Introduction
| At a Glance | |
|---|---|
| Product | Cisco Wireless-N VPN Firewall (RV 120W) |
| Summary | Small-biz IPsec endpoint single-band N router with 10/100 ports |
| Pros | • IPv6 support • 802.1q VLANs • Easy to use VPN • Automatically changes LAN IP to avoid VPN problems |
| Cons | • Automatically changes LAN IP to avoid VPN problems • Doesn’t support L2TP / IPsec • Outbound only QoS / bandwidth control • Slower WLAN uplink throughput vs. downlink |
The Cisco RV 120W is an update to the Cisco WRV210 small business router. Like the WRV210, the new RV 120W is targeted at small networks needing IPsec VPN capability and a customizable firewall.
The RV 120W brings some updates to the Cisco RV series. The RV 120W includes an 802.11b/g/n 2.4 GHz wireless radio and 802.1q VLAN support vs. the 802.11b/g wireless radio and port based VLAN support on the WRV210. Other key improvements over the WRV210 are support for IPv6, content filtering, greater security controls, and enhanced traffic management.
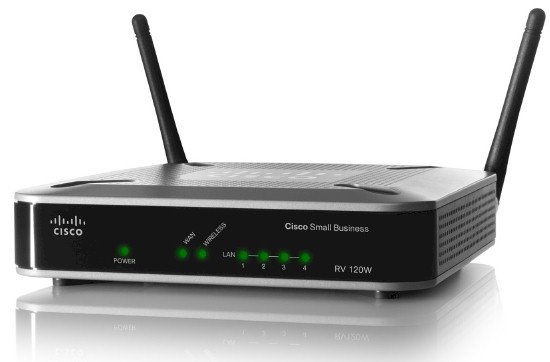
The RV 120W looks very similar to the WRV210. The RV 120W has a classic gray and black business look, with Cisco logos prominently displayed on the front and top of the unit. The front of the device has the indicator and port status lights, as shown in the product shot above.
The rear of the device, shown in Figure 1, has two non-upgradeable antennas, a reset button, the LAN and WAN Ethernet ports, as well as the power connector and a power switch. The power supply is a basic wall wart.
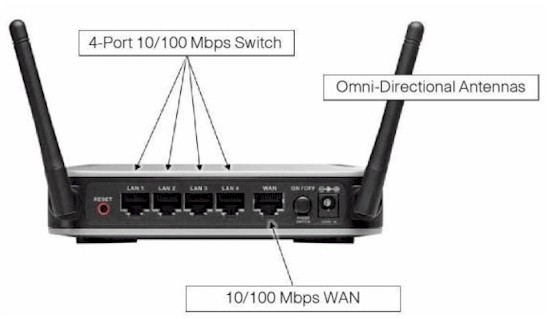
Figure 1: RV 120W rear view
The RV 120W is a small desktop device, measuring 5.9”W x 5.9”D. x 1.4”H. The device runs silent with no cooling fan. Inside the case is the motherboard and components, which were detailed in Tim’s New To The Charts article. The quick summary of the hardware is Cavium CN5010 CPU, Broadcom BCM5325 10/100 switch, 64 MB of RAM and 16 MB of flash.
Physically, the RV 120W is pretty basic. It’s the configuration options that make it interesting.
The volume of configuration options is deceptive. The menu is a simple web GUI with configuration options down the left side, as shown in Figure 2. At first look, it doesn’t seem like there are that many menus.
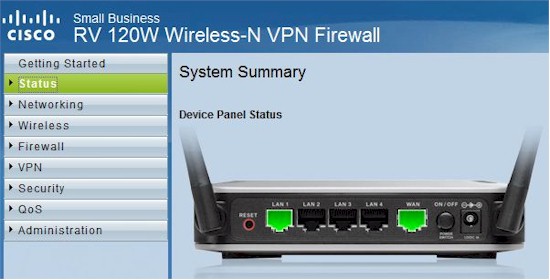
Figure 2: Admin GUI
There are 8 different menus that expand when you click on them. Each of the main menus has 2-12 submenus, and some of the submenus have another 2-10 more submenus. It all adds up to 101 different configuration screens.
Despite this abundance of options, I found the RV 120W relatively easy to configure. Sure, configuring the RV 120W is more advanced than configuring a Linksys/Cisco WRT or E series consumer router. But the choices are familiar and, for the most part, easy to figure out.
I spent a couple weeks with the RV 120W, and never crashed it. At times, there was a brief lag in menu responsiveness, but the router always responded.
I found the RV 120W to be more than a standard gateway router for connecting to the Internet and sharing an Internet connection. In addition to the typical functionality of most gateway routers, the RV 120W supports IPv6, Dynamic Routing, VPNs, Security, and a host of 802.x technology, including 802.1q VLAN, 802.11b/g/n wireless, 802.1X authentication, and 802.1p QoS. Let’s take a look.
IPv6
In an article from late 2010, John Curran, chief executive of American Registry for Internet Numbers (ARIN), stated 32 percent of ISP’s offer IPv6 services to business customers today. He went on to say 60 percent intend to have services within a year, and within two years, 80 percent.
Cisco has long supported IPv6 in its Enterprise grade devices; it’s nice to see Cisco include IPv6 for small network devices. Other devices, such as the D-Link DIR-825, Apple Airport Extreme, and devices using DD-WRT software have supported IPv6 for some time.
My ISP does not support IPv6, which is frustrating. I’ve emailed them several times and asked when they will support it, but I’ve never gotten an intelligent response. Personally, I can’t wait for IPv6 to gain traction and become widely used. My day job involves VoIP networking, and using IPv6 has the potential to resolve a lot of VoIP problems. Sure, deploying IPv6 will likely cause challenges and confusion, but I believe IPv6 will improve networking.
To use IPv6 on the RV 120W, you change its routing mode from IPv4 to IPv4/IPv6 mode, which then requires a reboot. This was surprising, as the devices listed previously don’t require a reboot to enable IPv6. Rebooting the RV 120W is a bit slow; it takes about 2 minutes for the router to completely restore.
Once the reboot is complete, you can enable various IPv6 options. An IPv6 address can be statically assigned to the WAN interface, or it can receive an IPv6 address via stateful or stateless DHCPv6. Likewise, on the LAN interface, you can set up the RV 120W to provide an IPv6 address via stateful or stateless DHCPv6.
Stateful DHCPv6 is akin to the DHCP services we’re used to with IPv4. Stateless DHCPv6 is where a device will learn its subnet from another router, but create its own IPv6 address based on the learned subnet and its own MAC using the EUI-64 format.
I set up a simple test where I used a PC connected to the WAN interface of the RV 120W and gave both the PC and WAN interfaces a static IPv6 address. I used 5001::1/64 for the RV 120W and 5001::2/64 for the PC. To test the functionality, I ran a simple ping from the PC to the WAN interface of the RV 120W, and you can see in Figure 3, my ping succeeded.
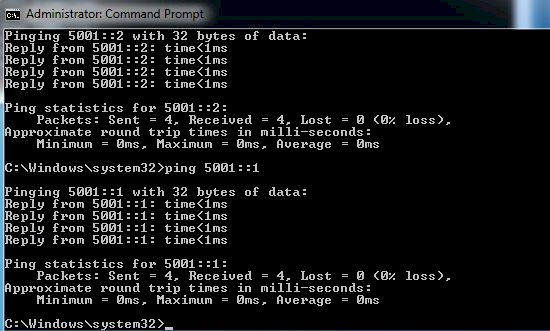
Figure 3: IPv6 ping test
I configured the LAN side of the RV 120W to be 4001::1/64 and set up its DHCPv6 server to run in stateful mode. I set up a DHCPv6 range of 4001::10 – 4001::1F on the RV 120W DHCPV6 server. My Windows 7 PC interface was set to obtain an IPv6 address automatically.
As you can see in Figure 4, my PC has both an IPV4 address and IPv6 address from the RV 120W. Note that the IPv6 address is 4001::10, which is the first address from the range I created.
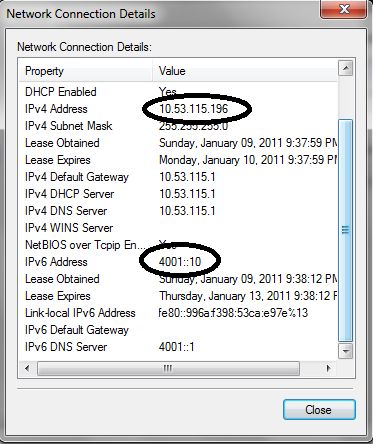
Figure 4: IPv4 and IPv6 addresses via DHCP
These two tests are pretty basic, but they show IPv6 functionality on the RV 120W. I’m not sure I’d use IPv6 today without an ISP connection that supports it, other than messing around with it on my LAN. However, for a small business, I think it is good Cisco included IPv6 functionality.
I mentioned the RV 120W supports dynamic routing. RIPv1, RIPv2, and RIPng are all supported if you’re going to use the RV 120W to exchange routing information with other routers. RIPng is the version of RIP for IPv6 routing.
VPN
The RV 120W has Remote Access VPN and Site-to-Site VPN capability. I found both quite easy to set up and use. Cisco lists their Quick VPN Client as the supported VPN client, which is available on a disk included with the router, as well as on Cisco’s website here.
Installing and configuring the client and router involved just two steps. First, I installed the client on a 64bit Windows 7 Pro laptop. Second, I configured a Quick VPN user name and password on the router.
Upon configuring a Quick VPN user name and password on the RV 120W, the router automatically changes its LAN IP address from 192.168.1.0/24 to 10.x.x.0/24. The LAN subnet is randomly created from 10.x.x.x. The first time I added a Quick VPN user name and password, the router configured its LAN subnet to 10.150.55.0/24. I defaulted the router two more times and re-added Quick VPN user names and passwords. One time, the router configured its LAN subnet to 10.124.31.0/24, the other to 10.53.115.0/24.
A common challenge on VPN tunnels is the subnets on both ends of a tunnel must be different. Thus, it is useful Cisco automatically changes the router’s LAN to a random subnet. However, if you’ve had the router in use for awhile, changing the LAN subnet can cause issues with your configurations, as per the warning shown in Figure 5. If you plan to use Quick VPN, I recommend you set up a Quick VPN user name and password right away.
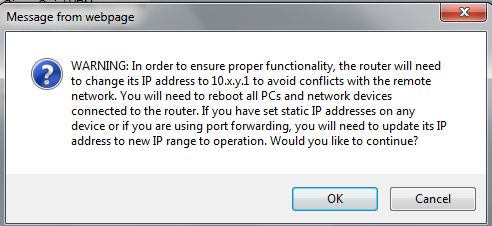
Figure 5: LAN subnet change warning
I also created a dynamic DNS address on the RV 120W so I could use a static address for remote access. The RV 120W supports dynamic DNS from DynDNS.com and TZO.com.
Once the Quick VPN client is installed and the user name and password are created on the router, you simply run the software, enter the user name and password and the IP or dynamic DNS address of the RV 120W, and click connect. An IPsec tunnel is then created to the RV 120W LAN and you’ll see a message on your PC like Figure 6 indicating your tunnel is successfully up.
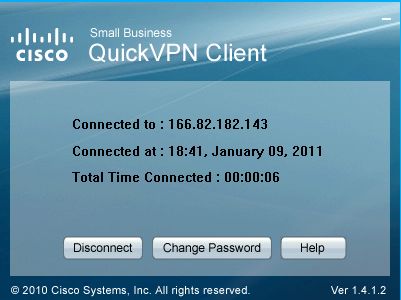
Figure 6: QuickVPN tunnel up
In all, the Quick VPN software is easy to use and stable. I used it to connect to the RV 120W LAN while traveling, and had no problem establishing a secure remote connection.
Site-to-Site VPNs are also easy to configure. I used a NETGEAR SRX5308 to test a Site-to-Site VPN tunnel with the RV 120W. Figure 7 shows the status screen of my active VPN tunnel.
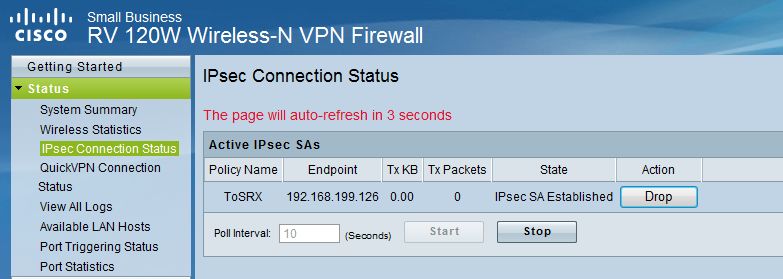
Figure 7: Site-to-site tunnel status
I found it remarkable that I was able to use the VPN Wizard on both the RV 120W and SRX5308 to successfully set up a tunnel. I’ve had success using VPN Wizards before, but I was surprised to find both Cisco and NETGEAR use the same settings in their VPN Wizards. (For the record, the default settings used by the RV 120W VPN are Main exchange mode, 3DES encryption, SHA-1 authentication, DH Group 2, and Perfect Forward Secrecy (PFS) enabled.)
Cisco rates the RV 120W at 25 Mbps for VPN throughput and that it can support up to 10 Quick VPN tunnels and 10 Site-to-Site tunnels.
I tested the RV 120W’s VPN throughput with iperf using default TCP settings, with a TCP window size of 8KB and no other options. (Running an iperf throughput test between two PCs to test throughput requires the command iperf -s on one PC and iperf -c (ip) on the other PC.)
I was pleased my tests verified Cisco’s ratings, as you can see in Table 1. I measured VPN throughput on the RV 120W at 21.2 – 23.1 Mbps on the Quick VPN connection, and 25.3 – 26.6 Mbps on a Site-to-Site VPN connection. (Note, the SRX5308’s VPN throughput is 38.1 – 42.6 Mbps, meaning it wasn’t a limiting factor in my tests with the RV 120W.)
| LAN-WAN (Mbps) |
WAN-LAN (Mbps) |
|
|---|---|---|
| Client VPN | 23.1 | 21.2 |
| Site-to-Site VPN | 25.3 | 26.6 |
Table 1: VPN throughput
The main downside for the RV 120W is that it only passes through L2TP. So when I tried to establish a tunnel to it from my notebook using Win 7’s built-in L2TP / IPsec VPN client, I couldn’t get it to connect. This would have been a bigger mark against it had not the free, bundled Quick VPN client worked as effortlessly as it did.
Firewall
The firewall on the RV 120W is customizable and intuitive to configure. Basic firewall configurations includes a check box page to enable/disable traffic blocking such as ICMP traffic to the WAN port and DoS checks such as TCP and UDP flooding. UPnP and a SIP ALG are also features that can be enabled or disabled.
More advanced firewall configurations involve controlling traffic between the three zones: WAN, LAN, and DMZ. Rules can be created to filter different traffic flows between zones based on traffic type, time of day, and source and destination IP addresses.
There are 63 different predefined traffic types. Additional custom traffic types can be defined based on TCP, UDP, or ICMP protocol and port. I created a custom traffic type for iperf traffic, which uses TCP and port 5001. Figure 8 shows a firewall rule I created to allow and forward iperf traffic from the WAN to a specific PC on the LAN side of the RV 120W.
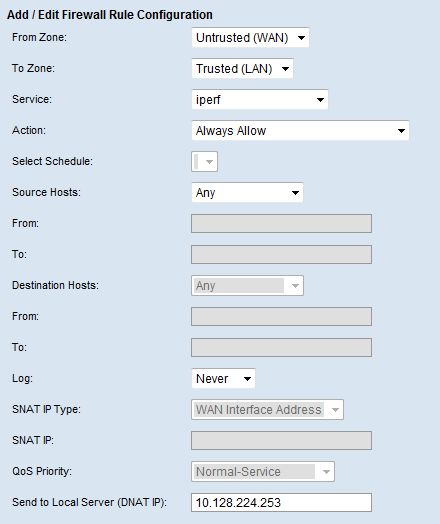
Figure 8: Firewall rule
The RV 120W also has content filtering capability. The RV 120W enables content filtering to block web components utilizing Java and ActiveX, as well as web sites that manipulate traffic via proxy servers, or those that track activities via cookies.
More detailed content filtering requires specifying which devices on the LAN will have content filtering applied and defining keywords. To specify which devices on the LAN will have content filtering applied, you create a list of the IP addresses whose traffic should be filtered called a LAN Group. Then, you define your keywords and apply the filter to the LAN Group.
Any keyword defined in the RV 120W and found in the website’s URL or web page will display the warning shown in Figure 9 instead of the offending website. In addition, a list of trusted domains can be created for websites where content should not be filtered.

Figure 9: URL keyword block alert
Keyword blocking is a basic means of restricting web traffic, but isn’t all that effective by itself. Keyword blocking will filter some sites depending on the list of words you build, but it won’t filter images or media. However, Cisco doesn’t claim that the RV 120W is a true Unified Threat Management (UTM) device. The RV 120W would have to be combined with a more advanced content filtering solution if comprehensive web filtering is desired.
Another interesting feature on the RV 120W firewall is One-to-One NAT. Per Cisco, “One-to-One NAT is a way to make systems behind a firewall that are configured with private IP addresses appear to have public IP addresses.” With this feature, and public IP addresses from your ISP, you can map a range of private IP addresses on your LAN to a range of public IP addresses on the WAN, even though the WAN interface has only one IP address.
When One-to-One NAT is fully configured, outbound traffic from devices with private IP addresses in the defined range will appear to be coming from one of the configured public IP address. Inbound traffic that matches one or more of the predefined or custom traffic types and has a destination of one of the public IP addresses will be mapped to the corresponding private IP addresses.
VLAN
In my review a couple of years ago of the Linksys RV042, I noted the RV042’s support for multiple LAN subnets, but was disappointed the RV042 didn’t support 802.1q VLAN tagging. Even the newer Cisco WRV210 doesn’t support 802.1q tagging. So it’s nice to see the RV 120W supports 802.1q VLANs.
On the RV 120W, VLAN IDs can be assigned from 1-4094, with up to four active VLANs. With VLANs enabled, multiple subnets are created, one per VLAN. In addition, the RV 120W will create a DHCP server for each subnet. Finally, each port on the RV 120W can be configured as access, general, or trunk.
An access port on the RV 120W is a member of a single VLAN. A general port on the RV 120W is useful when connecting to a VoIP device. If a VoIP device is connected to a general port on the RV 120W, and the VoIP device supports tagging and has a PC connected to it, the untagged traffic from the PC connected to the VoIP device will be assigned to the port’s VLAN ID, separate from the VoIP VLAN. Finally, a trunk port on the RV 120W can connect to another VLAN capable device that supports 802.1q trunking.
To test access ports, I added VLAN 2 to the RV 120W and configured port 2 to be an access port on VLAN 2, I noticed the router automatically created a new subnet, 192.168.2.0/24 for VLAN 2, different from the default subnet of 192.168.1.0/24. Figure 10 shows the subnets assigned to each VLAN. I connected a PC to port 2 and it received an IP address from the 192.168.2.0/24 subnet, as expected.
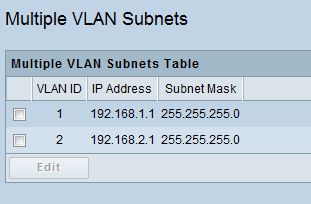
Figure 10: VLAN subnets
To test trunking, I configured port 3 on the RV 120W to be a trunk and a tagged member of both VLAN 1 and 2. I then connected port 3 of the RV 120W to port 3 of the recently reviewed LG ES-2026 smart switch. On the LG, I configured port 1 as a member of VLAN 1, port 2 as a member of VLAN 2, and port 3 as a trunk. I was pleased to see a PC connected to port 1 on the LG got an IP in the 192.168.1.0/24 subnet from the RV 120W, and a PC connected to port 2 on the LG got an IP in the 192.168.2.0/24 subnet from the RV 120W, validating 802.1q trunking/tagging.
The VLAN functionality of the RV 120W is not limited to just wired networks. It is also useful with wireless networks, which I’ll describe next.
WLAN
The RV 120W has a flexible single-band 802.11b/g/n wireless radio that supports up to four different wireless networks. Each wireless network can have a different SSID which can be hidden or broadcast. Further, each RV 120W wireless network can utilize different security protocols (WEP, WPA, WPA2), and can be a member of a different VLAN.
The RV 120W can also be configured to support 802.1X authentication using an external RADIUS server for devices on both the LAN and WLAN.
Having multiple wireless SSIDs is pretty useful. A hidden, private and secure wireless network can be set up for internal use. A separate, open wireless network can be set up for guest access. Additional wireless networks can be set up for other purposes. Since each wireless network can be on a different VLAN, traffic from each wireless network can be filtered by the firewall. For example, a network administrator could block guest wireless clients from secure areas of the network.
I did some basic tests, enabling multiple access points on the RV 120W and assigned each to a different VLAN. I configured each access point with a different VLAN and different security setting, as shown in Figure 11.
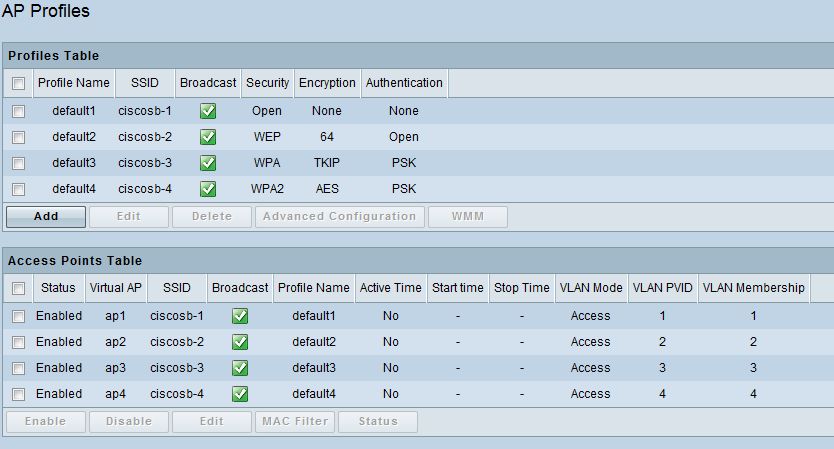
Figure 11: Multi-SSID configuration
I was able to use my Window 7 laptop to connect to each of the different SSIDs. I entered the appropriate security code for WEP, WPA, or WPA2 and was able to surf.
QoS
Bandwidth controls on the RV 120W are pretty granular. Bandwidth controls can be applied to outbound traffic flows based on traffic types.
Profiles are created to define traffic priority (low, medium, or high) or rate limits based on minimum and maximum bandwidth values. Finally, Traffic Selectors are created where profiles are applied to traffic types based on the IP addresses, MAC address, RV 120W port, VLAN, DSCP code, or wireless LAN.
To test, I used my previously created custom traffic type for iperf. I set up a profile with a traffic limit of 100-1000 Kbps, and applied my profile to iperf traffic originated from VLAN 1.
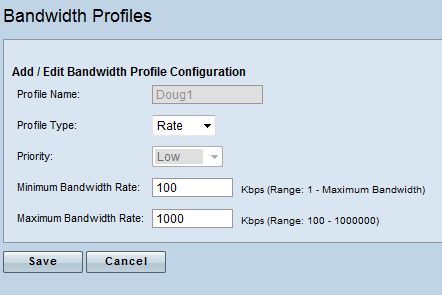
Figure 12: Bandwidth rate limiting
Figure 12 shows a screen shot of the profile I created, and Figure 13 shows the Traffic Selector I created to apply my profile.
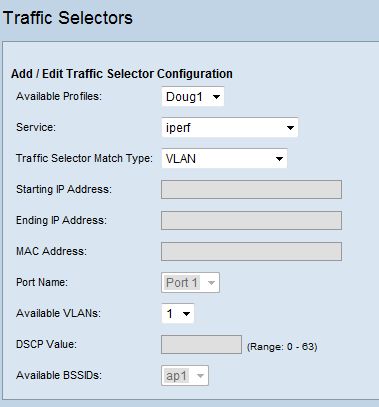
Figure 13: Traffic selector
I then ran a few iperf tests, again using the defaults as described in my VPN testing. With the above selector disabled, my iperf throughput was over 50 Mbps. With the above selector in place, my iperf throughput was limited to 912 Kbps, pretty close to the 1000 Kbps limit I set, proving the selector limited the desired traffic when enabled. In short, bandwidth management worked as expected.
If you want to prioritize traffic instead of apply rate limits, the RV 120W supports 802.1p traffic prioritization. This feature uses traffic marking based on CoS and DSCP values and assigns traffic to low, medium or high priority queues. VoIP traffic, which is often assigned CoS value = 5, and/or DSCP value = 46, could be assigned to the high priority queue to ensure that it always gets through.
Last, the RV 120W supports traffic metering. Some ISPs are going to a metered service, where if your network utilization exceeds a certain amount, you can be charged by the MB for the overage, similar to the pricing model of many 3G and 4G WWAN services. The RV 120W allows for metering and blocking traffic if your Internet usage exceeds anywhere up to 99,999 MB per month. Even if you don’t want to limit your traffic, enabling this feature in unlimited mode allows you to measure your monthly outgoing and incoming traffic volume by MB.
Performance
Testing and analysis by Tim Higgins
As described in our New To The Charts article on the RV 120W, at just shy of 90 Mbps, routing performance isn’t the highest we’ve tested, but perfectly adequate for many broadband connections. While spec junkies may like having a router with hundreds of Mbps throughput for bragging rights, all that extra throughput doesn’t do anything when used with slower Internet service.
Figure 14 is a screenshot of the Router Charts’ WAN to LAN benchmark, filtered to show only Cisco and Linksys routers, so you can see where the RV 120W ranks.
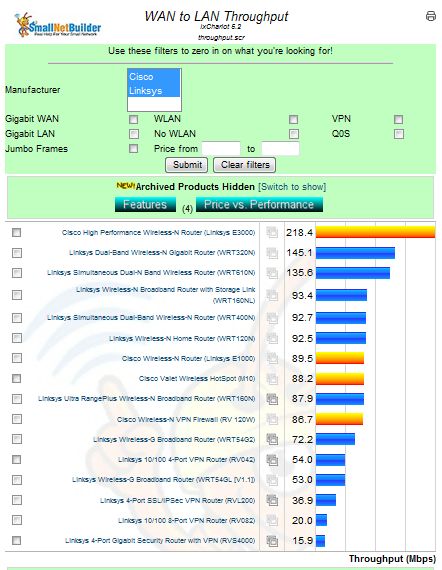
Figure 14: WAN to LAN throughput chart
Table 2 lists the router performance for the Cisco RV 120W along with the Cisco E1000 and E3000, as well as two IPsec VPN routers, the Draytek 2130n and the NETGEAR FVS318G.
| WAN – LAN (Mbps) |
LAN – WAN (Mbps) |
Total Simultaneous (Mbps) |
Maximum Connections | |
|---|---|---|---|---|
| Cisco Linksys E3000 | 218.4 | 249.4 | 257.5 | 12,277 |
| Cisco RV 120W | 86.7 | 86.6 | 136.3 | 12,086 |
| Cisco Linksys E1000 | 89.5 | 90 | 88.1 | 8,192 |
| Draytek 2130n | 638.2 | 691.1 | 765.7 | 16,384 |
| NETGEAR FVS318G | 22.5 | 22.9 | 25.8 | 200 |
Table 2: Routing Throughput comparison
The RV 120W beats the NETGEAR across the board, but lags way behind the Draytek, which has Gigabit WAN and LAN ports. Note, however, that the 2130n provided a little over only 1 Mbps of 3DES encrypted tunnel throughput.
We’ve tested only one other VPN router with built-in 802.11n radio, again the Draytek 2130n. So that’s what’s compared in the Wireless Performance Table in Figure 15.
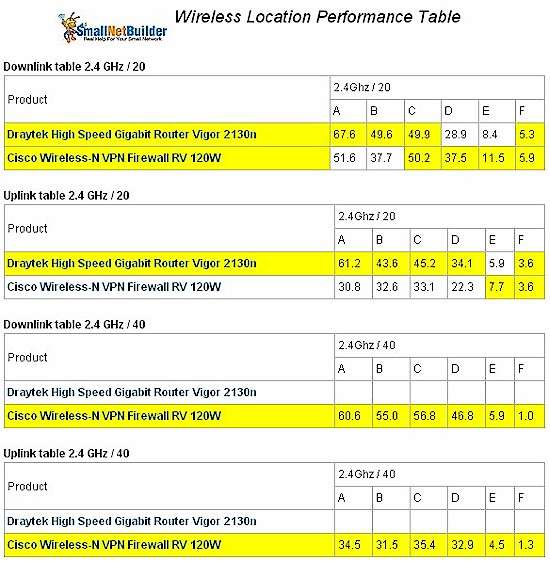
Figure 15: Wireless performance comparison
The Draytek and Cisco have similar downlink throughput. But the Draytek is faster running uplink with a strong to medium signal. The RV 120W is the winner in 40 MHz bandwidth mode because the 2130n doesn’t support that mode.
Closing Thoughts
There are a lot of Linksys/Cisco routers in the wild and I’ve worked with many different models. So, I found the configuration and feel of the RV 120W familiar and intuitive. Moreover, testing the RV 120W was a pleasure. The manual is relatively clear and the RV 120W functioned as the manual and specs said it would.
Cisco has loaded the RV 120W with some significant strengths. I love the fact that IPv6 is included and the firewall is highly customizable. I also found the VLAN functionality solid, and the VPN capability easy to configure and use and stable in use. The single-band 802.11n wireless is an overall plus with its four SSID support, even if its uplink throughput is a bit weak. And routing and VPN throughput will make the most of bandwidth available to many small business users. The main downside on the wired side is the 10/100 Ethernet ports. But that’s nothing that a small uplinked Gigabit switch can’t solve.
Table 4 highlights features and pricing details for the RV 120W and NETGEAR and Draytek routers previously compared.
| IPsec tunnels | Gigabit Ports | WAN Ports | Price | |
|---|---|---|---|---|
| Cisco RV 120W | 20 | No | 1 | $134 |
| Draytek 2130n | 2 | Yes | 1 | $180 |
| NETGEAR FVS318G | 5 | Yes | 1 | $129 |
Table 4: Price comparison
It’s obvious that the RV 120W looks like a pretty good deal, especially when you consider that the NETGEAR doesn’t have wireless built in and includes only one license for its IPsec client.
Bottom line, the Cisco RV 120W has the right mix of performance, features, support, ease of use and, let’s face it, the Cisco name that will make it a popular choice for many small businesses in need of a reliable and easy-to-use IPsec router.