Introduction
For the person not familiar with DEFCON, it can be an overwhelming experience. DEFCON is unlike any typical convention that you might go to. It’s also a huge success. It was started thirteen years ago by Jeff Moss who goes by the handle “Dark Tangent” and has grown to a massive event with dozens of speakers and an audience of over five thousand people.
The activities include many contests and lectures, as well as many open discussions throughout the convention grounds. Both formal and informal discussion is aided by the DEFCON hotel (the Alexis Park Hotel in Las Vegas) being completely rented out by DEFCON attendees for the three days of the conference.

Because of this, it’s easy to talk to people and get involved in discussions as a community. All the talks were held in two of the large ballrooms and a tent the DEFCON staff setup in the parking lot with air conditioning. And if you ever got tired of going from lecture to lecture, you could watch the talks on DEFCON TV from the comfort of your own hotel room.
When I first learned about this convention a couple years ago, I wondered what it must be like. Seeing pictures and hearing stories, it sounded like a free-for-all with hackers running loose and terrorizing Las Vegas. Before arriving, I was still a little concerned about what I would be experiencing. Hackers and computer geeks have a reputation for not being the most sociable people and I didn’t expect to be let in that easily.
There was also the matter of the hacking. I thought that with this many experienced, knowledgeable people spending all their time trying to take down websites and cause terror on the Internet, there would be a lot of trouble at the event. I wouldn’t have been surprised if they shut down all electronic devices in the area, broke into casino computer systems, stole bank information, and then ran off to further exploit their powers!
In short, I felt that DEFCON had the potential to become a huge quagmire with nothing but destruction on its agenda. But what I learned after the three days of the convention was much different than my imagined story of terror.
My introduction to hacking
Since that hackers at DEFCON live in a different world, they take on alternate names or handles. Everyone at DEFCON has a handle and go by only that name at the convention. Names ranged from cool to goofy, depending on the person who came up with the name.
Since I am an intern at Tom’s Hardware, it was an obvious choice to be called simply “Intern.” The name also helped me fit in with my group since it made my role clear. I tried to help out with group activities and in turn, other members showed me around and gave me helpful advice.
I like the name Intern since it’s short, easy to remember, and catchy, so I’ll keep using it for my future DEFCONs. Other interesting handles from my group were KeLviN (Figure 1), Kallahar, Tacitus, and TwinVega. These handles were all unique and stood out during the convention.

Figure 1: KeLviN with his BIG DEFCON necklace
Since hacker handles are used so much, hackers’ real names are generally unknown. At first, I ran into problems when calling our Editor, Humphrey Cheung, “Humphrey”, instead of his hacker handle NOT5150. People looked at me with blank stares and asked, “Who is Humphrey?” Anonymity is further enhanced because the admission fee to DEFCON is paid in cash, providing no paper trail of a person’s attendance.
When I first arrived at DEFCON I was greeted by a group known as the Irvine Underground, IVU for short. IVU is a hacking group based out of Irvine, California, but which has also spread to other parts of California and the rest of the country. Part of their goal is to bring people together in a constructive manner, throwing away some of the elitism of other hacking or computer groups. The gang at IVU took me in immediately and showed me around DEFCON. They told me about the contests they were entering and the different convention activities that were worth checking out.
The Talks
From there I went to my first talk. I was surprised to see that it was actually about security and given by Phil Zimmerman (Figure 2), the founder of PGP. He talked about his new VoIP encryption system that he hopes to release in the coming year.
The system is installed on the phones of each client and produces codes unique to each user in order to set up a secure connection. A live demonstration showed a working model based on the open source VoIP client, Shtoom.

Figure 2: Phil Zimmermann talks on his cellphone
The next talk I went to was a discussion of a new product called Unicornscan, another piece of software aimed towards keeping things secure. It’s actually a program that allows network security staff to scan network logs and produce reports from which they can check for suspicious behavior. It’s mainly directed towards scanning TCP/IP activity, but includes many more features.
I was overwhelmed by the amount of information the creators of Unicornscan provided. I have no experience in IT or networking beyond setting up my home network, so it was a challenge to keep up with the talk. But even though I didn’t understand the specifics, I still felt they still did a good job of giving abstract descriptions of what they were doing. So when I left the discussion, I felt a little more knowledgeable about the general subject.
After Unicornscan I went to the Google Adwords hacking talk. This talk was much easier to follow and had techniques that anyone with an adwords account could apply. I wasn’t that interested in most of it, since it was mainly just novelty uses. But it was great to see how you could manipulate a service through experimentation.
Most of the issues the speaker covered were about getting around the censoring systems Google has in place to prevent promoting sites that promote hacking. He also gave tips on buying ads on words that can produce great results but are cheaper to buy on Adsense and simple exploits on misspellings.
More Talks
The highlight of the discussions was the Shmoo Group. The Shmoo Group is known throughout the hacker community as a leader, and is respected by everyone. The line to get into the talk went from the front to the back of the hotel, so I decided to watch it from my room – sitting on a nice couch instead of packed in the tent with standing room only.
There were a lot of very technical discussions which again mystified me, but there was also the Wi-Fi pistol (Figure 3) which can detect signals miles away.

Figure 3: Showing off the Shmoo Group Bloodhound Wi-Fi pistol
This device follows in the footsteps of last year’s gadget from the Flexilis group, the Bluetooth sniper rifle, which they used to wreak havoc on Bluetooth devices at last year’s DEFCON. The WiFi pistol matched this feat with its power to detect any access points within a few miles and then close in on them. The gun is not only powerful, but an amazing device to look at.
Some other topics Shmoos covered were encryption algorithms and flaws in different security programs. Even more impressive than the talk, however, was the respect the group received and how they covered a wide area of research and demonstrated their ability to be creative through hacking.
Lock picking draws a crowd
One thing that surprised me at DEFCON was the lock picking talks and competition. I hadn’t thought about the usefulness of lock-picking to a hacker. But the speakers pointed out that while being able to break into someone’s computer over the Internet is fine, you can do a lot more damage if you can actually gain physical access to a system.
The talks showed the ins and outs of lock picking and described the different tools and techniques that will thwart lock pickers. After all, DEFCON also concentrates on providing information and techniques on defending yourself against hackers.
An interesting story was how one lock company made a popular lock that a lock picker found a flaw in and told the company about it. Instead of trying to sue the picker or cover up the flaw, the company designed a new core for the lock and released it – much like a software company would release a patch. This story once again showed the value of hacking, uh, “flaw exposure”, as a means toward the goal of higher security. Along with lock picking were also discussions on safe cracking.
Even though these discussions were about breaking into things, they stressed the importance of using these tools to make better designs. Speakers also stressed that they do not promote use of the information they provided for illegal activities of any kind. Some even pursue these activities as a hobby, which was demonstrated during the lock picking contest.
The contest had about seventy contestants in all, with only three of those contestants making it to the second round. The event organizer said that last year, locks were being picked after five or six seconds, causing him to go through dozens of locks. So this year, he decided to step up the level of difficulty, but didn’t realize just how big a step he made.
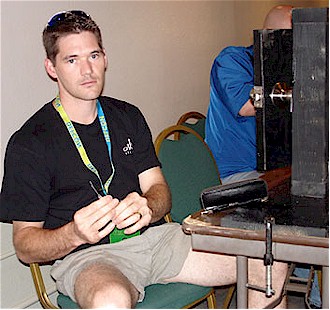
Figure 4: Gandalf wins the lockpicking contest
For the first round, competitors had ten minutes to pick a lock. The people who did it successfully completed the challenge in around three minutes. For the second and final round, the winner – a picker by the handle Gandalf (Figure 4) – picked the lock in about six seconds. The other two competitors continued their battle for over an hour until second place was decided. Not only were there a lot of contestants for the lock picking contest, but the turnout for people watching the contests and the talks was huge, with the Parthenon Ballroom packed with attendees.
The vendors selling lock picking supplies also sold out of all their merchandise. Lock picking was definitely popular and people are very interested in a hobby that they can afford and get into with a low degree of difficulty to start. It is also one of the few things at DEFCON that didn’t use a lot of technical jargon, in addition to being a fun activity to participate in.
More competitions
The lock picking competition wasn’t the only hard-fought contest. One of the great features of DEFCON was the number of activities that everyone could participate in. Along with the elite Capture the Flag and Wardriving contests, there were fun and quirky events such as the Coffee Wars and Scavenger Hunt.
Capture the Flag at DEFCON is unlike any you’ve played at the park. It involves teams of hackers all trying to break into a central server and each other’s servers while defending their own. This demands much more skill than any other competition, with the teams competing including some of the best hackers in the world.
The Wardriving competition involved teams tracking Wi-Fi signals while driving and walking around, requiring skills in hacking and tracking. One segment even included lock picking! The Wi-Fi shootout required teams to send and receive WiFi signals over a long distance. The winning team sent a signal that was captured 150 miles away in Utah.
The Robot Warez competition only had two teams, but showed off the power of robotics. The teams had to knock down soda cans with ping pong balls they collected over an obstacle course. The winning team used remote control for their robot and would have lost on points – had the other team had completed the course in time – because the ‘bot wasn’t fully automated.
The losing team’s robot operated completely on software and used a modified paintball gun to shoot the balls, and a camera to detect black circles below the cans in order to aim. It was an impressive robot, but knocked down its last can just after the time ran out.
Another device-oriented contest was the Beverage Cooling Contraption contest. Entries ended up not being contraptions as much as they were baths of super-cool liquids. One team used rubbing alcohol with chunks of dry ice to cool down to about minus 90 degrees Fahrenheit while another team employed liquid nitrogen to get the job done. Everyone who entered was successful in cooling the drinks in a matter of seconds.
One of the most entertaining contests was the Scavenger Hunt. Teams had to complete tasks and find items on a list and receive different point values depending on the task. Some of the challenges included bringing back a live chicken (Figure 5), duct-taping a teammate to a tree by the pool, making a suit of armor out of aluminum cans, or jumping up during a talk and screaming “I’m covered in bees!” and then running out of the room. All the items on the list had comedic value and everyone at the convention would break out in laughter even when reading the list.

Figure 5: One of the many items in the Scavenger Hunt
The Coffee Wars was another fun contest that anyone could compete in. The goal was to make a blend of coffee beans that tasted better than any other. They had a winner based on overall taste and a winner based on the cheapest roast. The judges enjoyed the tasting, but had a few regrets when the caffeine was too much to handle. The most popular contest was Hacker Jeopardy. It involved teams answering a range of silly pop culture and difficult computer junkie questions.
The contests showed the full range of the DEFCON experience. There were high-skill contests as well as light-hearted friendly competitions. People had fun in every contest and sportsmanship was high.
Closing thoughts
I found one of my biggest misconceptions about DEFCON was about the people. When someone talks about hackers or computer geeks, they usually never give a very positive description. Hackers are typically viewed as social outcasts who spend more time in front of a computer screen than out with friends.
This is dead wrong. Almost everyone I met was immediately friendly and opened up without any probing. The presenters, organizers, and contestants were all inviting and open to any discussion. The openness also proved how productive open discussion can be. There were many questions at every talk and when something was left unanswered, people would provide helpful input. This open discussion is why the computing community has grown to what it is. Newcomers like me can come into this existing community and learn just from being around these great people.

Figure 6: Jeff Moss, organizer of DEFCON, after being dunked with water during the closing ceremonies
I can’t describe how much fun I had at DEFCON and how much I learned. It was a completely new experience and I was able to immerse myself in something I knew very little about. The people were friendly, the talks were informative, and the contests mixed everything together. The organizers of this event did a great job producing an event that many people would think of as impossible.
The community is continually growing and DEFCON smoothly handled even the largest crowds. I left with new friends and a new sense of how security over the Internet works – which is really what this was all about. It wasn’t just about hacking, but a lesson in how we can all benefit from greater security and finding new ways to achieve it.
