Introduction

| Belkin 802.11g Wireless Network Access Point (F5D7130) | |
|---|---|
| Summary | Broadcom-based 802.11g wireless Access Point. 11g and WPA compliant. Also supports WDS-based bridging and repeating. |
| Update | None |
| Pros | • No WEP enabled performance degradation • 802.11g spec compliant • Supports WPA with optional AES encryption • Supports multi-point wireless bridging |
| Cons | • No monitoring or logging features • 15% throughput reduction in WPA-TKIP mode • Antennas are not upgradeable |
Belkin was one of the first companies to have 802.11g wireless products that were both 802.11g spec-compliant and supported Wi-Fi Protected Access (WPA) enhanced security. I found their F5D7130 802.11g Wireless Network Access Point to be a good entry into the hot and heavy 11g market, but not without its faults.
Basic Features and Internal details
The 7130 comes in an attractive grey-on-grey plastic enclosure about the size of a 300 page hardcover novel. It has mounting slots on the bottom and ships with a plastic stand that snaps on either end of the box to stand it vertically on your desktop.
All indicator lights are on the top front of the box on a panel that’s slightly sloped. They would be viewable in typical desktop mounting situations, but could be difficult to see if the 7130 were mounted high on a wall. The indicators include: Power, WLAN Link/Activity, and LAN Link/Activity. Both Link/Activity LEDs operate as you’d expect, steady for Link and flashing when there is activity.
The Ethernet 10/100 port and power jack are on the rear panel, along with a reset switch that does double duty as a reset-to-factory-defaults-switch.
The 7130’s design sticks pretty close to Broadcom’s AP reference design, using their BCM94306MP mini-PCI radio, Broadcom BCM4702 Wireless Network Processor for the processing chores, and RAM, Flash memory, and an Altima AC101 10/100 Ethernet chip for the LAN connection. Figure 1 shows the radio board with RF shielding removed.

Figure 1: Broadcom BCM94306MP mini-PCI ’54g’ radio
My internal exam also revealed that the Ethernet connector is wired for Power Over Ethernet operation, although Belkin is not specing or supporting the feature. I was disappointed, however, to find that the dual dipole antennas are not removable, so upgrading to higher gain antennas will be possible only for those willing to do some hacking… and kiss their warranty goodbye.
The last construction feature of note is an RF shield between the radio board and the processor that sits directly below it – probably a wise choice on Belkin’s part!
Setup, Administration, & Basic Features
Belkin doesn’t bother with supplying a software setup utility, opting instead to use the 7130’s browser admin interface for initial setup.
The AP comes set to 192.168.2.254 (subnet 255.255.255.0) as its factory default, so you’ll need to make sure the computer that you’re running the browser on is setup in the 192.168.2.X subnet.
TIP: Try setting your computer to 192.168.2.200 (or any other 192.168.2.X address except 192.168.2.254 ), subnet 255.255.255.0. You’ll probably need to reboot, too, or “Repair” the connection if you’re running WinXP.
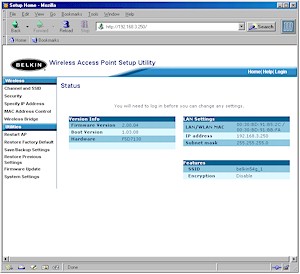
Once you get your computer and the AP in the same subnet, open your browser and enter the default IP address, and you’ll get the home screen shown in Figure 2.
Figure 2: Home screen
(click on the image for a full-sized view)
Note that I didn’t say you were first presented with a login prompt. Belkin has chosen to leave admin security for the 7130 wide open, presumably to make things easier for home users to set up. Although you could argue that Belkin’s choice of no password is essentially the same as having the common choices of “admin”, “1234”, “password”, etc. that other products use, I think it’s a less secure choice. In any case, password or not, anyone knowing the AP’s IP address can always view the Home screen, which although handy, is also not good security practice.
The interface is generally quick, with under 5 second saves for the changes you make on each page. A longer 10 – 15 second save is required when you make changes to the Bridging settings (more later). Multiple admin logins are not allowed, and you’ll get a warning that includes the IP address of the current administrator if you try. Once you’re logged in, there’s a default 10 minute idle timeout that you can change on the System Settings page, or you can use the Logout button when you’re done.
I should note that although you can change the 7130’s IP address and subnet mask, you can’t have it act as a DHCP client and automatically pick up its IP address from your LAN’s DHCP server. This isn’t that big an omission as it may sound, since I recommend statically setting the IP address of access points anyway so that you always know where to reach them.
Setup, Administration, & Basic Features, Continued
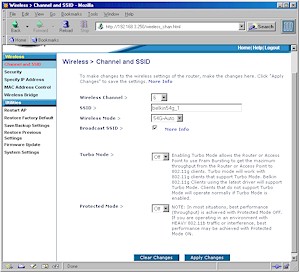
Clicking over to the Channel and SSID screen shown in Figure 3 presents you with your entire selection of wireless settings.
Figure 3: Channel and SSID Setup
(click on the image for a full-sized view)
The pickin’s are relatively slim compared to similar products, with the most significant omission being the ability to set the transmit rate. I was glad to see the Broadcast SSID checkbox, however, even though it doesn’t guarantee your AP won’t be found by wandering clients.
The other settings require a little bit of explanation, especially since Belkin’s printed manual doesn’t reflect the current firmware, and the downloadable versions aren’t much better (at the time of this review at least).
Wireless Mode – I’ll be happy once manufacturers agree on what to call the various operating modes that they provide for customers to puzzle over. Heck, I’d even settle for all the Broadcom-licensees using the same names! The 7130’s modes include the following choices:
54G-Auto(default), which allows both 11b and 11g clients to connect.
54G-Only will exclude clients that support only CCK rates. If a client advertises that it supports CCK and OFDM, i.e. it’s an 11g client, then it will be allowed to associate. Note that this mode will not prevent in-range 11b clients and APs from negatively affecting each other. 11b and 11g products sharing the same channel will act as 2.4GHz interference, degrading throughput and possibly causing more severe problems.
54G-LRS (Limited Rate Support) is intended to support “legacy” clients that can’t deal with APs that advertise supported rates in their Beacon frames other than the original 802.11’s 1 and 2Mbps. You can should use this setting only if you can’t get a client to connect in the other modes.
NOTE! The 7130 no longer has the 802.11b-only mode described in the printed User Manual.
Turbo Mode – This mode enables Broadcom’s Xpress throughput enhancement technology, which is intended to provide improved aggregate throughput performance primarily in WLANs with mixed 11b and 11g clients. More on this in the Performance section.
Protected Mode – This switch allows you to control the 802.11b protection mechanism that is part of the 802.11g standard. Belkin ships the 7130 with protection disabled (Off) by default. If you’re sure that you won’t be having any 802.11b visitors to your WLAN, it’s ok to leave this switch off. Otherwise, I recommend you turn it on to prevent to prevent your 11g traffic from getting clobbered by 11b stations.
Security
The 7130 was one of the first to support Wi-Fi Protected Access (WPA) for improved WLAN security. Figure 4 shows the WPA “Enterprise” mode setup, which requires using an external RADIUS server.
Figure 4: WPA settings
(click on the image for a full-sized view)
The 7130 also supports WPA’s “SOHO” mode, which is also known as WPA-PSK (Pre-Shared Key). I didn’t show this screen because all it has is an entry box for the 8 to 63 character key and a selector for Encryption method.
The encryption method selector is actually due to Broadcom’s choice of providing access to its hardware-based AES (Advanced Encryption Standard) encryption in addition to the TKIP encryption that is mandatory for all WPA implementations. AES is part of the full 802.11i (now known as WPA2) spec, but wasn’t included in WPA because its processing requirements would have killed the throughput of “legacy” 11b adapters that don’t have hardware AES encryption processors.
The 7130 also supports 64 and 128 bit WEP encryption if your wireless client’s WPA driver update isn’t yet available. But if you’re using any of Belkin’s 54g clients, forget about WEP and use WPA – it’s easier and more secure.
If you’re looking for the “Advanced” wireless settings typically found on other AP’s, don’t bother. This means that you can’t set Authentication Type, Beacon & DTIM Intervals, or RTS & Fragmentation Thresholds, nor can you adjust Transmit Power. These features probably won’t be missed by most home networkers, but sophisticated users might wish they were available.
Wrapping up the 7130’s security features is its Filtered MAC Address control. You can enter a list of client MAC addresses, which can all be either permitted or denied association with the AP. But the list can’t be saved or loaded to / from a file, and you aren’t given a pick-list of associated or in-range clients to ease the chore of creating your list.
Other Features
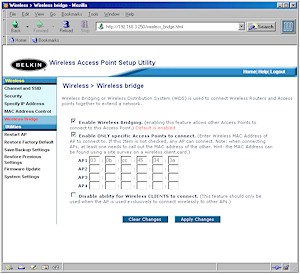
The 7130 provides both wireless bridging and repeating to up to four other WDS-based APs. Figure 5 shows the setup screen.
Figure 5: Wireless bridging controls
(click on the image for a full-sized view)
Although bridging it enabled by default, I couldn’t get it to work until I checked the “Enable only specific Access Points to connect checkbox” and entered the WLAN MAC address of the other AP into each AP. I left the “Disable ability for Wireless Clients to connect” box unchecked, but you’d check it if you wanted pure AP-to-AP bridging with no client connection.
I tried out this feature using two 7130s and it worked just fine. After getting both 7130’s setup and confirming that they were wirelessly connecting (I just unplugged one from its Ethernet connection and pinged its IP address), I left one connected to my LAN’s switch and moved the other to an upstairs room. I was able to connect my wireless laptop to either AP and keep a nice strong signal as I moved between floors.
I especially liked being able to still wirelessly connect to the admin pages of both APs while they were bridging / repeating instead of having to physically plug into their Ethernet jacks as is necessary in some other inexpensive repeaters. But, as with other wireless repeaters, you’ll lose about half your throughput for each repeater between your client and an Ethernet-connected AP.
Status and Monitoring
The biggest disappointment is the 7130’s total lack of monitoring capability. This means no Transmit and Receive stats, no logging, no list of associated clients… no nothin’! I asked Belkin whether they had any plans to correct this and the reply was “No plans for the near future”.
Wireless Performance
NOTES:
• SNR readings were taken from the Belkin client application
• Testing was done with a Belkin F5D7010 Cardbus client card in a WinXP Home Dell Inspiron 4100 laptop, unless otherwise noted.
Since the 7130 is the first spec-compliant 802.11g AP to hit the SmallNetBuilder test bench, I started to run many of the tests that I used to check previous draft-11g products. But I quickly discovered that there was not much difference between the 7130’s behavior and that of later Broadcom-based 11g products such as Linksys’ WRT54G router, which I had previously tested with late draft-11g (6.1) firmware. So I didn’t beat on it as much as I was going to, but still gave it a good workout.
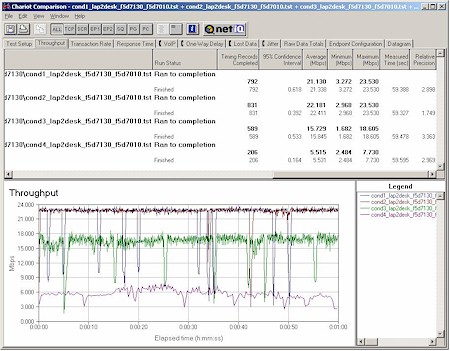
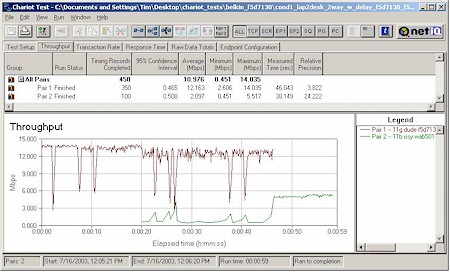
Figure 6: Four location 802.11g throughput comparison
(click on the image for a full-sized view)
Figure 6 shows the results of my four-location Chariot throughput test, which are reminiscent of those obtained from other Broadcom-based products such as Linksys’ WAP54G and previously-mentioned WRT54G. Range seemed similar to most good 802.11b and 11g products I’ve tested, but as you can see, the toughest (weakest signal) test location still yielded an average 5.5Mbps throughput – which is equal to the best-case performance of most 11b products.
Wireless Security
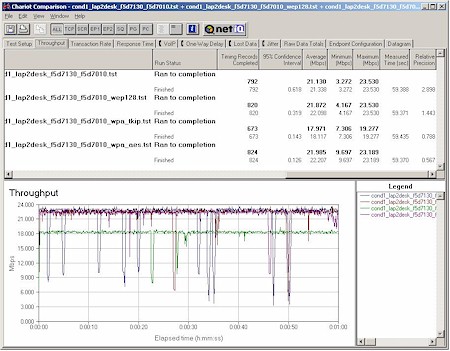
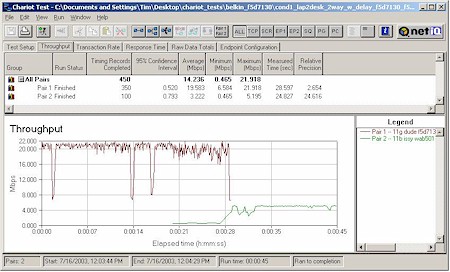
I then checked to see whether enabling WEP or WPA caused a throughput hit. Figure 7 tells the tale.
Figure 7: Normal, WEP, WPA throughput comparison
(click on the image for a full-sized view)
The results are a mixed good-news / bad-news story. The good news is that you don’t have to take a throughput hit when enabling either WEP or WPA-based security. The bad is that when using WPA you must use the AES encryption mode to avoid the 15% throughput reduction that you’ll get using TKIP encryption.
Since AES is not part of the WPA spec, it’s not supported by all WPA-compliant products, and WPA-enabled APs can’t simultaneously support both TKIP and AES WPA clients. So if you have an all-Belkin (or Broadcom-based) 11g WLAN, you’ll be ok using WPA with the optional AES encryption. But other product combinations could result in a WPA-enabled throughput hit.
Even with this issue, however, I still strongly encourage you to use WPA and not worry about the throughput hit. The improved security is worth it and 11g has bandwidth to spare for most SOHO users.
Turbo mode
Next up was checking Condition 1 performance using the Belkin card with Turbo mode enabled. Since “Turbo” / Xpress / frame-bursting is aimed at improving mixed WLAN performance, I didn’t expect to see any improvement with a single 11g client and that’s what I found. I did run some tests with one 11b and one 11g client, but since Broadcom disses Chariot-based testing for evaluating Xpress’ performance and also stresses that you need multiple 11g and 11b clients to really see Xpress’ advantage, I decided to put that testing aside until I discuss test techniques with Broadcom.
11b Protection
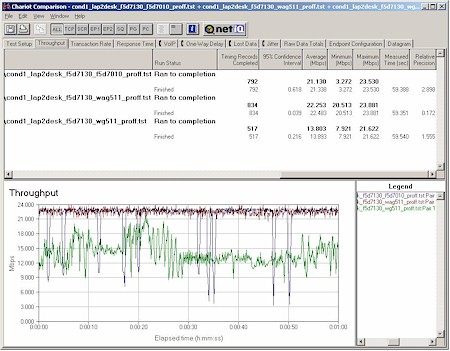
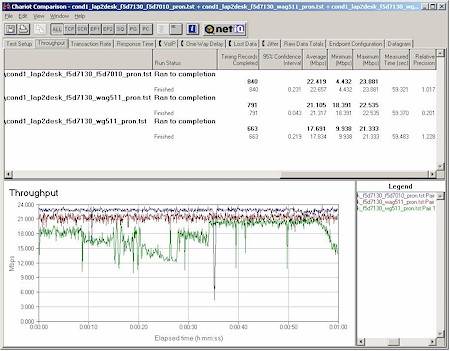
I also ran my closest-range Condition 1 tests on NETGEAR WG511 (Intersil GT), and NETGEAR WAG511 (Atheros 5001X+) cards with the AP’s 11b protection enabled and disabled to check for interoperability with other manufacturers chipsets. The results are shown in Figures 8 and 9, which compare Condition 1 results for the Belkin and two NETGEAR adapters in both protection modes.
Figure 8: Broadcom, Atheros, Intersil Condition 1 throughput – 11b protection off
(click on the image for a full-sized view)
Figure 9: Broadcom, Atheros, Intersil Condition 1 throughput – 11b protection on
(click on the image for a full-sized view)
Note that the Belkin (Broadcom) and NETGEAR WG511 (Intersil GT) adapters had 11g-compliant drivers installed, but the NETGEAR WAG511 (Atheros 5001X+) was run with its latest, but still draft-11g driver. I have no explanation for the WG511’s poorer performance and even ran the tests multiple times to see if I was seeing some sort of startup / warmup transient performance.
Note also that the above tests were performed with no 11b clients in range. Those test results are next.
802.11b Interoperability
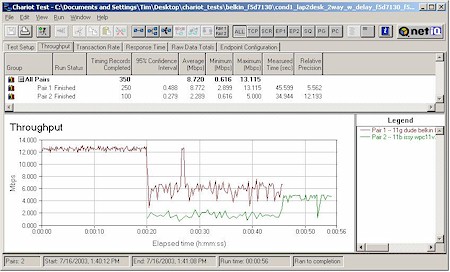
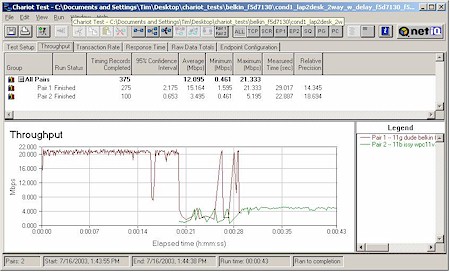
My last round of tests checked the handling of simultaneous 802.11b and 11g traffic. Again using Chariot, I set up a test using two client pairs. The reference 802.11g test pair for each test was a WinXP Home Dell Laptop with Belkin F5D7010 Cardbus card to Win98SE Ethernet client. The second pair used a WinXP Home Compaq Presario 1650 Laptop with various 802.11b cards to a different Win98SE Ethernet client. I tested the following cards:
- Linksys WPC11 v3 (Intersil PRISM III based card)
- NETGEAR WAB501 (Atheros 5001X dual-band chipset)
In each test, I started the Belkin card first, then kicked in the 802.11b card. Both cards then run simultaneously for awhile, with the Belkin card stopping first to let the 11b card finish by itself. As Figures 10 -13 show results with 11b protection enabled and disabled.
Figure 10: Two pair test, 11b protection enabled – Linksys WPC11 v3
(click on the image for a full-sized view)
Figure 11: Two pair test, 11b protection disabled – Linksys WPC11 v3
(click on the image for a full-sized view)
The results clearly show better “cooperation” between the 11g and 11b stations with protection enabled – as I’d expect – but with significant top-speed reduction for the 11g client with the 11b client associated to the same AP but idle. It also shows the price that might be paid for disabling protection when 11b clients are around, with the 11g station taking a much harder throughput hit when the 11b station starts transmitting.
By comparing the start of Figure 11‘s 11g plot with the top plot in Figure 9, you can see that even with protection disabled, the 11g client experiences a slight throughput reduction (about 1Mbps) when the 11b client is associated by idle. This says to me that even when the “official” 11b protection mechanism is shut off, Broadcom still has some sort of 11b detection mechanism running.
Figure 12: Two pair test, 11b protection enabled – NETGEAR WAB501
(click on the image for a full-sized view)
Figure 13: Two pair test, 11b protection disabled – NETGEAR WAB501
(click on the image for a full-sized view)
I included the WAB501 results in Figures 12 and 13 to show the variation in mixed WLAN performance that apparently still exists even in 11g spec-compliant products. The difference in interaction between the Broadcom, Intersil, and Atheros clients is striking, and probably why all vendors are pushing forward with their mixed-mode throughput enhancement technologies.
802.11g Wireless Performance Test Results
| Test Conditions
– WEP encryption: DISABLED |
Firmware/Driver Versions
AP f/w: |
||||
|---|---|---|---|---|---|
| Test Description | SNR (dB) | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
| Throughput (kbps) | Lost data (%) | ||||
| Client to AP – Condition 1 | 55 | 21.3 [No WEP] 22.1 [w/ WEP] |
1 (avg) 2 (max) |
499 | 0 |
| Client to AP – Condition 2 | 23 | 22.4 | 1 (avg) 2 (max) |
499 | 0 |
| Client to AP – Condition 3 | 10 | 15.8 | 1 (avg) 3 (max) |
499 | 0 |
| Client to AP – Condition 4 | 4 | 5.5 | 1 (avg) 2 (max) |
491 | 0 |
See details of how we test.
Wrap Up
My general impression of the the 7130 is that it’s a nice product, but with one fatal flaw. The complete lack of monitoring features is simply not acceptable for a wireless Access Point, and especially one with wireless bridging features. Wireless networks are hard enough to debug without depriving users of the ability to see whether their AP at least thinks a problem wireless client is connected, and the same goes for verifying bridging setups. Monitoring is not just for enterprise APs any more!
Potential buyers looking for the flexibility to add higher-gain antennas to solve wireless coverage problems will also have to take a pass, since the 7130’s dual dipoles are firmly fixed in place.
That said, I applaud Belkin for including both WDS bridging and repeating, giving it an edge over Linksys’ WAP54G, which supports only WDS bridging without allowing simultaneous client connection, i.e. repeating.
Kudos also to Belkin for having one of the first (if not the first) 11g product lines that is both 11g spec compliant and that supports Wi-Fi Protected access. Both features should help 11g fence-sitters finally take the plunge, should they not be concerned about the 7130’s limitations.