Introduction

| ZyXEL ZyAIR G-2000 Plus 802.11g Wireless 4-port Router | |
|---|---|
| Summary | 802.11g router with built-in PEAP / RADIUS authentication |
| Update | None |
| Pros | • Supports WPA, WPA2 with PEAP / RADIUS authentication • Rich feature set with many user-settable options • Configurable via web and Telnet command line interfaces |
| Cons | • Relatively slow routing throughput • Web interface needs polish • Firewall configuration harder than it should be |
A few months ago, ZyXEL released an updated version of its G-2000 wireless router. The new product, labeled the ZyXEL G-2000 Plus, replaces the earlier G-2000 model we reviewed last year. The Plus’ main claim to fame is the addition of a built-in Protected Extensible Authentication Protocol (PEAP) Remote Authentication Dial-In User Service (RADIUS) server. What makes this special? To quote the press release:
“The ZyAIR G-2000 Plus with built-in PEAP RADIUS server enables companies to implement WPA-Enterprise providing each user their own unique username and password…. With WPA-Enterprise, the ZyAIR G-2000 Plus strengthens security and simplifies administration so now awarding or revoking access to users is effortless. In addition, ZyAIR G-2000 Plus can act as a PEAP RADIUS server for other APs on the network.”
What this basically means is that the G-2000 Plus can perform secure user authentication as well as encryption of wireless traffic. I’ll go into a bit more detail on this later.
Other than its PEAP RADIUS server, the G-2000 Plus is like many other wireless routers these days. It’s a four port 10/100 switch (Figure 2), an 802.11b/g wireless access point, and a firewall / router all rolled into one. It features the usual web-driven configuration interface, along with a few niceties such as simple content filtering and remote logging.
Included with the product is a printed “Quick Start Guide” and “User’s Guide” on CD. It’s easy to see why a printed version of the user’s guide isn’t included with the product as it’s 430 pages long and quite detailed.
Basic Features
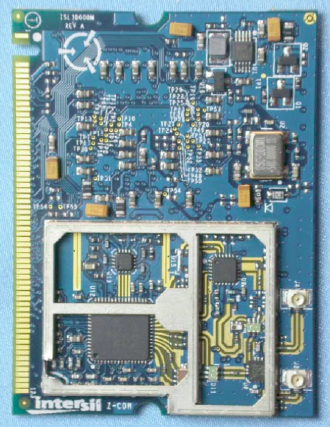
The Plus features an 802.11b/g wireless access point with two detachable antennas connected using standard RP-SMA jacks. According to the FCC documents, the radio is an XG-600 mini-PCI module (Figure 1) that appears to be manufactured by ZCom and uses a Conexant PRISM chipset. While the exact model number is different, ZyXEL said that this is essentially the same radio used in the G-2000.
Figure 1: The radio
(click to enlarge)
I didn’t crack open the case to peruse the Plus’ innards, but ZyXEL confirmed that the main board design is also essentially the same as that of its older sibling, (A picture of the G-2000’s main board is here.) and is based on an ARM-based Samsung 2510.
In addition to the four 10/100 switched LAN ports found on one it the Plus’ side panels (Figure 2), there’s also a single 10/100 WAN port. All ports are auto-negotiating and auto MDI / MDI-X (automatically adjust to either a crossover or straight-through Ethernet cable). The connector panel also sports a recessed reset-to-factory-defaults button and power jack.
Figure 2: The ports
(click to enlarge)
Easy-to-read status lights are arranged in a strip on the top of the Plus and indicate power, system status, and wired LAN and WAN activity. There’s also a large blue well-illuminated ZyAIR logo, which is used indicate wireless activity.
Setup and Administration
Installing the G-2000 Plus is simple. Even without referring to the extensive documentation, most seasoned geeks should be able to get everything connected up and running without any trouble. After everything is plugged in, just open a web browser on any computer connected to the LAN and point it to the router’s default address of 192.168.1.1. You can also connect using telnet if you’d prefer, though this means you must wade through device configuration using a text-based interface. It’s there if you need it, and handy for quick fixes or changes, though.
The web interface makes configuring everything pretty easy, even for folks who may not need or understand some of its more advanced features. The web interface also includes a decent online context-sensitive help system.
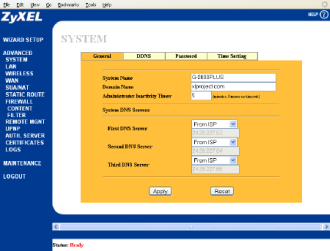
Figure 3: System General Configuration
(click to enlarge)
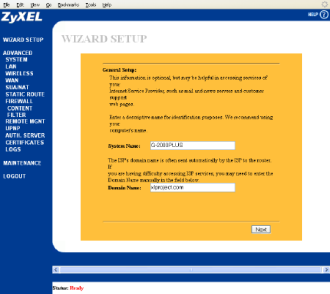
Once you’re connected to the web interface and logged in, you can configure the device in a couple of different ways. On the left, there’s a list of topics. Click on a topic, and you’re taken to a setup page, usually with tabs across the top. Click through the tabs to configure various related items There’s also a “Wizard Setup” method provided (Figure 4), which walks you through the basics for those in need of hand-holding.
Figure 4: Wizard Setup
(click to enlarge)
The rest of the configuration follows the same tabbed layout shown in Figure 3.
Setup and Administration – Firewall
The Plus’ firewall / routing portion uses stateful packet inspection (SPI) to provide protection against denial of service (DoS) and other attacks. The firewall is primarily rule-driven in its configuration and behavior and uses a basic set of default rules but custom firewall rules may be defined and added to its rules base.
The documentation includes a reasonably helpful and comprehensive rule logic overview for those who want to create custom firewall rules, and includes a checklist to determine the intent of the rule, label it as an allow or deny mechanism, specify whether its focus is on inbound or outbound traffic, identify IP services involved, as well as computers affected.
The rule definition interface is visual, and includes data entry fields or pull down lists to specify what action to take (Block, Forward) and the service against which it operates (the interface includes a large list of predefined services, but also includes a mechanism to add new definitions to that list).
Default rules permit LAN-to-WAN (outbound) traffic, but deny traffic initiated from WAN-to-LAN (inbound). Firewall rules are grouped based on direction of travel, into the following categories:
- LAN to LAN / ZyAIR
- LAN to WAN
- WAN to LAN
- WAN to WAN / ZyAIR
The default stateful inspection rules block WAN to LAN and WAN to WAN / ZyAIR traffic, so that computers on the Internet cannot use the Plus as a gateway to other computers on the WAN, nor can they attempt to manage the Plus itself. It’s possible to add custom rules by comparing Source IP address, destination IP address and IP protocol type for traffic to rules defined by the administrator.
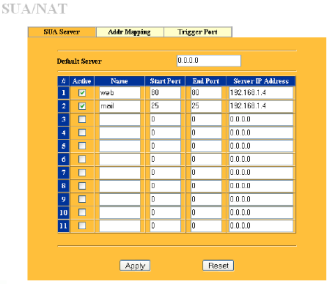
One of the first things I needed to do was to set up inbound access for my web and email server, which meant changing firewall settings. This was fairly simple using the SUA/NAT page (Figure 5).
Figure 5: SUA Server
(click to enlarge)
Unfortunately, making these entries did not achieve the desired results, which should have been to forward all incoming requests on ports 80 and 25 to my server at IP address 192.168.1.4. The G-2000 Plus’s own logs even confirmed that those requests were being dropped. I managed to figure out that in addition to making the proper SUA / NAT entry, I also had to create rules in the firewall to tell the system to properly forward such requests. Once that was done, it worked fine.
While I now understand why the firewall rules had to be entered, I think ZyXEL should either provide some sort of reminder or flag that a firewall rule creation is necessary when defining an SUA / Server, or do it automatically like many other consumer routers do! And to make matters even more confusing, I found that when setting a “Default Server” (commonly known as a “DMZ” machine), I didn’t need to program a matching firewall rule!
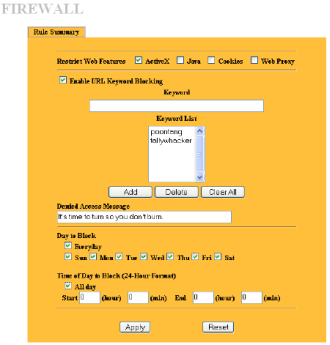
Besides the usual firewall functions of keeping out the bad guys and acting as a gatekeeper for your local network, the Plus also performs basic web filtering. You can restrict web features like ActiveX and Java, and you can restrict URL’s by outright specification or by keywords. You can even assign the days and times when filtering is active (Figure 6).
Figure 6: Firewall Content Filter
Other Features
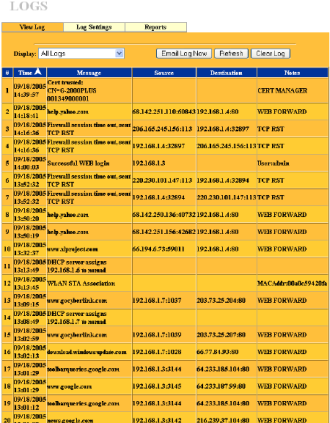
I really liked about the logging features of the G-2000 Plus. You can set the system to log as many or as few different types of events that you’d like, such as system errors, attacks, wireless activity and so forth. It will communicate with a Syslog server if configured to do so, and you can also set it to send email alerts when certain events occur, or to email you entire logs as directed. Viewing logs is easy from within the web interface, although they can get lengthy if you’ve choose to log everything (Figure 7).
Figure 7: Log Viewer
There’s also the usual DHCP server included, along with a Dynamic DNS updating service. These services all worked well for me, and of course the web interface makes them easy to configure.
Wireless
Along with the Plus’ other wireless security features (MAC address filtering and SSID broadcast disable), you have your choice of the following ways to secure your wireless LAN:
- Static WEP
- 802.1x and Dynamic WEP
- 802.1x and Static WEP
- 802.1x and no WEP
- WPA-PSK
- WPA-Enterprise
The main story of the Plus, however, is its built-in PEAP RADIUS server. PEAP stands for Protected EAP, and is one of several TLS-based (Transport Layer Security) protocols developed for use with EAP (Extensible Authentication Protocol) in wireless environments. (The IEEE 802.1x standard makes use of EAP to define an authentication framework for wireless communications.)
PEAP is a joint effort undertaken by Microsoft, Cisco, and RSA, supported on the client side by Microsoft in Windows XP, and Cisco (and compatibles) on the server side. PEAP (and other forms of EAP, which include EAP-TLS and TTLS) are important because they provide for strong encryption of ongoing traffic, secure exchange (and regular rotation) of keys, and strong authentication of user identity.
PEAP RADIUS is an implementation of PEAP that uses a RADIUS (Remote Authentication Dial-User Service) server to handle the authentication side of things, which essentially uses a challenge / response exchange with an authentication server (RADIUS) to perform that action. PEAP is a two-stage protocol, where security is established in stage by establishing a TLS tunnel and authenticating the (RADIUS) server to the client with a certificate. Client authentication exchanges then occur during stage two. The flavor of PEAP supported by the Plus uses MS-CHAP v2 for authentication and authorization.
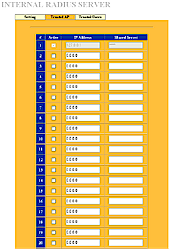
Figure 8: RADIUS Server Trusted AP’s
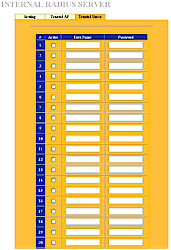
Although the PEAP RADIUS features may sound complex, the web interface makes it easy to set those up. Basically, you set up trusted wireless access points (Figure 8) and trusted wireless users (Figure 9) using simple lists:
Figure 9: RADIUS Server Trusted Users
Using this feature, the system can authenticate not only individual users, but also other access points. It’s easy to see how this ability could be daisy-chained together to serve users over a wide area. Unfortunately, you’re limited to authenticating a maximum of 32 wireless users using the RADIUS server built into the G-2000 Plus, no matter how many access points you connect. That said, the Plus will forward authentication requests to an external IAS or RADIUS server you can designate to handle authentication requests for more users.
Performance and Closing Thoughts
I performed all throughput testing using three computers:
- Mercury: Compaq Presario S5400NX with a P4 2.6Ghz processor and 504MB of memory
- Zombie: Dell XPS D333 with a PII 333Mhz processor and 256MB of memory
- Nomad: Dell Inspiron 1000 laptop with Celeron 2.2Ghz processor, 224MB of memory and a ZyXEL ZyAIR G-100 wireless card.
Tests were performed with all computers running Windows XP and using IXIA’s QCheck utility set to TCP 1000 kByte file size. All results represent an average of at least three tests.
I placed the ZyXEL G-2000 Plus in my computer “dungeon”, a spare bedroom upstairs in my two-story wood-frame home, stocked with all sorts of things like monitors, TV sets, and flourescent lights that can sometimes affect wireless connectivity.
| Location | Throughput | Location Description |
| Dungeon | 20.05 Mbps | Sitting right beside the G-2000 Plus |
| Upstairs Hallway | 15.87 Mbps | About 10 feet away with a clear line of sight to GP2 |
| Upstairs Bedroom | 16.27 Mbps | About 10 feet away, through 1 interior wall |
| Dining room | 16.35 Mbps | About 15 feet away, through 1 interior wall and a wood frame floor |
| Living room | 12.02 Mbps | About 15 feet away, through 2 interior walls and a wood frame floor |
| Bottom of stairs | 7.12 Mbps | About 20 feet away through 1 interior wall and down a flight of steps |
| Den | 17.3 Mbps | About 20 feet away, through 4 interior walls and a wood frame floor |
| Garage | 8.12 Mbps |
About 35 feet away, through 2 interior walls, 1 exterior wall, and a floor |
|
Table 1: Wireless Throughput Test Results |
||
To test routing throughput, I connected Zombie to the WAN interface, and set Mercury up as the “Default Server” connected to the LAN.
| Direction | Throughput |
| LAN to WAN | 9.62 Mbits/sec |
| WAN to LAN | 9.27 Mbits/sec |
| Table 2: Router Throughput Test Results | |
The LAN to WAN and WAN to LAN results are disappointing, since I expected throughput to be at least equal to the 16Mbps throughput of the G-2000. But these results were verified by ZyXEL, and unfortunately are correct, at least for the moment. The performance is still fast enough to keep up with most U.S. cable modems and many DSL connections. But if you have a very fast Internet link, such as those found in many locations outside the U.S., the Plus will be the limiting factor in your Internet performance. I’d expect Zyxel to remedy this problem with a firmware upgrade, which will be easy to apply using the web interface.
Overall, the Zyxel G-2000 Plus is a full-featured wireless router that will work well for many users, offering good functionality at a reasonable price. The real attraction, however, is its built-in PEAP and RADIUS server capabilities that make it easier for SMB users to take advantage of enhanced WPA-Enterprise level wireless security.
What may hold those same small-biz buyers back from adding the Plus to their LANs is its disappointing throughput. While 10Mbps may seem pretty good, it’s more reminiscent of previous-generation routers than current-gen models that feature near 100Mbps wire-speed routing. But if your routing-speed requirements tend more toward Mbps in the single digits, then the G-2000 Plus could be your key to a more secure wireless LAN.