
| At a glance | |
|---|---|
| Product | Cisco Dual WAN VPN Router (RV042 v3) [Website] |
| Summary | New version of popular Cisco small-business VPN router |
| Pros | • Flexible Dual WAN ports • Dual-stack IPv6 support • Up and downlink priority and bandwidth QoS • 50 IPsec tunnels • Subscription content filtering option |
| Cons | • 10/100 vs. Gigabit ports • Admin access problem with Firefox / Windows |
Typical Price: $0 Buy From Amazon
Introduction
Updated 6/23/2011: Clarified port forwarding features
We first reviewed the Linksys RV042 back in 2007. Four years later, the Linksys branding is gone and the device is now the Cisco RV042 and in its third hardware revision. In fact, Cisco has changed processors and increased memory across its RV0XX line, hence this new look at the RV042 "v3".
The RV042 is still the little brother to the RV082 and RV016. They all still have 10/100 ports, both on the LAN and WAN, the difference being in the total number of LAN and WAN ports. The RV042 has 4 LAN, 1 WAN, and 1 WAN/DMZ port. The RV082 has 8 LAN, 1 WAN, and 1 WAN/DMZ port. The RV016 has 16 total ports, of which 8 are LAN, 5 can be LAN or WAN, 2 are WAN, and 1 WAN/DMZ port.
Physically, the RV042 is pretty much the same. It is still 5.1” across the front, 7.9” from front to back, and 1.5” high. In back of the RV042 are the WAN and LAN ports, as well as a recessed reset button. The front of the device has the indicator lights. Both the rear and front are shown below.
Figure 1: RV042 front and rear panels
The power connector is on the side of the RV042. There is no cooling fan, so it runs quiet. It has rubber feet for placing on a desk, as well as holes on the bottom for wall mounting.
Inside
As described in the New to the Charts article, the RV042 is powered by a 300 MHz Cavium CN5010, replacing the Intel IXP425-266 in the V1. RAM and flash have been bumped up to 128 MB and 32 MB, respectively, up from 32 MB and 8 MB in the original RV042. A Realtek RTL8309G switch rounds out the list of major components.
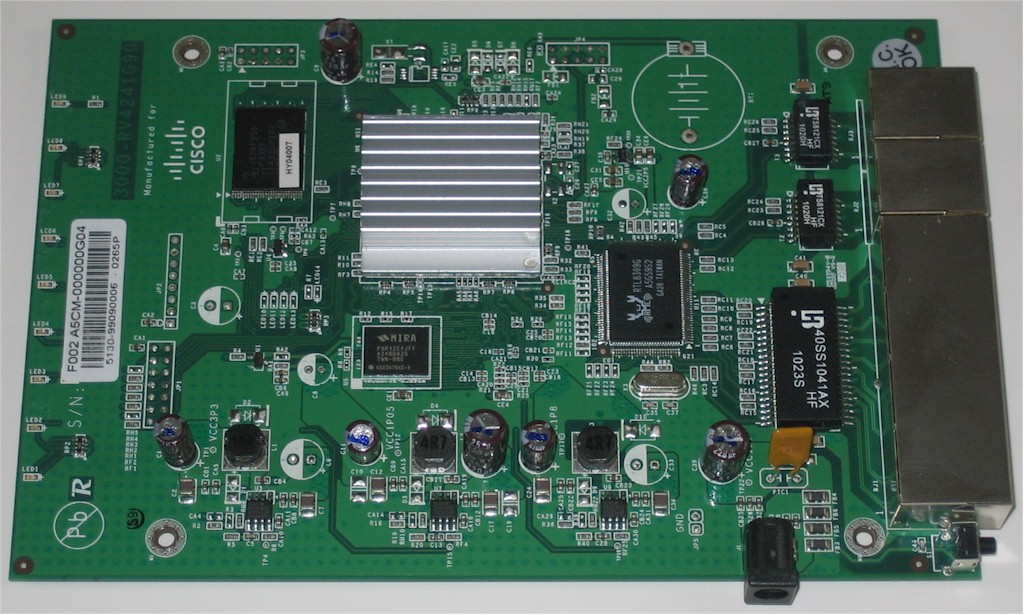
Figure 2: RV042 board
In Use
For 2011, the look and feel of the RV042’s menu has been updated, but remains intuitive and easy to navigate. There are 10 main menus on the left side of the screen, each with 1-11 sub-menus. Figure 3 provides a glimpse of the new Admin GUI.
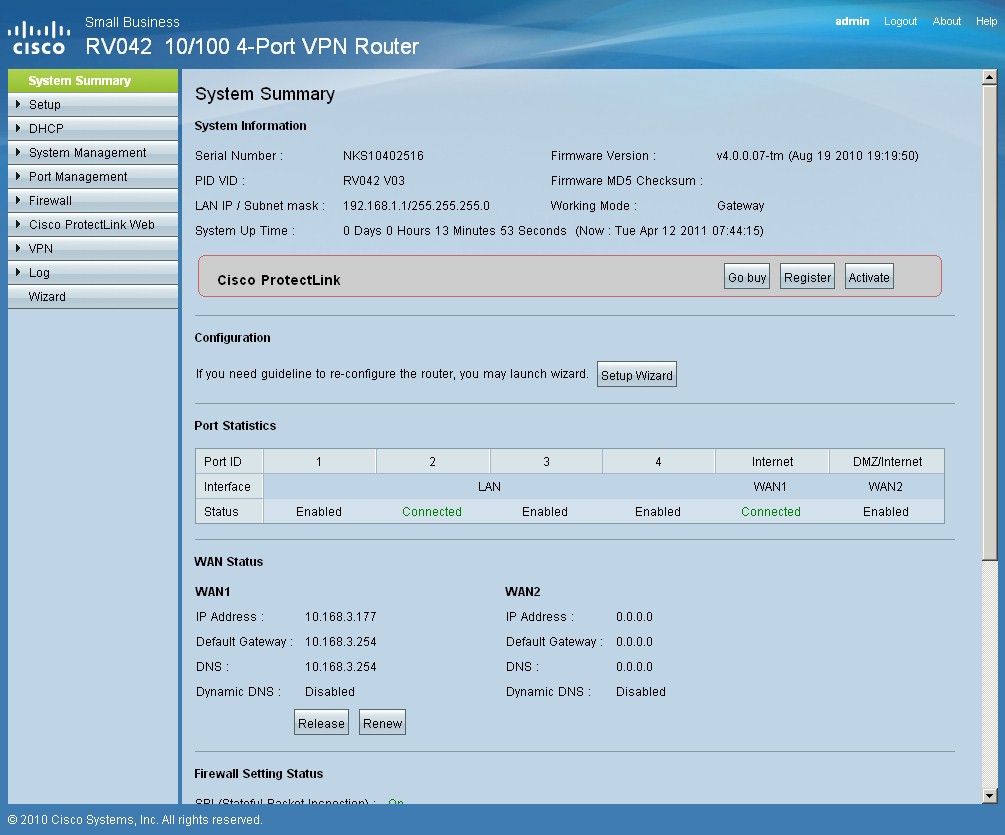
Figure 3: RV042 v3 admin interface
You configure the RV042 via a browser, but there is a known problem with Firefox. I had no trouble with IE8 and Safari connecting to the RV042, but the configuration pages were not completely displayed using Firefox on Windows. Cisco told me this is a known issue and they have resolved it in the next firmware release. I was able to use Firefox with the RV042 on a Linux machine without issue.
My 2007 review described support for multiple LAN subnets, which remains a feature in the v3. This feature allows you to use different subnets on your LAN, a useful and simple way to segment a small network.
The RV042 supports up to 4 port-based VLANs, but doesn’t support 802.1q VLANs. Port-based VLANS allows you to separate traffic by physical LAN port on the RV042, although all devices will be on the same subnet.
Dynamic DNS can be configured on both WAN ports. I had no problem configuring a Dynamic DNS account on WAN1. Dynamic DNS is a very useful service, especially if you don’t have static IP addresses from your ISP.
The RV042 supports RIPv1 and RIPv2 for IPv4 dynamic routing and RIPng for IPv6 dynamic routing. Static routes can also be added to direct traffic to specific next hop IP addresses. If the RV042 isn’t being used as a Gateway router to your ISP, it can be configured in Router mode, which disables NAT functionality on the router.
The RV042 supports multiple other networking protocols, including Universal Plug and Play (UPnP), Apple’s Discovery-Bonjour service, One-to-One NAT, and SNMP. IPv6 is a new networking feature in the 2011 RV042, which deserves its own section.
IPv6
IPv6 support in the RV042 was introduced in firmware 4.0.2.08. The manual for the RV042 hasn’t kept up with the firmware, though, because it lacks documentation on the RV042’s IPv6 features.
I recently reviewed the Cisco RV220W, which has extensive IPv6 support. The RV042 has fewer IPv6 options than the RV220W, and thankfully doesn’t require a reboot to enable or disable IPv6 as the RV220W does. The RV042 can run IPv4 only, or Dual-Stack IPv4/IPv6 mode.
Dual-Stack enables the router to support IPv4 addressing and IPv6 addressing, as shown in Figure 4.
Figure 4: IP mode selection
With Dual-Stack enabled, the RV042 can provide IPv6 addresses to devices on its LAN via DHCP or stateless auto-configuration. My test RV042 had a LAN IPv6 address of fc00::1. The RV042’s IPv6 DHCP default configuration dished out IPv6 addresses in the fc00::100-17f range. My PC was issued fc00::13c and I could successfully ping the RV042’s fc00::1 address.
Enabling stateless auto-configuration for IPv6 addressing tells the RV042 to advertise its IPv6 subnet in response to an IPv6 router solicitation multicast message. This method of IPv6 addressing can be more efficient than DHCP, as the router doesn’t need to maintain a list of IPv6 leases.
If using stateless auto-configuration, the RV042 will advertise the fc00::/64 prefix, enabling clients to construct an IPv6 address based on this prefix and their MAC address. With stateless auto-configuration enabled on the RV042, my PC gave itself an address of fc00::f2dd:f1ff:fe2b:5953, which is correct per the eui-64 standard and my MAC address of f0:dd:f1:2b:59:53.
The WAN interfaces on the RV042 support IPv6 addressing via static or DHCP. As a simple test, I used the Cisco RV220W, which also supports IPv6, to supply an IPv6 address via DHCP to the RV042. As you can see in Figure 5, the WAN 2 interface on the RV042 has an IPv6 address of fec0::100/64, which is from the range of addresses I configured on the RV220W.
Figure 5: WAN status showing IPv6
An additional IPv6 function on the RV042 is 6to4 tunneling, which facilitates IPv6 connectivity through an IPv4 network. Enabling 6to4 tunneling on the RV042 tells the router to advertise a 2002::/ subnet to LAN clients capable of 6to4 tunneling.
A 6to4 enable router has to add its own IPv4 address in the 2002 address it advertises. The WAN IP address on my RV042 was 166.82.189.193. 166.82.189.193 = a652:bdc1 in hex, and the RV042 correctly advertised the 2002:a652:bdc1::/64 prefix. (Isn’t IPv6 fun!?)
VPN
Cisco rates the v3 as capable of supporting up to 50 Site-to-Site IPSec tunnels, 50 Client-to-Site IPSec tunnels and 5 Client-to-Site PPTP tunnels. This is another upgrade from the 2007 RV042, which supported only 30 Site-to-Site tunnels and 10 Client-to-Site tunnels, plus 5 Client-to-Site PPTP tunnels.
According to Cisco’s specs, the RV042 can support all these tunnels simultaneously. There is a counter in the VPN status screen that shows the number of tunnels used and available. With both a Site-to-Site and Client-to-Site tunnel active, the counter showed 1 tunnel used and 49 tunnels available, indicating that Client-to-Site tunnels don’t count against the total number of supported Site-to-Site tunnels.
I set up all three connection types and verified they can be run simultaneously. As you can see in Figure 6, the top connection is an active Site-to-Site tunnel and the bottom connection is an active Client-to-Site tunnel.
Figure 6: Simultaneous client and site-to-site tunnels
In addition, I was able to run a PPTP tunnel at the same time as the Site-to-Site and Client-to-Site tunnels. PPTP tunnel status is displayed in the RV042 menu separately, shown in Figure 7.
Figure 7: PPTP status
Setting up a Site-to-Site tunnel was simple. I used a NETGEAR SRX5308 [reviewed] as the other end of the Site-to-Site tunnel. I configured both ends with 3DES encryption, SHA-1 authentication, Diffie Hellman Group 2 (1024 bit) key exchange, and Perfect Forward Secrecy (PFS) enabled. The RV042 also supports DES and AES-128, AES-192, and AES-256 encryption, as well as MD5 authentication.
Client-to-Site IPSec VPN tunnels are supported via Cisco’s QuickVPN Client, which you can download here. I used the latest version, 1.4.1.2. The RV042 manual also states you can use third-party VPN client software such as TheGreenBow.
Setting up a QuickVPN tunnel is a matter of adding a user name and password in the RV042 and installing the software on your PC. Cisco’s QuickVPN software actually runs on top of the IPSec software built into Microsoft Windows.
I had some inconsistent performance with the QuickVPN client with my Windows 7 PC. I had a couple instances where the client would time out without connecting. Cisco’s release notes for QuickVPN version 1.4.1.2 here provide some useful information. For Windows Vista and 7, you must have the Windows Firewall enabled for the QuickVPN client to work. Further, QuickVPN must be run with administrative rights. I found that disabling the Windows Firewall resulted in consistent failure of the QuickVPN client.
PPTP tunnels are one of the easiest of all remote access tunnels, a feature I noted on the 2007 RV042 and am glad to see is retained on the 2011 RV042. Enabling PPTP on the RV042 is a matter of clicking a check box to enable the PPTP server and adding user names and passwords.
No software needs to be downloaded or installed on Windows PC for a PPTP tunnel. From the Windows Network and Sharing Center, select Setup a New Connection or Network, then select Connect to a Workplace, enter the RV042’s WAN IP or Dynamic DNS name and the user name and password you created on the RV042, and you’re good to go.
Cisco rates the RV042 as capable of 59 Mpbs for IPSec VPN throughput. I used the Cisco QuickVPN Client to measure IPSec VPN throughput.
I tested the RV042’s VPN throughput with iperf using default TCP settings, a TCP window size of 8KB, and no other options. I ran iperf on two PCs running 64-bit Windows 7. (Running a simple iperf throughput test between two PCs uses the command iperf -s on one PC and iperf -c (ip) on the other PC.)
As you can see in Table 1, the RV042 didn’t measure up to its rated 59 Mbps throughput on any of my tunnels. But, relatively speaking, the RV042 made a decent showing for itself, nearly matching the recently reviewed Cisco RV220W, which didn’t measure up to its 90 Mbps for IPSec VPN throughput, either.
| RV042 v3 | RV042 v1 | RV220W | |
|---|---|---|---|
| PPTP WAN > LAN | 10.8 | – | 16.3 |
| PPTP LAN > WAN | 9.7 | – | 14.1 |
| IPsec WAN > LAN | 37.1 | 21.9 | 38.3 |
| IPsec LAN > WAN | 47.5 | 32.6 | 49.3 |
Table 1: VPN throughput (Mbps)
You can also see that the v3 is significantly faster than the original (v1) RV042. WAN-LAN throughput has improved a bit more than 70%, while LAN-WAN throughput is improved by 46%.
Dual WAN
The RV042 has two WAN ports, with the second WAN port useful for connecting to a second ISP or serving as a DMZ port.
The default for WAN2 is as a second ISP connection. The RV042 provides two options for managing dual ISP connections, Load Balancing (default) and Smart Link Backup.
The Load Balancing option allows you to use both ISP connections simultaneously and manage traffic flows over the two interfaces. Traffic flows are managed via the bandwidth settings on the RV042.
The bandwidth management feature allows you to define the upload and download bandwidth of each interface. You then have the option to control traffic flows over each interface by protocol type, as well as source and destination IP addresses. Specific traffic types can be bound to a specific interface and then allocated minimum and maximum bandwidths or prioritized as high or low. There are 19 pre-defined traffic types, and you can add custom traffic types as needed.
To test bandwidth management, I first measured my ISP connection via speedtest.net. My download was 11.35 Mbps and upload was 650 kbps as shown in Figure 8.
Figure 8: ISP connection speed
I then set up the bandwidth management rule shown in Figure 9 to limit throughput to a maximum download of 5 Mbps and upload to 200 kbps.
Figure 9: Bandwidth limits
I then re-ran the speed test. As you can see in Figure 910, the RV042 throttled traffic pretty close to my settings, limiting my download speed to 4.8 Mbps and upload speed to 170 kbps.
Figure 10: Speed test w/ bandwidth limits
Smart Link Backup allows you to designate one ISP as primary, the other as backup. This would be a useful setting if you wanted all traffic to go over the primary ISP and only use the secondary ISP in the event of failure.
Failover from primary to backup, and failback from backup to primary was nearly instantaneous. This is an improvement over the 2007 RV042, which lagged on reconnecting to the primary ISP. Packet loss was minimal (one ping in a continuous ping) when I disconnected the primary ISP connection. Upon reconnecting the primary ISP, a traceroute showed all traffic was again routing through the primary ISP connection within seconds.
The WAN2 interface can also be configured as a DMZ port or Transparent Bridge. A DMZ port requires you have multiple public IP addresses from your ISP, which then allows you to place a web server and other public facing devices outside the RV042’s firewall. The Transparent Bridge option enables using the DMZ port to connect to another segment of your internal network.
Firewall / Security
The RV042’s firewall feature set remains fairly standard, with the expected options for customization, displayed in Figure 11.
Figure 11: Firewall options
Additional firewall functionality includes designating a single host on the LAN in a DMZ, port forwarding and port triggering, rule-based firewall permissions, website black listing, and URL keyword blocking.
Setting up a single host on the LAN in a DMZ is different than designating the WAN2 interface as a DMZ port. Setting up a single host on the LAN in a DMZ essentially applies a port forwarding rule to send all unrecognized inbound traffic to the specified host. Designating the WAN2 interface as a DMZ port creates a different zone completely outside the firewall.
The RV042’s port forwarding and port triggering are also pretty standard. One note, the forwarding and triggering configuration pages seem like they should be under the Firewall menu instead of the Setup menu.
Updated 6/23/2011
The Firewall menu has three options, the general page shown in Figure 10, the ability to create access rules, and a simple Content Filter. The RV042’s access rule functionality allows or denies traffic based on source interface, traffic type, source and destination IP address and by a user defined schedule. There are 20 pre-defined traffic types (HTTP, FTP, SMTP,etc..), more can be added based on protocol (UDP/TCP) and destination port number.
There is a non-subscription based Content Filter in the Firewall menu that allows for creating a black list of specific URLs, as well as URL keyword blocking. Both of these lists can be applied on a user-defined schedule. If a user on the LAN browses to a listed URL or one containing a listed keyword, they will receive the below message. I added google.com to a URL black list and was presented with this message when I tried to browse to Google.
“This URLs or Page has been blocked.”
New to the 2011 RV042 is a more advanced subscription based Content Filter available via the ProtectLink feature. This feature enables website content filtering and web-reputation assessment to block web-based attacks and control web access. Website and web-reputation filtering is done through a partnership with TrendMicro.
The ProtectLink feature on the RV042 is similar to the feature I described on the RV220W, but without the email protection. On the RV042, the feature is called ProtectLink Web, while on the RV220W the feature is called ProtectLink Gateway.
Cisco provides a 30 day free trial of ProtectLink Web with the RV042. 1 year and 3 year licenses of ProtectLink Web are available via Cisco resellers. CDW lists a 1 year license for ProtectLink Web at $132.99 and a 3 year license at $194.99. Both licenses allow for unlimited users.
The ProtectLink Web Content Filter defines seveb web site categories, each with 7-19 sub-categories for a total of 83 different types of traffic. You can block one to all of these categories all the time or based on customizable schedules. Users browsing to any of the blocked categories will receive the message:
“The URL you are attempting to access has been blocked. Your organization’s policy prohibits accessing this web site.”
Another aspect of the ProtectLink Content Filter is web-reputation assessment, which blocks potentially malicious websites based on data collected by TrendMicro. You select whether to apply a security level of High, Medium or Low.
A security level of High will block most websites with questionable reputations, but also may have some false-positives, meaning it may block some acceptable websites. A security level of Low will block fewer websites with questionable reputations, but may have some false-negatives, meaning it will not block some malicious websites. The default setting is Medium.
The RV042 firewall also has the ability to create a white list of websites for those you want permanently approved and not subject to filtering. Similarly, you can create a list of "trusted" host IP addresses on the LAN that will not be subjected to filtering.
Routing Performance
The RV042 is a Dual WAN gateway router, so I grabbed data from our charts for other Dual WAN gateway routers. Interestingly, there are not many other non-wireless Dual WAN routers with 10/100 ports in our charts. However, the RV042 matches up closely to the Draytek 2920 and Netgear FVS336G, even though both have Gigabit ports.
Table 2 below shows the throughput numbers, IPSec Tunnel capacity and pricing. As you can see, the v3 RV042’s throughput is near line speed at about 90 Mbps in both WAN-LAN and LAN-WAN on 10/100 Ethernet ports. There is a significant throughput improvement over the original version, especially for WAN-LAN throughput.
The Gigabit NETGEAR FVS336G at about 59 Mbps WAN-LAN and LAN-WAN is actually slower than the RV042. However, the Draytek 2920 takes advantage of its Gigabit ports and produces higher throughput at 147 Mbps WAN-LAN and 136 Mbps LAN-WAN. The lack of Gigabit Ethernet, in my opinion, is a weakness of the RV042.
| WAN – LAN (Mbps) |
LAN > WAN (Mbps) |
Total Simultaneous (Mbps) |
# IPsec tunnels | Lowest Price | |
|---|---|---|---|---|---|
| RV042 v3 | 91.1 | 89.9 | 91 | 50 | $160 |
| RV042 v1 | 54 | 80.1 | 59.1 | 30 | $150 |
| NETGEAR FVS336G | 59.2 | 58/3 | 56.3 | 25 | $226 |
| Draytek Vigor 2920 | 147.5 | 136.5 | 147.3 | 40 | $190 |
Table 2: Router Performance comparison
Closing Thoughts
On the plus side, the RV042’s VPN tunnel capacity is highest of any VPN routers we’ve tested to date. The RV042 supports up to 50 IPSec Site-to-Site tunnels, plus 50 IPSec Client-to-Site and 5 PPTP Client-to-Site tunnels. And you’ll be able to take advantage of all those tunnels without worrying about breaking the bank. Because QuickVPN software and licensing for up to 50 users is now free on the RV042, where in 2007 it was $119, another nice change.
Another strength of the RV042 is its flexible Dual WAN functionality. A business or home dependent on connectivity cannot afford to have its Internet connection down for a significant period of time. The RV042 solves that problem. It can send and receive traffic over two ISP connections simultaneously, and provides multiple options for managing traffic flows over those connections.
The main disadvantages of the RV are its lack of Gigabit Ethernet ports and current admin interface problems with Firefox / Windows. The latter should get straightened out via new firmware at some point. But if you want Gigabit ports, you’ll need to add a switch or pick another product.
Overall, the RV042 v3 is a solid improvement over the original. The updated hardware design has improved both its VPN and Routing performance. And the addition of Cisco Protectlink for Content Filtering is also a plus.
I gave the original RV042 a thumbs up because it was extremely stable and reliable for me. I give the RV042 v3 a thumbs up as well. It’s faster, has more features and capacity, and retains the same ease of use I enjoyed in the original version.
