| At a Glance | |
|---|---|
| Product | Cisco SG500-28P Gigabit Stackable Managed Switch [Website] |
| Summary | High speed, full-featured smart network switch with PoE and 5/10 GbE uplink options |
| Pros | • Support for 4096 simultaneous VLANs • Layer 3 switching • Advanced QoS options • PoE on all ports • 5 and 10 GbE uplink options |
| Cons | • Configuration can be slow • Manual lacks examples • Losing your settings when switching to Layer 3 |
Introduction
Update 11/27/2012 – Clarify VLAN
This is a review of the Cisco SG500-28P small business switch. We don’t usually look at network products costing almost $1000. But for those who need more than simple "smart" switches can provide, but don’t want to wrassle with learning Cisco IOS, Cisco’s new switches may be what you’re looking for. To set the stage, I’ll start with a very brief overview on Cisco products.
Cisco classifies products into three groups: Home; Small Business; and Enterprise/Service Provider. The Cisco Home product group consists primarily of Linksys branded devices. The Cisco Small Business product group consists of routers, switches, and other network devices targeted at networks with greater demands than the typical home environment. The Enterprise/Service Provider product group consists of the high end/high performance gear for much larger networks.
In the small business product group, Cisco has four series of switches, ranging from unmanaged switches to high performance, fully managed, full featured stackable switches. Within these four series of switches, there are 52 different models! The models within each series vary on features, number of physical ports, port speeds and the option for PoE (Power over Ethernet).
With all the models, it is challenging to understand which is the best fit for a small network. Toward that end, I found there are some key differences among the series and have put together Table 1 to help understand them.
| Cisco Series | Configurable | Layer 3 | Stackable | Expansion |
|---|---|---|---|---|
| 100 | N | N | N | 1G combo mini-GBIC |
| 200 | Y | N | N | 1G combo mini-GBIC |
| 300 | Y | Y | N | 1G combo mini-GBIC |
| 500 | Y | Y | Y | 1/5/10G SFP / SFP+ |
Table 1: Cisco small business switch feature comparison
As you can see in Table 1, the 100 series are not configurable. These switches are ideal for simple deployments requiring basic connectivity. The 200 series are relatively easy to configure Layer 2 “smart” switches with support for VLANs, QoS, and other options. The 300 series are fully-managed switches and add Layer 3 functionality, meaning they can route traffic at switch speeds. The 500 series switches add stacking functionality. Stacking means multiple switches can be connected together and configured as a single switch. Multiple 500 series switches can be combined into a single stack with a maximum of 200 ports.
Cisco’s small business switch model numbers tell a lot about the device. All the Cisco small business switch model numbers have an S as the first character. The next character is an F or G, indicating whether the ports are Fast Ethernet or Gigabit Ethernet. Following the SF or SG is 100, 200, 300 or 500 to indicate series. Following the series number is a dash and the number of ports. (An exception to the model naming convention is the SG500X switches which have (4) 10Gbps ports in addition to the number of ports indicated in their model number.) Finally, a P at the end of the model number indicates the switch supports PoE.
In this review, I’m looking at the SG500-28P, positioned just below the top-of- line 500X models. The SG500-28P has 24 Gigabit Ethernet (GE) ports, 2 combo GE ports, and 2 dedicated SFP (small form-factor pluggable) fiber stacking ports that support 5 Gigabit SFP connections.
Inside
Physically, the SG500-28P measures 17.3” W x 1.73” H x 10.1” D and weighs 8.69lbs. It comes with brackets for rack mounting, and has a pair of 6300 rpm non-controllable fans for cooling. The fans aren’t quiet, thus this is a device that is designed for a data closet or server room, not a desk top.
Internally, the SG500-28P has two circuit boards and a power supply The main board holds an 800 MHz ARM CPU, 32 MB of flash memory and 256 MB of RAM. A second upper-level board holds circuitry that provides the 802.3af Power over Ethernet feature. Figure 1 provides a look inside the SG500 with the PoE board in place. Those are two Microsemi PD69012 12 port PoE devices you see on the board.
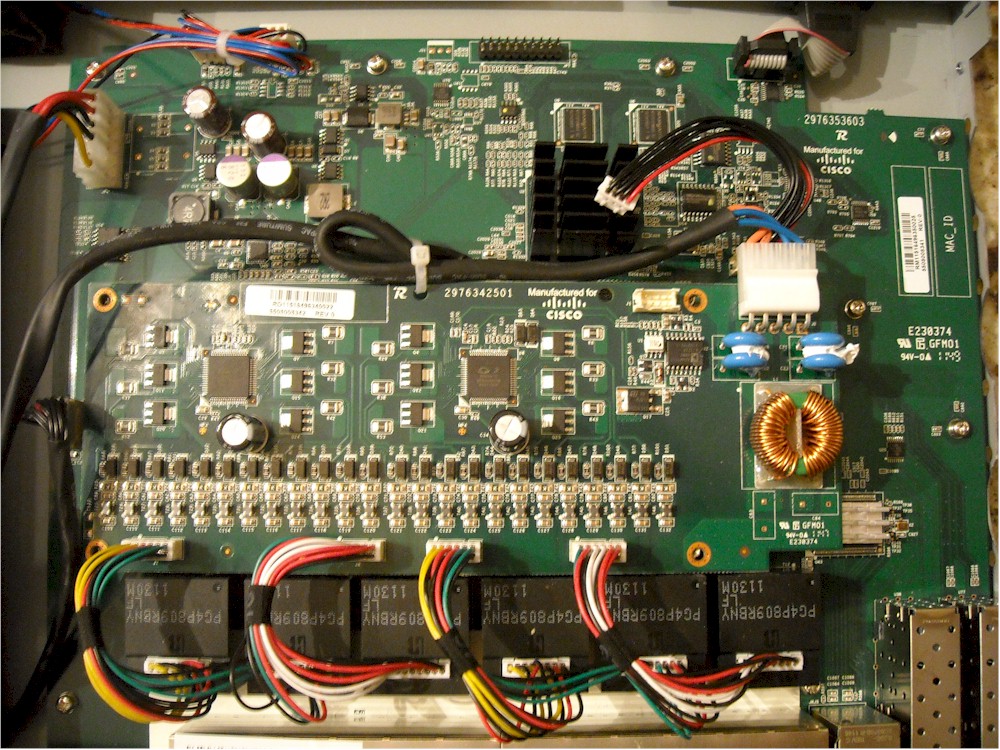
Figure 1: SG500-28P Inside view w/ PoE board
Figure 2 removes the PoE board to reveal the heatsinked switch chips. The CPU and switch chips all have firmly-attached heatsinks, so we’ve asked Cisco for help in identifying the components. We’ll update if we hear back.
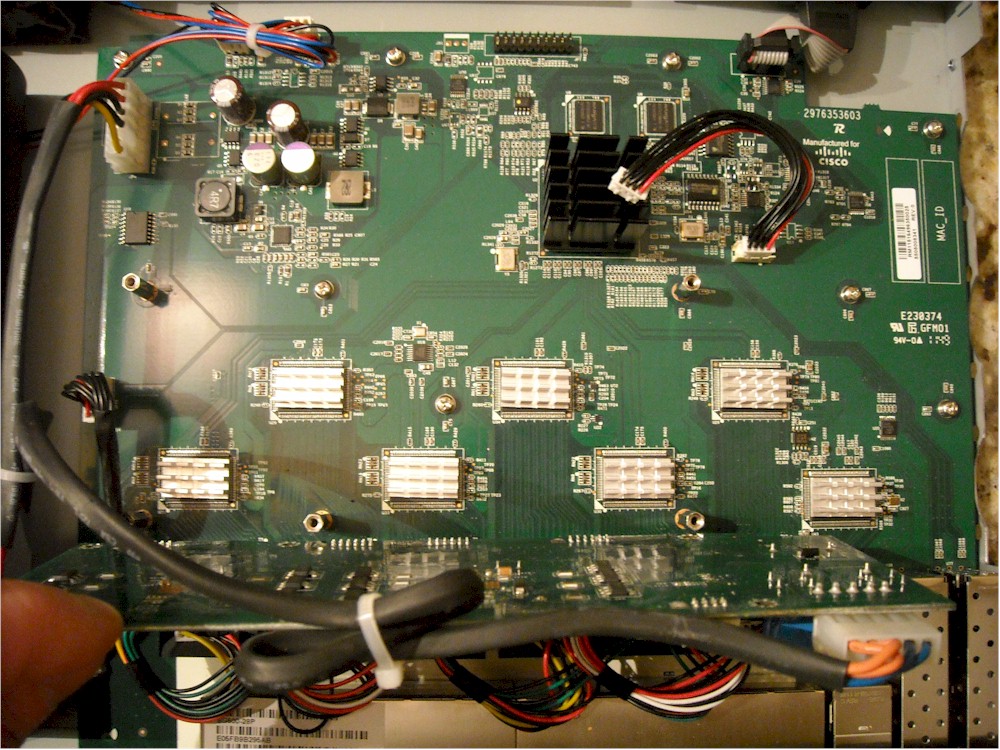
Figure 2: SG500-28P Inside view w/o PoE board
The indicator lights as well as the RJ45 and SFP ports are on the front of the switch, shown in Figure 3.

Figure 3: SG500-28P front view
The back of the switch, shown in Figure 4, has a console port, exhaust vents for the two fans and the power connector for the internal power supply.

Figure 4: SG500-28P rear view
Configuration
Cisco small business switches are configured via web based graphical user interface (GUI) as opposed to the IOS-based command line configuration used on Cisco’s Enterprise and Service Provider switches. Cisco’s command line configurations require a bit of a learning curve. But the web admin GUI makes the small business switches easier to configure.
The downside to the web GUI is there is a lag between some of the configuration screens. So I got to see the "Processing Data" graphic quite often when changing between admin screens. The delay isn’t horrible, only a couple seconds here and there, but not as responsive as Cisco’s IOS command line configuration. The menu lag is similar to what I’ve experienced on some of Cisco’s RV series routers, such as the recently reviewed RV180.
Figure 5: Waiting for the admin page to change
If you want to configure the SG500-28P from the command line, a serial cable is included to connect to the console port. The SG500 can also be configured from the command line via a telnet or ssh if enabled.
There are 13 configuration menus listed on the left side of the web page, with numerous submenu options in each. A look at the screen presented upon login is shown in Figure 6 below.

Figure 6: Main admin screen
The SG500-28P is a complex switch. I think you get a good idea of what you can do with a device by looking at a list of its configuration options. In Table 2, I’ve listed the 13 menus and their sub-menus. (Note, to fit all the sub-menus into a single table, I abbreviated some of the options.)
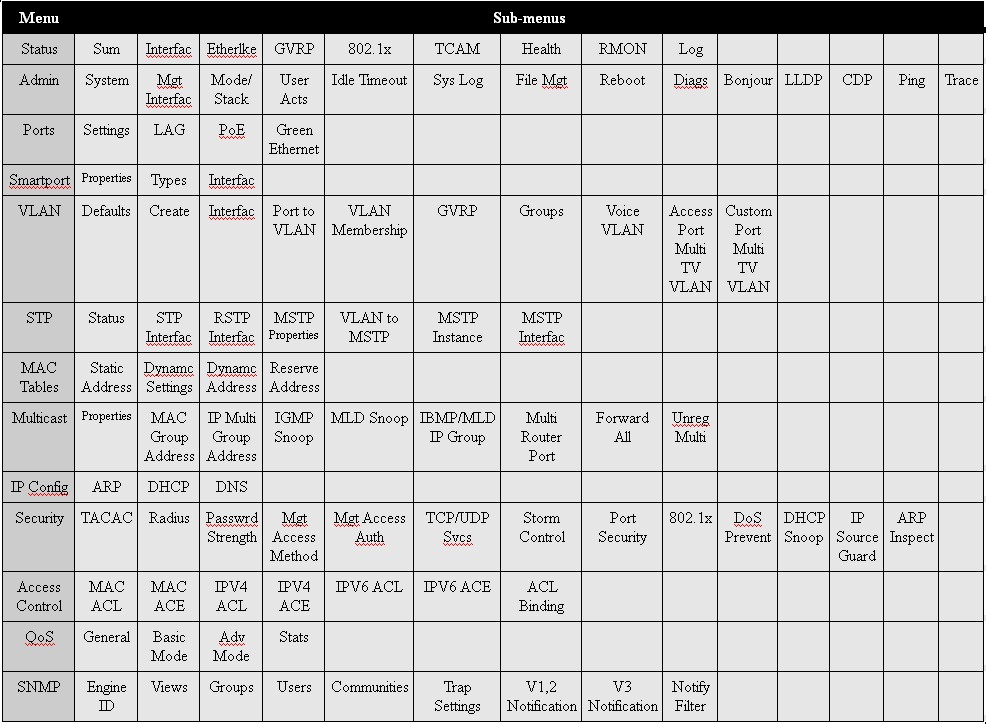
Table 2: Menu tree
A nuance in configuring this switch is that you must save your configs for them to persist through a reboot or power loss. Applying your configs make them active, but you’ll lose them in a reboot or power loss if you didn’t save them. This is similar to the copy run start command in Cisco’s IOS command line based devices. Fortunately, the GUI flashes a “Save” reminder in the top of the screen if there are newly applied configurations that haven’t been saved.
For information and help on how to configure the SG500-28P, you’ll have to refer to the Cisco 500 Series Admin Guide. This 469 page document is available on Cisco’s website, but surprisingly not on the disk that comes with the switch. The manual outlines the features, but could use a few examples to better explain the configuration options. If you’re a command line fan, you can download its guide, too.
Features – VLAN
The SG500-28P supports up to 4096 simultaneous VLANs. I found basic configuration of VLANs on this switch similar to the Linksys SRW2008 switch I used in the VLAN How To article I posted awhile back.
VLANs are created by giving them a number and optionally a name. Each port on the switch is then configured as an Access, Trunk or General port and given a Port VLAN ID (PVID). Access ports are members of a single VLAN with no tagging applied. Trunk ports are members of one or more untagged VLANs and zero or more tagged VLANs. General ports can be members of one or more untagged and tagged VLANs. The PVID identifies the port’s native/untagged VLAN.
I had no problems segmenting the ports on the SG500-28P into several VLANs as well as setting up an 802.1q trunk to a NETGEAR GS108T switch. There is a handy copy function on the SG500 which allows you to configure VLAN settings on one port and copy it to multiple other ports. In Figure 7, you can see my VLAN port status for ports 1-16.
Figure 7: VLAN port status
Port 1 is a trunk port with a configuration of “1UP, 2T” which means it is an untagged (U) member of VLAN 1, its PVID (P) is VLAN 1, and it is a tagged (T) member of VLAN 2. Port 1 is my trunk to the GS108T. Ports 2-12 are “1UP” which means they are untagged members of VLAN 1 and their PVID is VLAN 1. Ports 13-16 are “2UP” which means they are untagged members of VLAN 2 and their PVID is VLAN 2.
Of course, the SG500-28P VLAN capability is more advanced than the SRW2008 or GS108T previously mentioned. The SG500-28P has options for Generic VLAN Registration Protocol (GVRP), VLAN grouping to enable traffic load balancing, Voice VLANs for detecting and separating VoIP traffic into a different VLAN and options for allowing Multicast traffic to pass between VLANs.
Layer 3 Switching
VLANs separate traffic into different groups, and a good network practice is to assign a different subnet to each VLAN. To pass traffic between subnets, routing needs to occur, either with a router or Layer 3 switch. Layer 3 switches are desirable as they can pass traffic between subnets much faster than routers.
The SG500-28P can be configured as a Layer 2 or Layer 3 switch. With Layer 3 switching enabled, virtual Layer 3 interfaces can be created per VLAN and physical interfaces (single ports and LAGs) can be converted from a switched interface to a Layer 3 interface. Both virtual and physical Layer 3 interfaces can be assigned IPv4 and IPv6 addresses on the SG500.
By default, the switch runs in Layer 2 mode. If you choose to use Layer 3 mode, enable this option first. When you covert the SG500-28P to Layer 3 mode, it reboots and erases itself, regardless of whether you did a config save, wiping out all your previous configurations. (I learned this the hard way!)
With the SG500-28P in Layer 3 mode, you can configure an IP address for each VLAN interface on the switch. Each VLAN interface establishes a directly connected route in the SG500’s route table, which enables the switch to route directly between VLANs. Static routes can also be added, enabling routing between an external router, such as adding a default route to the router used to connect to the Internet.
I had no trouble configuring multiple VLANs, each with their own VLAN interface and IP address on the SG500-28P, as well as configuring a default static route. Figure 8 shows my two VLAN interfaces and their IP addresses.
Figure 8: IPv4 interfaces
Configuring a network with a Layer 3 switch involves multiple details in the switch, router and end devices, so I won’t cover all my configurations. However, with the correct static routes on the SG500-28P and my router, as well as the appropriate configuration in my end devices, I found the SG500-28P routed traffic at Layer 3 as expected.
The SG500 also supports IPv6 addressing and switching. Virtual and physical interfaces can be addressed with both IPv4 and IPv6 addresses, and you can create static routes for both IPv4 and IPv6 routes. Further, the SG500 supports IPv6 tunneling using Intra-Site Automatic Tunnel Addressing Protocol (ISATAP). ISATAP tunneling is a method for passing IPv6 traffic through an IPv4 network.
STP
The SG500-28P supports class Spanning Tree Protocol (STP), Rapid STP (RSTP), and Multiple STP (MSTP). Rapid STP is enabled on the SG500 by default.
STP prevents network loops from being formed by automatically taking down one or more interfaces suspected to be part of a loop. RSTP is a faster version of STP. MSTP allows for running multiple instances of RSTP to enable to loop prevention in a network running multiple VLANs.
To test RSTP, I connected two trunks on ports 1 and 5 between the SG500 and my NETGEAR GS108T with RSTP enabled on both switches. Without RSTP, both trunks would come up on both sides, resulting in a switching loop. With RSTP enabled, one interface on one switch should go into an Alternate (= blocking) state, preventing a switching loop.
The default settings of both switches led to the GS108T becoming the Root bridge and the Alternate port being established on port 5 the SG500 as shown in Figure 9, validating proper RSTP functionality.
Figure 9: RSTP settings
Jumbo Frames
The SG500-28P supports up to 10k byte jumbo frames. Enabling jumbo frames on the switch is a check box and reboot, as shown in Figure 10. Once enabled, I was able to pass up to 4k jumbo frames over the SG500, which is my end device limit.
Figure 10: Jumbo frame enable
LAG
Link Aggregation Groups allow for grouping multiple interfaces to form a single “pipe” between the switch and another LAG capable device. LAG trunking increases bandwidth between devices and improves redundancy as the LAG connection will stay up and carry traffic as long as one of its interfaces is up.
The SG500 supports static LAG trunks and dynamic LAG trunks using Link Aggregation Control Protocol (LACP). I configured two ports on the SG500 and GS108T to form a static LAG trunk. As shown in Figure 11, my LAG trunk came up without issue.
Figure 11: LAG settings
QoS
Quality of Service (QoS) is quite advanced on the SG500-28P. The switch can recognize Class of Service (CoS) values or Differentiated Service Code Point (DSCP) values for applying traffic prioritization. There are four queues and two different methods for queue management, as well as options for bandwidth limiting via ingress and egress rate controls.
In basic QoS mode on the SG500, QoS values can either be trusted or overridden per interface. In advanced QoS mode, QoS rules can be configured using Access Control Lists (ACLs) as part of a Class Map to match different traffic types, using the Class Map in a Policy Map to define how to prioritize that specific traffic type and finally applying the Policy Map to an interface via Policy Binding.
Traffic prioritization is handled via four queues, with traffic assigned to each queue based on QoS value. If there is congestion on the switch, traffic will get delivered based on queue priority. The SG500 can operate using either strict priority or Weighted Round Robin (WRR) method. Strict priority will ensure that traffic in the high priority queue gets through first, but can result in dropping too much traffic in the low priority queue. WRR provides a middle ground, allowing prioritization of delay sensitive traffic, yet permitting all traffic access to network resources.
Basic bandwidth utilization can be managed by port with Ingress and Egress rate limits. I ran a simple test by configuring a port on the SG500 with Ingress and Egress rate limits of 500Kbps. See port GE13 in Figure 12.
Figure 12: Bandwidth control
I connected my PC to port 13 with the above bandwidth limits and connected another PC to an unlimited port on the SG500. I then tested the SG500’s bandwidth limiting capability with iperf using default TCP settings. Using iperf, I measured 540 Kbps in each direction with the bandwidth limit applied, closely matching the 500 Kbps limit set.
Security
The SG500-28P has extensive security controls. Access to the switch can be controlled via a local database of user names or via external TACACS+ or RADIUS servers. To protect against various network threats, the SG500 has options for Storm Control, Port Security, 802.1x end device authentication, DoS Prevention, DHCP Snooping, IP Source Guard, and ARP Inspection.
To control traffic flows, the SG500 supports filtering traffic based on source and destination MAC, IPv4 or IPv6 addresses, QoS values, Layer 4 ports, and protocols. Traffic filters on the SG500 are applied to physical interfaces with Access Control Lists (ACLs). ACLs are lists of Access Control Entries (ACE). A total of 2000 different ACEs can be created on the SG500.
As a test, I created a basic MAC based ACL with a single ACE to shutdown the port if it saw traffic from a specific MAC and applied it to port 7. I then plugged the device with the specified MAC to port 7 on the SG500, which resulted in the switch disabling port 7 as expected.
PoE
The “P” in the SG500-28P model name means it supports Power over Ethernet (PoE). PoE is used frequently with VoIP devices, providing power over the network cable and eliminating the need for a separate power cable and outlet for the PoE end device.
The SG500-28P supports PoE standards 802.3af and the newer 802.3at. The SG500-28P can provide a maximum of 180W of power on ports 1-26. As a simple test, I plugged in a Grandstream PoE device to a port, saw it get power and boot immediately. You can see that port 7 is drawing 7600mW in Figure 13.
Figure 13: PoE port status
Other Features
The SG500-28P is an advanced stackable switch with a massive array of features. You can check out a complete list of features on Cisco’s small business 500 series switches is available in the 500 Series Data Sheet. Here’s a rundown of a few other key features:
- “Smartports” on the SG500 are statically or dynamically customized ports configured via Link Layer Discovery Protocol (LLDP) or Cisco Discovery Protocol (CDP) for specific device types, such as printers, PCs, VoIP devices, network devices, and so on.
- Port mirroring can be applied by port or by VLAN, enabling packet captures and advanced troubleshooting of network devices.
- The SG500’s “Green Ethernet” feature will temporary disable a port when it becomes inactive, and reduce power on ports connected to short Ethernet cables (less than 50m).
- More complex features on the SG500 include an array of options to manage Multicast traffic, as well as detailed support for SNMP communication with network monitoring systems.
Performance
To understand how Cisco’s small business switch series vary in performance, I looked at Cisco 24 port Gigabit capable switches in the 100, 200, 300, and 500 series.
Note, the Cisco 24 port 200-500 series switches may have up to 28 ports counting combo and stacking ports. A combo port is actually two physical ports, one copper and one fiber, with the fiber port supporting a fiber connector. If both the copper and fiber port in the pair are connected, the fiber port will be active. A stacking port is used for connecting, or stacking, multiple switches together. Also, I added the SG500X-24P to the comparison to include Cisco’s fastest switch in the small business series.
The performance and capacity data in Table 3 are from Cisco’s website and pricing is from Pricegrabber.com. Switching capacity, measured in Gigabits per second (Gbps), is the size of the data bus on the switch, which is a physical component rating. Forwarding capacity, measured in millions of 64-byte packets per second (mpps), is the speed of the packet processor, which is a throughput rating.
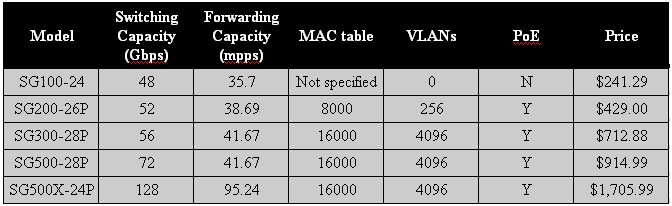
Table 3: Cisco switch comparison
As you can see in Table 3, as the model numbers go up, so does switching and forwarding capacity. MAC table capacity and the number of supported VLANs increase from the 100 to the 300 series, but are the same in the 300 and 500 series. Obviously, price goes up as you add capacity, speed, and functionality.
Closing Thoughts
Update 11/27/2012
So, which Cisco small business switch is the ideal switch for your network? I recommend starting by evaluating the number of ports and port speed required. If you need a simple "dumb" switch, the 100 series fits that bill. If you need VLANs, port mirroring or other simple managed switch features, you need at least the 200 series. If you need your VLANs to live on different subnets, you need the Layer 3 functionality of the 300 series. If you need routing on the switch, you need the Layer 3 functionality of the 300 series. Finally, if you’re looking to consolidate management of multiple switches with stacking, or need 5 or 10 Gigabit Ethernet uplinks, the 500 series is for you.
It’s hard to compare apples to apples when you compare different switch manufacturers, as different manufacturers bundle features differently. For example, the Cisco SG500 Series Stackable Managed switches seem to fall between NETGEAR’s ProSafe Stackable Smart switches and NETGEAR’s ProSafe Stackable Managed switches, as shown in Table 4.
| Model | Switching Capacity (Gbps) | MAC table size | VLAN | PoE | Price |
|---|---|---|---|---|---|
| NETGEAR GS724TPS | 48 | 8000 | 128 | Y | $700 |
| Cisco SG500-28P | 72 | 16000 | 4096 | Y | $915 |
| NETGEAR GSM7228PS | 144 | 8000 | 1024 | Y | $1504 |
Table 4: NETGEAR, Cisco switch comparison
Interestingly, the Cisco switch sits in the middle of the two NETGEAR switches in terms of switching capacity and price, yet has a larger MAC table and supports more VLANs than either NETGEAR.
Comparisons to NETGEAR aside, with the Cisco SG500-28P you get a high speed switch with 24 Gigabit Ethernet ports, 4 Gigabit Ethernet expansion ports (2 "combo" Gigabit Ethernet plus 2 1GE/5GE SFP), VLAN and Layer 3 functionality, and the ability to combine multiple switches into an easier to manage switch “stack.”
You also get support for network protocols and services including LLDP, CDP, STP, RSTP, MSTP, IPv6, TACACS+, RADIUS, 802.1x, ACLs, 802.1p, SNMP and a price around $950. With all these features, the SG500-28P is a high performance switch for a substantial network!
