Introduction

For many people, wireless and security don’t belong in the same sentence. Unprotected wireless networks are around every corner, inviting curious wardrivers, or worse. There is a perception that good security is too difficult to achieve, so why even bother to do anything? Sure, there are networking-savvy users who can easily set up WPA with AES encryption, but what about the “average Joe”?
Some consumer networking product makers are finally listening to “Joe” and are slowly introducing “push button” wireless security configuration. No longer do you have to wade through confusing menus and arcane instructions – just push a button and magically your Wi-Fi card and router or access point will negotiate a secured connection.
We recently compared Buffalo Technology’s AirStation OneTouch Secure System (AOSS) with Linksys’ SecureEasySetup (SES). Both technologies promise quick and easy setup of secured wireless networks and have similar user interfaces.
While we found that both did provide the secured networks they promise, we also found that each has its quirks and potholes that can provide a less than “one touch” experience.
The Technologies compared
Buffalo developed AOSS in-house and was first to market, shipping its WBR2-G54 in March 2004. Linksys, on the other hand, adopted SES from Broadcom, which supplies the wireless chipsets for many of Linksys’ – and Buffalo’s – WLAN products. Broadcom announced the first version of SES – called SecureEZSetup – at the beginning of May 2004 and demonstrated it at the Networld+Interop show later that month. The first version of SES required a “wizard” application to be run that prompted the user with two questions to be answered to begin its process. The current SecureEasySetup has eliminated the wizard and has adopted AOSS’ router / AP client pushbutton method to start the process.
Buffalo provides details of how AOSS performs its magic via this white paper (PDF), and while neither Broadcom nor Linksys has published an SES white paper or technical details, Linksys did provide us with enough details on SES’s workings to make a comparison.
AOSS uses a secret 64 bit WEP key to establish the initial authentication of client and AP, but then switches to an RC4-encrypted tunnel that uses a dynamically generated key for all subsequent communications between the two. SES starts out with a WPA-PSK / TKIP connection then switches to a Diffie-Hellman secured connection.
The two methods also differ in their supported security levels. AOSS supports security levels from the weakest 64 bit WEP to the strongest available WPA2-PSK, while SES supports only devices capable of WPA-PSK / TKIP security. This difference is indicative of the two companies’ approach to the market.
Linksys’ SES Product Manager said that WPA2 is not supported because “WPA2-AES is not as widely adopted right now as WPA-TKIP”. But he also said that “as WPA2-AES becomes more widely adopted, we may update SES to support WPA2-AES”. And as far as the other end of the security spectrum, the PM said SES will NOT support WEP connections, citing that a “network is only as strong as its weakest link”.
Although it can be argued that AOSS’ support of WEP leads to weaker security, Buffalo thinks it is taking a more pragmatic approach. Even though WEP is a flawed security method, WEP protection is better than no protection at all. Buffalo’s approach also accomodates cost-driven consumer product manufacturers, who think WEP is sufficient for devices such as gaming consoles, Wi-Fi phones and similar products.
AOSS also exceeds SES’s capability at the other end of the security scale. It currently supports WPA-PSK with the optional AES encryption that Broadcom has supported in its drivers since it first rolled out WPA support. While WPA-PSK with AES isn’t actually WPA2-PSK, it provides the same level of encryption and stronger protection than WPA-PSK with its mandatory TKIP. Buffalo also said that WPA2 support is currently in development and that there would be an AOSS WPA2 upgrade available, but did not provide a timeframe.
Technologies compared – more
The user interfaces of AOSS and SES may be similar, but Buffalo and Broadcom also differ in their view of the target markets for these technologies. Buffalo has taken a more inclusive approach and pushed to make AOSS upgrades available across its wireless product line, initially even for older products that didn’t have AOSS pushbuttons. AOSS is even supported on its latest AirStation MIMO router and companion CardBus card, which is based on Airgo‘s TrueMIMO chipset.
Linksys, on the other hand, is taking a slower approach to its SES rollout. The WRT54G (v3.1) router and WPC54G (ver. 3) client card Linksys shipped for testing came in what appeared to be official retail packaging. But Linksys’ SES product manager said the product is at “release candidate” status as this is written and still not formally announced.
When asked whether SES would be available across the Linksys product line, the reply was that it would eventually be available on Broadcom-based routers and APs and all Linksys client adapters. But that “all” doesn’t include older versions of its widely-available WPC54G Cardbus card, since SES will work only with the new “ver. 3” card. This isn’t seen as a problem, however, since Linksys said that new users, i.e. without existing Linksys wireless products, are the targeted customers for SES.
The last point of comparison is installed base. There are currently more AOSS products in the field than SES, since AOSS has been shipping for over a year and is supported across all of Buffalo’s current wireless products. AOSS is also supported on a few Japan-only consumer products such as Sharp’s CE-MR01 Network Media Player, Seiko Epson’s PA-W11G Wireless Print Server, SANYO’s Hovica Home View Camera, and most notably in two games for Sony’s Play Station Portable.
SES so far has Linksys and HP printers in its corner, so it has the potential for zooming past AOSS pretty quickly – once both companies start shipping. HP joined the Broadcom / Linksys joint announcement at this year’s CES, but has not yet started shipments of SES-enabled printers.
Buffalo AOSS
We used Buffalo’s WZR-RS-G54 Wireless Gateway and WLI-CB-G54S PC Card for the AOSS tryout. The process for using AOSS is very simple. You first install the WZR-RS-G54 and client card and make sure they connect and work with no encryption.
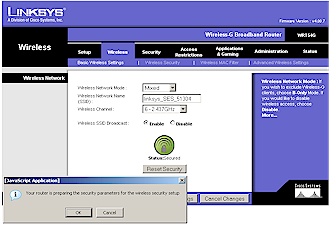
You then start the AOSS process by pushing the AOSS button on the side of the Gateway (Figure 1) and holding it until the AOSS light on the front of the Gateway starts blinking in a recognizable double-blink, pause cadence. This is your cue to click the AOSS button buried on the Buffalo Client Manager’s Profiles screen to begin the AOSS negotiation between card and router.
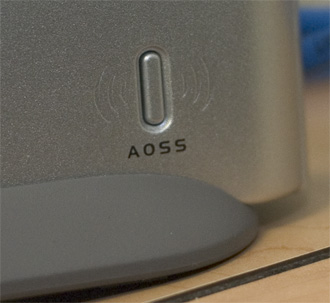
Figure 1: AOSS button on the Buffalo WZR-RS-G54
You don’t need to hurry to click the button, since you have a two-minute window before the router terminates the AOSS search mode. The Gateway temporarily changes its SSID to ESSID-AOSS (which we observed in NetStumbler) and the card associates and authenticates using 64-bit WEP using a preset “secret” key.
An RC4-encrypted tunnel is then established and combinations of four keys (AES, TKIP, 128-bit WEP and 64-bit WEP) and four random SSID’s are created by the Gateway and passed back to the client via the RC4 tunnel. The negotiation process stages are displayed in the AOSS screen (Figure 2), so the user can track progress.
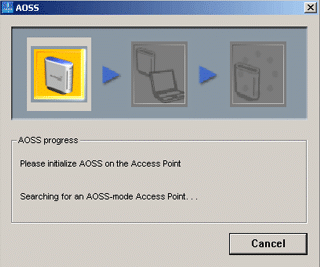
Figure 2: AOSS in progress
After the client and AP find a mutually-supported security level, they both reboot with their security set to use the proper set of SSID, encryption level and key. Once the reboots are done, the client associates, authenticates using the agreed upon key and security method, and obtains a DHCP lease. When everything is complete, the AOSS completion screen (Figure 3) is displayed.

Figure 3: AOSS process complete
The whole process took about 105 seconds the couple of times we tried it, but about 30 seconds of that looked like it was due to DHCP leasing.
As we noted earlier, AOSS supports encryption levels from 64 bit WEP up to WPA2-PSK (with AES) and automatically uses the strongest encryption level supported by all wireless clients. The level negotiated in our testing was WPA-AES, which while not officially WPA2-PSK, is essentially as secure.
Linksys SecureEasySetup
Linksys’ SecureEasySetup looks essentially the same as Buffalo’s AOSS, in terms of user interface. Once again, there’s a button on the wireless router – in this case the WRT54G v3. Given that there is a SecureEasySetup logo also on the front panel (Figure 4), you would think that it would be the button. But instead, somewhere in the Cisco Borg it was decided that you push the lighted Cisco Systems logo button right next to it.

Figure 4: Push the Cisco logo to start SecureEasySetup
The logo is lit with a reddish hue (the User Guide says this is orange) when the router powers up in its factory default unsecured state. The instructions in the WRT54G’s User Guide just say to press the SES button. But there is an approximately 8 second pause between the button push and three seconds of no light, followed by the rapid white flashing backlight that indicates the router is in SES search mode. We found these delays confusing and ended up pressing the button repeatedly the flashing light started. Fortunately, this didn’t seem to mess anything up.
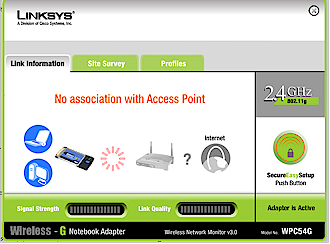
Figure 5: The SES client button is easier to find
Linksys makes the SES button on its client manager software easier to find (Figure 5), displaying it prominently no matter whether you’ve selected the Link Information, Site Survey or Profiles tabs. After clicking on it, and the Next link on the next screen, a “Searching the wireless network” progress bar pops up, which soon subtly changes to “Connecting the wireless network” if all goes well (Figure 6).
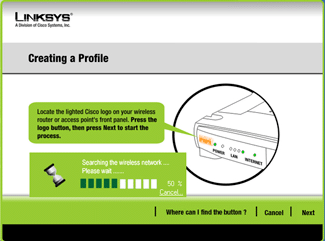
Figure 6: SES in progress
(click image to enlarge)
A successful SES negotiation is indicated by the Congratulation (sic) screen (Figure 7), which conveniently displays the SSID and WPA-PSK key used. Given that SES employs essentially the same methodology as AOSS, we were surprised to see the SES completion message in about 45 seconds, just about a minute less than AOSS took!
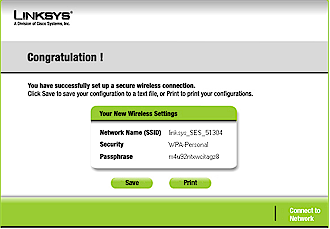
Figure 7: SES complete
By the way, both the Buffalo and Linksys routers display the generated SSID, encryption settings and keys in cleartext in their admin interfaces. You’ll need these to connect non AOSS / SES clients into a wireless LAN secured by either technology.
Bumps and Potholes
Both AOSS and SES are great when they work. But both suffer from assorted bugs and problems. For example, we found that the client manager and driver that came with the Buffalo products (which had been shipped to us for our previous review in December 2004) didn’t produce a successful AOSS negotiation. But after downloading the latest drivers and Client Manager from Buffalo’s support site, we did get a working connection.
We also think the AOSS user interface both in the Client Manager and router shouldn’t be as difficult to find. The AOSS start button should at least be visible on the first Client Manager screen you see, if not on every “tab” as the Linksys manager does. And having a separate AOSS page buried under the router’s Management section, and not linked from the normal Wireless security settings pages is just not good design – especially since normal wireless security settings are “grayed out” when AOSS is engaged.
But SES suffers from its small problems too, such as the error shown in Figure 8 that popped up every time we clicked the Reset Security button, and which never let us actually reset security!
Figure 8: SES Reset Security error
We also discovered that on some occasions when the SES process finished, our client was forced to 11Mbps and other times we’d get error message pop-ups thrown from Microsoft Visual C++. We were also frustrated to find that the Profile Edit function in the Client manager always threw us into a Creating a Profile screen instead.
But the biggest problem for both AOSS and SES is that they don’t play well if you attempt to use them in computers that already have Broadcom-based adapters installed. In the case of Buffalo’s AOSS client adpater, we tested the latest drivers on three laptops, and discovered that they will wreak havoc with pre-exisiting Broadcom drivers. On one laptop, the Buffalo driver disabled the built-in Ethernet (!) driver and Broadcom WLAN adapter. These problems were resolved by going into Device Manager and re-enabling the disabled drivers.
In SES’s case, the conflict with built-in Broadcom wireless adapters didn’t manifest itself in any obvious way, but we were unable to get it to work in any of three notebooks with built-in Broadcom WLAN adapters, despite numerous attempts and fresh installs of WinXP SP1. But when the WPC54G was installed on a WinXP SP2 notebook without a built-in wireless adapter, SES worked on the second attempt.
Both Buffalo and Linksys acknowledged the problems we experienced, with Linksys saying that existing wireless users were not part of their intended customer base. Although we have to agree that few people would be installing AOSS or SES client adapters in notebooks that already had built-in WLAN adapters, we feel that both companies should warn of these problems in their printed startup guides and possibly flag users to potential problems during driver and/or client manager installation. In our case, at least, it would have saved days of frustration!
Linksys also needs to train its support personnel in SES troubleshooting, since the support person we contacted via online chat ended up directing us to the online NETSET assistant instead of troubleshooting SES.
Update June 22, 2005 Linksys said that reason that support personnel were not able to properly support SES is that they are not trained on unreleased products.
Conclusions
Both AOSS and SES can automatically configure a secure wireless connection with the touch of two buttons. User interaction is similar and, while both user interfaces could use some tweaking, simple enough for first-time wireless users to successfully execute.
On a more negative note, both will also behave badly when installed on computers that already contain Broadcom WLAN hardware and don’t flag the user to potential problems in those cases. And neither technology will support the other’s clients (yes, we did try this).
The main difference between the two is in installed base and commitment to the technology. Buffalo has the edge here with (they say) 6.5 million AOSS current users, availability across all its current consumer wireless LAN product line and ongoing recruitement of new companies to AOSS-enable their wireless products.
SES, by contrast, has virtually no installed base, is still not released by either Linksys or HP six months after being announced at this year’s CES, and is MIA on both Linksys and HP’s websites. But given the marketing and distribution muscle of both companies, SES could easily overtake AOSS should both companies decide to get firmly behind the technology.
What’s really needed is for these two separated-at-birth technologies to merge into one, preferably under the umbrella of a Wi-Fi Alliance working group similar to the one that resulted in WPA. This might not get wireless security that the “average Joe” could set up into her hands any sooner (given the glacial rate of rollout of WPA and now WPA2 by WLAN product manufacturers). But it would certainly serve “Joe” much better than the current battle between two technologies that are more alike than different.