Introduction
Updated 9/24/2010: PKG info

| At a Glance | |
|---|---|
| Product | Cisco NSS300 Series (NSS322, NSS324, NSS326) |
| Summary | Intel Atom D510 RAID SATA NAS family with Gigabit Ethernet and many serving options including RADIUS. |
| Pros | • RADIUS server • 5 year warranty including drives in populated systems • Priority support options available ($) |
| Cons | • No network camera support • Does not accept QNAP QPKGs for add-on apps • Plugins still a work in process • No bundled client backup software |
I’ve already covered Cisco’s new NSS300 NAS line pretty well. First with a comparison to the QNAP NASes that form their nuclei [QNAP Probably Behind Cisco’s New Small Business NASes], then with performance tests of the NSS322, NSS324 and NSS326.
So in this review, I’m just going to try highlight some of the "value add" that Cisco brings to the party so that you can decide for yourself whether to buy these or their QNAP versions, i.e. the TS-259 Pro, TS-459 Pro and TS-659 Pro.
Feature Summary
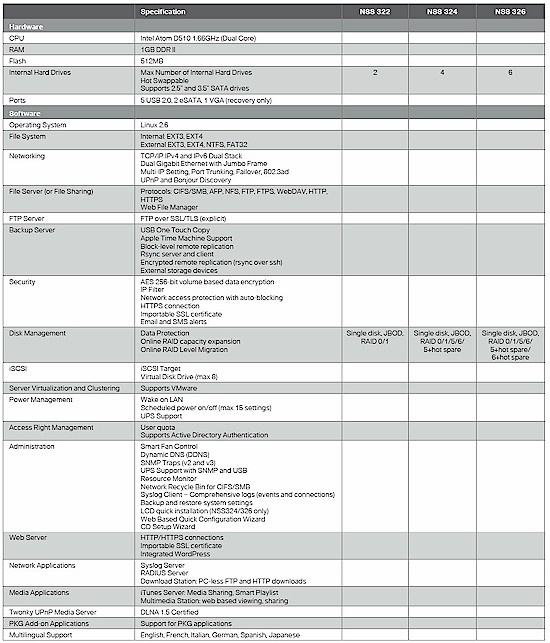
The NSS feature set is summarized in the Figure 1 table taken from the NSS300 family data sheet. It shows features essentially equivalent to those in QNAP’s V3.3 firmware. The only QNAP feature that I could find that Cisco doesn’t support is the Surveillance Station support for recording and viewing network cameras.
Figure 1: NSS family feature summary
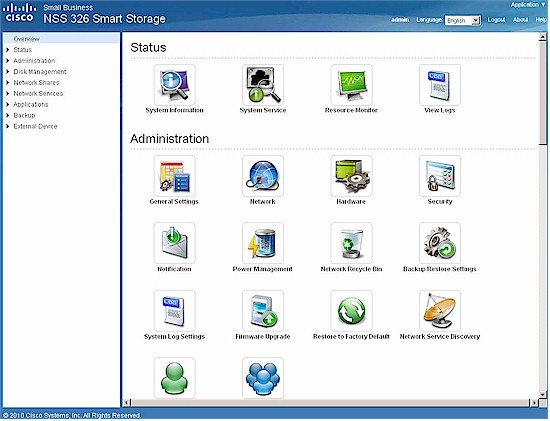
Cisco has reorganized the QNAP interface a bit (Figure 2), bringing the Status information up from the bottom and separating User and Group admin from Share and Quota management.
Figure 2: NSS family admin interface
If you want a closer look at the differences in how Cisco and QNAP have approached organizing the admin interfaces, use the links below to bring up screenshots.
Unique Features
A key differentiating feature from the QNAPs is the RADIUS server. Figure 3 shows the settings page, where it’s important to note the limited number of 802.1x authentication options. The NSSes support authentication only via PAP, EAP-TLS/PAP and EAP-TTLS/PAP.
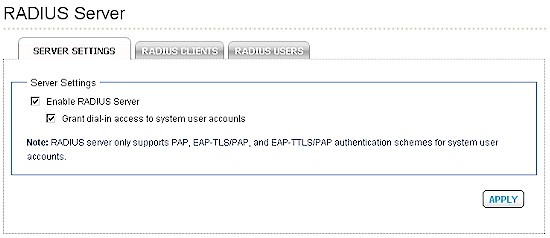
Figure 3: Cisco NSS300 RADIUS settings
I didn’t think this was a problem until I tried to set up authentication of a Win 7 netbook connected via an Ethernet port provided by an Atheros AR8131 PCIe Gigabit Ethernet controller to a NETGEAR GS108T switch. I was able to (I think) get the NSS and GS108T properly configured, by adding a RADIUS client (Figure 4) on the NSS and entering the NSS’ info into the Security > RADIUS screen of the GS108T.
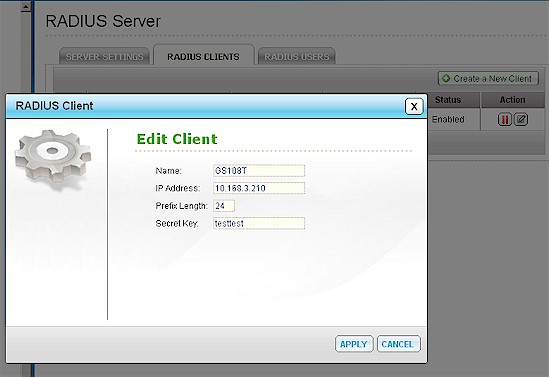
Figure 4: Cisco NSS300 add RADIUS client
I then had to enable the Wired AutoConfig service on the netbook, which added an Authentication tab to the Atheros adapter’s network properties. Figure 5 shows the authentication options presented, with only one (Intel: EAP-TTLS) matching those available from the NSS.
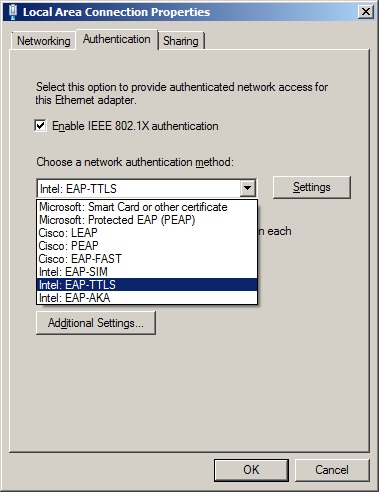
Figure 5: Atheros AR8131 authentication options
Unfortunately, no matter how much I futzed with the settings, I couldn’t get the network to successfully authenticate. After skimming through Cisco’s How to Use RADIUS on Cisco Smart Storage app note, I think the problem was my inability to download a Certificate Authority (CA) certificate from the NSS. The instructions in the app note didn’t help though, and neither did any online Windows help.
Unique Features-more
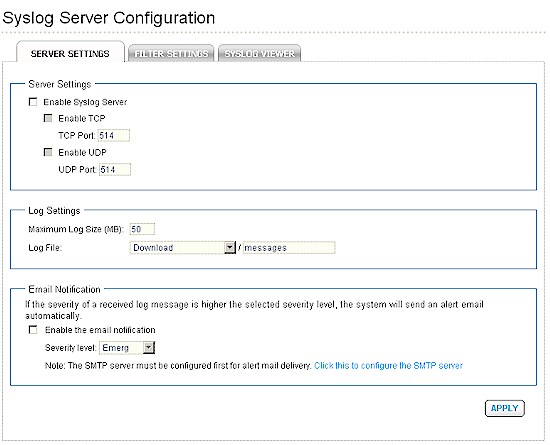
The other unique feature that the Ciscos have is a syslog server (Figure 6).
Figure 6: NSS Syslog server
Implementation includes filtering, which is aided by a Filter Wizard (Figure 7). The wizard ands all rules added. So if you need to or rules or nest them, you’ll have to use the Manual edit feature.
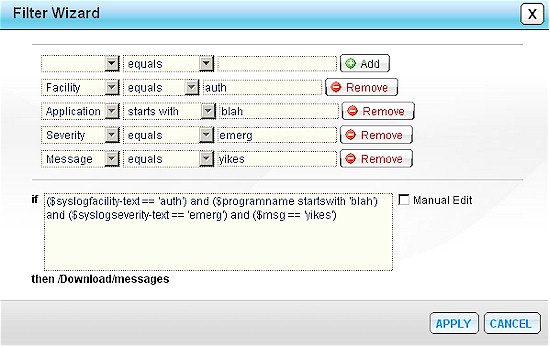
Figure 7: NSS syslog filter
Plugins
Updated 9/24/2010
One of the factors against choosing an NSS over a QNAP is the state of Cisco’s support for plugins. QNAP calls these QPKG and provides a button on their QPKG Plugins page to bring up a list of available plugins (Figure 8).
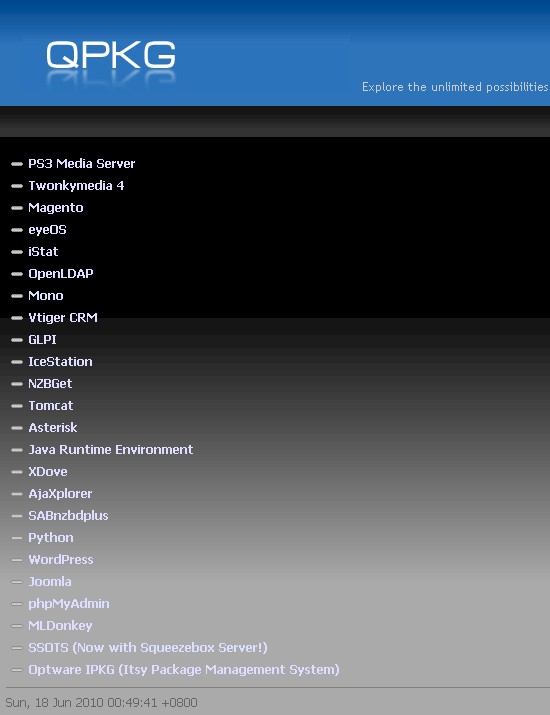
Figure 8: QNAP QPKG plugin list
Visting the NSS PKG page (Figure 9), however, reveals no button and no list. Visiting the NSS PKG page (Figure 9), however, reveals only two installed PKGs—WordPress and phpMyAdmin.
Figure 9: Cisco NSS PKG Plugin screen
Cisco told me that the NSSes will not run QNAP QPKG plugins and the only other package ready for download now is Joomla. Cisco said they have an alternate method for communicating available PKGs in the works for a future firmware release. But for now, you’ll have to check the Smart Storage Application Software page for your model. Here’s the link for the NSS326, which shows the Joomla 1.5.15 PKG installer.
But its installation will be complicated by the lack of support for the phpMyadmin plugin. There is a nice note on the MySQL Server page and in the admin guide telling you that you can install phpMyAdmin, but no plugin available to do so.
One of the NSS app notes explains how to install WordPress. But again, you won’t get very far without either the WordPress PKG plugin or phpMyAdmin.
Closing Thoughts
Updated 9/24/2010
The main thing that Cisco brings to the NAS party over QNAP is, frankly, the Cisco name and reputation, better warranty and, hopefully, a stronger support infrastructure. I say hopefully because it will take some time for knowledge transfer from QNAP to Cisco and there are bound to be some hiccups.
Table 1 sums up the situation for Warranty, Price and Support for the two product lines. For the driveless systems shown, Cisco is asking a moderate price premium in exchange for a 5 year warranty with return-to-the-factory (not reseller) replacement.
| Cisco | QNAP | |
|---|---|---|
| Warranty | 5 year (includes drives in populated systems) |
1 year |
| Lowest Price (w/o shipping) |
NSS322: $589 NSS324: $875 NSS326: $1152 |
TS-259 Pro: $564 TS-459 Pro: $844 TS-659 Pro: $1115 |
| Support | – Email – Online Chat – Telephone – Forums – Priority support ($) |
– Email – Telephone – Forums – Skype |
Table 1: Cisco and QNAP comparison
A bit more detail about support plans obtained from Cisco follows below.
What’s included:
* 5-year limited hardware warranty with return to factory replacement (vs. QNAP 1-year warranty); 5-year warranty covers hard drives as well if you buy the device populated with drives (covering drives longer than the standard 3-years)
* Cisco Small Business Support Center: 12 months telephone and online chat support
* Cisco Small Business Support CommunityWhat’s optional:
* Cisco Small Business Support Service: 3-year peace of mind coverage including software upgrades, extended access to the Cisco Small Business Support Center, and next-business-day hardware replacement; $149 for most SKUs, $499 for NSS326 w/ 6TB and NSS326 w/ 12TB
* Cisco Small Business Partner Rapid Response Service: Offers phone support 24 hours a day and four-hour advance hardware replacement; $999 for three years
If you opt for a NSS over a QNAP, you won’t get support for network camera recording and monitoring. But more significantly, you’ll have to wait for Cisco to crank out its version of plugins that you can get right now from QNAP. For business users, most of the not-yet-available-plugins will probably be no biggie, though. But for anyone planning to use the built-in MySQL database support, lack of phpMyAdmin will certainly put a crimp in their plans.
Bottom line is that if you’re a Cisco shop or fanboy, you now no longer have to be embarrassed by purchasing a Cisco NAS. But if you want to be on the fast track for firmware updates and plug in support and support is a secondary concern, you’ll probably be happier with a QNAP.