
| At a glance | |
|---|---|
| Product | Cisco Dual Gigabit WAN VPN Router (RV320) [Website] |
| Summary | PPTP / IPsec /SSL VPN router with Gigabit ports and USB WWAN failover |
| Pros | • Responsive admin GUI • Automatic WAN load balance & failover • Easy to use firewall • 3G/4G USB modem support |
| Cons | • Balky SSL VPN • More minor bugs than there should be |
Typical Price: $0 Buy From Amazon
Introduction
Cisco has twelve RV series small business routers that support IPsec VPN tunnels. The models are summarized in the table below and vary in number and speed of WAN and LAN ports, built-in Wi-Fi, plus routing and IPsec VPN throughput.
Note, the throughput numbers in the table below are Cisco’s rated throughput numbers. You can go to the Router Charts for our throughput measurements and you can click on the model number in the below table to read our reviews. (The prices in the chart are taken from Pricegrabber.com.)![]()
| Model | WAN/DMZ Ports | LAN Ports | Gigabit | Wi-Fi | Router Throughput (Mbps) | IPsec Throughput (Mbps) | Price |
|---|---|---|---|---|---|---|---|
| RV016 | 2-7 | 8-13 | N | N | 200 | 97 | $340.91 |
| RV042v3 | 2 | 4 | N | N | 100 | 59 | $164.59 |
| RV042G | 2 | 4 | Y | N | 800 | 75 | $176.99 |
| RV082 | 2 | 8 | N | N | 200 | 97 | $241.93 |
| RV110W | 1 | 4 | N | b/g/n | 90 | 5 | $69.93 |
| RV120W | 1 | 4 | N | b/g/n | 100 | 25 | $162.54 |
| RV180 | 1 | 4 | Y | N | 800 | 50 | $108.00 |
| RV180W | 1 | 4 | Y | b/g/n | 800 | 50 | $142.99 |
| RV220W | 1 | 4 | Y | a/b/g/n | 800 | 90 | $215.87 |
| RV215W | 1 | 4 | N | b/g/n | 90 | 5 | $86.62 |
| RV320 | 2 | 4 | Y | N | 900 | 100 | $182.99 |
| RV325 | 2 | 14 | Y | N | 900 | 100 | $306.88 |
Table 1:
The Cisco RV320 and RV325 stand out among the RVxxx routers by having Cisco’s highest router and IPsec throughput ratings in the RVxxx family. The main difference between the RV320 and the RV325 is the RV320 has four LAN ports compared to the RV325’s fourteen LAN ports. This review will cover the Cisco RV320.
Inside
The RV320 is a desktop router, measuring 8.1″W x 5.2″D x 1.7″H. The case is metal and has an external power supply. It uses passive cooling, thus is silent. The indicator lights are on the front of the device, shown below and the RJ45 ports are on the back.
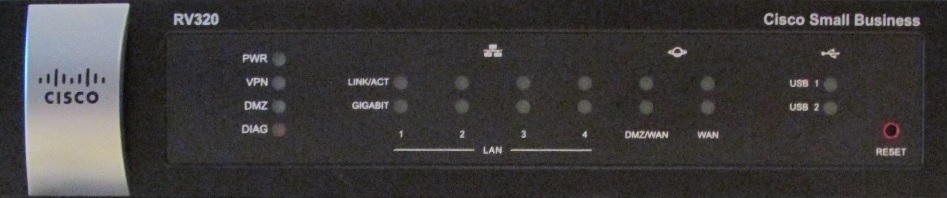
Front View
There are two 10/100/1000 WAN and four 10/100/1000 LAN ports. One of the WAN ports can be configured as either WAN or DMZ. There are two USB 2.0 ports, one on the side, the other on the back, which are for 3G/4G modems and/or loading firmware from a flash drive. The router does not support USB storage or printer sharing
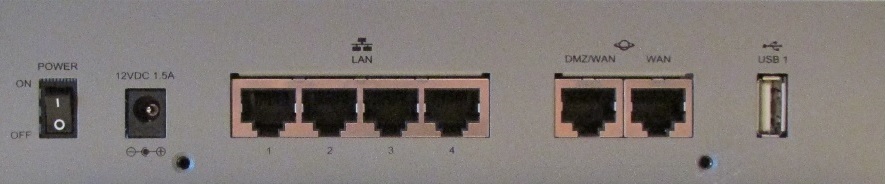
Rear View
The case on the RV320 seems a bit taller than other members of the RVxxx family, which may help airflow within the case. I used the RV320 for several weeks and never noticed it to be more than slightly warm. Inside the case is the main board, shown below.
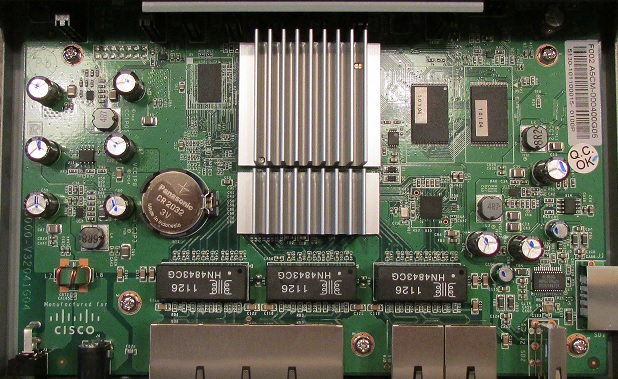
Main Board
Under the large heatsink is the CPU, which is a dual core Cavium CN5020 running at 300 MHz. The RV320 has 256 MB or DDR2 RAM and 64 MB of flash storage. The Ethernet ports are supplied by a Broadcom BCM53125M 7 port switch.
Features
The feature summary below is based on information from Cisco’s RV320 product site.
Router
- (4) 10/100/1000 LAN, (1) 10/100/1000 WAN, (1) 10/100/1000 DMZ/WAN
- (2) USB 2.0 ports
- 3G/4G WWAN Support
- 900 Mbps NAT throughput
- Dual WAN failover and load balancing
- Protocol based load balancing
- RIPv1/v2, RIPng
- 802.1Q VLAN – Support for 7 VLAN IDs
- IPv6
- QoS – application and service-based bandwidth and priority controls
SPI Firewall
- DoS, ping of death, SYN flood, land attack, IP spoofing protection
- 50 Schedule-based access rules
- 30 Port Forwarding rules
- 30 Port Triggering rules
- Static URL or keyword blocking (content filtering)
- DMZ port and DMZ host functionality
VPN
- IPsec – DES, 3DES, AES Encryption; MD5, SHA1 Authentication
- 50 IPsec Site to Site tunnels
- 10 SSL tunnels
- 10 PPTP tunnels
- 100 Mbps IPsec throughput
- 20 Mbps SSL throughput
Other
- SNMP
- LLDP
- 802.1X Authentication
Menu/Configuration
I generally like Cisco’s menus on their small business products. The RV320’s menus have the same look and feel of other Cisco small business products including RVxxx routers, SGxxx switches,WAPxxx access points and even the Cisco ISA550W.
Most options are either a check box or on a single page. For example, enabling remote access on the RV320 is just a check box, no firewall modifications are required. Configuring an IPsec VPN on the RV320 tunnel is a single page, which makes it easy to see all selected options, shown below.
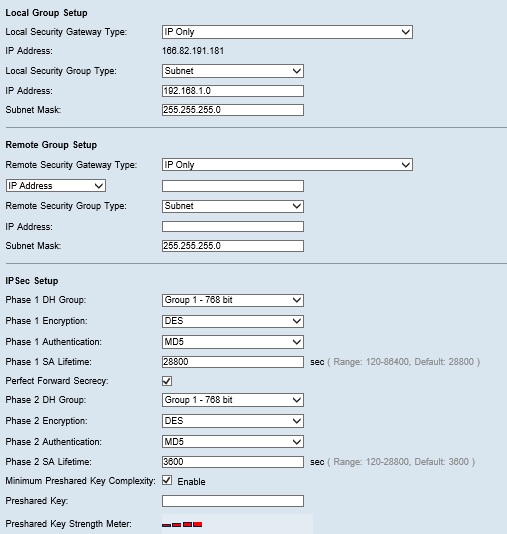
IPsec VPN Configuration
The RV320 has configuration wizards for setup of the WAN / DMZ interfaces and for firewall access rules. There are 10 main menu options, each with submenus for configuration. I’ve listed the main and sub menus for the RV320 in Table 2.
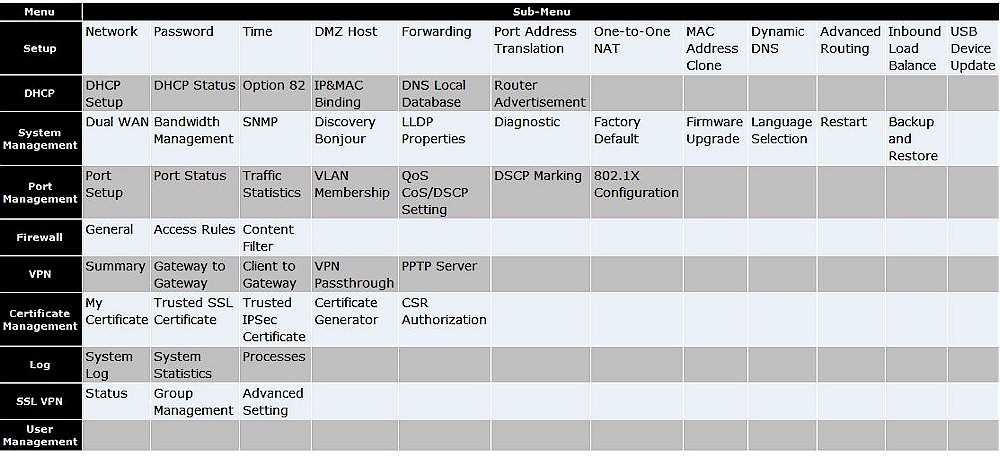
Table 2: Admin menu summary
At the top right of the RV320 configuration utility is a Help link that brings up menu descriptions and configuration options. Additional help is available via the 122 page admin guide, available on Cisco’s website.
One of the complaints I had with the Cisco RV180 and other members of the RVxxx family is menu lag and long boot times. The RV320’s menu is far more responsive and it boots up in about 1 minute.
A software detail on the RV320 that could be corrected is the menu for configuring the device’s time setting. It is important for a network device to have accurate time, so logs and event time stamps are accurate. The RV320 supports setting time zone, enabling daylight savings, and connecting to an NTP server. However, the RV320 only allows configuring a daylight savings rule following month and day, shown below, which doesn’t line up with the US daylight savings rule going from the second Sunday of March to the first Sunday of November.
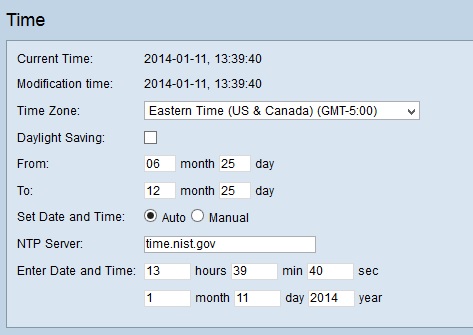
Time Configuration
Network
The Ethernet ports on the RV320 are all 10/100/1000, with two WAN ports and four LAN ports. The default for the WAN ports is Auto Mode, which load-balances traffic over both WAN ports using weighted round-robin load balancing. Optionally, you can set one WAN port as primary and the other as backup.
Using the default Auto Mode, my failover test on the WAN ports worked well. With both WAN ports enabled, I ran a continuous ping to google.com and disconnected one of the WAN ports. The RV320 dropped only one ping packet when it failed over to the other WAN port.
To optimize bandwidth utilization of each WAN port on the RV320, you can set your ISP’s max bandwidth by WAN port, for both upstream and downstream traffic. Bandwidth utilization can then be managed by setting rate control or prioritization rules. Rate control rules can be applied by interface, traffic type, IP address, upstream or downstream direction, and rate. Priority rules can be applied by interface and traffic type, and then given a high or low priority.
I created a rate control rule for one of the WAN interfaces to limit iperf traffic to 256 Kbps to see the accuracy of the RV320’s bandwidth controls. With the rule in place, my iperf test came back with a speed of 243 Kbps, closely matching the rule I set, shown below.
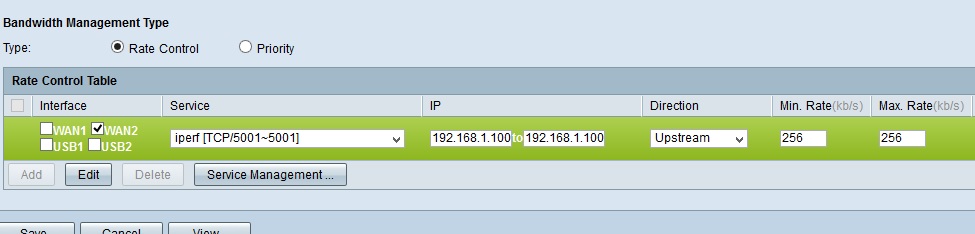
Rate Control
The bandwidth controls on the RV320 appear to be the primary QoS options on the device. There are two other menus that appear to offer additional QoS functionality, but they are confusing since the menu labels don’t match the functionality in the menus. The RV320 menu labeled CoS/DSCP Setting is actually a menu for mapping DSCP values to one of four priority queues. The RV320 menu labeled DSCP Marking is actually a menu for mapping CoS values to DSCP values.
In addition to the two WAN ports, there are two USB 2.0 ports. The USB ports can be used to connect a 3G/4G modem as a primary connection or as backup to the WAN ports. 3G/4G modem support makes for a great backup option to wired WAN ports. A backhoe could take out your physical Internet connections, but won’t affect wireless WAN connections! Cisco provided us this list of supported 3G/4G modems for the RV320.
When set as backup to the WAN ports, the 3G/4G modem can be setup in Hot Standby mode or Cold Standby mode. The difference is Cold Standby mode leaves the 3G/4G modem powered off until needed. Traffic controls can also be applied to the USB port so mobile data plan limits aren’t exceed.
The other intended function for the USB ports is to upload new firmware to the RV320. I tried several USB drives in the RV320. Based on the indicator lights on the front of the RV320 and the lights on the USB drives, my USB drives seem to have been recognized by the RV320. However, I couldn’t browse the content on the USB drives and thus couldn’t have uploaded a firmware file from a USB drive.
The RV320 supports up to seven 802.1q VLANs. Three VLANs are already defined: the default VLAN (=VLAN1), a guest VLAN (=VLAN25) and a voice VLAN (=VLAN100). Only VLAN1 is enabled initially. By default, all four LAN ports are untagged members of VLAN 1 and tagged members of the guest and voice VLANs. The RV320 already has a DHCP server enabled for VLAN 1, 25, and 100.
To test 802.1q tagging on the RV320, I connected the RV320 to a Cisco SG200 switch, set up a VLAN trunk on the SG200 belonging to VLAN 1 and 100, and connected a PC to an access port on the SG200 assigned to VLAN 100. My PC connected to the access port on the SG200 assigned to VLAN 100 got an IP address from the DHCP server in the RV320 assigned to VLAN 100, validating the RV320’s 802.1q tagging capability. Below is a screenshot of my RV320 VLAN configurations.
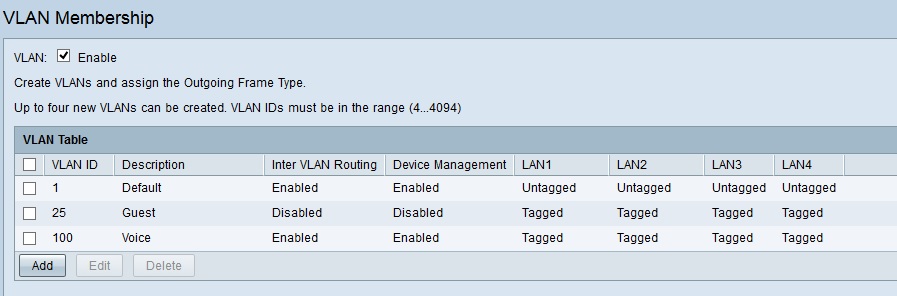
VLANs
Cisco’s RVxxx all support IPv6, including the RV320. The RV320’s WAN ports have IPv6 options for DHCPv6, stateless autoconfiguration, manual IPv4 to IPv6 tunnels, automatic 6to4 tunnels and IPv6 Rapid Deployment tunnels. The RV320’s LAN has IPv6 options for DHCPv6 and router advertisement to allow host stateless autoconfiguration.
VPN
IPsec, SSL and PPTP are the supported VPN methods on the RV320. The RV320 will support up to 50 IPsec tunnels, including IPsec Site-to-Site and Client-to-Site tunnels, plus (not mentioned in Cisco’s specs) 30 additional IPsec Easy VPN tunnels, which are established using the Cisco VPN client. Further, the RV320 supports 10 SSL tunnels and 10 PPTP tunnels.
Configuring an IPsec tunnel was straightforward. The RV320 supports DES, 3DES, 128/192/256 AES encryption, MD5 and SHA-1 authentication, as well as most typical Phase 1 and Phase 2 IPsec options. As mentioned earlier, all the IPsec configuration options on the RV320 are available on a single page, which helps keep track of selected options.
Using 256-bit AES encryption and SHA-1 authentication protocols, I was able to concurrently establish an IPsec Site-to-Site tunnel with a Cisco ISA550W and Zyxel Zywall 110, as well as an IPsec Client-to-Site tunnel to a PC running the Shrew Soft IPsec client. The screen shot below shows all three tunnels connected.
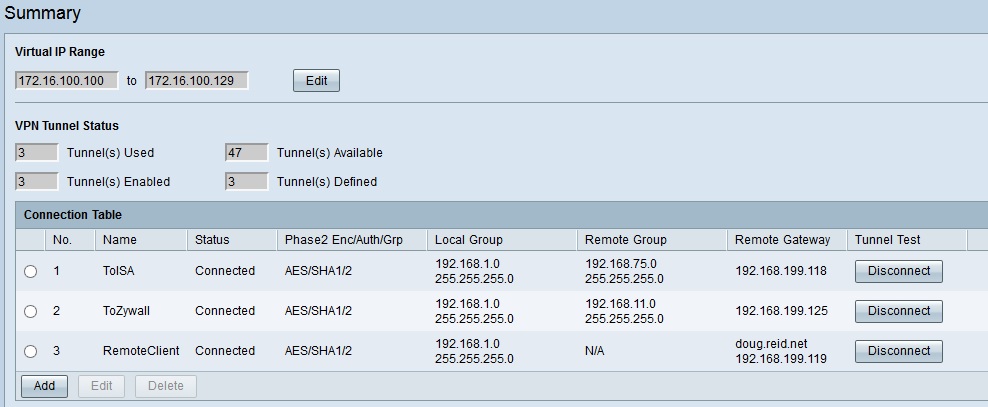
VPNs
The RV320 includes Cisco’s VPN client software on a utilities disk for Easy VPN connectivity. According to the RV320 manual, the version 5.0.0.7 Cisco VPN client on the disk supports Win 7 (32-bit and 64-bit), Windows Vista (32-bit and 64-bit), and Windows XP (32-bit). Older versions of the Cisco VPN client support Mac OS 10.4 and 10.5, as well as Linux.
I was able to establish an Easy VPN tunnel with the RV320 using the Cisco VPN client with a Win 7 64-bit PC by following the instructions in the RV320 manual. My RV320 configs for the Cisco VPN client are shown below.
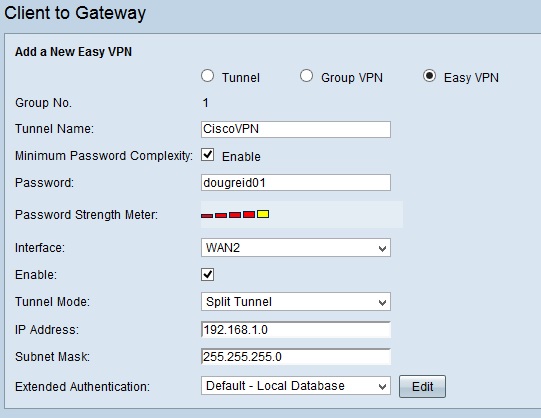
Easy VPN
The RV320 admin guide states TheGreenBow IPsec VPN client is also supported. As mentioned above, I found ShrewSoft’s IPsec VPN client also works with the RV320.
Configuring the RV320 for SSL VPN wasn’t too difficult, just click a checkbox in the firewall menu to enable SSL VPN, add a Mobile user name and password in the user management menu and enable the SSL Mobile user group. Configuring a client for SSL VPNs is supposed to be even easier, but I had trouble due to the virtual passage adapter/driver that should automatically install on the client PC.
I was able to establish an SSL VPN tunnel from a Windows 7 32-bit PC to the RV320. However, I couldn’t get an SSL VPN tunnel to work on a Windows 8.1 64-bit PC, a Windows 7 64-bit PC, or a Mac OS 10.6.8 PC. In each case, I saw error messages on my PCs regarding the virtual passage driver. Below is a screenshot of the error message from my Win 7 64-bit PC.
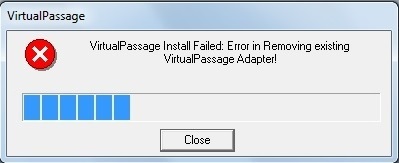
SSL Driver Error
I did some digging to see if I could resolve these problems. The release notes for the RV320’s current firmware (1.1.1.06) state the “SSL VPN virtual passage adapter does not work on Windows 7 (64-bit) with IE10, and on Windows 8.1 with IE11”. I also contacted Cisco and was told to disable popup blockers, enable Java and Javascript, and turn on Active X for Windows clients. Further, I was also supposed to open Internet Explorer as administrator so the virtual adapter would install.
For Mac OS, I was told to log in as root to install the virtual passage driver. Last, Cisco told me they have verified SSL VPN with the RV320 with the following operating systems and browsers:
- Win7 32 bit with IE9 and Firefox
- Win7 64 bit with IE9 (64bit)
- Linux (Ubuntu) with Firefox
- Mac OS(10.7.5) with Safari
- Mac OS (10.8.2, 64bit) with Firefox, Safari, Chrome
With this new information, I downgraded my Win 7 64-bit PC to IE9 and followed Cisco’s guidance, but had no luck. Perhaps the problem was in my PC. However, I recently had SSL VPNs working with this same Win 7 64-bit PC to both the Cisco ISA550W and the Zywall 110. Interestingly, neither the ISA550W or the Zywall 110 use the virtual passage driver.
I had better success with PPTP VPN tunnels. All I had to do on the RV320 was enable PPTP with a single checkbox. The user name I created for remote access above worked on PPTP, so I didn’t have to add a new one.
I had no problem establishing a PPTP connection to the RV320 from all my Windows PCs, my MAC, and an iPhone. Below is a screenshot from the RV320 showing an active PPTP connection.
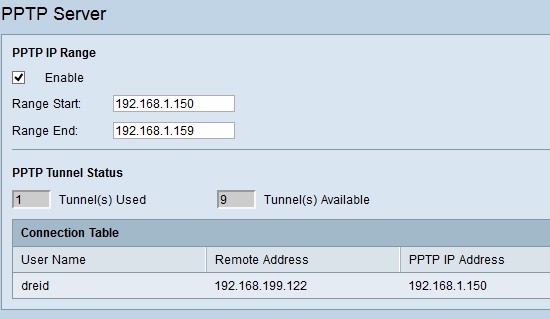
PPTP VPN
VPN Performance
Cisco rates the RV320 capable of 100 Mbps IPsec throughput for UDP traffic. I tested the RV320’s VPN performance with TCP traffic, which is the protocol used for common network applications like web browsers and email clients and also my VPN performance test standard.
I used iperf as my throughput measuring tool with default TCP settings, a TCP window size of 8 KB and no other options. I ran iperf on two PCs running 64-bit Windows with their software firewall disabled over a Gigabit network. (Running a simple iperf throughput test between two PCs uses the command iperf -s -w 8k on one PC and iperf -c (ip) -w 8k on the other PC.)
Table 3 summarizes my peak throughput measurements for each VPN tunnel type.
| VPN_Tunnel_Type | Throughput (Mbps) | |
|---|---|---|
| Client-Gateway | Gateway-Client | |
| IPsec Site to Site | 39.4 | 55.3 |
| IPsec Client | 8.6 | 56.0 |
| PPTP Client | 20.9 | 22.7 |
| SSL Client | 10.7 | 15.2 |
Table 3: VPN Performance summary
The RV320’s IPsec VPN measurements of 39.4 / 55.3 Mbps for a Site-to-Site IPsec tunnel were achieved with a ZyWALL 110, which I recently measured as capable of 61.3 / 72.5 Mbps.
The IPsec Client throughput numbers of 8.6 / 56.0 Mbps are with the Cisco VPN Client. I also tested IPsec Client throughput with the Shrew Soft VPN client and got slightly different numbers of 11.5 / 52.7 Mbps.
PPTP and SSL VPN throughput were a bit more symmetrical and closer to what Cisco reported. Cisco told me they measured PPTP above 20 Mbps and SSL VPN around 18 Mbps. As you can see in the table, I measured the RV320 PPTP performance at 20.9 / 22.7 Mbps and SSL performance at 10.7 / 15.2 Mbps.
To summarize my VPN impressions of the RV320, I found the configurations on the router to be easy and IPsec and PPTP VPN tunnels worked well. Based on my tests, the RV320 IPsec throughput isn’t significantly faster than Cisco’s RV180 or RV220W, which I measured at 39.7 / 50.9 Mbps and 38.3 / 49.3 Mbps.
On the downside, SSL VPN connectivity on the RV320 was a bummer; I could only get it working on Win 7 32-bit. Fortunately, both Quick VPN and PPTP connectivity on the RV320 worked well and provide good options for remote connectivity.
Firewall
The RV320’s firewall has three options. First, you can enable/disable standard firewall protections such as SPI (stateful packet inspection), DoS (denial of service), WAN ping, remote access and so on. Second, you can create access rules to allow or deny traffic using a specific protocol/port, interface and IP address or range of addresses. Third, you can implement content filtering by creating lists of trusted/forbidden domains and keywords. Access rules and content filtering can be applied 24×7 or based on customizable schedules.
RV320 firewall rules can be created to filter traffic based on TCP/UDP protocol, source and destination interface, source and destination IP address or range and be applied based on hourly and daily schedules. Below I’ve created a simple firewall rule to block iperf traffic from passing through the RV320.
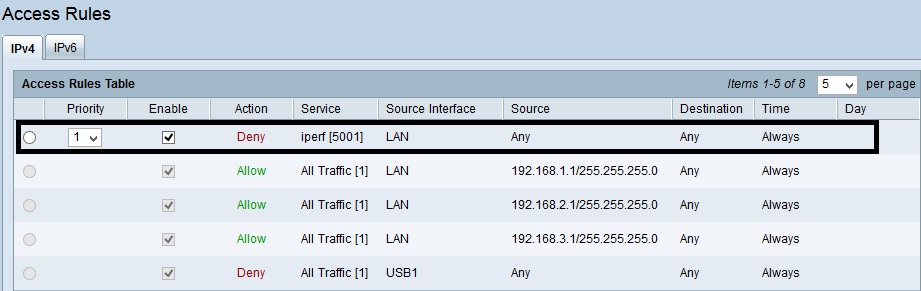
Firewall Rule
Content filtering on the RV320 is basic. You can block or allow websites based on manually entered domain names, as well as block websites based on keywords. If a user browses a web page from either the blocked domain or keyword list, they are presented a message stating “This URLs or Page has been blocked”.
Another element to the RV320 firewall is DMZ interface support. WAN2 can be configured as a DMZ interface. Separate firewall rules can be created in the RV320’s firewall to allow or deny traffic to/from the DMZ interface. In addition, a single host on the LAN can be defined as a DMZ host. Typically, a firewall will pass unsolicited inbound traffic from the WAN interface to the DMZ host.
Routing Performance
Routing performance for the RV320 with firmware v.1.1.1.06 and using our standard test method is summarized in Table 4. I added the Cisco RV180 to the table as a comparison, which I’ll comment on shortly.
The maximum simultaneous connections result for the RV320 is 32,249, which is the test limit. That’s good.
| Test Description | RV320 | RV180 |
|---|---|---|
| WAN – LAN | 887.0 | 798.3 |
| LAN – WAN | 746.3 | 811.2 |
| Total Simultaneous | 832.3 | 1,191.6 |
| Maximum Simultaneous Connections | 32,249 | 10,000 |
| Firmware Version | v1.1.1.06 | v1.0.1.9 |
Table 4: Routing throughput summary
Our throughput tests for download and upload speeds on the RV320 are shown in the IxChariot plot. The download speed was consistently above 900 Mbps, but a few downward spikes dropped the average to 887 Mbps. Upload speed averaged 746 Mbps, with a few spikes peaking over 900 Mbps.
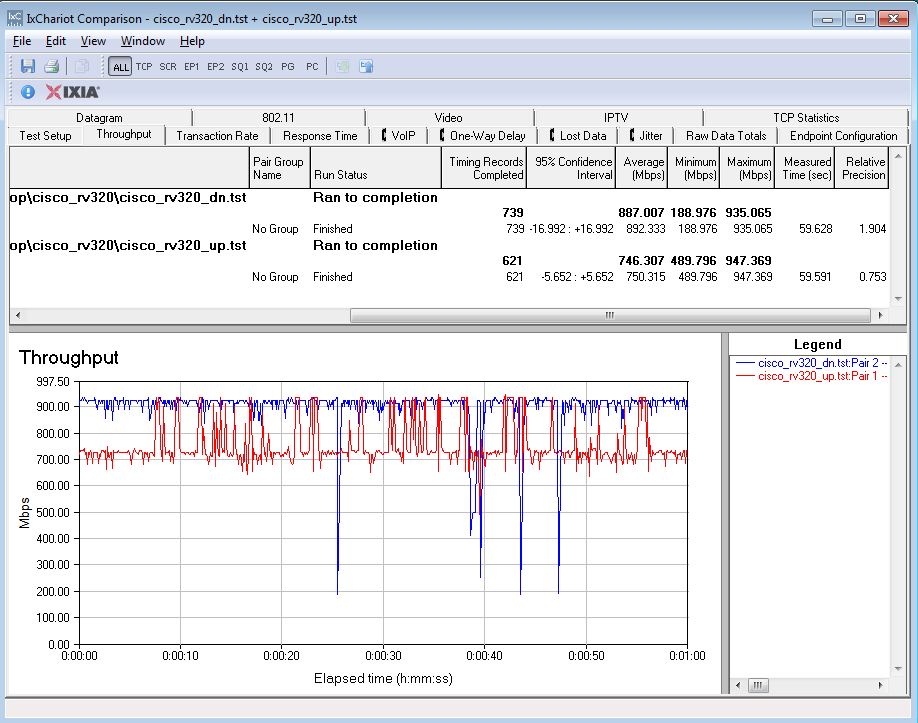
Unidirectional Throughput
Simultaneous up/downlink measured 832 Mbps.
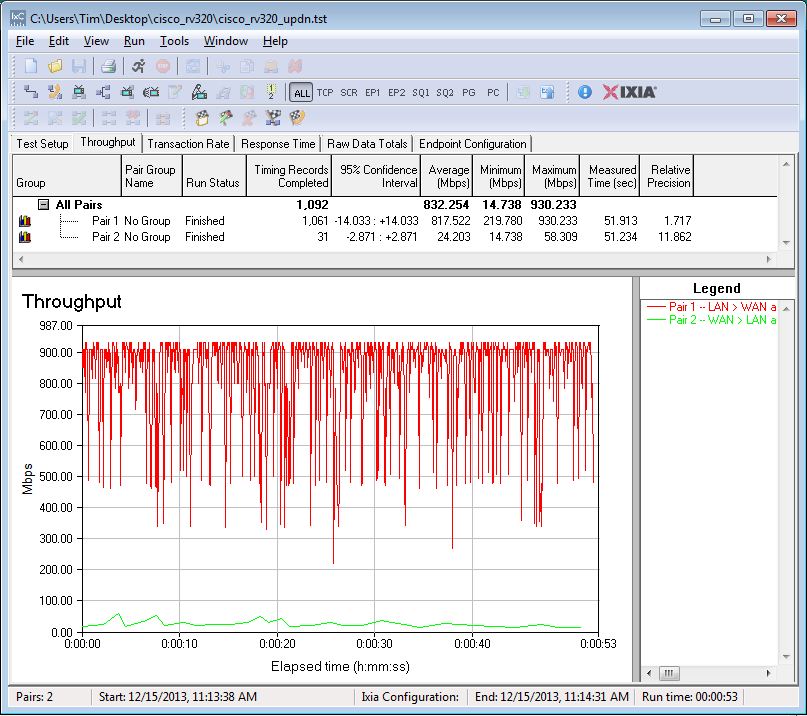
Bidirectional Throughput
Overall, these numbers are pretty good. The WAN-LAN throughput number puts the RV320 in the top 10 of our Router performance charts. The LAN-WAN throughput number puts the RV320 in the top 25. Total Simultaneous throughput puts the RV320 in the top 22. Interestingly, we measured the RV180 to be a bit faster than the RV320 in LAN-WAN and Total Simultaneous throughput.
I should note that getting best throughput performance required changing some router settings from their defaults, which is not our normal practice. But initial runs produced suspiciously slow throughput that caused us to check with Cisco to see if we were getting expected performance.
We had to disable Enable Network Service Detection (System Management > Dual WAN > Edit WAN) on both WAN ports and make the Bandwidth Management settings shown below to get simultaneous tests to complete.
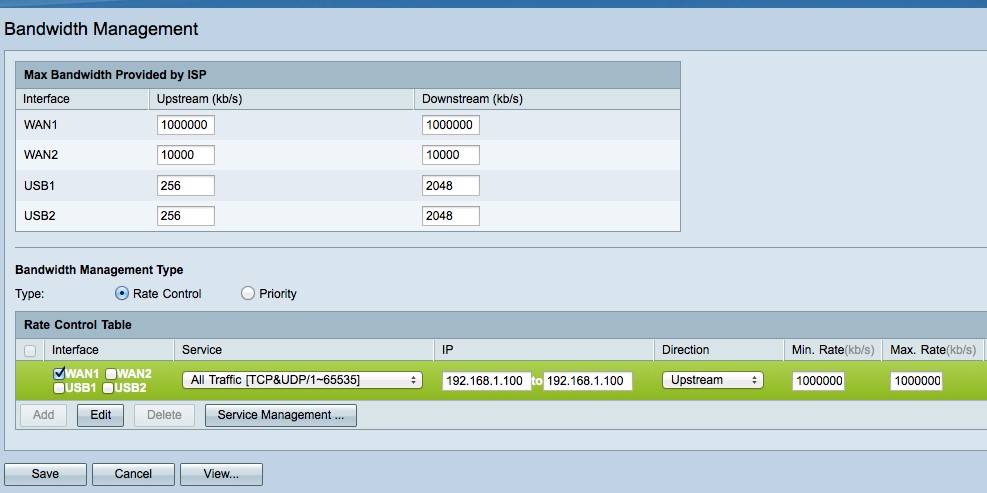
Bandwidth Rules for Maximum Connections Test
Normally, our maximum simultaneous test tool doesn’t require messing with router default settings. But, according to Cisco, hardware NAT acceleration is enabled when QoS rate control isn’t engaged. Entering the rules above shut off the acceleration and allowed the test to hit our limit. Of course, disabling hardware NAT would also reduce routing throughput.
Closing Thoughts
I’ve summarized key performance numbers and price for the RV320 and several other multi-WAN VPN routers I’ve tested in Table 5. The RV180 is not a multi-WAN router, but I included it in the table because I have referenced it previously in this review.
| Router | Throughput (Mbps) | Price | ||
|---|---|---|---|---|
| WAN-LAN | LAN-WAN | Max_IPsec | ||
| Cisco RV320 | 887 | 746.3 | 56.0 | $182.99 |
| Cisco RV180 | 798.3 | 811.2 | 50.9 | $108.00 |
| ZyXEL ZyWALL 110 | 662 | 420 | 185 | $354.75 |
| Cisco ISA550 | 200 | 255 | 91.6 | $224.99 |
| Cisco RV042 v3 | 89 | 91 | 47.5 | $164.59 |
| NETGEAR SRX5308 | 448 | 581 | 42.6 | $342.62 |
Table 5: Competitive comparison
At the beginning of this review, I listed prices for the RVxxx series routers. Among dual-WAN Cisco RVxxx routers, the RV320 costs just $6 to $18 more than the older and slower RV042G and RV042v3, so the price is pretty reasonable. The RV320 comes with a limited lifetime warranty, as do all Cisco RV series routers. And the RV320 has no monthly licensing fees, which is good.
As discussed, I ran into multiple minor bugs while testing the RV320, such as the Time menu lacking complete daylight savings adjustablility, mislabeled QoS menus, problems using the USB port to load firmware and the SSL VPN driver compatibility. None of these (except maybe the SSL incompatibilities) were show-stoppers and the router itself proved to be stable and never hung or needed to be rebooted. But I hope firmware updates can iron out these items, because they really shouldn’t be there.
I must admit, Cisco’s performance specs and a dual-core CPU gave me the expectation that the RV320 would be significantly faster than the rest of the RVxxx series routers. While the RV320’s VPN performance is faster than the other RVxxx routers I’ve tested and its router performance is faster than most of the other RVxxx routers, I still wanted to see more throughput. (Who doesn’t?)
Nevertheless, the Cisco RV320’s dual WAN, support for 3G/4G modems and flexible VPN capability is a pretty reasonable deal for less than $200.
