with PoE |
| Pros | • 70 W total PoE power • Silent • Relatively inexpensive |
| Cons | • Auto Voice VLAN assignment didn’t work • Limited QoS marking options for DSCP and IP Precedence |
Introduction
ZyXEL’s GS1900 series of 10/100/1000 Ethernet switches are 8-48 port Layer 2 managed switches designed for small business connectivity. Some of the models have two Small Form-Factor Pluggable (SFP) Ethernet port and some also support 802.2at Power over Ethernet (PoE) Plus. Table 1 summarizes the key differentiating features of the eight models in the GS1900 series.
| Model | Ethernet Ports | PoE | SFP |
|---|---|---|---|
| GS1900-8 | 8 | N | N |
| GS1900-8HP | 8 | Y | N |
| GS1900-16 | 16 | N | N |
| GS1900-24E | 24 | N | N |
| GS1900-24 | 24 | N | Y |
| GS1900-24HP | 24 | Y | Y |
| GS1900-48 | 48 | N | Y |
| GS1900-48HP | 48 | Y | Y |
Table 1: ZyXEL GS1900 series switch models
Although ZyXEL lists the GS1900s as small business switches, I think the GS1900-8HP, which is the focus of this review, is a good switch for a home network, especially if you need PoE ports.
Features
ZyXEL lists the features for the GS1900 on its product page, on a separate features page and in model-specific details when you click specifications and select a model number. Below is a listing of the GS1900-8HP’s features compiled from these sources.
- (8) 10/100/1000 Mbps GbE ports
- Browser-based switch management
- Set up wizards
- Fanless
- Network error prevention dual images, SSL
- Green Ethernet IEEE 802.3az support and intelligent ZyXEL green features
- PoE – (70 watts total, max 30 watts per port), IEEE 802.3at
- 16Gbps switching capacity
- 11.9Mpps forwarding rate
- 525K packet buffer
- 8K MAC table
- VLANs – port-based, 802.1q, Guest VLAN, Voice VLAN
- LACP Link Aggregation
- STP, RSTP, MSTP, BPDU guard
- LLDP neighbor detection
- Security
- 802.1x authentication
- TACACS+, RADIUS
- DoS prevention
- Port security, MAC filtering
- QoS
- 8 Priority queues
- Queuing methods = SPQ, WRR, WFQ
- 802.1p, CoS, ToS
- 802.3x flow control, storm control, per port rate limiting
- IPv6
- Dual stack
- ICMPv6
- Neighbor discovery
- Auto configuration
- Duplicate address detection
- SNMP v1-3
- IGMP Snooping v1-3
Under the Covers
The GS1900-8HP is a desktop switch, measuring 9.84″ x 4.10″ x 1.06″. It comes with adhesive rubber feet. The power supply is external and is a pretty hefty-sized “brick.” An impressive thing about this desktop switch is its PoE capabilities, yet it has no cooling fans so runs silently. Many PoE switches require noisy cooling fans due to the increased power demands of PoE.
I powered a VoIP device and two Wi-Fi access points via the GS1900-8HP and it remained cool to the touch. The GS1900-8, GS1900-8HP, GS1900-16, GS1900-24 and GS1900-24E are all fanless.
Below is a shot of the main board on the GS1900-8HP. The
GS1900-8HP runs on 64 MB of DDRII RAM with 16 MB of Flash memory.
ZyXEL hasn’t identified the switch device yet, but I will update when they do.
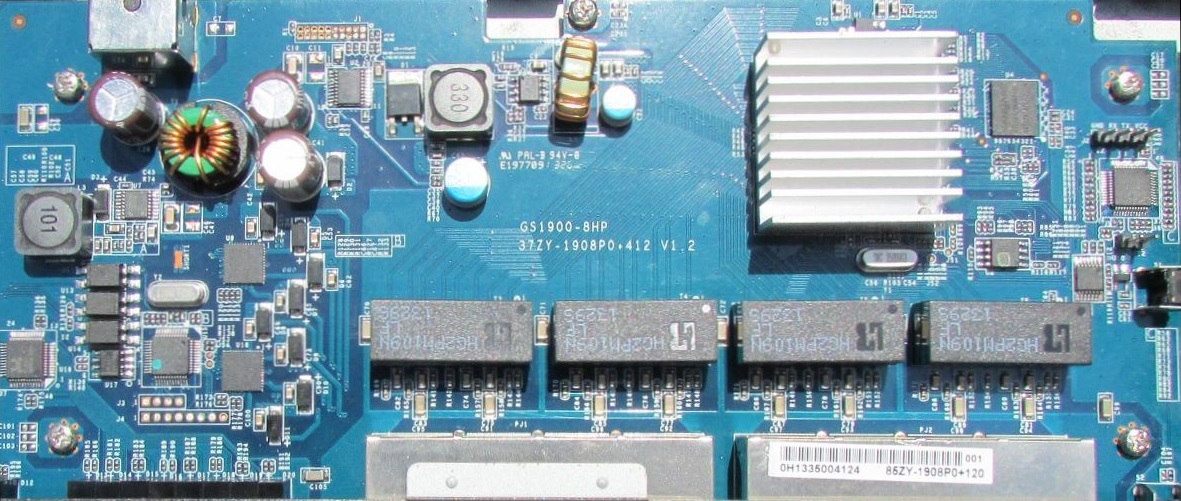
Main Board
The front panel of the GS1900 has eight Gigabit Ethernet ports and LEDs, shown below.

Front
The rear of the GS1900 is simply the power connection, also shown below.

Rear
Menu/Configuration
Taking a look at the configuration options in Table 2 provides a good listing of a device’s configurable features. The GS1900 has 14 main menus, each with several sub-menus and many of the sub-menus have multiple configuration tabs. I counted over 70 different configuration tabs!
The STP (Spanning Tree Protocol) menu, for example, has no sub-menus, but there are tabs for configuring Global STP on/off, STP port, STP priority and timers, STP port priority, MST (Multiple Spanning Tree) instances, and assigning ports to an MST instance.
| Menus | Sub-Menu | |||||
|---|---|---|---|---|---|---|
| System | IP | Time | Info | |||
| Port | Port | EEE | PoE | Band Mgt | Storm Control | |
| VLAN | VLAN | Guest VLAN | Voice VLAN | |||
| MAC Table | ||||||
| LAG | ||||||
| Loop Guard | ||||||
| Mirror | ||||||
| Multicast | IGMP | |||||
| STP | ||||||
| LLDP | ||||||
| QoS | General | Trust Mode | ||||
| Security | Port Security | Protected Port | 802.1X | DoS | ||
| AAA | Auth Method | RADIUS | TACACS+ | |||
| Management | Syslog | SNMP | Error Disable | HTTP /HTTPS | Users | Remote Access Control |
Table 2: ZyXEL GS1900 menu tree
The volume of configuration screens shouldn’t be intimidating. Even though this is a managed switch, it acts like any other switch out of the box. Even PoE works right out of the box with no need to configure anything.
I found the menus intuitive and rarely needed the 227 page manual as I tested various features. A nice convenience, which exists in other ZyXEL devices I’ve tested, is the manual is available by clicking “?Help” in the top right of the GUI. It would be nice, however, if ZyXEL provided configuration examples for various features.
The first page of the GUI when you log in provides a graphical view of the switch, access to four configuration wizards (Startup, VLAN, QoS, and LAG), and a table of information about the switch, including its name, model, serial, MAC, firmware, up time, current time, CPU and memory usage. Below is a screen shot of the graphical view of the switch. I find a graphical view of a device that displays actual LED status useful for remote management.
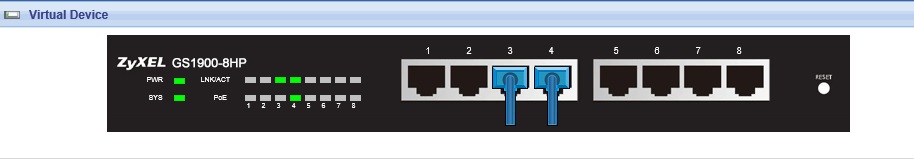
Front_GUI
I learned while configuring the GS1900 to remember to click “save.” Configurations are active when you apply them, but are lost during a reboot if they weren’t saved.
VLAN
The GS1900-8HP supports port-based and 802.1q VLANs. You can enter a VLAN ID from 1-4094, but it is unclear whether the device can support 4094 VLANs. (We’ve reached out to ZyXEL for clarification.) You can make a port an untagged member of multiple VLANs, which essentially provides the ability to do port-based VLANs.
The GS1900 also provides Guest VLAN and Voice VLAN functionality. The Guest VLAN functionality is useful if you’re using secure authorization via 802.1X, but want to allow restricted access to users who don’t have a valid user name and password. If one of these users connects to a port configured for the Guest VLAN without authenticating, they will be placed in the Guest VLAN. It is up to you to configure and apply the desired restrictions to the Guest VLAN.
A Voice VLAN can also be created, but requires a few steps, including creating a VLAN ID, assigning the VLAN ID to the Voice VLAN, adding the OUI and enabling the port for the Voice VLAN. Adding the OUI, which are the first 6 digits of a MAC address, is to enable automatically assigning a VoIP device to the VoIP VLAN. I was able to configure a Voice VLAN on the GS1900, but the OUI functionality didn’t seem to work as my VoIP device was not automatically placed in the Voice VLAN. As with the Guest VLAN, it is up to you to apply desired restrictions for the Voice VLAN.
I had no problems with 802.1q VLAN configuration. I set up an 802.1q trunk port between the ZyXEL GS1900-8HP and a Cisco SG200-26. The trunk port between the GS1900 and SG200 was set up to carry untagged traffic for VLAN 1 and tagged traffic for multiple VLANs. Access ports on the GS1900 assigned to the VLANs carried by the 802.1q trunk showed end devices in the proper VLAN.
Each port can be configured as a tagged or untagged member of a VLAN. In addition, a port can be configured as Excluded or Forbidden from a VLAN. If you configure a port as Excluded from a static VLAN, you’ve removed it from that VLAN. Forbidden prohibits a port from joining a dynamic VLAN. Below is a screen shot showing each port and LAG’s setting for VLAN1.
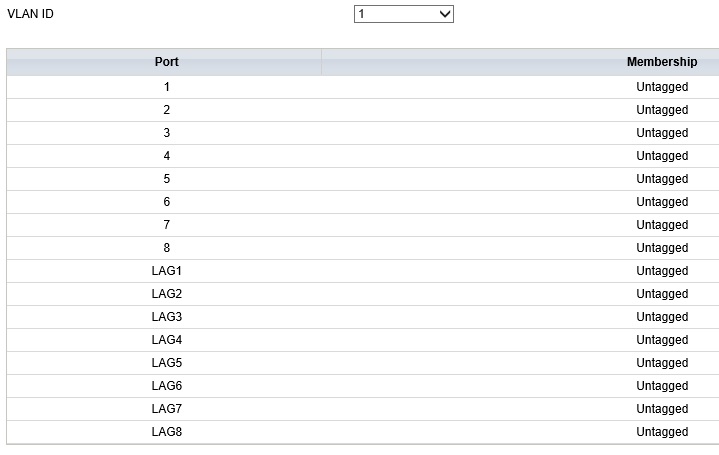
VLAN
PoE
For a small network running a couple of PoE devices, it is great to have a PoE switch to power remote devices like access points via the same Ethernet cable that provides data or to simply reduce the number of power outlets required. Unlike other inexpensive PoE switches that support PoE on only select ports, the GS1900-8HP supports PoE on all eight ports. Maximum power output is 30 W per port with a limit of 70 W for all ports. The other two PoE capable GS1900 switches, the GS1900-24HP and GS1900-48HP, provide up to 170 W total.
I connected three PoE powered devices to the GS1900-8HP, including Ubiquiti and Cisco access points, as well as a Panasonic VoIP device. All three powered up and worked as expected. As you can see in the below screenshot, the GS1900-8HP reports my devices were consuming 48.6 W, leaving 21.4 W to power additional devices.
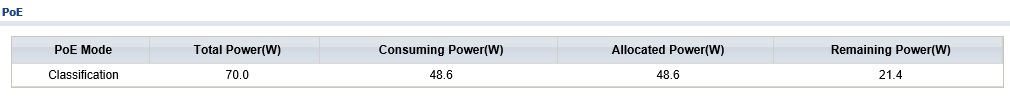
PoE
Each port on the GS1900-8HP can be enabled or disabled for PoE support, as well as assigned a PoE priority of Low, Medium, High or Critical. In the event power consumption exceeds the switch capability, power is distributed based on priority. Further, ZyXEL advertises that the GS1900s can reduce energy utilization by reducing power consumption during low link utilization, reducing power output on shorter cables and by monitoring link status.
QoS, Security
The GS1900 has multiple QoS tools available. The easiest option is to simply use the QoS Wizard that allows graphically applying High, Medium, and Low priority to each port.
For more advanced QoS configuration, CoS, DSCP and IP Precedence values can be used to control traffic priority. CoS values can be accepted, i.e. trusted, as marked on ingress frames or re-marked to a different value by port. CoS, DSCP and IP Precedence values can be mapped to 8 different queues for traffic prioritization. Traffic prioritization can be based on Strict Priority Queuing or Weighted Round Robin (WRR) Queuing.
I noticed the GS1900 menu has an option to re-mark CoS, DSCP, and IP Precedence values, but only provides a drop-down option to select new CoS values. Thus, it seems you either have to trust DSCP or IP Precedence values, or you’re limited to using CoS values.
Bandwidth utilization can also be explicitly controlled by port. I configured the GS1900 to limit ingress and egress bandwidth on a port to 1 Mbps, as shown below. Note, bandwidth limits on the GS1900 must be set to multiples of 16 kbps, so 992 kbps is the nearest multiple of 16. Before applying this limit, I ran a throughput test between two PCs using TotuSoft’s LAN Speed Test tool. Without the limit in place, my PCs could pass traffic in excess of 300 Mbps. Without the limit in place, my PCs passed traffic between 840-945 kbps, essentially validating the GS1900 can limit bandwidth utilization on a port.
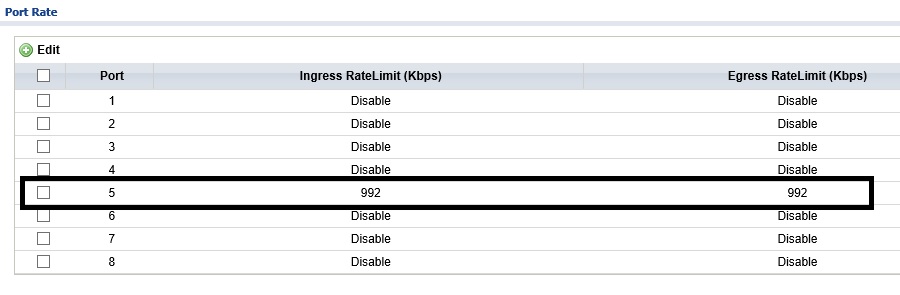
Bandwidth
Access to the GS1900’s network can be secured by port. Static MAC addresses can be entered as permitted devices or the number of permitted MACs per port can be set. When a port violation occurs, the port can be configured to drop packets or shut the port down. 802.1X authentication can also be set up, with the option of using a local database of user IDs, a RADIUS server, or a TACACS+ server.
Other
Spanning Tree Protocol (STP) is enabled by default on the GS1900. I ran my simple STP test on the GS1900 by plugging in both ends of an Ethernet cable to two ports on the switch. With STP enabled, the switch should put one of the two ports into a blocking or discarding state to prevent a switching loop, which is exactly what the GS1900 did, as shown in the below screenshot.
I plugged my loop into ports 7 and 8. Notice that port 8 is in a Discarding state to prevent a switching loop. With STP disabled, creating a switching loop often floods the network and results in traffic coming to a grinding halt. Indeed, with STP disabled and my Ethernet cable into ports 7 and 8, the GS1900 network was down until I unplugged the Ethernet cable causing the loop.
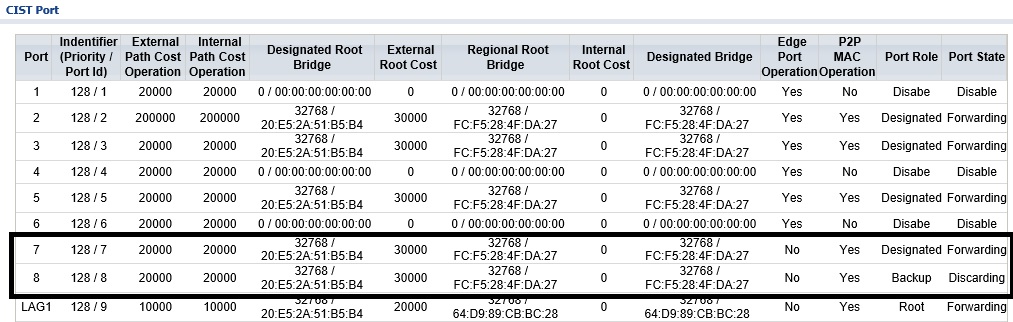
STP
Up to eight Link Aggregation Groups (LAGs) are supported on the GS1900-8HP. LAGs can be set up dynamically using Link Aggregation Control Protocol (LACP) or statically. I did a quick test and set up a static LAG between the GS1900 and my Cisco SG200-26 switch. As you can see in the below screenshot from the GS1900, I have an active LAG on ports 1 and 4.
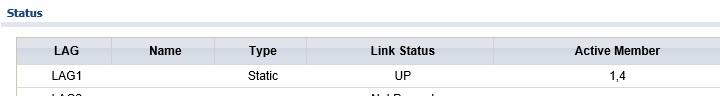
LAG
The GS1900 also supports IPv6. The management interface can be configured with both an IPv4 and IPv6 address. An IPv6 address can be statically applied, learned via DHCPv6 or set via stateless auto configuration.
Last, port mirroring can be configured to mirror egress and/or ingress traffic from any of the eight ports to a monitoring port. I find port mirroring is a useful feature for network troubleshooting.
Closing Thoughts
The ZyXEL GS1900-8HP is compared to two other current 8-port 10/100/1000 PoE capable switches from NETGEAR and Cisco in Table 3.
| Model | Max. PoE Power | Price |
|---|---|---|
| ZyXEL GS1900-8HP | 70 W | $116.14 |
| NETGEAR GS110TP | 46 W | $134.99 |
| Cisco SG200-08P | 32 W | $162.93 |
Table 3: Competitive Comparison
As you can see, the ZyXEL is the least expensive of the three, with the greatest PoE capability. Outside of the fact that the NETGEAR has two SFP ports and the other two don’t, all three of these switches are pretty similar.
I use a Cisco SG200-26 and a NETGEAR GS108T (which is functionally very similar to the GS110TP) in my network. Based on my experience with these two switches and my tests with the ZyXEL GS1900-8HP, I can say all three provide similar functionality needed for a small network. The ZyXEL’s differentiators are obvious: higher PoE power and lower price.
The bottom line is the ZyXEL GS1900-8HP provides more PoE power than the NETGEAR and Cisco 8-port PoE desktop switches, for less money.
