Introduction
| DrayTek Vigor 2900 Series Broadband Security Router | |
|---|---|
| Summary | PRISM GT-based wireless 802.11g router. Has PPTP, IPsec, L2TP VPN endpoint, which also supports wireless clients.Has VLAN and Bandwidth control features Also available w/o wireless and with ISDN WAN |
| Update | 10/24/2005 – Updated U.S. vendor info |
| Pros | • Includes both VLAN and bandwidth limiting features • 10Mbps PPTP tunnel throughput • Unique combination of features, especially VPN |
| Cons | • User interface needs better navigation • VLAN and bandwidth limits do not apply to wireless • A work in progress |
DrayTek gained some notice as the first (and only) company to produce a broadband router that connects to DSL modems with USB outputs. I’ve been in search for a consumer-priced router with bandwidth management capabilities for some time now and it appears that Draytek has produced another first.
The Vigor 2900G Broadband Security Router combines a four port VPN-endpoint router, 802.11g wireless access point and LPR-based USB print server. That in itself is a first, but there are more surprises in store once you start digging into the 2900G’s wide array of features.
There are actually four products in the 2900 series. The 2900 drops the 2900G’s wireless capabilities, while the 2900i and 2900Gi add integrated ISDN terminal adapters to their non-“i” siblings’ capabilities. Note the ISDN versions are not available in North America.
Internal Details
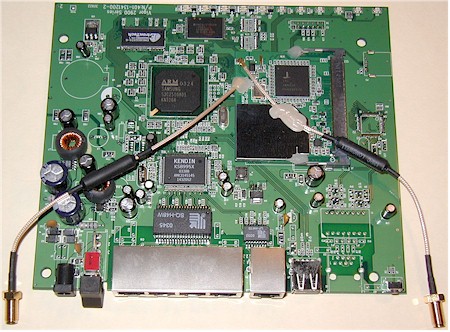
The 2900G’s board has a clean layout and surprisingly small parts count. It’s powered by a Samsung S3C2510A 16/32-bit ARM9-based micro-controller with 2MB X 32 of RAM and 16Mbit of flash and a Kendin / Micrel KS8995X 5 Port 10/100 Integrated Switch providing the Ethernet and switch functions.
Figure 1: The 2900G board
(click on the image for a full-sized view)
The radio is a mini-PCI design based on Conexant’s 802.11g PRISM GT chipset, which is cabled to two RP-SMA style connectors that connect to dual jointed dipole antennas.
Of note is the fact that the Samsung processor has built-in hardware DES and 3DES encryption, which helps the 2900G achieve surprisingly fast VPN tunnel throughput (more later).
Setup and Administration
The 2900G comes set to 192.168.1.1 as its factory default and with its built-in DHCP server enabled. It also comes without a default password set, so when the login authentication box pops up, all you need do is hit return and you’ll be at the Home screen (Figure 2).
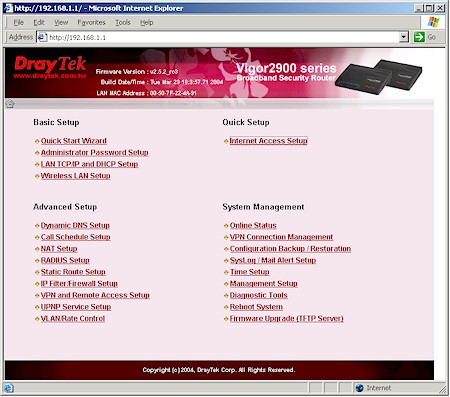
Figure 2: Home screen
Providing an understandable and easy-to-navigate interface is important in order for users to take advantage of all that the 2900G has to offer. Unfortunately, DrayTek has a ways to go to achieve this. While the Home screen presents links to all the major functional groups, you’ll be visiting it a lot because the 2900G’s interface doesn’t have a navigation bar that appears on each screen.
You instead navigate around using your browser’s Back button or the back-arrow and house icons that appear on most pages – a method that gets old real quick. I also found some problems with button clicks not being accepted while using Mozilla 1.6b as my browser, which switching to IE 6 seemed to remedy.
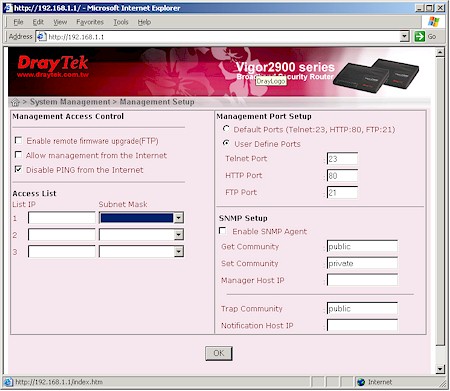
Figure 3: Management options
You actually get a pretty good set of management options (Figure 3), including a command-line Telnet interface and support for SNMP. You can also limit remote access (disabled by default) to three different IP addresses. You can’t, however, access the admin features from a wireless client, since DrayTek feels this is too insecure.
One of your first duties will be to set up your Internet access (Figure 4).
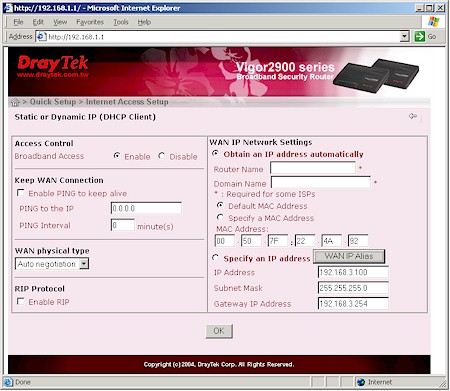
Figure 4: WAN DHCP client settings
You choose between Static / Dynamic IP, PPPoE and PPTP connection types and can set the WAN port connection speed and full / half duplex (WAN physical type) in all three. PPPoE users should note that connections with static IPs are supported and you can choose from PAP or PAP / CHAP authentication. You can also adjust the MTU value, but you’ll need to Telnet into the command-line interface to do it (see FAQ #8 on this page).
A feature that flashed me back to the very early days of consumer routers is the Call Schedule setup. Its ability to schedule the times and days that the 2900G is connected to the Internet is probably more suited to the ISDN versions of the 2900. But in these days of around-the-clock port scans, worms and other Internet-based attacks, I can see how it would be handy just to simply automatically disconnect your LAN from the Internet while your office is closed or family is fast asleep (or supposed to be).
The 2900G also has Multi-NAT capability, handling up to eight WAN IPs if you’re fortunate enough to get them from your ISP. You can’t use Multi-NAT if you’re using a PPTP or PPPoE connection, though, and only one IP address can be shared using the 2900G’s NAT router. The other seven can only be passed through to one LAN client each, essentially opening all ports on each IP address to each client.
The interface is generally quick, with very quick reboots needed to get the changes you make on each page to take. Multiple admin logins are allowed, with no warning given when two or more admins log on. Once you’re logged in, there’s no idle timeout, and you just need to remember to quit your browser when you’re done, because there’s no logout button.
Firewall Features
The 2900G has a very capable SPI+NAT firewall, but again, the interface may keep you from taking full advantage of it. I found myself frequently consulting the PDF-based User Guide on the CD supplied with the router to translate terminology and figure out how to use some of the less common features.
I have to say that DrayTek’s method of using multiple PDF files linked via an HTML page for its User Guide gets points for novelty, but a thumbs-down for usability. Make sure you check out all the info on the CD, too, since there are useful tools and documentation there that aren’t found in the User Guide.
Port forwarding is handled three ways by the 2900G: Port Redirection, Open ports and DMZ. The most flexible is Port Redirection, which is shown in Figure 5.
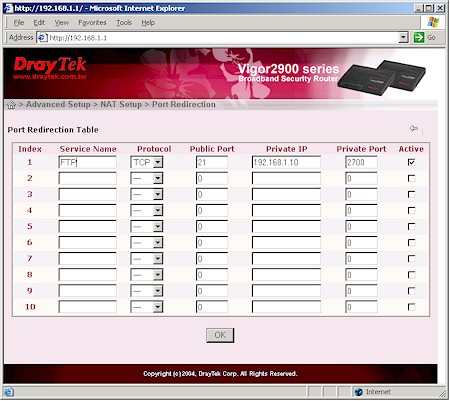
Figure 5: Port Redirection
This feature both opens up to ten ports in the 2900G’s firewall so that Internet-based users can access a server on your LAN, but also allows you to run that server on a different port than its publically-known one. Figure 5 shows a sample mapping that will take normal port 21 FTP requests and direct them to a LAN-side FTP server running on port 2700. Note that you can specify TCP or UDP mapping, but not both, and can’t redirect port ranges.
The Open Ports feature handles mapping 10 port ranges to LAN-side clients, but you’re still limited to specifying TCP or UDP as the protocol. Note that neither feature supports triggered port mappings or server loopback. Lastly, the DMZ feature lets you open all ports to one client on the router’s LAN.
UPnP is also supported and disabled by default. You even get separate check boxes to enable Connection Control and Status services.
Now that you know how to let traffic into your LAN, let’s look at the controls you get for outbound data flow. DrayTek uses a rules-based filtering system that will be more comfortable to folks accustomed to configuring enterprise-grade firewalls. You get twelve filter sets, each of which can have up to seven filter rules like the one shown in Figure 6.
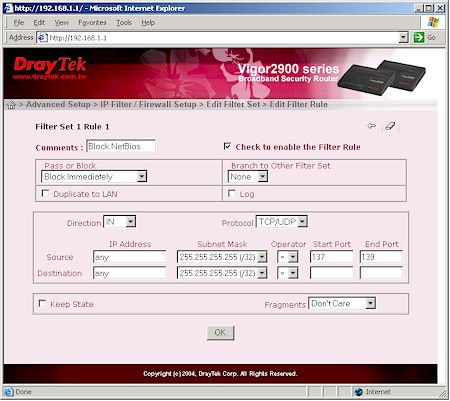
Figure 6: Filter Rule
Rules can be applied to outbound or inbound data, which DrayTek terms Call and Data filters respectively. I won’t get into a tutorial on how to program these filters, but suffice it to say that if you have complex filtering needs, the 2900G’s IP filters can probably handle it – if you can figure out how to work them.
Firewall Features – Content Filters
About the only control you don’t get for IP filtering is day / date control. That’s reserved for the Content Filtering feature (Figure 7).
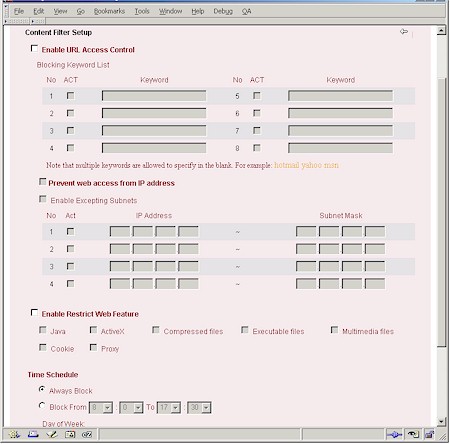
Figure 7: Content Filtering
As you can see, this is a pretty complete set of content filtering features, all of which can be scheduled by time of day and day of week. You get eight sets of URL keyword blocks with multiple keywords allowed per set (as long as you don’t exceed 32 characters per set).
In case your LAN users are savvy enough to try using website IP addresses to bypass the keyword blocking, you can enable the Prevent Web access from IP address feature. This blocks web access for any IP address entered (or clicked into) a client browser by any LAN user.
There’s also the ability to block access to Web Proxies and download of ActiveX and Java applets and browser Cookies – features commonly found on other products. However, the 2900G also has the not-so-common ability to block download of common compressed, executable and multimedia file types – the first time I’ve seen this feature. This will be a welcome addition to anyone trying to control bandwidth usage by download-happy teens or employees.
The downside of the Content Filtering features is that they apply to all users. The only feature that can be bypassed by “trusted” users is the Prevent Web access from IP address feature, where you have four entries in the Enable Excepting Subnets feature that can be used to enter individual IP addresses or subnets that will be allowed IP address-based web access.
Finally, I’d be remiss if I didn’t mention the 2900G’s DoS Defense settings (Figure 8).
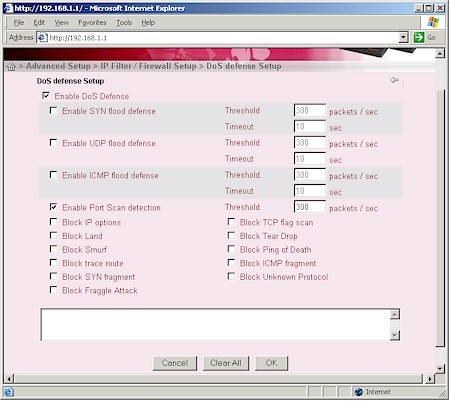
Figure 8: DoS Defense setup
This screen controls the stateful inspection features of the router’s firewall that are focused on Denial of Service types of attacks. These features are disabled by default, which is probably appropriate for most users. I’ve always wondered about the value of this feature category for consumer firewall / router products, since any DoS attack will flood a user’s broadband connection, essentially taking it down no matter what the router / firewall does anyway. But at least the Port Scan detection that I tested worked well, sending a series of messages to the syslog stream (more later) as soon as I started the scan.
My test of the Email Alert feature didn’t fare as well, though, with not one email received throughput my port scans.
Bandwidth Management and VLANs
Two of the 2900G’s features not commonly found on consumer-grade routers are its Virtual LAN (VLAN) and Rate (bandwidth) Control features (Figure 9).

Figure 9: VLAN and Rate Control settings
Both features are applied to clients connected to the 2900G’s physical ports, so are somewhat limited in flexibility. Still, it’s nice to see these features incorporated into a consumer-priced product.
You get a matrix of four VLANs and four ports, so VLAN assignment is as easy as checking the appropriate boxes. Clients in the same VLAN will be able to communicate with each other and with the Internet, but not with any other clients.
Rate Control sets the upper speed bound of inbound and outbound traffic from each of the 2900G’s four ports. Anyone who is plagued by family members who monopolize the broadband connection will be able to put this feature to good use. Figure 9 shows you can set throughput caps in increments of 32kbps in each direction separately.
My testing showed that both features worked well. Putting clients in different VLANs kept them from being able to ping or connect to each other, but still allowed Internet access. Bandwidth control also worked as you’d expect with average throughput maintained pretty close to the set rate. But the way the capped throughput is maintained is interesting.
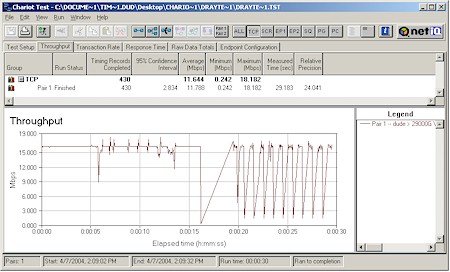
Figure 10: Rate control throughput characteristic
Figure 10 shows a Chariot throughput plot that starts out without Rate Control, then kicks it in with a cap of 2048 kbps. You can’t really tell from this plot, but a run I did with a rate cap of 2048 kbps for the entire run had an average throughput of 1967 kbps over a 30 second measurement.
Another side effect I noted with rate limiting cranked down in the 100’s of kbps was the the web admin interface response became very sluggish while the Chariot test was running. Most users probably wouldn’t notice any slowdown with normal intermittent web traffic, but if you have a busy LAN you might.
Note that neither feature works on the wireless part of the 2900G, although DrayTek said that’s on the list for a future firmware upgrade. I hope they also enhance the Rate Control feature to include port (application) and user (IP or MAC address) based controls, which would make a good feature even better!
VPN
The 2900G’s is the first product I’ve tested that includes a VPN endpoint handles PPTP, IPsec and L2TP tunnels for LAN to LAN, remote client to LAN and wireless client to WAN. You can specify up to 32 LAN-LAN tunnels and 32 more remote-LAN tunnels. (Note the remote-LAN tunnels are used for connections from both WAN and wireless “remote” clients.)
Though the Sonicwall TZW [reviewed here] provides similar functions for IPsec tunnels only, it’s priced at about three times the cost of the 2900G and limits the number of tunnels and users.
VPN setup is tricky even when you know what you’re doing, and worse if you’re a newbie. While DrayTek provides more documentation help with VPN setup (and here) than many other vendors, you still may find yourself pulling at your hair. Since I had only one 2900G, I focused on checking out Remote client-to-LAN features (Figure 11).
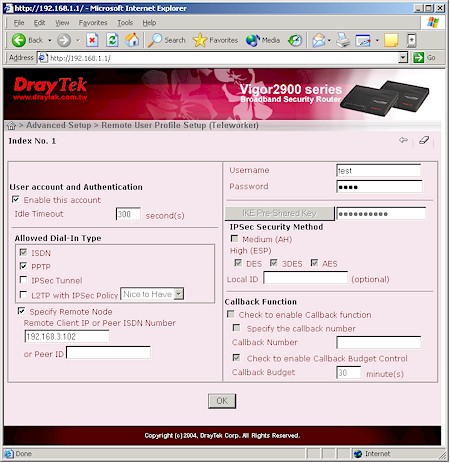
Figure 11: Remote User VPN setup
The simplest type of remote-to-LAN VPN to set up for Windows users is a PPTP link, since it has been championed by Microsoft and included in every Windows version since Win98. If you’re using WinXP you can use the Network New Connection Wizard (Start > Settings > Network Connections) to get set up.
I found that the default settings in the connection set up by XP’s Wizard worked just fine with the PPTP defaults in the 2900G. Though Figure 11 shows that I specified the IP address of my “remote” client, you can do that only if you want improved security and know the IP address of connecting clients.
Most of the settings in Figure 11 come into play when using IPsec-based clients. On the router side you can enter a pre-shared key for IKE-based authentication and choose from DES, 3DES and AES encryption levels. Client side configuration is more involved, unless you’re using a VPN client application, which DrayTek doesn’t provide.
What they do provide on their CD (and also in a Router Tools download) is a little Smart VPN client application. This isn’t actually a VPN client, but a helper application that sets up WinXP and 2000’s notoriously-difficult-to-configure built-in IPsec client. The little app even will install a Registry key required by Win2000 in order to allow IPsec connections using pre-shared keys.
TIP: If you want to learn how to configure the WinXP built-in IPsec client manually see our Problem Solver.
I tried setting up an IPsec tunnel using this little client and had partial success. I was able to establish the tunnel just fine, but couldn’t get traffic flowing through it. I even tried manually adding a static route to the 2900G’s WAN IP address for the remote subnet’s (192.168.1.X) traffic, but still couldn’t get traffic to flow.
I had even less success getting an L2TP or L2TP / IPsec connection to work. But I confess that I know nothing about wrestling that flavor of VPN into submission, so can’t really attest to the 2900G’s capabilities in that area.
As I indicated earlier, I didn’t try setting up a LAN-to-LAN VPN either, but Figures 12 and 13 give you an idea of the available knobs that you can twiddle. My experience with other products is that you’ll be able to get a LAN-to-LAN tunnel working if you use two of the same product (or at least products from the same product line).
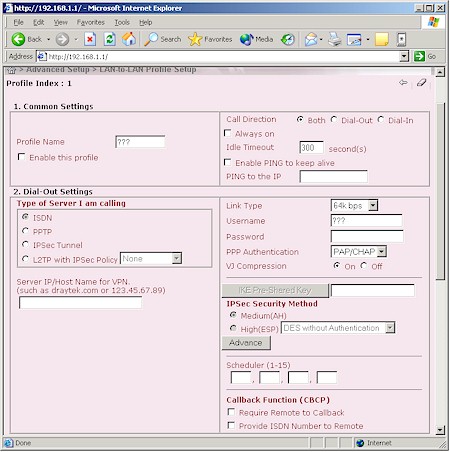
Figure 12: LAN-LAN VPN setup – common and dial-out settings.
Interoperability with another vendor’s product can be a fruitless exercise, however, unless you’re very knowledgeable in the ways of VPNs and have access to good (and patient) support folks for both vendors’ products – unfortunately rare in the world of consumer networking products.
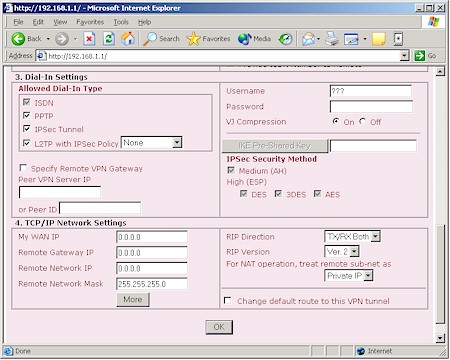
Figure 13: LAN-LAN VPN setup – dial-in and TCP/IP settings
Something that definitely helps when trying to get a tunnel set up is access to good setup log data. The 2900G actually does produce some useful VPN setup log information, but none of it is available via the router’s web interface (more on this later).
As far as VPN tunnel performance, I was pleasantly surprised. I used Qcheck to run a quick PPTP throughput check and found I had a nice steady 10Mbps from WinXP client, through the tunnel, to a LAN-side client. Note that this was measured without any other traffic running through the router, but it’s still damned impressive!
Print Server
The only indication of the built-in LPR-based USB print server is the Printer light on the front panel and USB connector on the rear. Setup instructions aren’t found in the User Guide, but in the TIPS folder on the CD instead.
TIP: If you are setting up the printer on either WinXP or 2000 don’t skip the step of switching from the Raw protocol that the Printer setup wizard sets to LPR and enter a LPR queue name of p1, or printing won’t work. You’ll also need the disk with your printer’s drivers on them for the install.
Once you get set up, it either works (which it did with my Epson Stylus Color C80) or it doesn’t since there are no settings to tweak or status indicators to view in the 2900G’s web admin interface.
Logging & Other Features
The 2900G actually has pretty comprehensive logging capabilites. But that plus is offset by its complete lack of log viewing capability in its web-based admin interface. Fortunately, DrayTek’s Router Tools package includes a very nice Syslog viewer, but unfortunately only runnable on Windows machines (Figure 14).
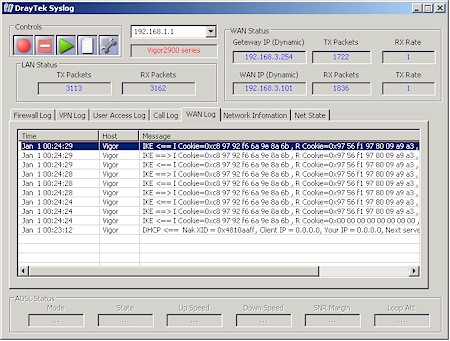
Figure 14: Viewing logs with DrayTek Syslog
Figure 14 shows the IKE exchange for a successful IPsec tunnel setup and gives you an idea of the viewer’s capabilities. I wish it came with documentation, though, since the information I found on the Network Information and Net State tabs looked particularly interesting.
There are other treasures to be found among the 2900G’s many menus. To wrap up the feature description, I’ll try to list them all here:
- Up to ten static routes
- Dynamic DNS client support for dynsns.org,.no-ip.com, dtdns.com, changeip.com, dynamic-nameserver.com
- authentication support via external RADIUS server
- force dial and drop of PPTP and PPPoE connections
- ability to view routing and ARP cache tables, dialing trigger packet header, DHCP client, NAT port redirection and active NAT sessions tables
Routing Performance
Testing Notes:
• All tests were run with LAN endpoint in DMZ
Though slower than many of the router’s I’ve recently tested, I doubt the 2900G’s 16Mbps routing speed would give many buyers pause.
I was pleased that I didn’t have any problem running Qcheck’s UDP streaming tests in either WAN-LAN or LAN-WAN directions, and even with all the 2900G’s DoS features enabled. This is sometimes a problem in NAT+SPI routers, but apparently not in this one.
Routing Performance Test Results
| Test Description | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
|---|---|---|---|---|
| Throughput (kbps) | Lost data (%) | |||
| WAN – LAN | 16.6 | 1 (avg) 1 (max) |
500 | 0 |
| LAN – WAN | 15.1 | 1 (avg) 1 (max) |
500 | 0 |
| Firmware Version | 2.5.2_rc3 | |||
See details of how we test.
Wireless Features
Given the rich feature set on the 2900G’s wired side, the wireless side of the router has a way to go before it adequately holds up its end of the product. Figure 15 shows that you pretty much just get the basics, though the ability to shut off the radio and disable SSID broadcast are pluses in my book.
I did like, however, that the Call Scheduling feature can also be applied here to automatically turn the wireless section on and off at programmed times as an extra measure of security.
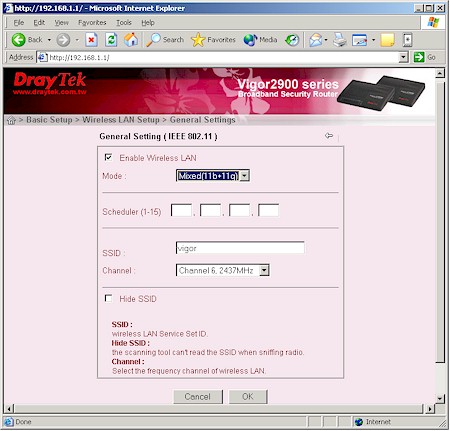
Figure 15: Wireless Setup screen
The list of missing features is long, though, with transmit rate, VLAN and Bandwidth Control features at the top my desired “To Do” list for both security and usability reasons. Next on the list are support for WDS-based bridging and repeating, since there are few 11g routers with this desirable range-extension capability.
In the “would be nice” category are settings such as transmit power control, Beacon and DTIM Interval and Fragmentation and RTS Threshold, though I admit these are interesting to a relatively small number of users. I’d also like to see an enable for any “enhanced” throughput features (since the 2900G is PRISM based these would be Nitro or Nitro XM), though it appears that none are currently supported (more in the Wireless Performance section).
Also on my missing feature list is wireless client monitoring since the 2900G lacks any features for specifically monitoring wireless clients or traffic. Maybe it’s just me, but I still can’t figure out why companies continue to get away with not providing the ability for administrators to quickly and easily see the wireless stations associating (and attempting to associate) with a network. Sure, you can use the DHCP client list and syslog User Access log info, but I don’t consider that very helpful for easily keeping an eye on wireless activity.
Wireless Security
Turning to wireless security, the picture is much better, if not a little unusual.
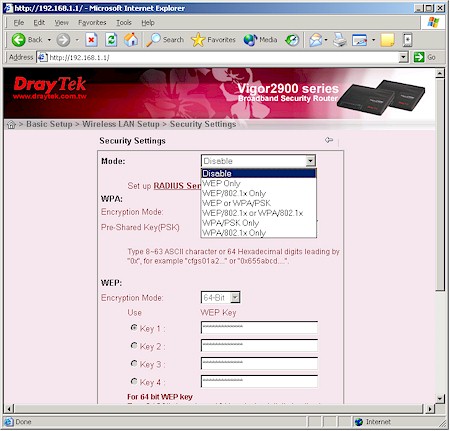
Figure 16: Wireless Security settings
As you can see in Figure 16 you get support WEP, Wi-Fi Protected Access (WPA) and 802.1x flavors of security, although 802.1x and WPA “Enterprise” (WPA / 802.1x) support requires that you supply the required external RADIUS server. The unusual capability that the 2900G provides is its simultaneous support for WEP and WPA (shown in the drop-down in Figure 16).
Though handy for folks trying to transition from WEP to the more robust WPA, this mixed-mode support is discouraged by the Wi-Fi Alliance. This is because any WEP clients associated to the 2900G could be compromised, essentially neutralizing any advantage provided by the more secure WPA.
On a more positive wireless security note, the 2900G provides the much-desired ability to support VPN connection from wireless clients.
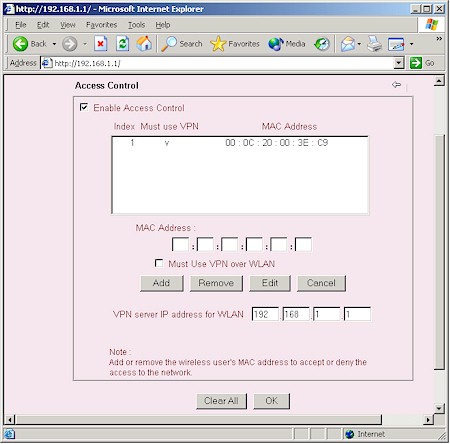
Figure 17: Wireless access control with VPN
This feature is incorporated into the MAC address Access Control feature shown in Figure 17. You have the option of limiting access to specific wireless clients by just MAC address or MAC address plus VPN. Note that you’ll need to configure a tunnel for each client to which you wish to grant access. Also note that you don’t get a pick list of currently associated clients to choose from when creating the Access Control list, nor can you load or save a file with the MAC addresses.
Unfortunately, when I checked this feature the MAC address control portion worked fine, but I found the Must Use VPN over WLAN checkbox had no effect. A quick check with DrayTek confirmed that this is broken in the v2.5.2_rc3 firmware I was using, but is on the fix list for an upcoming firmware update.
Wireless Performance
NOTES:
• “Signal Quality” readings were not available from the WinXP Zero Configuration client used
• Testing was done with a DrayTek Vigor540 Wireless 11g CardBus Adapter in a WinXP Home Dell Inspiron 4100 laptop unless otherwise noted
The throughput test results in Figure 18 show best-case performance of 24Mbps, which is comparable to other 802.11g products running without any of the myriad throughput enhancement technologies.
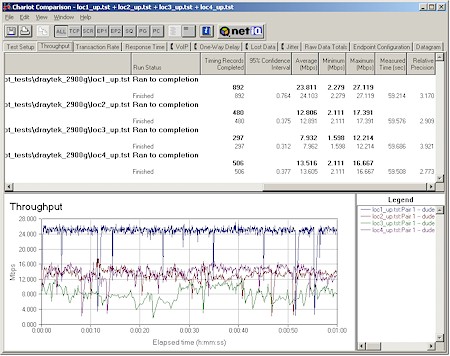
Figure 18: Four Condition Throughput test
(click on the image for a full-sized view)
Note that the lowest result was obtained in Location 3, which is one floor below and at the opposite end of the test building.
Though a check of the Vigor540 test partner client card’s Advanced Network properties showed a Nitro mode (Conexant’s throughput-enhancement technology) entry that was set to 1, I suspect that neither Nitro nor Nitro XM is enabled in the 2900G itself. If it had been, I would have expected to see more like 27Mbps under the same test conditions.
Location 1 (best case signal) runs with WEP128 then WPA-PSK (TKIP) enabled yielded average 1 minute speeds of 23.0 and 18.1Mbps respectively. These translate to throughput reductions of about 5% and 25% respectively, when compared to the “naked” best-case 24.1Mbps result.
The 25% reduction for WPA (TKIP) is right in line with tests I’ve run on other PRISM-based products and appears to be baked into the chipset. Unfortunately, the PRISM chipset doesn’t support the alternative AES encryption that Broadcom provides as a way around the problem in their chipset. So if you want to use WPA with the 2900G, you’ll unfortunately pay a high throughput penalty.
802.11g Wireless Performance Test Results
| Test Conditions
– WEP encryption: DISABLED |
Firmware/Driver Versions
AP f/w: |
||||
|---|---|---|---|---|---|
| Test Description | Signal Quality (%) | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
| Throughput (kbps) | Lost data (%) | ||||
| Client to AP – Condition 1 | 0 | 24.1 [No WEP] 23 [w/ WEP] |
1 (avg) 1 (max) |
500 | 0 |
| Client to AP – Condition 2 | 0 | 12.9 | 1 (avg) 2 (max) |
500 | 0 |
| Client to AP – Condition 3 | 0 | 8 | 2 (avg) 4 (max) |
500 | 0 |
| Client to AP – Condition 4 | 0 | 13.6 | 1 (avg) 3 (max) |
500 | 0 |
See details of how we test.
Wrap Up
The 2900G promises a lot and delivers much of it. Where else can you get everything that the 2900G provides, and for around $200, and without per-user license requirements or paying for the ability to get firmware updates?
The part that’s not delivered, however, is a stable, finished product. The good news is that features and improvements are still being added. The bad is that some of the current features don’t work and you’ll get to pay for the privilege of waiting for those to be fixed and helping to debug the new ones.
This method of product development is encountered too frequently, methinks, by today’s networking product consumer, and DrayTek appears to be part of the pack. DrayTek’s U.S. presence, however, is small compared to the major manufacturers, being supported by a single rep. (Guideband.com). Products are only available direct and through “affiliate” resellers and all product support is handled via an on-line trouble ticket system and user Forum – phone calls are not an option.
The bottom line is that if you’re expecting a polished product similar to those from the “big guys”, you’d better pass the 2900G by, no matter how tempting the feature set. And even if you’re comfortable helping (and paying!) to polish a diamond in the rough that has a combination of features you won’t find anyplace else, I’d wait a few update cycles to let someone else shake out the bugs and see whether the VLAN and Bandwidth Controls really do get added to the wireless side.