Introduction

| At a Glance | |
|---|---|
| Product | Linksys Instant Wireless-G Broadband Router (WRT54G) |
| Summary | Broadcom based 802.11g Router |
| Update | 2/1/2004 Wireless bridging support for WAP54G added in Version 2.02.2 firmware. |
| Pros | • No WEP enabled performance degradation • Removable antennas • Inbound and Outbound traffic logging |
| Cons | • Mixed mode operation kills draft-11g client throughput |
Linksys’ WRT54G Wireless-G Broadband Router seems to be more popular than its WAP54G Access Point sibling, or maybe it’s just the marketing push that Linksys is putting behind it. At any rate I received it a few weeks ago and used it extensively for the draft-11g performance testing that I did for the 802.11g NeedToKnow, and figured it was time to give it a review of its own.
Although both it and the previously reviewed WAP54G run on essentially the same Broadcom platform, the WRT54G came with newer firmware that yielded significant performance differences.
Basic Features
The WRT54G comes in Linksys’ usual purple and grey plastic box. All indicator lights are on the front of the box and are bright and viewable from a wide angle. The indicators include Link/Activity, Full/Collision and 100Mbps for the four 10/100 LAN ports and one 10/100 Ethernet WAN connection, separate Activity and Link lights for the wireless LAN connection, and Power, Diag, DMZ general indicators.
The DMZ indicator is supposed to be lit whenever the DMZ feature – which opens up all ports to one selected LAN machine – is enabled, but I couldn’t get it to light. Linksys appears to have improved the function of the wireless Activity LED, so that it blinks only when there is wireless activity instead of constantly as it did on the WAP54G. The wireless Link LED is actually more of a wireless On/Off indicator, and shuts off only when you set the Wireless Mode selector in the admin interface to Disabled and shut off the router’s radio.
Four 10/100 LAN ports, one 10/100 WAN port and power jack are on the rear panel, along with the Reset switch, which serves both reboot and reset-to-factory-defaults functions. Note that all ports are auto MDI / MDI-X which means they’ll figure out how to connect to whatever you plug into them, including switches or hubs if you decide to expand the number of ports.
Linksys includes a wall-mounting plate that does double-duty as an adapter to allow Linksys’ smaller boxes (such as their 5 port switch) to be stacked with their “normal” sized boxes. Also included are a CD with the PDF User Guide and Windows-based Setup Wizard, normal UTP Ethernet cable, and second CD with a trial version of Symantec’s Norton Internet Security suite.
Inside
The router uses a Linksys-branded WM54G mini-PCI radio. But a quick look at Figures 1 and 2 below reveals that Linksys hasn’t strayed very far from Broadcom’s BCM94306MP reference design.

Figure 1: Broadcom BCM94306MP mini-PCI radio

Figure 2: Linksys WM54G mini-PCI radio
The radio card plugs into a connector on the main board, which is based on Broadcom’s BCM4702 Wireless Network Processor, supported by RAM, Flash memory, and an ADMtek 6996 for the 10/100 WAN Ethernet port and four 10/100 switched LAN ports.
The radio is cabled to two RP-TNC style connectors (that Linksys uses throughout its 802.11b product line) which have two moveable, jointed dipole antennas attached.
That about wraps up the internal exam. Let’s move on to the setup.
Note: Since the WRT54G is based on a different processor platform, you should not assume that it has the same features as other Linksys routers such as the BEFW11S4. I’ll point out some of the more noticeable differences during the review.
Setting Up
Setup for the WRT54G is similar to that of Linksys’ other current routers. You can run a Windows-only setup utility that walks you through choosing a WAN type and other setup steps, or go directly to the built-in web-based admin interface, which was my choice for setup.
Since the WRT54G comes set to 192.168.1.1 as its factory default and built-in DHCP server enabled, all you’ll need to do is plug in a client that’s set to obtain its IP address information automatically, maybe do a DHCP release / renew (or reboot your client computer), and enter the default password into the login box that pops up. If all goes well, you’ll get the main Setup screen shown in Figure 3.
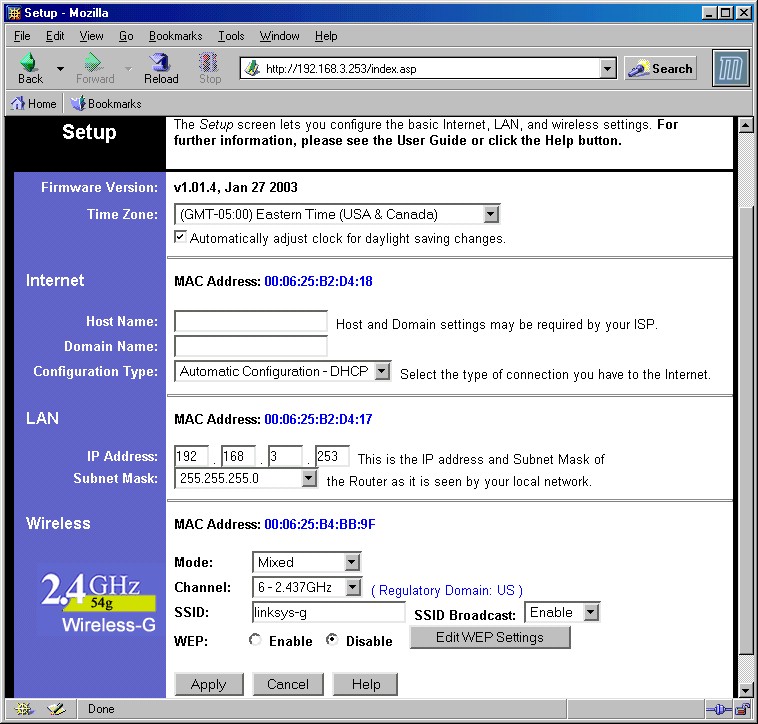
Figure 3: Setup screen
The interface follows Linksys’ recent trend toward putting most of the stuff that you need to futz with for a basic setup on one screen, in this case the Internet (WAN), router LAN address (in case you need to get the router in tune with an existing LAN addressing scheme), and basic Wireless settings.
Also in keeping with trying to prevent user information overload, the Internet Configuration Type selector automatically refreshes the browser screen to present settings appropriate to the choices of Automatic Configuration – DHCP, Static IP, PPPoE, and PPTP Internet connection types. The one curious choice was not having the MAC address cloning feature needed for many broadband ISPs on this main Setup page. Instead, you’ll need to click over to the System tab if cloning is what you need to do.
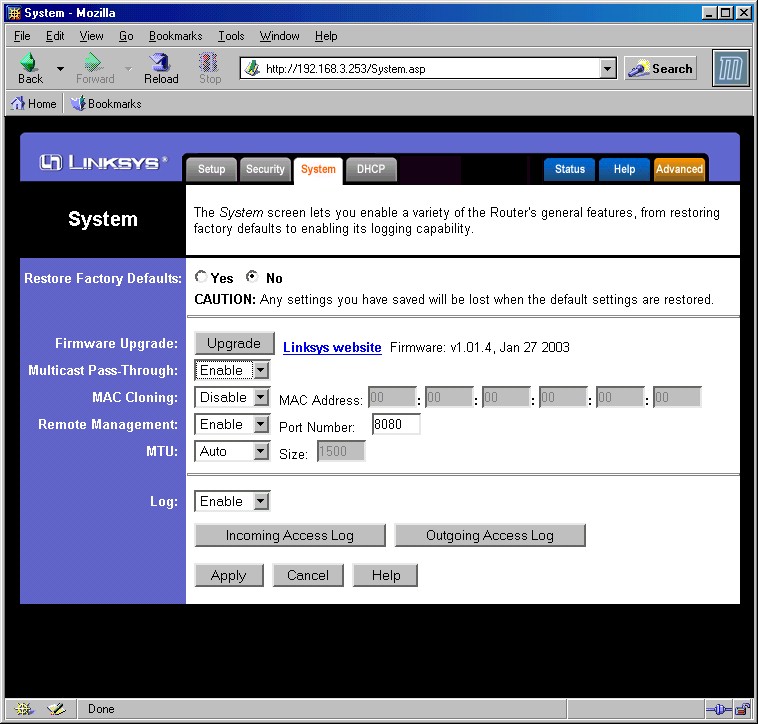
Figure 4: System screen
The Wireless settings here are just the basics, except for the (E)SSID Broadcast Enable/Disable, which prevents your WRT54G from showing up automatically in wireless client applications (such as WinXP’s “Available Wireless Networks”) that show in-range AP’s.
I was glad to see that Linksys included Disable as one of the Wireless Modes, since the ability to shut off the radio is a definite plus for security purposes. I’ll describe what the Mixed and G-Only modes do in the Wireless performance section later.
The interface is generally quick, with quick mini-reboots needed to get the changes you make on each page to take. Multiple admin logins are allowed, with no warning given when two or more admins log on. Once you’re logged in, there’s no idle timeout, and you just need to remember to quit your browser when you’re done, because there’s no logout button.
One feature that I liked a lot involved the Remote Management feature. Enabling this for the first time popped up a message that told you that you were going to need to change the router’s default password, then sent you to the Security screen to make the change. This is something that’s very important, since default router passwords are so widely known.
Without it, an unsuspecting (or lazy) user could enable remote management without changing the password and expose their router – and all the LAN machines behind it – to control by anyone on the Internet.
You can also change the port used for remote management, which I’d advise doing since the default port of 8080 is included in just about every port scan that hits your WAN IP address on a (too) frequent basis.
Firewall Features
Linksys doesn’t actually specify whether the router is NAT or SPI based. From the trouble that I had running the QCheck UDP streaming tests, however, I’d say that the product is mostly NAT based, but with some SPI going on.
Although the admin screens for Port Forwarding and Filtering should be familiar to Linksys devotees, the functions that are actually implemented come up a little short vs. other members of Linksys’ router product line. For example, Figure 5 shows the Port Forwarding interface.
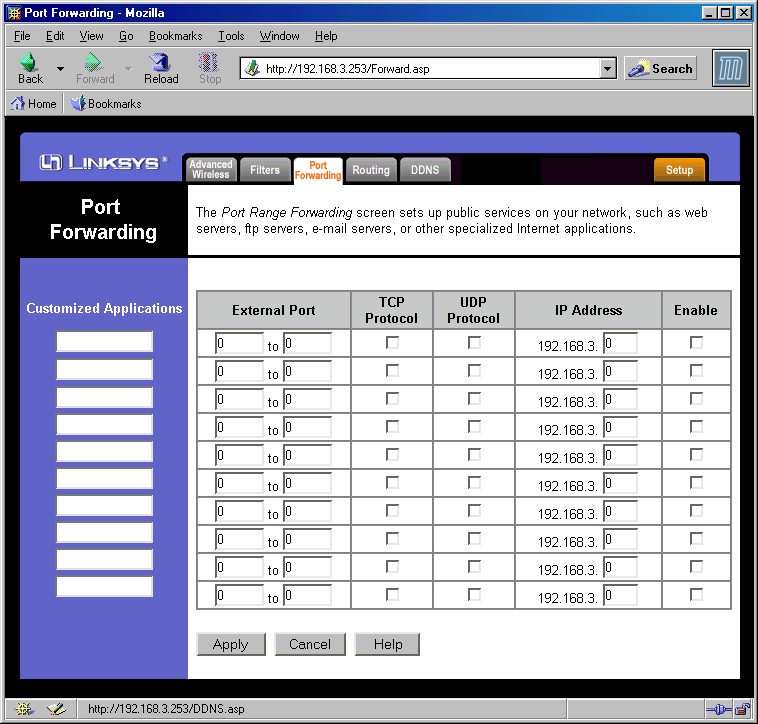
Figure 5: Port Forwarding
If you look closely you’ll note that the Port Triggering button is missing, even though it’s described in the User Guide. When I asked Linksys about this, they said that the feature will be included in a future firmware update, but that they’ll fix the User Guide for now.
I liked that all Port Forwarding entries are both editable and able to be disabled and left programmed, something I wish were standard on all routers. I also checked for and found that loopback is supported for servers on forwarded ports.
The router also supports putting one computer in DMZ via a setting on the Security tab of the interface.
On the negative side, port forwardings are not schedulable by day and time, and – although I don’t really think it’s a negative – UPnP is not supported.
Turning to the Filtering (Access Control) features shown in Figure 6, I found the interface somewhat confusing.
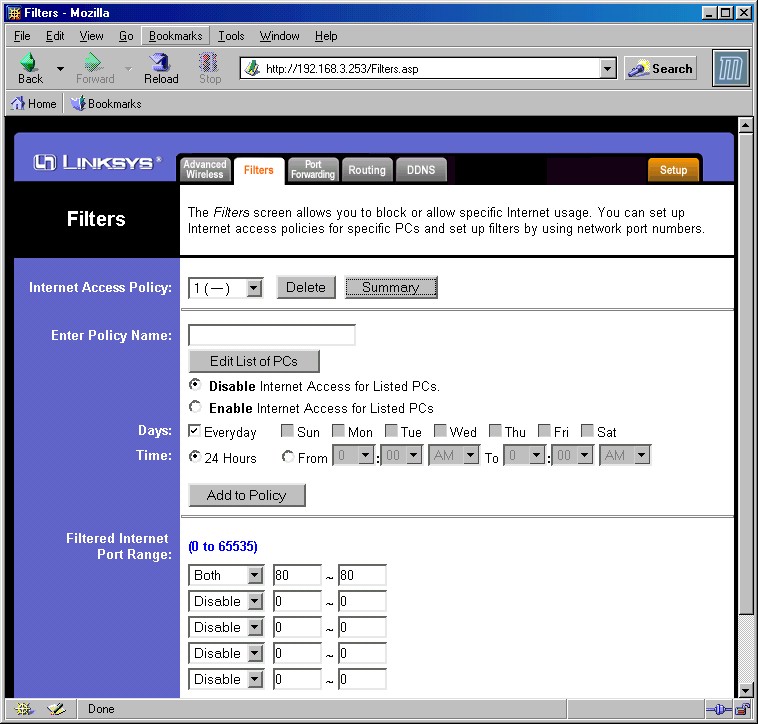
Figure 6: Filters screen
It wasn’t obvious, at least to me, that the Internet Access Policy and Filtered Internet Port Ranges were entirely separate functions. The Access Policy is schedulable by day and time, and up to 10 different policies can be created. Each policy has its own schedule and group(s) of LAN computers that it applies to, but is an all-or-nothing proposition. The Access Policy either grants all or denies all Internet access, and can’t be limited to specific ports.
Specific port filtering is controlled by the Filtered Internet Port Ranges settings, but these settings can’t be scheduled and apply to all LAN machines.
It’s worth noting that Linksys hasn’t yet provided even simple keyword content filters even though many of its competitors have had them for awhile. They do plan to implement the Web Filters features described in the User Manual in a future firmware release, but for now, you’ll have to do without the ability to block Web Proxies, ActiveX, Java, and Cookies.
VPN
VPN capabilities are limited to pass through mode for PPTP and IPsec clients. Port forwarding to one PPTP and IPsec server is also supported, provided you enter the proper ports.
Logging and Other Features
The WRT54G’s logging features are the usual Inbound and Outbound traffic logs that you’ve come to expect with Linksys routers. But once again, there’s work left to do since the usual SNMP Trap logging mechanism that’s used to send detailed logs to a LAN server isn’t implemented yet. You won’t be able to save logs to a file either, but you can clear them.
Other features worth mentioning are the ability to disable the Internet Sharing function and use the WRT54G as a non-NAT router. When in this mode, you also get to control the interfaces (but not the direction) that Dynamic Routing RIP-1 and 2 messages are allowed on. You can also define up to 20 Static Routes in either Gateway or Router modes.
Version 1.01.4 firmware added a built-in client for TZO’s Dynamic DNS service, in addition to the usual dyndns.org offering that you find on most routers that implement dynamic DNS. I may be biased, since TZO both hosts SmallNetBuilder and provides our DNS, but if you’re going to use dynamic DNS, you really should use a reliable service, which is one of TZO’s strengths.
That about wraps up the features. Let’s move on to Performance.
Routing Performance
Testing Notes:
• All tests were run with LAN endpoint in DMZ
As you can see from the numbers, you’ll find it hard to complain about the WRT54G’s routing speed, which was evenly matched in both WAN-LAN and LAN-WAN directions. If 20Mbps isn’t good enough for you, then I’m not sure you should be using a consumer-class router!
Note that the lack of UDP test results in the LAN to WAN direction isn’t Linksys’ fault, but a problem that Qcheck has with some newer routers. I’d expect actual performance to mirror that of the WAN to LAN UDP stream test results.
Routing Performance Test Results
| Test Description | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
|---|---|---|---|---|
| Throughput (kbps) | Lost data (%) | |||
| WAN – LAN | 19.7 | 1 (avg) 1 (max) |
498 | 0 |
| LAN – WAN | 21.7 | 1 (avg) 21 (max) |
||
| Firmware Version | 1.01.14 Jan 27 2003 | |||
See details of how we test
Wireless Features
As I mentioned earlier, the router’s wireless features are separated into Basic (on the Setup tab) and Advanced, shown in Figure 7 below

Figure 7: Advanced wireless
You’ve seen most of these settings before, and if you can’t figure out what some of them do from reading the online help or User Guide, then just leave them alone.
The MAC Address Filter feature lets you enter 40 MAC addresses of clients that will be denied or allowed access to your Wireless LAN. This is actually a wireless association control, so if you have the Prevent mode set and a wireless client’s MAC address entered, not only will they be denied Internet access, but more importantly access to all your wired and wireless LAN clients.
This feature uses three different windows to view and set MAC addresses and I found it somewhat confusing to navigate. The good news is that it has a feature that shows you a list currently connected wireless clients, that you can just select and have copied to the MAC address list window. The bad news is that the list of filtered MAC addresses can be neither saved or loaded to/from a file.
WEP setting from the Setup tab is straightforward. You can enter 64 or 128 bit keys either in Hexadecimal or via an alphanumeric passphrase. The passphrase method generates four different keys, which unfortunately can’t be saved to a file, which would make client entry a little easier.
The main missing pieces are the ability to monitor wireless clients and information about wireless data flow or signal strength. The only way you have of knowing whether wireless clients are connected is to enable the MAC Filter list, click the Edit MAC Filter List button, then click the Wireless Client MAC List button on the window that opens. Not very handy at all.
The other thing to note is that the Wireless Bridging capabilities found in the WAP54G Access Point are not included in the router. So if wireless repeating or bridging are on you list of must-haves, you’ll need to look at Buffalo Tech’s WBRG54 router instead, which performs both functions.
Update 2/1/2004 Wireless bridging support for WAP54G added in Version 2.02.2 firmware.
Wireless Performance
NOTES:
• “Signal Quality” readings were not available
• Testing was done with a Linksys WPC54G Cardbus client card in a WinXP Home Dell Inspiron 4100 laptop
I used the WRT54G extensively in the examples in my 802.11g NeedToKnow, and will just repeat some of that information here for your convenience. Although as I was writing this review, new firmware was released for the WAP54G that incorporated changes mandated by version 6.1 of the 802.11g draft standard, Linksys had not yet released a similar version for the WRT54G. So the results you see here reflect the performance provided by 1.01.4 router firmware and original WPC54G client drivers.
I also won’t be spending any time discussing the ins and outs of draft-802.11g throughput testing. Again, if you want the background, read the NeedToKnow. I’ll only say that to get an accurate picture of what draft-802.11g products will deliver in the throughput department, you need to test under three scenarios:
-
Without any 802.11b clients active
-
With an 802.11b client associated to the same draft-802.11g access point or router, but idle
- With an 802.11b client active, i.e. transmitting data simultaneously with 802.11g data
Scenario 1 – No 11b active
Figure 8 shows the first scenario and with WEP disabled and with the router set to Mixed wireless mode.

Figure 8: Four Condition Throughput test
The “warmup” effect that I found in my WAP54G testing appeared to be solved by the newer firmware and the 21Mbps average throughput under Condition 1 is the best of the draft-11g products that I’ve tested so far. I didn’t try to find the limit of the range of my test pair, since I was seeing signs of being close to the range limit similar to those that I see when testing 802.11b product. It’s worth noting, though, that my worst-case Condition 4 throughput of about 4.8Mbps is about equal to the best throughput that typical 802.11b equipment provides.
Also in Linksys’ favor is that enabling WEP doesn’t appreciably affect throughput, as shown in Figure 9.
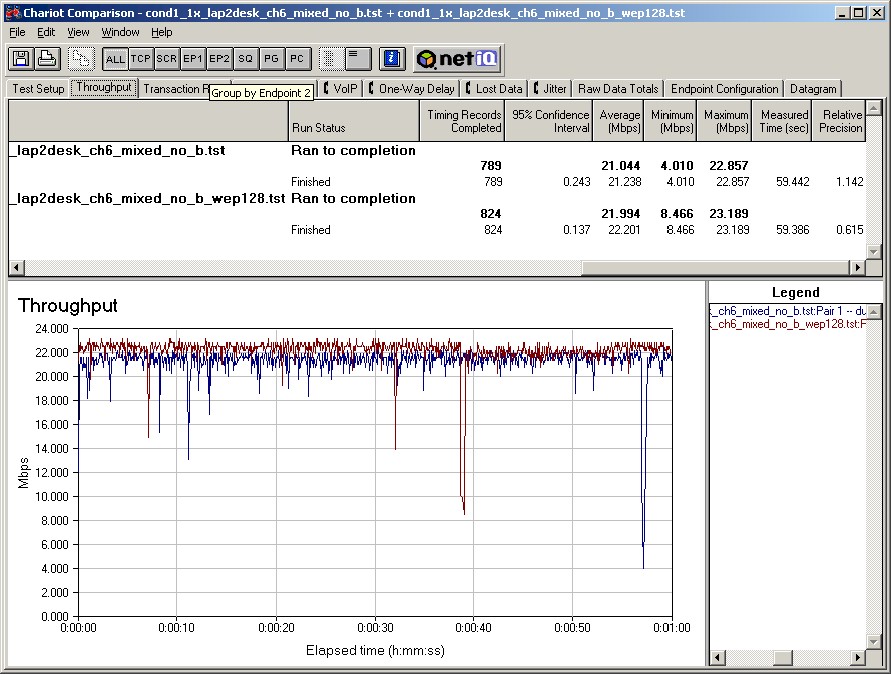
Figure 9: Test Condition 1 – No WEP vs. 128 bit WEP
The summary for Scenario 1 then, is that the WRT54G does pretty well with no 11b competition around and with a Linksys client card.
Scenario 2 – 11b associated, but idle
As I’ve discovered while testing both Broadcom and Intersil-based draft-802.11g products, the trend is definitely toward implementing automatic and what I call “adaptive” 802.11b protection. This method of protection yields higher throughput in what appears to be a protection “standby” or “sniffing” mode, when there are no 802.11b stations in range. Throughput drops noticeably, though, once an 11b client is detected and associates with the AP. Figure 10 provides two examples of this behavior.
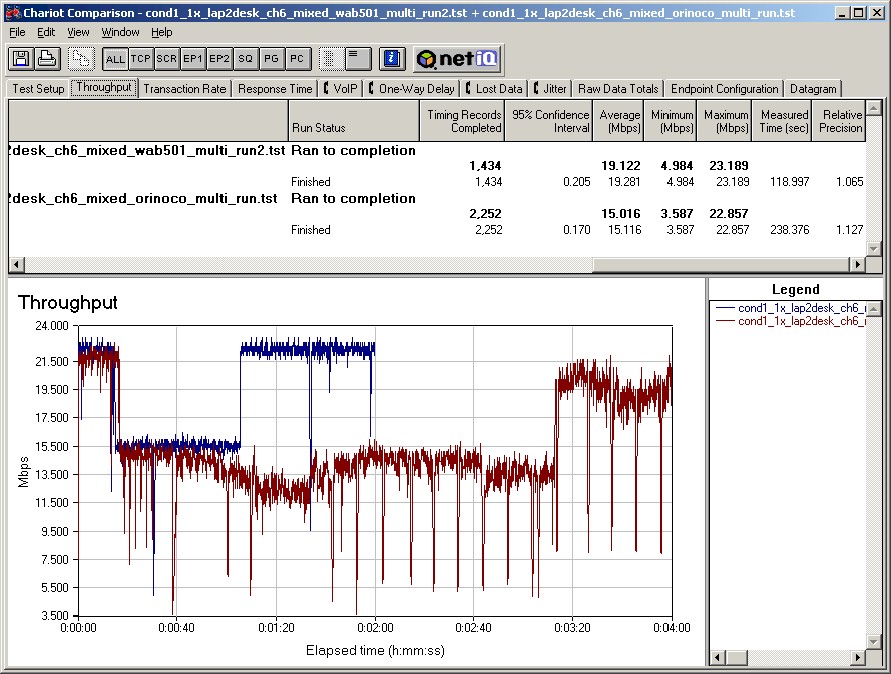
Figure 10: WAB501 vs. ORiNOCO Temporary Association
The screen shot shows the effect from the temporary association of two different 802.11b clients on a throughput test running between the WRT54G and a WPC54G client. During each Chariot run, I plugged an 802.11b client into a second laptop sitting close by at about the 20 second point in the test run. I then shut down and removed the 11b card at about the 50 second mark.
The bluish plot shows the throughput effect from the temporary association of a NETGEAR WAB501 Dual-Band CardBus card (Atheros 5100X-based), and the reddish plot the effect from an ORiNOCO Gold client. Although both cause a throughput drop at about the same time, the effect from the WAB501’s association goes away seconds after I shut down and remove the card. But throughput doesn’t recover from the ORiNOCO’s association until about a minute after I remove the card.
The main points here are:
-
The throughput of your draft-11g WLAN will drop when even one 802.11b client comes into range and associates with your access point or wireless router
-
The lowered throughput can remain in effect for minutes after 11b clients leave your WLAN.
I expect that manufacturers will be tuning their algorithms to minimize both effects, but you should expect lower throughput when 802.11b clients are present in your draft-802.11g WLAN, at least until manufacturers stop tweaking their protection algorithms.
Wireless Performance – more
Scenario 3 – 11b associated and simultaneously active
Once 11b clients connect to your AP, sooner or later they’re going to start using it! Figure 11 shows one example of what you might expect.
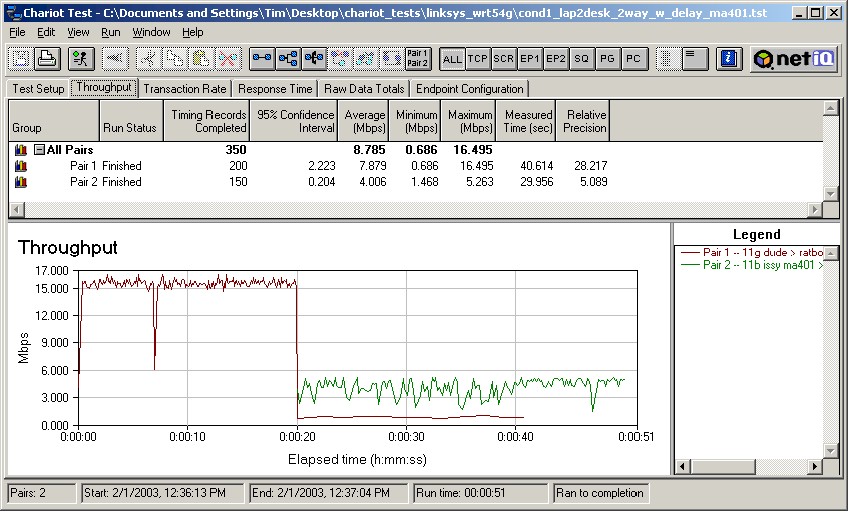
Figure 11: Linksys WPC54G & NETGEAR MA401 Stations
The screen shot shows a test done with Linksys WPC54G and NETGEAR MA401 clients. The Linksys draft-11g card starts first, and is joined by the NETGEAR 802.11b card at the 20-second mark. Both cards run until the Linksys card completes its programmed number of transfers and stops, letting the NETGEAR card finish by itself.
Testing Notes:
• Two separate Ethernet client machines were used to avoid overloading any single CPU,
• All clients were on the LAN side of the router, so the routing portion of the product is not involved in the test.
The plots clearly show that the Linksys draft-11g client’s throughput really takes it on the chin, dropping well below the NETGEAR 11b client’s. The effect, however, is once again client dependent, as shown in Figure 12.
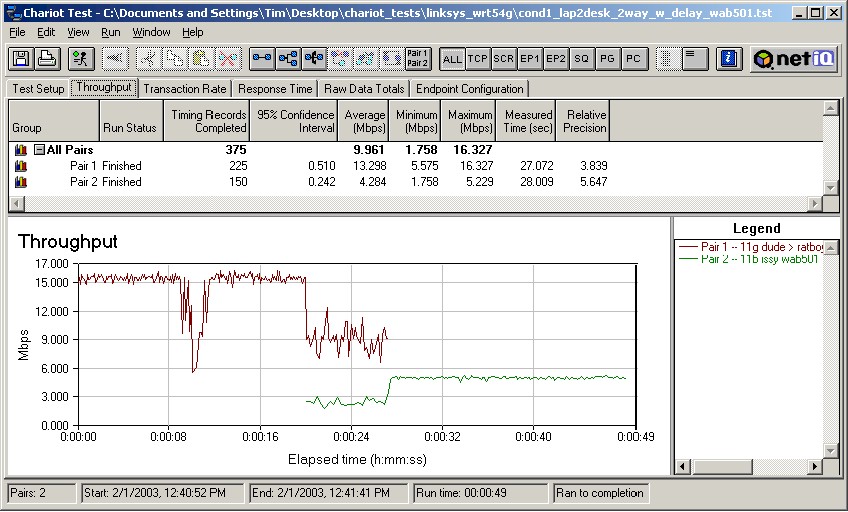
Figure 12: Two pair test – NETGEAR WAB501
This second screen shot shows the same test, but this time with the second card being a NETGEAR WAB501 Dual-Band client forced to 802.11b mode. This test shows behavior more like what you should expect in all cases, once Linksys gets its firmware released that has draft 6.1 improvements, which mandate that 11g clients get more air time than 11b clients in mixed WLANs.![]()
802.11g Wireless Performance Test Results
| Test Conditions – WEP encryption: DISABLED – Tx Rate: Automatic – Power Save: disabled – Test Partner: Linksys WPC54G Wireless-G Notebook Adapter |
Firmware/Driver Versions AP f/w: 1.01.4 Jan 27 2003 Wireless client driver: 3.10.27.0 (WinXP) Wireless client f/w: No Info |
||||
|---|---|---|---|---|---|
| Test Description | Signal Quality (%) | Transfer Rate (Mbps) | Response Time (msec) | UDP stream | |
| Throughput (kbps) | Lost data (%) | ||||
| Client to AP – Condition 1 | 0 | 21.2 [No WEP] 22.2 [w/ WEP] |
1 (avg) 2 (max) |
493 | 1 |
| Client to AP – Condition 2 | 0 | 20.5 | 1 (avg) 2 (max) |
499 | 0 |
| Client to AP – Condition 3 | 0 | 11.6 | 60 (avg) 890 (max) |
499 | 0 |
| Client to AP – Condition 4 | 0 | 4.8 | 8 (avg) 30 (max) |
382 | 0 |
See details of how we test
Wrap Up
Although the WRT54G is street priced about the same as its WAP54G access point sibling, the choice may not be as easy as it seems. Even though the router can always be used as an access point, it does not include the wireless bridging capabilities found in the WAP54G. If you need both routing and bridging in a draft-11g router, you should look at Buffalo Tech’s WBRG54, which throws in wireless repeating, too.
Like all draft-802.11g products, the WRT54G is a work in progress on its wireless side, and will remain so until the 802.11g spec is released this coming June. On the positive side is that Linksys appears to be leading the pack in wireless throughput with a top speed of about 21Mbps. Linksys’ weakness however, is its handling of mixed WLANs which in some cases can slow draft-11g clients to a crawl.
NOTE: A quick look at the latest 1.06 firmware for the WAP54G, which is supposed to incorporate draft-11g version 6.1 mechanisms, showed me that Linksys still has work to do to handle mixed WLANs smoothly. The new code made the WAP54G behave similar to, but not better than the WRT54G with its 1.01.4 firmware.
In addition to these wireless issues, the routing side also needs work to bring it up to par with the rest of its Linksys siblings because of the newer Broadcom-based routing platform. These “to-do’s” don’t seem to be holding the WRT54G back though, at least according to Linksys, which expects to ship more than 500,000 Wireless-G products by the end of this month (March 2003).
Call me conservative, but I still think there’s an advantage in holding off for another month or so. Not only will you get to skip one or two firmware update cycles, but you’ll also get more products to choose from, including the tri-mode dual-band (a/b/g) products that have been announced by NETGEAR and should start appearing in on-line stores shortly. Although these products will start out at a price premium to single band b/g products, once the enterprise folks start buying tri-mode dual-band clients, their volume could drive tri-mode prices down to where they’re the logical choice.
