Introduction
Intrusion Detection (ID) is the process of monitoring for and identifying attempted unauthorized system access or manipulation. An ID system gathers and analyzes information from diverse areas within a computer or a network to identify possible security breaches that include both intrusions (attack from outside the organization) and misuse (attack from within the organization).
An Intrusion Detection System (IDS) is yet another tool in the network administrator’s computer security arsenal. It inspects all inbound and outbound network activity, identifying suspicious patterns that may indicate an attack on the system. An IDS also acts as a security check on all transactions that take place in and out of the system. There are four main types of IDS:
Network intrusion detection system (NIDS)
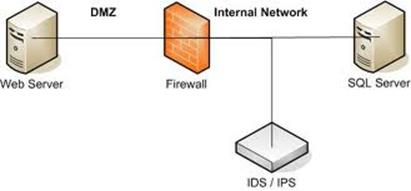
A NIDS is an independent platform that identifies intrusions by examining network traffic and monitors multiple hosts. NIDS gain access to network traffic by connecting to a network hub, switch configured for port mirroring or a network tap. In a NIDS, sensors are placed at choke points in the network, often in the network "demilitarized zone" (DMZ) or at network borders. Sensors capture all network traffic and analyze the content of individual packets for malicious traffic. An example of a NIDS is Snort.
Host-based intrusion detection system (HIDS)
A HIDS consists of an agent on a host that identifies intrusions by analyzing system calls, application logs, file-system modifications (binaries, password files, capability databases, Access control lists, etc.) and other host activities and state. In a HIDS, sensors usually consist of a software agent. Some application-based IDS are also part of this category. An example of a HIDS is OSSEC.
Intrusion detection systems can also be system-specific using custom tools and honeypots. In the case of physical building security, IDS is defined as an alarm system designed to detect unauthorized entry.
Protocol-based Intrusion Detection System (PIDS)
A PIDS is focused on ensuring the correct use of a protocol. A common PIDS use is on a web server to monitor HTTP activity.
VM-based Intrusion Detection System (VMIDS)
A VMIDS detects intrusions using virtual machine monitoring. By using this, we can deploy an Intrusion Detection System with Virtual Machine Monitoring. It is the most recent type and it’s still under development.
IDS vs. Firewall
Though both relate to network security, an intrusion detection system (IDS) differs from a firewall in that a firewall looks outwardly for intrusions in order to stop them from happening. Firewalls limit access between networks to prevent intrusion and do not signal an attack from inside the network.
An IDS evaluates a suspected intrusion once it has taken place and signals an alarm. An IDS also watches for attacks that originate from within a system. This is traditionally achieved by examining network communications, identifying heuristics and patterns (often known as signatures) of common computer attacks, and taking action to alert operators. A system that terminates connections is called an intrusion prevention system (IPS), and is another form of an application layer firewall.
Detection
All Intrusion Detection Systems use one of two detection techniques. A statistical anomaly-based IDS establishes a performance baseline using normal network traffic evaluations. It will then compare samples of current network traffic activity to this baseline in order to detect whether or not activity is within baseline parameters. If the sampled traffic is outside baseline parameters, an alarm will be triggered.
A signature-based IDS examines network traffic for predetermined attack patterns known as signatures. Many attacks today have distinct signatures. In good security practice, a collection of these signatures must be constantly updated to mitigate emerging threats. Signature comparison is also used in virus and malware detection.
Intrusions can present themselves in different ways. Here are some of them:
System Intrusions
- System failure in identifying valid user
- Active access to unused logins
- Login during non-working hours
- New user account created automatically
- Modification in system software or configuration files
- System logs are deleted
- System performance decreased drastically
- Unusual display of graphics, pop-ups
- System crashes suddenly and reboots without user interventions
File Intrusions
- Identifications of unknown files and program on your system
- File permission modifications
- Unexplained modifications in file size
- Identifications of strange file presence into system directories
- Missing files
Network Intrusions
- Identifications of repeated attempts to log in from remote locations
- Sudden increase in bandwidth consumption
- Repeated probes of existing services
- Arbitrary log data in log files
A network security administrator must take various precautions to defend the network from external or internal attacks. Some of these are:
- Frequently updating the antivirus signature database
- Configuring firewalls to filter out attacker IP addresses
- Configuring an audible alarm to signal an attack
- Forcing a TCP FIN or RST packet to terminate rogue connections
- Saving a trace file of raw packets for future analysis
- Saving the attack information (Intruder IP, victim IP, timestamp)
IDS vs. IPS
The traditional Intrusion Detection System is a detective technology; it only detects the anomaly in the network and notifies a concerned person. In contrast, an Intrusion Prevention System (IPS) is both detective and preventive technology.
Said differently, an IDS just makes a database of irregularities occurring in the inner network executed by the malicious hacker; it is not able to block the particular kind of attack. An IPS’ goal is to detect malicious activity and not allow the traffic to gain access to its target network. IDS is passive protection, IPS is active.
Conclusion
IDSes monitor hosts for system alteration or sniff network packets off the wire, seeking malicious intent. Security Administrators should contemplate using combinations of HIDS and NIDS, with both signature-detection and anomaly-based engines.
An Intrusion Detection System can be configured purely as monitoring and detection devices or it can participate as an inline device and prevent threats. Its biggest weaknesses are the high number of false-positives and the maintenance effort needed to keep signatures up to date and fine-tuned.
Ajay Yadav is a security researcher for the InfoSec Institute with a Masters Degree in Computer Science. He has attained numerous premier certifications in Information Security, Software and Database domain.
