
| At a glance | |
|---|---|
| Product | Cisco Dual WAN Gigabit PoE VPN Router (RV345P) [Website] |
| Summary | Dual-WAN 16 port Gigabit business VPN router with 802.3at PoE support |
| Pros | • Supports PPTP, IPsec, L2TP and SSL VPN • Supports USB WWAN dongle • Easy to configure • Supports application and web filtering |
| Cons | • Security feature and SSL license fees (both router and client side) • No OpenVPN support • Slow web admin |
Typical Price: $0 Buy From Amazon
Introduction
It’s been awhile since I’ve reviewed a Cisco small business router, going back to the RV320 in 2014. Cisco released their newest RV34x series routers back in early 2017. The lineup includes the RV340 dual WAN/4 LAN port, RV345 dual WAN/16 LAN port and the RV345P dual WAN/16 LAN port router with 8 Power over Ethernet (PoE) ports. In this review, I’m going to look at the RV345P.
An executive summary of the RV345P’s features is bulleted below. The full feature list can be found here.
- 2 WAN ports (RJ-45) allow load balancing and resiliency
- 16 LAN ports (8 data and 8 PoE ports, up to 30W per port
- 2 USB ports for 3G/4G modem or flash drive
- VPN functionality (IPSec, L2TP, PPTP, SSL)
- Support for Cisco AnyConnect Secure Mobility Client
- Dynamic web filtering
- Internet access policies
- Limited lifetime warranty and 1 year support included
Inside
The RV345P has a metal case measuring 11″ x 1.75″ x 6.75″. It includes rubber feet for desktop use and comes with rack mounting hardware. As shown in the below image, the WAN and LAN ports are all on the front of the RV345P. The power connector and on/off switch are on the rear, with USB ports on the front and right side of the chassis that can be used to connect a flash drive or a 3G/4G WWAN modem for additional redundancy.

Cisco RV34P Front
The RV345P is passively cooled, even though it supports eight PoE ports. It probably helps heat management that the power supply is external. A shot of the main board is below.
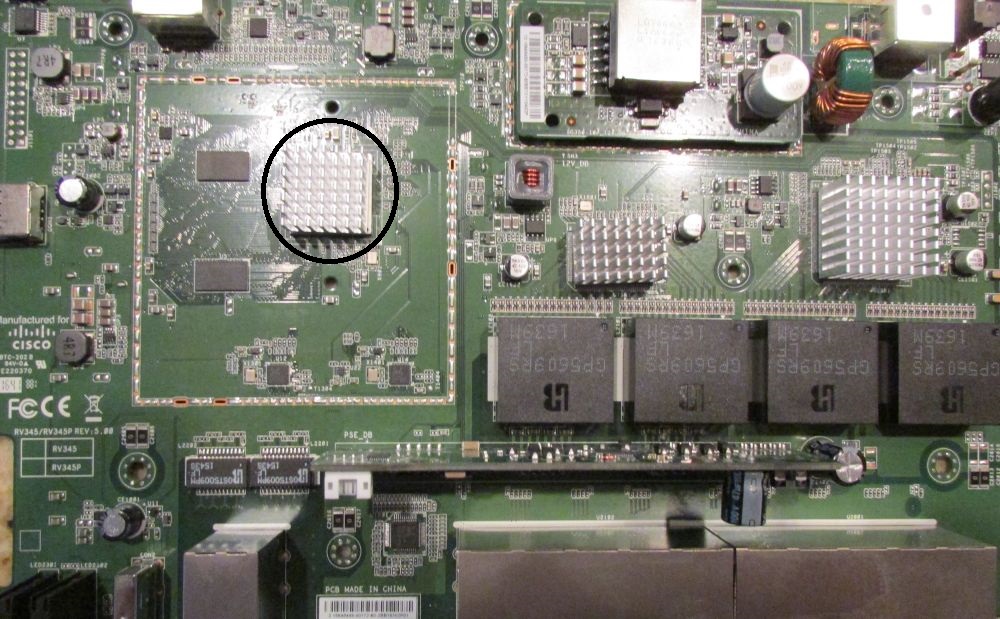
Cisco RV34P Mainboard
The board contains 256 MB flash, 1 GB RAM, and according to Cisco, “the most powerful processor(s) we have ever used (on the RV series)”. All heatsinks were firmly attached, so I didn’t remove them and risk damage. The unmarked processor is located under the heatsink circled in the above image. Cisco, however, said all RV34X series products are based on NXP‘s dual core ARM Cortex-A9 based QorIQ LS1024 and switches from Realtek.
The table shows key components for three RV series routers.
| Cicso RV34X | Cisco RV320 | Cisco RV042 v3 | |
|---|---|---|---|
| CPU | NXP QorIQ LS1024A @ 900MHz | 300 MHz Cavium CN5020 | 300 MHz Cavium CN5010 |
| Switch | Realtek | Broadcom BCM53125M | Realtek RTL8309G |
| RAM | 1024 MB | 256 MB | 128 MB |
| Flash | 256 MB | 64 MB | 32 MB |
Table 1: Cisco RV series key component comparison
Administration
Cisco lists the firmware for the RV345P as Linux based. However, the RV345P is configured via browser-based Graphical User Interface (GUI). The GUI is similar to previous models of Cisco RV routers I’ve used, so I found it intuitive and easy to use. As in previous Cisco RV routers, there remains a lag between clicking “Apply” on a configuration and the action’s completion, as well as when navigating between screens. A “Please wait…” message, shown below, is presented. In other words, the web GUI is pretty poky. Unfortunately, the GUI is your only administration option; the RV34X series does not support command line administration.
Configuration Lag
There are twelve main menus, including Getting Started, Status and Statistics, Administration, System Configuration, WAN, QoS, LAN, Routing, Firewall, VPN, and Security. Each menu has 3-14 different sub-menus. Below is a screenshot showing the main menus.
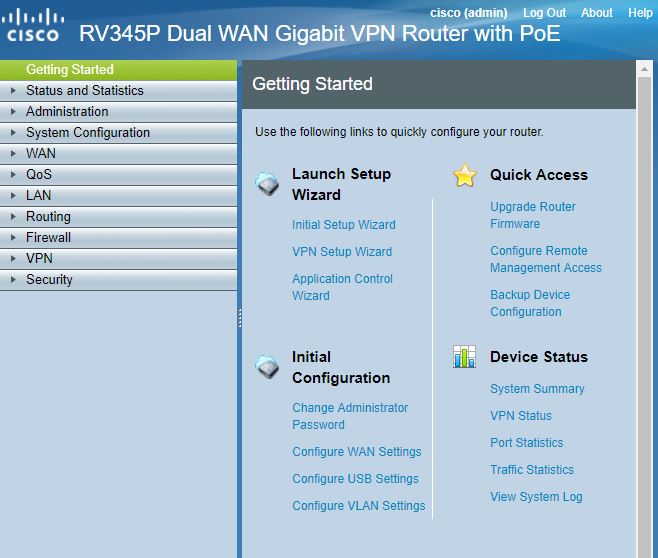
Main Menus
My test device came with the latest firmware, v1.0.01.17, so there was no need to use the GUI’s Administration-File Management sub-menu to update firmware.
The Setup Wizard has a simple five-step process to set up the WAN connection, set the time on the router, and edit the WAN MAC address if necessary. I ran this Wizard and quickly had the router passing traffic to and from the Internet.
Feature Tour
The RV345P is a Dual WAN router, with two additional USB ports for connecting a 3G/4G modem to connect to WWAN services for additional WAN redundancy. The default config on the RV345P is for WAN1 to be the priority, WAN2 to be second priority, USB1 third, and USB2 as fourth as shown below.
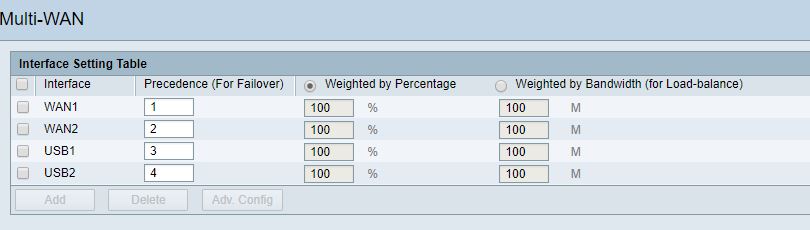
Multi-WAN
I connected both WAN1 and WAN2 to different Internet connections and set up a continuous ping to the Internet. I then physically disconnected WAN1. One ping dropped before the RV345P failed over to WAN2. I reconnected WAN1 and traffic eventually routed back over WAN1 without interruption, validating the RV345P’s Dual WAN capability.
More advanced Dual WAN management can be applied to load balance or distribute traffic over both WAN connection, as well as apply policies to direct specific traffic types over one or the other WAN connection.
VLAN
With 16 LAN ports, the RV345P provides a convenient all-in-one router and switch solution for a small network. The RV345P LAN menu provides options for enabling Port Mirroring, PoE, VLANs, DHCP servers, 802.1X authentication and IPv6 support.
In two steps, I had tagged VLANs running on the RV345P. First, I simply added a VLAN (VLAN 7). The RV345P conveniently made all ports untagged members of VLAN 1 and tagged members of VLAN 7. Second, I used the step-by-step DHCP menu to add a DHCP server on VLAN 7 using the 192.168.7.0/24 network. Below is a screenshot showing VLAN1 and VLAN7 configured on the RV345P.
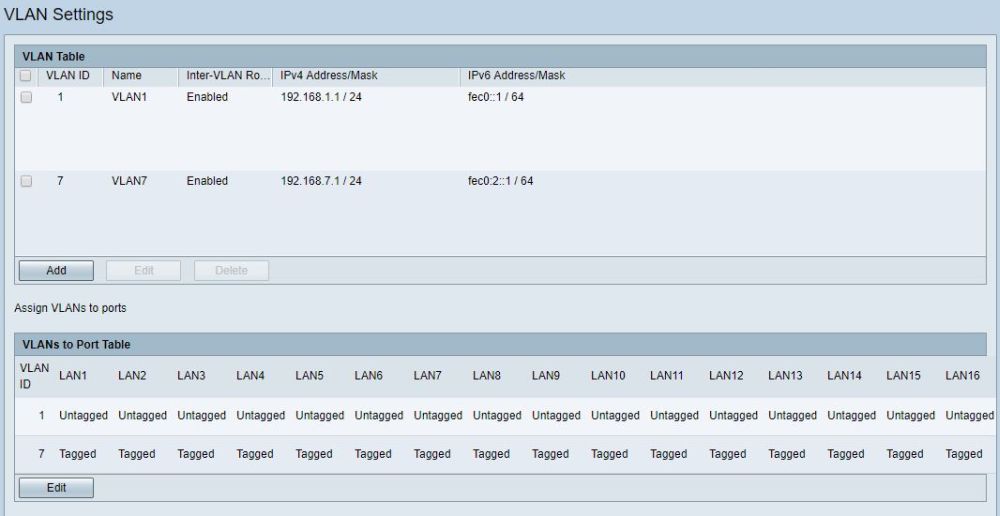
VLANs
I connected an 802.1Q-capable access point to port 1, with SSIDs configured for both VLAN 1 and VLAN 7. I was able to connect to both VLANs and get IP addresses from the correct subnet based on the SSID I attached to, validating the RV345P’s VLAN tagging capability.
VPN
The RV345P supports Generic Route Encapsulation (GRE), Site-to-Site (S2S) IPsec, Client-to-Site (C2S) IPsec, PPTP, L2TP, and SSL tunnels. I started by testing a S2S IPsec VPN tunnel.
When you create an S2S tunnel on the RV345P, you create a profile for your tunnel or use one of the pre-defined profiles labeled as Default, Amazon Web Services, or Microsoft Azure. These pre-defined profiles, if they apply to your desired tunnel, simplify S2S settings by filling in the DH, Encryption, and Authentication and Timer options.
There is a Wizard in the RV345P GUI for setting up S2S tunnels, which worked like a champ. I was easily able to set up and establish a S2S tunnel over a direct Gigabit Ethernet connection with a Linksys LRT224 router using AES-256 encryption and SHA-1 authentication. Below is a screenshot from the RV345P showing my established S2S tunnel to the LRT224.
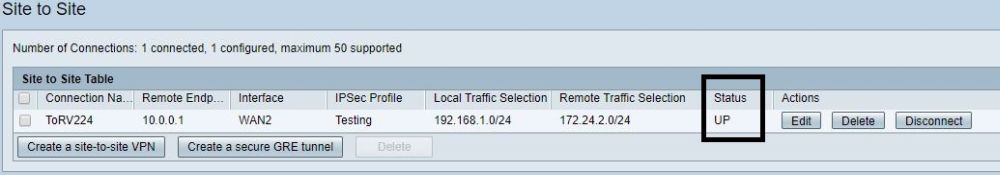
IPSec VPN Tunnel
For remote access, the RV345P supports C2S IPsec, PPTP, L2TP and SSL VPN connections.
Client to Site (C2S) IPsec tunnels are a bit more challenging to configure then S2S IPsec and the manual lacks detail and configuration examples. I couldn’t get a C2S tunnel to come up with trial and error, so asked Cisco for assistance. Cisco provided guidance that worked and they plan to update their instructions as well..
If you’re going to use a third-party IPsec client, like ShrewSoft‘s free IPsec client, you need to enable the third-party client option in the RV345P C2S menu, as well as enter your IPsec key and IPsec client IP address range. The RV345P’s default IPsec profile uses AES-128 encryption, SHA-1 authentication, and DH Group 5 for phase 1 and 2 IPsec configurations. You then need to select the same IPsec options, as well as “Mutual PSK+XAuth” for authentication on the ShrewSoft client. Once configured, my C2S connection succeeded, as shown below.
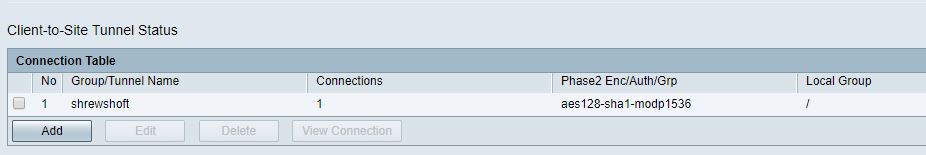
Client to Site VPN
Cisco states the RV345P supports 25 PPTP connections with 100 Mbps total throughput. The instructions in the Cisco manual were a bit vague, but enabling PPTP on the RV345P was pretty straightforward. I enabled the PPTP server and added IP address details for PPTP clients as shown below.
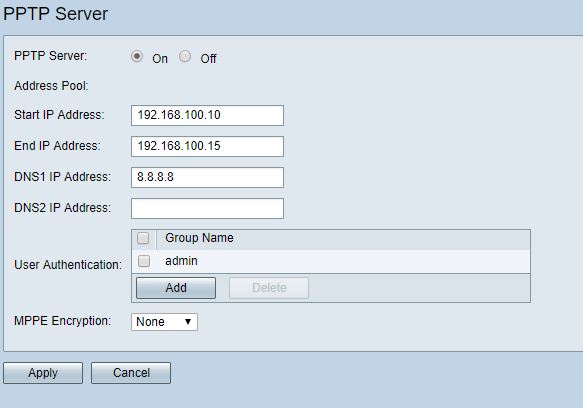
PPTP Setup
I had to play around with the PPTP settings on my Windows 10 PC until I got it to work. I ended up selecting PAP authentication after CHAP and MS-CHAP both failed. Below is my Windows 10 configuration that ended up working on the RV345P.
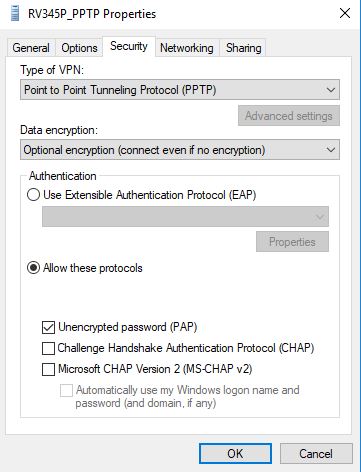
Windows PPTP Setup
Once I tried this setting, I was able to remotely connect to the RV345P, as shown below.
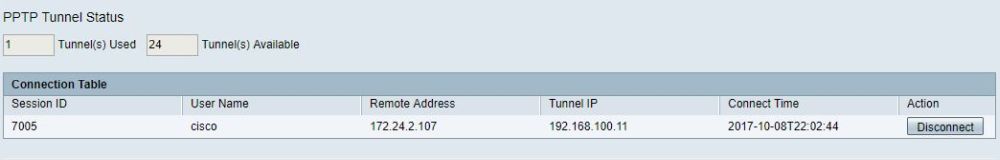
PPTP Connection
L2TP was more challenging than PPTP. As with C2S IPsec, I had to consult Cisco for assistance. The keys to setting up L2TP on the RV345P are to enable a user group with L2TP permissions and to create an IPsec profile that will work with Windows and Apple products. Cisco recommends the default RV345P IPsec profile using 3DES encryption, SHA-1 authentication and DH Group 2 for phase 1 and phase 2 IPsec configurations.
I tested L2TP to the RV345P from a Windows 10 PC. Below is a screenshot showing the Windows selections. As with PPTP, PAP is the authentication method for L2TP. In the Advanced settings section, you enter the pre-shared key you created on the RV345P.
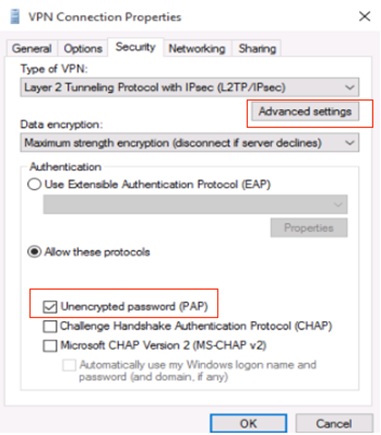
Windows L2TP Setup
With these settings applied on the RV345P and my Windows 10 PC, I was able to establish an L2TP VPN tunnel to the RV345P as shown below.
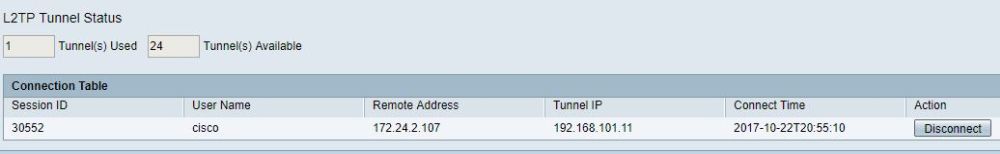
L2TP Connected
To remotely connect to the RV345P via SSL, you need to install the Cisco AnyConnect Secure Mobility Client. The RV345P supports 2 SSL VPN tunnels by default and, with a license (Cisco 1-Year RV Router Anyconnect Server 25 Tunnels, LS-RV-ACS-25-1YR=, $70), can support up to 50 tunnels. You can download the client software from Cisco.com (choose the "Pre-Deployment Package" option for your operating system) and use it during the RV345P trial license period (90 days). After that, you’ll need to purchase a license for the number of connections you want to support. A one year AnyConnect Plus license runs $3.99 for one user; $99.75 for 25.
The RV345P’s configuration was a matter of enabling the SSL VPN service and entering an IP address range for clients. The only trick on the AnyConnect software is to specify the IP address and port (8443) for the connection. My test RV345P had a WAN IP address of 172.24.7.101, so I used 172.24.7.101:8443 as the target in the AnyConnect software, which resulted in a working SSL connection, shown below.
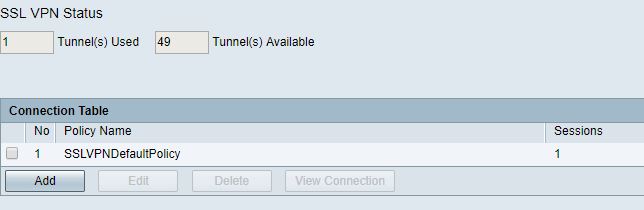
SSL Connected
I used TotuSoft’s LAN Speed Test client and server application for VPN throughput testing, using two PCs running 64-bit Windows with their software firewall disabled and 100 MB file size. I measured peak upload and download throughput over each of the VPN tunnels as shown in Table 2. Note that Cisco specs IPsec throughput at 650 Mbps.
| Max Throughput (Mbps) | ||
|---|---|---|
| Upload (Client-to-Gateway) |
Download (Gateway-to-Client) |
|
| IPsec | 202.9 | 216.8 |
| L2TP | 149.1 | 127.8 |
| PPTP | 147.9 | 2.5 |
| SSL | 7.0 | 5.6 |
Table 2: VPN throughput
PPTP and SSL results were surprising and not in a good way. I went back and retested my two PCs head to head, verifying they were capable of over 800 Mbps directly connected over a LAN. I then retested both VPNs to double-check my results, which were consistent. PPTP throughput on the RV345P was very asymetrical with 147.9 Mbps up and only 2.5 Mbps down. Cisco rates the RV345P capable of 100 Mbps for PPTP throughput.
SSL throughput on the RV345P was slow overall at 7.0 Mbps up and 5.6 Mbps down. This is very disappointing, considering you need to pay extra for the AnyConnect license to achieve such meager throughput.
I also tested IPsec Site-to-Site throughput connecting to a Linksys LRT224, measuring 48.9 Mbps up and 81.2 Mbps down. Given the Client-to-Site results above, the Linksys is obviously the limiting factor in these results.
PoE
802.3at Power over Ethernet is supported on eight of the 16 LAN ports (ports 1-4 and 9-12). The RV345P supports up to 30 W per port with a total capacity of 120 W. I connected a PoE capable switch to the RV345P, which powered up right away. As you can see in the screenshot, the RV345P is providing 13 W of power, with 107 W of power available.
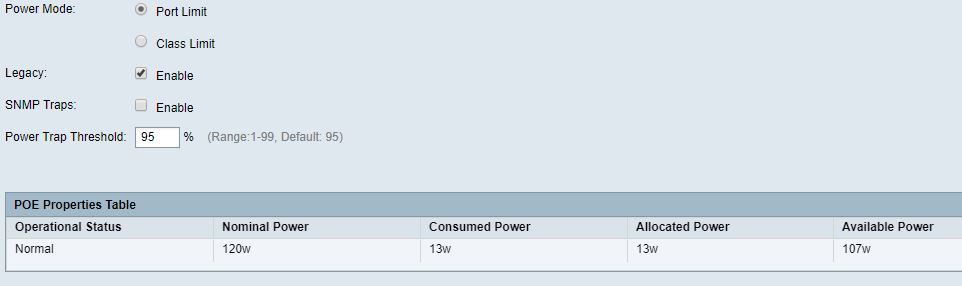
PoE
Firewall and Security
The Firewall menu on the RV345P is relatively basic, but easy to use. For example, enabling remote access is a simple check box titled “Remote Web Management,” a refreshingly simple process compared to more complex routers such as the recently reviewed MikroTik hEX and Ubiquiti EdgeRouter Lite.
Access Rules can be created to to control IPv4 and IPv6 traffic flows to allow or deny traffic based on source and destination interface and IP address, as well as based on daily and hourly schedules. The screenshot shows an RV345P Access Rule configuration.
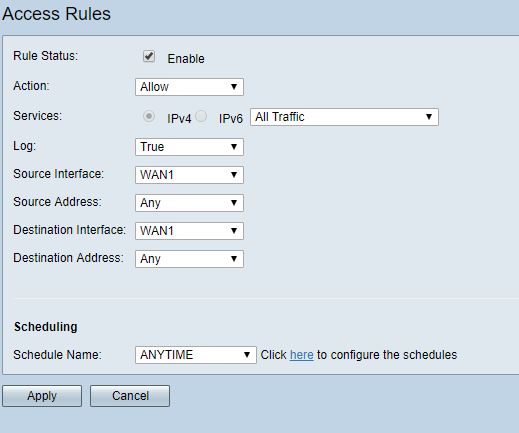
Access Rule
Cisco states the RV345P supports dynamic web filtering and internet access policies, which can limit Internet surfing to appropriate site categories and eliminate unwanted network traffic. The main Security menu options are Application Control, Web Filtering, and Content Filtering. All three are licensed features, so you’ll need to pony up $120 for a year of service if you want to use them beyond the 90 day trial period (order LS-RV34X-SEC-1YR=). This license is in addition to the AnyConnect SSL router and client licenses.
Application Control can be applied with a configuration Wizard or manually. I used the Wizard to block all types of Internet traffic, shown below, to see what it would do.

Application Control
Each of the above categories have multiple subcategories. For example, in the Shopping category, there is a subcategory for Amazon shopping. Each subcategory can be set to Permit & Log, Permit, Block, or Block & Log. I choose Block & Log on Amazon, which is a subcategory under Business/Investment, and then tried to surf to amazon.com. Before I applied the Application Control policy, I was able to surf to Amazon.com, but once applied, my browser just spun and the page wouldn’t come up. Once I removed the filter, I was again able to access amazon.com. I was a bit surprised an error message wasn’t presented instead of just blocking the page, though.
Application Control also provides the ability to control Internet access based on device type such as Camera, Computer, Game Console, Media Player, Mobile, and VoIP, as well as based on OSes including Android, Blackberry, Linux, OSX, Windows, and iOS. Further, pre-built schedules can be applied to filter based on Business, Evening and Working hours. You can also create custom schedules. Finally, filters can be applied by specific IP addresses or groups of IP addresses.
Web Filter rules can also be applied by device type, OS, schedules, and IP addresses as with Application Controls. Web Filtering can also be applied to protect end devices against malicious websites as shown in the screenshot. Web Filter rules can also be applied by device type, OS, schedules, and IP addresses as with Application Controls.
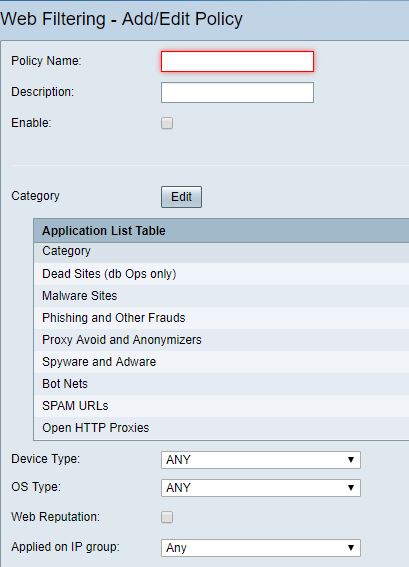
Web Filtering
To test the RV345Ps Anti-Malware protection, I used the Wicar.org malware test site. First, I left the Web Filter disabled to see what would happen. When I tried to download the test malware with the Google Chrome browser, I got a Google Chrome warning blocking the test malware, meaning the traffic got through the router and was blocked by Chrome. I then created a Web Filtering policy on the RV345P with a setting of high and selected all categories to filter, as shown below.
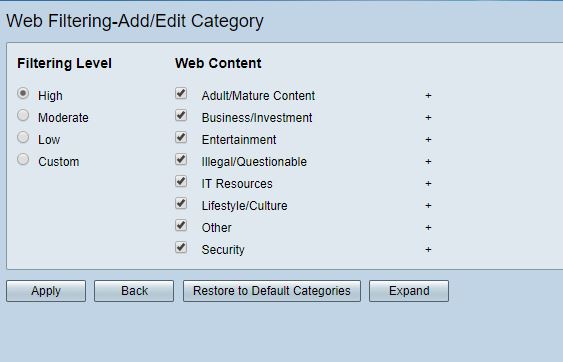
Malware Filtering
I then tried to browse to the site and download the test malware. Again, I received a Chrome block message, telling me the traffic got through the RV345P and was again blocked by Chrome. The test left me wondering about the effectiveness of the RV345P’s malware protection.
Content Filtering allows for blocking manually-entered domain names. I set up the below simple Content Filtering rule to block access to smallnetbuilder.com, which worked in the same manner as the Application Controls by blocking access, but not presenting an error or warning message.
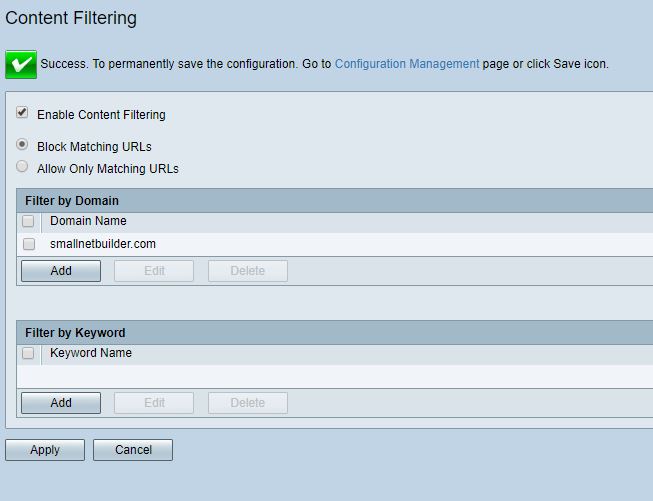
Content Filtering
QoS
The 345P supports both priority and bandwidth based QoS. Priority QoS controls can be applied by configurable traffic classes based on source/destination IP, network traffic types such as TCP, UDP, ICMP, HTTP, etc., device and OS type and DSCP codes. WAN Queuing and Policing rules can also be set to manage traffic flows to/from the Internet.
Bandwidth Management rules can be applied for each WAN interface to control upstream and downstream traffic. I set up the below rule to limit my Internet access to 500 Kbps up and down, and then ran a speed test on speedtest.net.
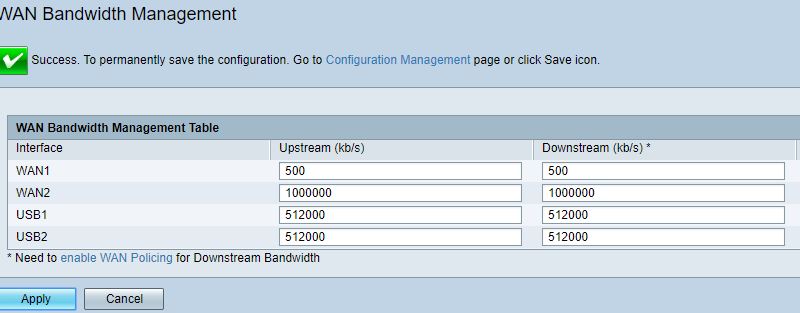
Bandwidth Management
As you can see in the below speedtest.net result, the RV345P effectively limited my 50 Mbps Internet to less then 500 Kbps as configured. Note, however both up and downlink throughput was significantly below the 500 Kbps programmed.
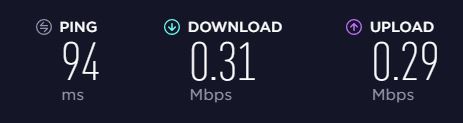
Speed Test
Reporting
The RV345P has numerous status pages for providing insight into traffic flows on the network and to/from the Internet. You can display statistics by by protocol, port, and IP address; packets/bytes sent/received by port; inbound and outbound QoS statistics by WAN port; and application stats as shown in the below screenshot.
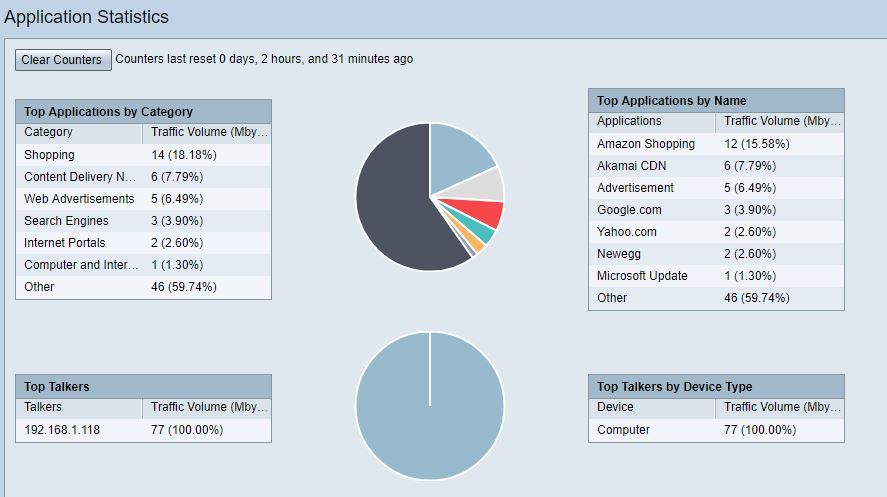
Application Statistics
Routing Performance
Analysis by Tim Higgins
We ran the RV345P through the Revision 10 performance test process with v1.0.01.17 firmware loaded, with the results summarized in the table.
| Test Description | Cisco RV345P |
|---|---|
| WAN – LAN Throughput (Mbps) | 936 |
| LAN – WAN Throughput (Mbps) | 938 |
| HTTP Score – WAN to LAN (%) | 54.6 |
| HTTP Score – LAN to WAN (%) | 55.0 |
| Bufferbloat Score- Down Avg. | 342 |
| Bufferbloat Score- Down Max. | 316 |
| Bufferbloat Score- Up Avg. | 313 |
| Bufferbloat Score- Up Max. | 272 |
| CTF Score (%) | 100 | Firmware Version | v1.0.01.17 |
There are no previous RV series routers tested with the Revision 10 process. So RV345P’s was matched against the Ubiquiti EdgeMAX EdgeRouter Lite. The EdgeRouter Lite is only a three port router designed to be paired with a network switch for additional Ethernet ports and is more challenging to configure than the RV345P. But the EdgeRouter Lite is known for its low price, yet high routing throughput and can be configured as a dual WAN router with many routing options like the RV345P.
The WAN to LAN and LAN to WAN tests at the top of the table are run with a single iperf3 TCP/IP connection and show results just a little shy of the usual 941 Mbps this test shows. For all intents and purposes, however, this test shows the 345P capable of gigabit wire-speed routing.
The WAN to LAN chart shows the Ubiquiti outpacing the Cisco on the smaller filesize tests (A and B), which present more load than the larger filesize tests, where both products do equally well.
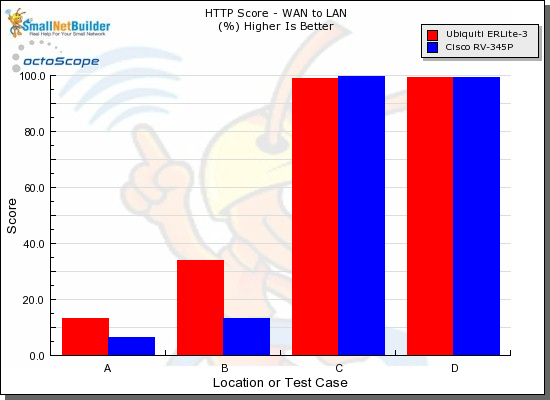
HTTP Score comparison – WAN to LAN
Plot key file size: [A] 2 KB, [B] 10 KB, [C] 108 KB and [D] 759 KB file
The LAN to WAN chart shows essentially the same result
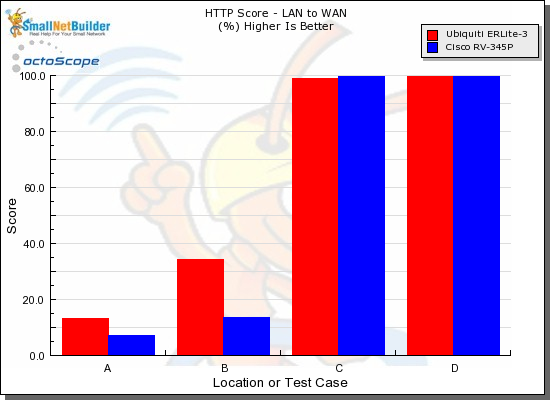
HTTP Score comparison – LAN to WAN
Plot key file size: [A] 2 KB, [B] 10 KB, [C] 108 KB and [D] 759 KB file
Our bufferbloat test measures ping variation while simultaneously running iperf3 traffic.Although the 345P comes in at the bottom of the chart, the scores shown represent average latencies of 2.9 ms downlink and 3.2 ms uplink, which are nothing compared to latencies of typical internet connections.
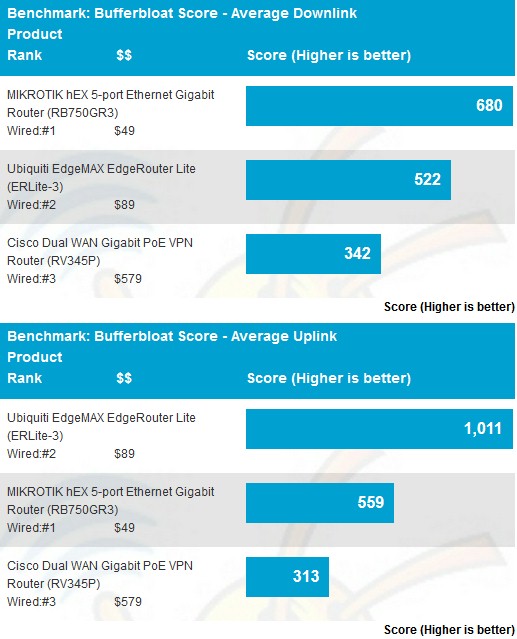
Bufferbloat test
Finally, the Cut Through Forwarding tests look for throughput reduction when various router features are enabled. The 100% result means there was no throughput reduction measured when Application Control, Domain blocking or Content filtering features were enabled.
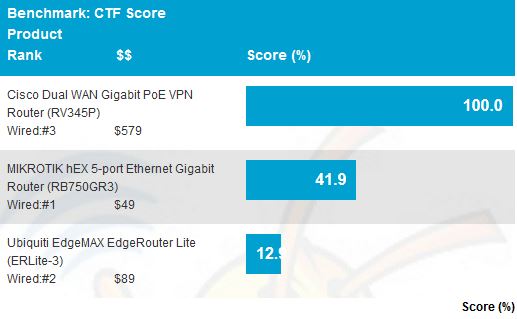
CTF score
Closing Thoughts
The RV345P is a dual-WAN router with ports for two wired and two 3G/4G Internet connections, plus a 16 port managed switch with VLAN and 120 W of PoE power! That’s a lot to pack into a relatively compact package. But all this capability comes at a price.
Amazon.com is showing the RV345P for over $425 as I write this. That doesn’t include AnyConnect or security feature licenses, neither of which is easy to buy or find pricing on. Cisco needs to address this if it wants to expand its customer base to smaller businesses.
Cisco may also need to look at pricing. If you want to support 25 SSL users and enable security features, your total will be over $700 and likely higher, depending on how good a deal you can find on the RV345P. And remember, you’re looking at $300/yr as an ongoing expense.
| Item | Price (US$) |
|---|---|
| RV345P | $425 |
| Security 1 year | $120 |
| AnyConnect (SSL) Server license – 25 users, 1 year | $70 |
| AnyConnect (SSL) Client license – 25 users, 1 year | $100 |
| Total | $715 |
In contrast, the EdgeRouter Lite used for comparison in the performance section is listed on Amazon for around $100. To get the same amount of Ethernet ports as the RV345P with the EdgeRouter Lite, you’ll also need a managed 16 port PoE switch, such as a NETGEAR JGS516PE, which runs about $185 on Amazon.
So the RV345P with router and PoE switch ports in one device is around $425, while an EdgeRouter Lite plus NETGEAR JGS516PE totals around $285, a difference of $140, give or take. If you’re only comparing routing and switching, the Ubiquiti and NETGEAR switch are a much cheaper option, but definitely not as easy to configure. More importantly, the RV345P brings dynamic application and web filtering, which you won’t find with the EdgeRouter. This filtering capability is a licensed feature, but you can try it for 90 days free.
If you like everything about the Cisco except the price and can also live without PoE, the RV345 would be your choice, for around $285. The security and SSL VPN license fees are the same.
At the end of the day, I found the RV345P quite simple to configure and fully-featured. Its menus are very similar to other Cisco small business network products I’ve tested and used, such as the Cisco SG200-26 small business switch I’ve been using in my lab for years. Although there may be cheaper solutions, not many are built into one package and as easy to use as the Cisco RV345P.
