
| At a glance | |
|---|---|
| Product | LogMeIn Hamachi2 () [Website] |
| Summary | Cloud-based VPN solution ideal for setting up quick and easy secured networks for non-technical users. |
| Pros | • Quick setup • Multiple network types • Free version has access to all major features • Fairly fast connection in free version • Support for all users |
| Cons | • Web portal is a little confusing • Documentation is lacking for using the web portal • Security technologies used not documented adequately • Some network types not available on all OSes |
Typical Price: $33
Setting up secure VPNs (Virtual Private Networks) usually involves purchasing special routers that secure in and outbound traffic for your LAN. Or if you want encryption all the way to your notebook or mobile device, the installation and configuration of a VPN client.
But, like many other applications, VPNs can now be purchased as a cloud service. I’ll be taking a look at one of the original hosted VPN services, LogMeIn Hamachi2.
Actually, the "Hamachi" part of LogMeIn Hamachi2 is the "oldie", which was around when "cloud" still meant those fluffy things in the sky. SmallNetBuilder took at look at the pre-LogMeIn Hamachi a few years back, when setup was considerably more involved.
The service was originally created to help PC gamers play LAN games over the Internet. The evolution into a SMB product began with the purchase by LogMeIn.
Hamachi2 thankfully hasn’t strayed too far from its roots. The design is simple: initial connectivity happens via a central server. Once connection is established, Hamachi2 will try to start up a VPN directly between peers running its client.
If Hamachi2 can establish this connection, traffic will use the peer-to-peer network instead of relaying through LogMeIn’s servers. LogMeIn has added to Hamachi’s original framework with additional connectivity modes that I’ll explore in a bit.
Technology Explanation
Before I get into the account types, I think it’s important to explain a little better how Hamachi2 works. It creates an entirely separate network connection on your computer by creating a virtual network adapter through a special driver.
This driver, called a TUN/TAP driver, is assigned a special IP address from the Hamachi network in the 5.x.x.x range. Incidentally, this range was recently allocated to a European Internet Infrastructure agency called RIPE NCC which has begun announcing subnet allocations for the range.
If you have Hamachi installed, any addresses or domains that resolve to that address will be sent to the Hamachi network instead. But if you happen to be a machine on a 5.x.x.x network, you could have a problem at some point.
Once your machine has a 5.x.x.x address, its network parameters are adjusted to properly route Hamachi2 traffic. You then set up a “Network†of computers. These networks are the fundamental feature of Hamachi and come in three flavors: Mesh; Hub and Spoke; and Gateway.
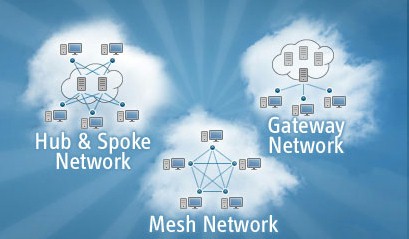
Three Hamachi2 Network types
Mesh is the original Hamachi network type. All computers joined into a mesh network can talk to each other, just as if they were connected on a LAN, only securely. This configuration is ideal for quickly setting up encrypted connection between two machines running the Hamachi client.
Hub and Spoke networking is a more secured version of mesh networking. The Hamachi2 Getting Started Guide says:
In a hub-and-spoke network, one or more computers act as hubs, while other clients connect as spokes. Spokes connect to hubs, but never to each other.
Hub-and-spoke is typically used when a workstation (spoke) needs to connect only to servers (hubs).
Hub-and-spoke is ideal if you want strict control over connections between network members.
The third type, Gateway, is most similar to a traditional VPN setup. Users connect to a dedicated (this is required) gateway machine running a Hamachi client, and all items available on the local network are then accessible, even those not running a Hamachi client. Note that, as with any other gateway-based VPN, the encrypted tunnel does not extend past the gateway.
Account Types
|
||||||||||||||||||||||||||||||||||
With all that out of the way, account types will make a little more sense. Free accounts (for non-commercial use only) have full access to all features but are limited to 16 connected computers per network. Commercial account members get upgraded to 256 computers per network, and have access to high speed relay servers in the event a normal peer to peer connection cannot be made.
Commercial accounts cost $199 / year or $33 / month. So you save about half by buying a year upfront. I’m going to be reviewing the free version.
Installation
Installation for a centralized platform is a two step process. After creating an account and logging into the backend web portal, you then choose to create a network or add clients. The recommended path is to create a network first.
This starts a wizard where you pick what type of network you want this to be. I chose Mesh to keep it simple, and required that all people trying to join the network would have to be allowed by me. Other options are: clients can automatically join, or only clients in a list are allowed to join. You can also add a network password for additional security. You can see this configuration process in the Gallery.
Once the network was set up, I set about installing the client, which is just like installing any other application. All the Gallery screen shots were taken from the Mac OS client, which is the same as the Windows client for installation and setup purposes.
Windows clients have a view features Mac clients don’t, which isn’t directly explained unless you read the manual (who does that anymore?). Windows clients can also route IPX traffic for everyone looking to play games made pre-Y2K. More importantly, Mac OS clients cannot act as gateway servers, which may put a kink in some networks.
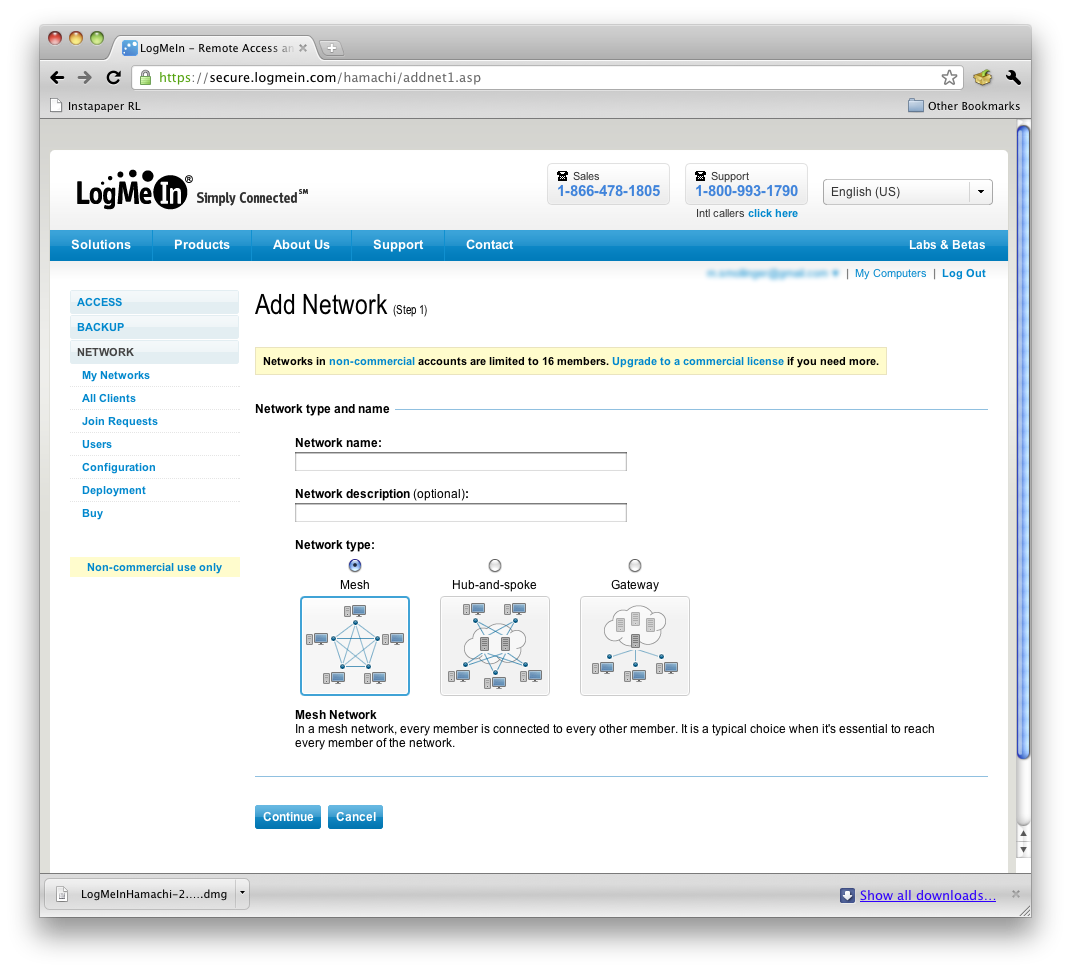
You first choose a network type. Mesh is the choice here.
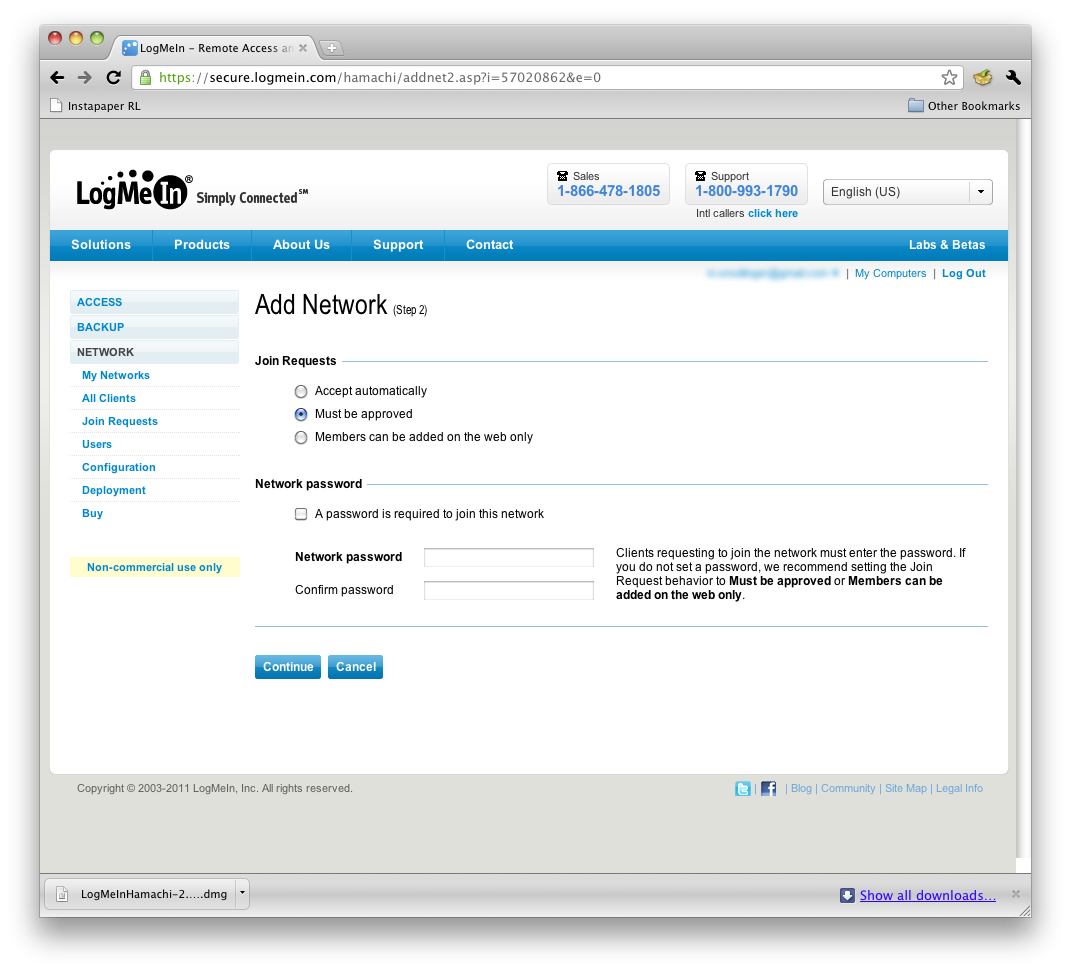
Join requests will need to be approved by an admin here.

Network overview where you also can see join requests.
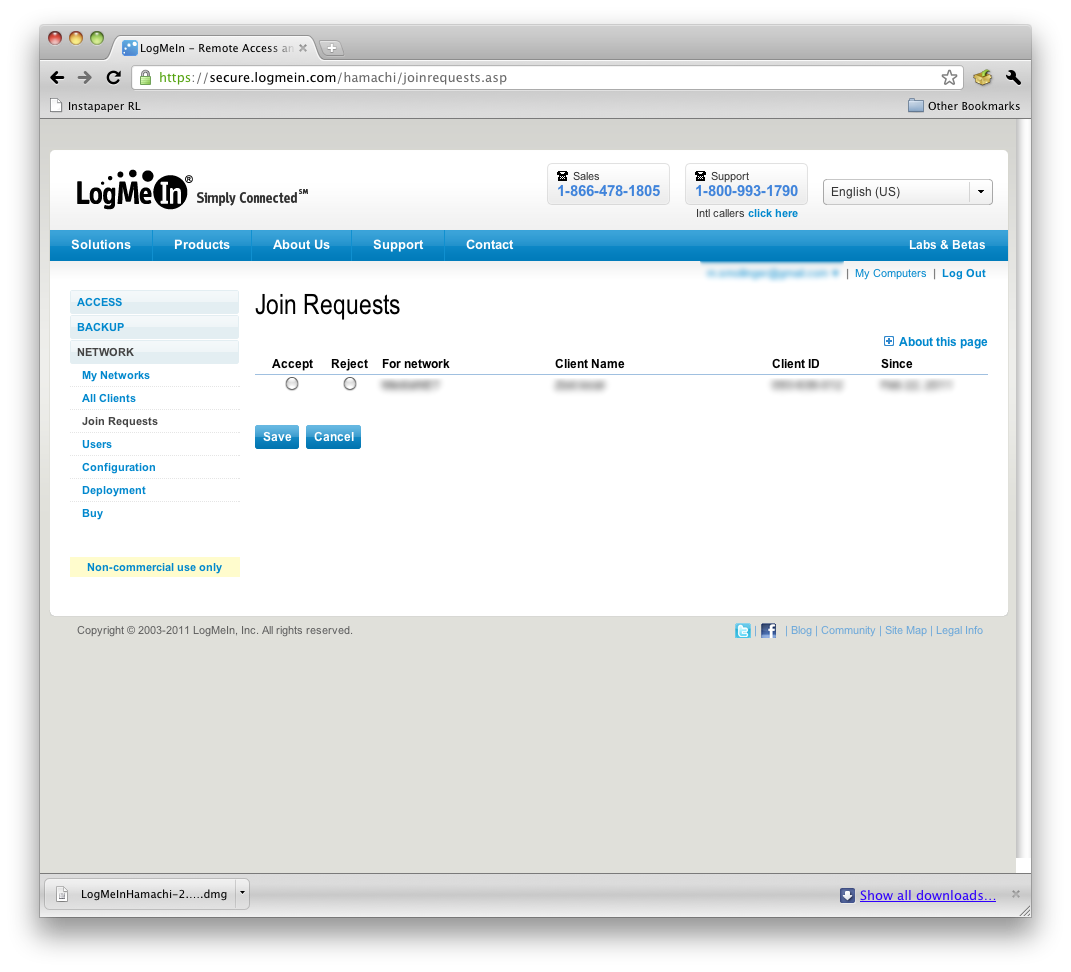
Here’s where you manage join requests.
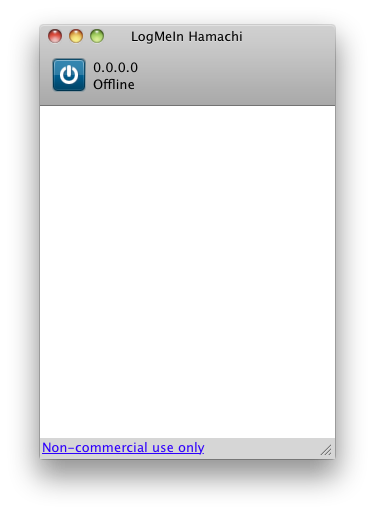
Disconnected MacOS client
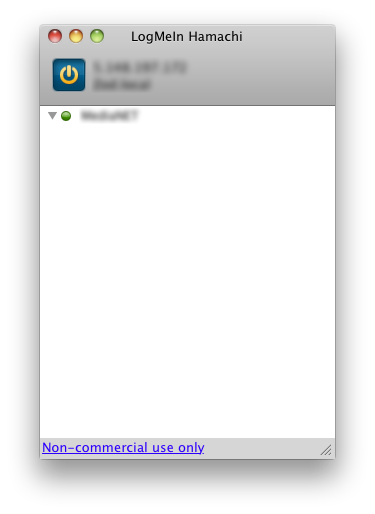
Connected MacOS client
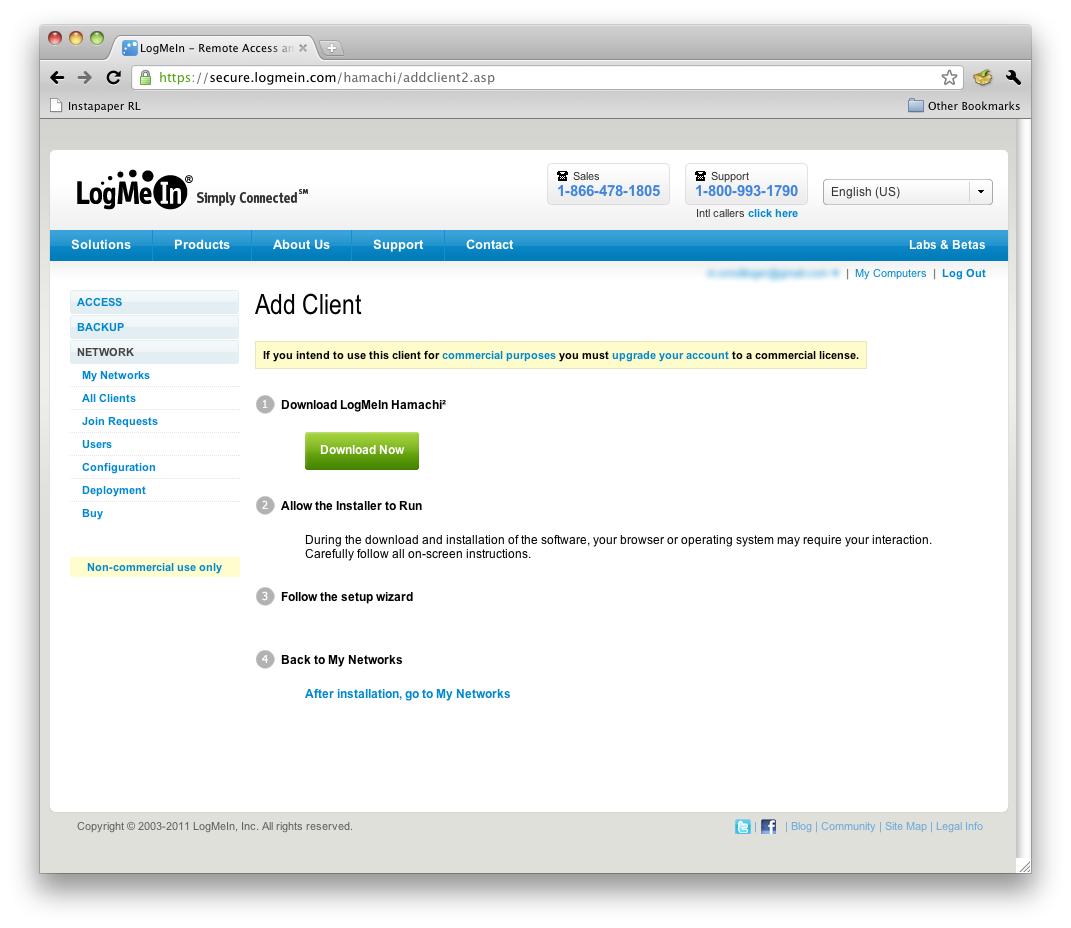
Adding clients is guided by these instructions and a wizard
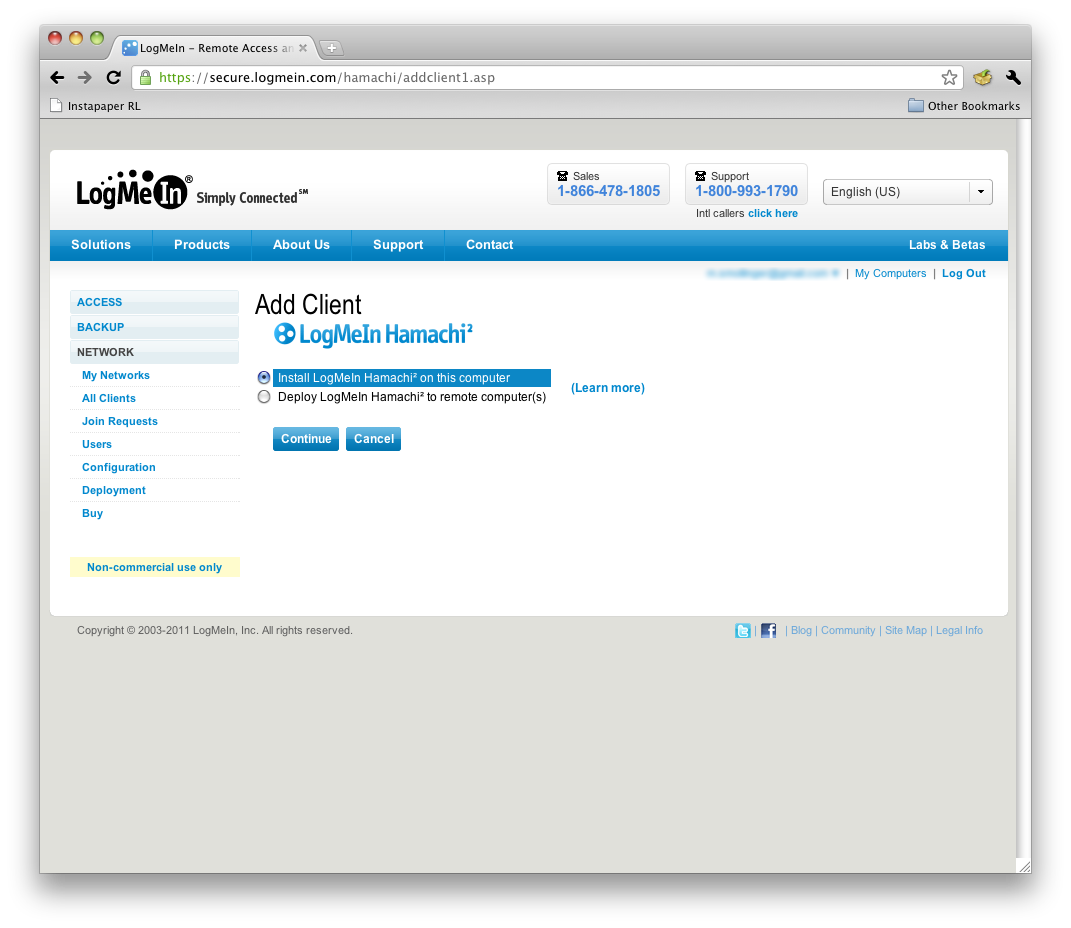
The Add Client Wizard provides two basic methods.
Once installed, the client connects and gets its IP address. You can then choose to associate it with an account, which will have it join all the networks on that account. Or you can join a network using the 9 digit network ID, or create a mesh network right within the client. I chose to associate it with my account, and connected to my mesh network easily.
I also tested the Windows client, and it seemed to automatically associate with my account when I installed it. I’m unsure if this is just additional polish on Windows, or a fluke. Both my friend, who helped me for remote testing, and I did not get an automatic association when we launched our Mac OS clients.
Speaking of my friend, I tried out the personalized client installer feature for his setup. Personalized installations create a unique URL that you then send out for people to download the client from. This allows you to track client installs, and expire the URL after a time period for increased security. In addition, personalized client installations allow clients to automatically join networks that the administrator sets for them to auto-join through the backend.
While he installed and joined the network just fine, LogMeIn’s web portal never updated to show that he downloaded the client. This could be problematic for trying to keep people with Macs from downloading too many client installations.
In Use
My friend happens to be in Boston, and has a decent cable connection (25/5 Mbps). The first thing we tried was pinging, which usually averaged 20 ms but would spike up to 400 ms every so often—not bad overall. My internet connection is a 25/25 connection from Verizon Fios.
We then decided to try file sharing. I pushed a file to him at an average speed of 15 Mbps, which was not maxing out either connection. We made sure nothing else was running on either network to be sure about this speed. 15 Mbps is pretty quick for a software VPN connection, especially after doing a traceroute and seeing the traffic was going through NYC, which is a very busy Internet hub.
After seeing that throughput, I decided to do one more test (which ultimately held up this review, but was worth it). We both opened iTunes and set up sharing. He then proceeded to stream an HD video (720p) from me, with no loss in quality and no dropouts for the 15 minutes he ran it. I then tried pulling from him, which didn’t work as well, since I maxed out his 5 Mbps upload speed, which is just not enough for HD. SD video worked well though, as did streaming MP3s.
We also tried a VNC connection, since this might be more typical VPN’d traffic. This also worked better connecting to my machine, because I have higher upload bandwidth. However, connecting to him on his 25/5 connection was very usable, as long as I tuned the VNC settings correctly.
Access and Security
|
|
||||||||||||||||||||||
Accessing the Hamachi2 VPN network is through the LogMeIn client only, due to the proprietary method it uses for creating connections. There are official clients for Windows and OS X, and a beta client for Linux, which is command line only and has limited support.
Administrators have control over the network from a decent web portal, and can configure numerous options. The web portal is a little confusing since it presents the entire LogMeIn product options. So if you are only using Hamachi2, there are several options you won’t ever use.
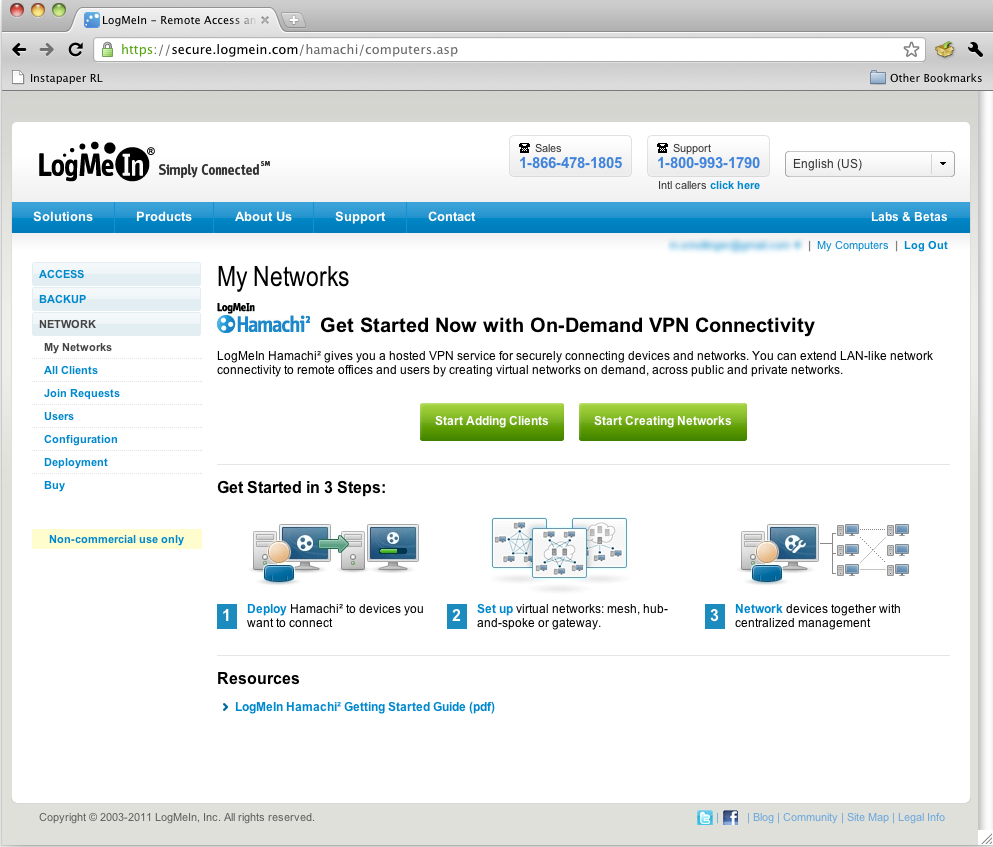
Hamachi2 backend web manage
Hamachi2 is well secured, offering RSA Key Exchanges and AES-256 tunnel encryption. Packets are authenticated using a SHA1 encryption hash, and are numbered to prevent replay attacks.
There are still some security concerns, however. Hamachi doesn’t use IPsec, most likely due to the nature of Hamachi’s connection types. For this reason alone, many businesses won’t be able to use Hamachi, since it won’t pass muster for information security audits.
VPN security technologies such as ESP, SA, and ISAKMP aren’t specifically called out in Hamachi2’s documentation. The use of Diffie-Helmann infers that perfect forward secrecy (PFS) is in use, but it can’t be managed.
Additionally, in the event you must use a relay server, data will be temporarily passed through LogMeIn. For many, this may seem innocuous because LogMeIn doesn’t keep data on its relay servers. But the fact a relay server could be used, means many businesses can’t use Hamachi2 for HIPAA or other compliance reasons.
Support
|
||||||||||||||
LogMeIn offers support to all people using Hamachi2 by way of a support hot line, email ticketing and an active community forum. It’s interesting to note that purchasing a subscription to Hamachi2 does not actually improve support in any fashion, which is not the case for most LogMeIn products. In fact, most LogMeIn products require purchasing a subscription in order to get support.
Closing
Overall, LogMeIn Hamachi2 does the job it sets out to do: creating secured VPN networks easily and quickly. Some of the security concessions won’t work for certain businesses that must meet specific industry regulatory requirements. But for many businesses, Hamachi2 will work quite well.
However, once a business hits a certain size, the mission-critical nature of VPN could rule out Hamachi2. The reason is most businesses will want to use Hamachi in the Gateway mode, which requires installing Hamachi on a Windows computer; something not generally known for long-term stability.
LogMeIn, however, does require that a Gateway system can’t be a member of any other network and can’t be a domain member. If absolute reliability is a must, it would make sense to have a dedicated gateway system with Windows update disabled and unnecessary processes shut down.
Even then, I recommend any business looking into Hamachi be aware of its limits, and plan to replace it once they have the revenue to step into a proper VPN appliance.
