
| At a glance | |
|---|---|
| Product | Linksys Wireless-N ADSL2+ Modem Router (X2000) [Website] |
| Summary | Entry-level Broadcom-based single band N router with 10/100 ports and both Ethernet and integrated ADSL2+ modem WAN connection. |
| Pros | • 100 Mbps wire-speed routing • Supports both Ethernet and ADSL2+ WAN connections |
| Cons | • No IPv6 support • Only three LAN ports |
Typical Price: $50 Buy From Amazon
Overview
Many people don’t like multiple networking boxes cluttering up their homes. So for those who take their Internet with a DSL twist, Cisco has come up with the Linksys X2000 Wireless-N ADSL2+ Modem Router.
The X2000 has all the ingredients that plug-and-go networkers desire. It sports a built-in ADSL modem that supports T1.413i2, G.992.1 (G.DMT), G.992.2 (G.Lite), G.992.3 (ADSL2), G.992.5 (ADSL2+) for Annex A, B, M, L, U-R2 for Annex B flavors. But it can also connect to a cable or any other modem type via a 10/100 Ethernet port.
Also inside is an 802.11bgn access point for connecting your wireless thingies via the 2.4 GHz band. There is no USB port for drive or printer sharing, however, and the built-in 10/100 switch has only three ports vs. the normal four.
The X2000’s housing is no-nonsense matte black plastic that harkens back to the smooth stingray styling of the first group of E-series products.
Figure 1 provides the rundown on front and rear panel indicators and ports. Not shown is the bottom of the router, where a reset-to-defaults switch and mounting screw slots reside.
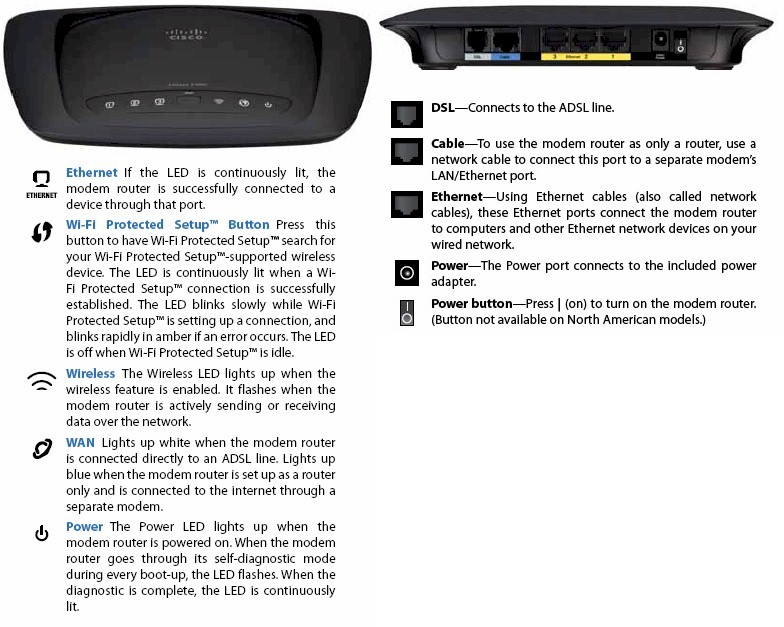
Figure 1: Cisco X2000 ports and indicators
Inside
While the X2000’s non-DSL features are similar to Linksys’ old entry-level E1000 and current E1200, its innards are very different. Figure 2 shows the FCC docs board shot, where you see a Broadcom BCM63281 Single-Chip ADSL2+ Router/Gateway Solution serving as command central with CPU and integrated 10/100 switch.

Figure 2: Cisco X2000 board
The 2.4 GHz radio comes from a Broadcom BCM43225 2.4 GHz 802.11n 2×2 SoC, which I’m encountering for the first time, tucked under the RF can at photo lower left. 64 MB of RAM and 8 MB of flash make up the rest of the key components.
Table 1 compares the X2000, E1200 and E1000’s key components.
| X2000 | E1200 | E1000 | |
|---|---|---|---|
| CPU | Broadcom BCM63281 | Broadcom BCM5357 | Broadcom BCM4716 |
| Switch | In BCM63281 | In BCM5357 | Broadcom BCM5325 |
| RAM | 64 MB | 32 MB | 32 MB |
| Flash | 8 MB | 4 MB | 4 MB |
| 2.4 GHz Radio | Broadcom BCM43225 | In BCM5357 | In BCM4716 |
Table 1: X2000, E1200 and E1000 component comparison
Figure 3 shows a wider view so that you can see the placement of the two hard-wired bent-metal internal antennas.

Figure 3: Cisco X2000 inside view
Sharp-eyed buyers may note the "V2" designation on the router’s serial number label. The FCC docs do show another version that uses the same components with a very similar layout, but different part number board. As far as I know, the V2 is the first model to ship.
Features
The X2000 supports the standard Linksys router feature set:
- DHCP, Static, PPPoE, PPTP, L2TP, Telstra Cable WAN types
- DHCP server with MAC address reservation
- Built-in Dynamic DNS clients for TZO and DynDNS
- Static and dynamic routing
- SPI firewall disable, multicast, WAN ping and IDENT filtering and Proxy, Java, ActiveX and Cooking blocking
- IPsec, PPTP and L2TP VPN passthrough (enabled by default)
- Single port forwarding and Port Range forwarding and triggered ports
- HTTPS admin access, remote management (HTTP / HTTPS) enable with IP range restriction and port setting
- Incoming, outgoing, Security and DHCP onscreen log access with support for Linksys Logviewer recording
- Access Restrictions with 10 deny or allow-based policies, each with its own list of clients and day/time schedule
- Uplink (LAN to WAN) only QoS with High, Medium, Normal or Low Priority that can be applied to specific applications (divided into Application, Online Game and Voice Device groups), physical switch ports or specific MAC addresses.
- WMM (Wireless MultiMedia) (enabled by default)
- Wireless Guest Access – Internet-only access with its own SSID, but no security except a common password for all guests and the ability to limit the number of guests from 1 to 10.
Of course the X2000 also can connect via DSL. That mode offers the selection of RFC 2684 Bridged, RFC2684 Routed, IPoA, RFC 2516 PPPoE and RFC2364 PPPoA connections. There’s a shot of the manual page in the Gallery that provides a bit more info on each of these modes. There is also a Bridged Mode Only mode if you will be using a separate router and don’t want to deal with double NAT from two routers.
I tried out the X2000 with my CenturyLink DSL service. In my neck of the woods, Century Link doesn’t require any visible sort of authentication (username, password). So I just connected it to my phone line and let it do its thing.
After a short time, the Internet light lit, indicating that I was connected. But when I checked the Basic Setup page I found no IP address had been pulled. I went back to my old DSL modem and noted that it had VPI and VCI settings of 8 and 35, while the X2000’s remained at 0.
So I changed the Autodetect radio button from Disable to Enable, hit the Reboot button at the bottom of the Basic Setup page, but still no joy. But after unintentionally power-cycling the X2000, I logged back in to futz with the settings some more and found it all connected up.
I can’t really judge the X2000’s modem performance, both because I have only 5 Mbps down / 0.8 Mbps up service and also because my speeds have been continuously ramping up and down for the past few days. After I get that sorted out, I plan to put the X2000 into service for awhile as my main router, to how it behaves over the long term.
You can download the User Guide to review all the X2000’s features. Pay no attention to the X3000 that you’ll find in the User Guide if you live in the U.S., however. Cisco says that X3000, which has four Gigabit LAN ports and USB 2.0 port for drive sharing will be offered in Europe only.
I loaded up the latest firmware (v2.0.00 build 027) before testing and found that it doesn’t include any IPv6 controls. Another feature that the X2000 shares with E-series routers is won’t let you access the Internet unless you run the Cisco Connect software or check a box in a captive portal that says you understand that the router isn’t secure.
I’ve included a few more admin screens in the gallery below.
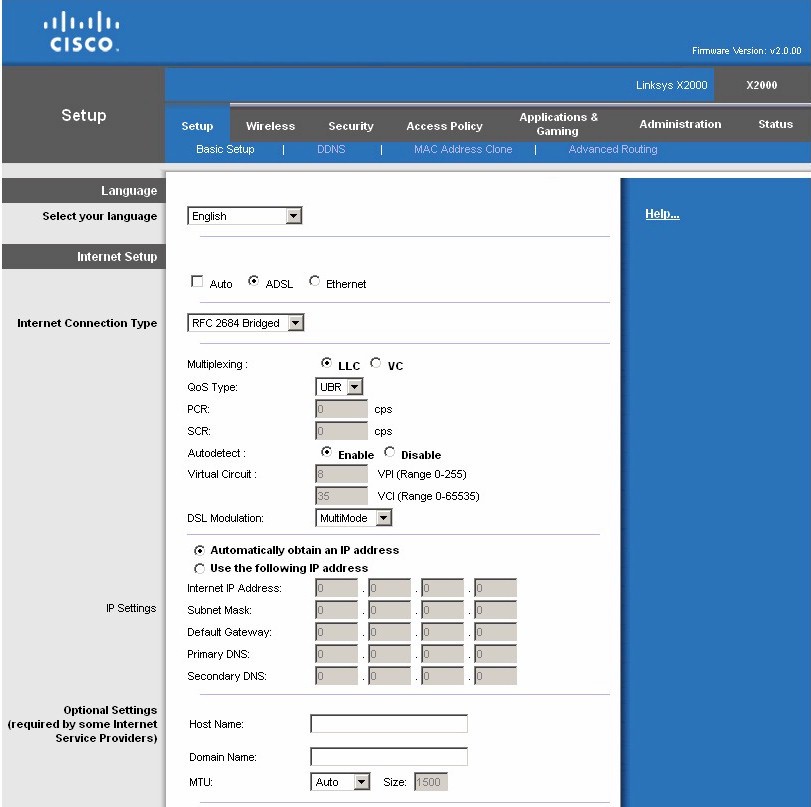
The WAN and LAN settings are on this screen. The top half shown has the default Auto mode set that will sense an Ethernet or DSL connection and try to set itself up automatically.

The bottom half of the Basic Settings screen holds the LAN settings that include the DHCP server.
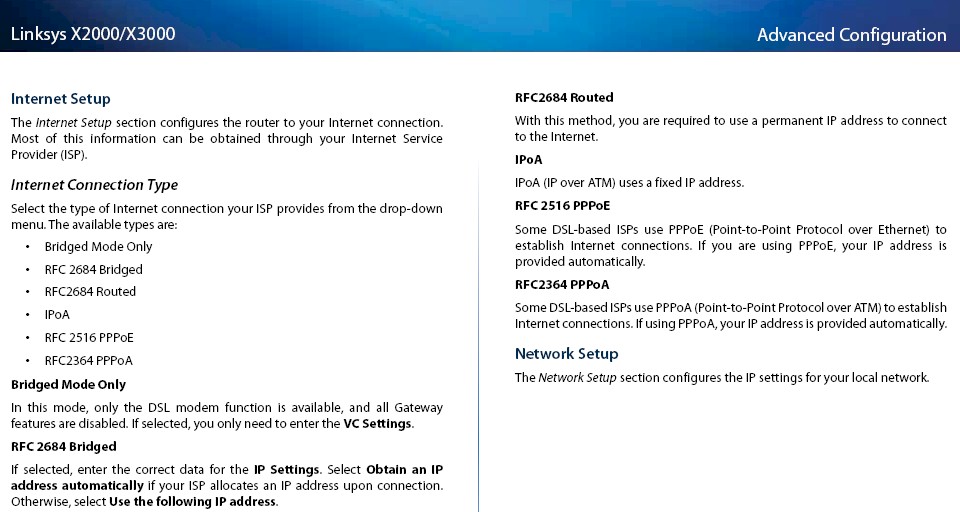
Explanation of the DSL modes
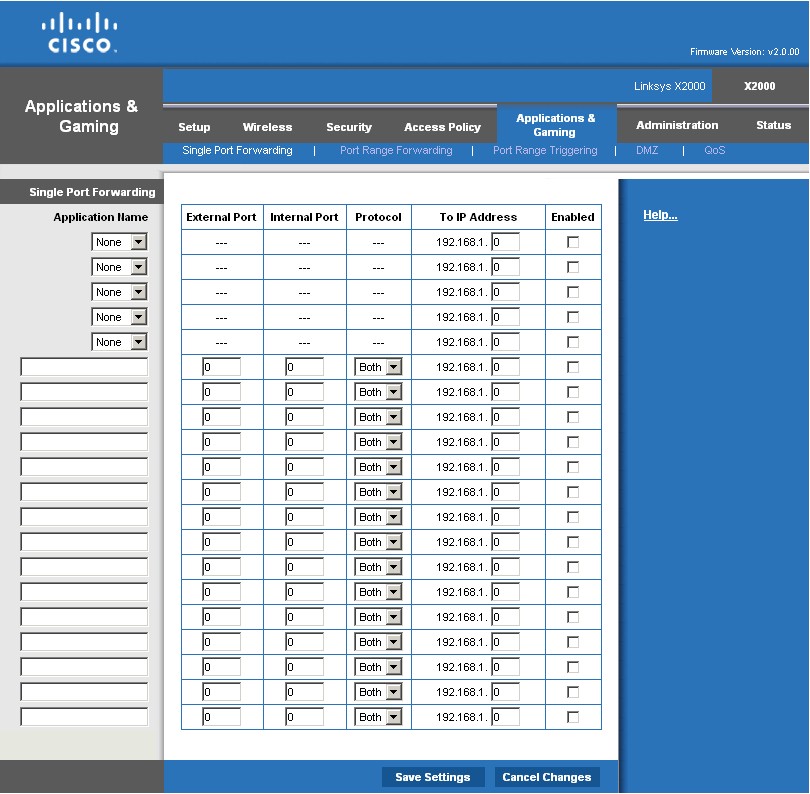
Note that you can specify both external and internal ports.
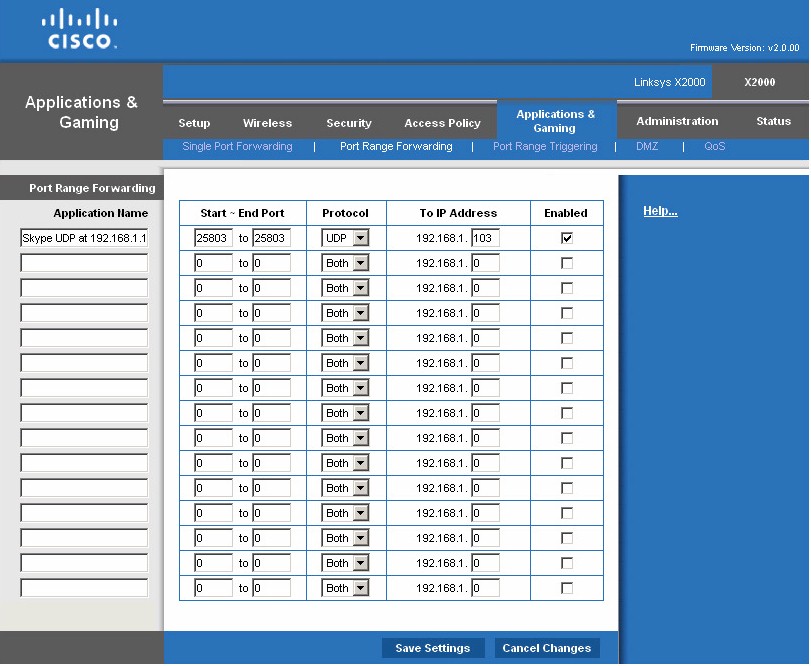
Looks like the default-enabled UPnP automatically opened ports for Skype.
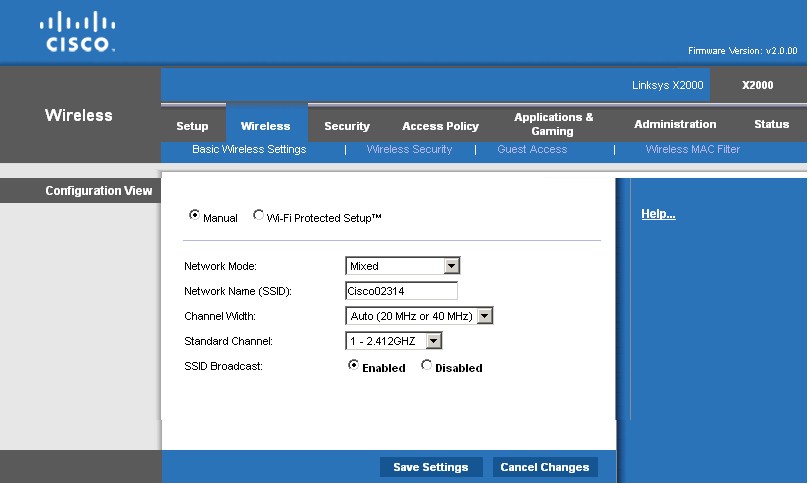
Basic wireless settings. The X2000 improperly defaults to Auto 20/40 MHz mode instead of 20 MHz only.
Routing Performance
Routing throughput running the latest v2.0.00 build 027 firmware and our router test process measured 93 Mbps WAN to LAN, 93 Mbps LAN to WAN and 154 Mbps total with up and down tests running simultaneously. The IxChariot composite plot in Figure 4 shows up and download speeds pretty evenly matched in the simultaneous routing test.
The maximum simultaneous connections test ran all the way up to our test maximum of 34,925.
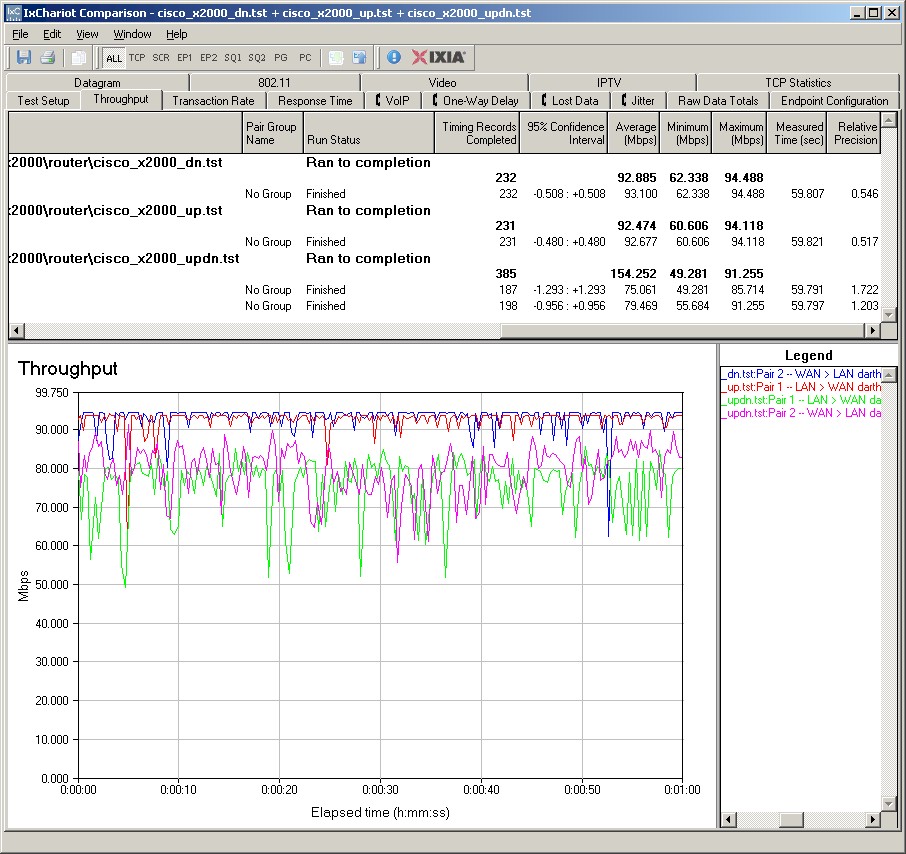
Figure 4: X2000 wired routing performance summary
Wireless Performance
The X2000 is Wi-Fi Certified but did not properly default to 20 MHz bandwidth mode on power-up. I asked Cisco to explain this and will update this when I receive an answer.
I successfully ran a Wi-Fi Protected Setup (WPS) session with my Win 7 client by entering the WPS code found on the X2000’s bottom label. The WPS session completed quickly and resulted in a WPA2/AES secured connection. All tests were run with this secured connection using our latest wireless test process.
I ran a 2.4 Wireless Performance table (Figure 5) for the X2000, E1200 and E1000 so that you can compare the X2000 with other Cisco entry-level single-band routers.
Highest 2.4 GHz throughput for the X2000 of 67 Mbps was measured using our wireless test process in Location C running downlink with the client set to Auto 20/40 mode. Running simultaneous up and downlink tests yielded 82 Mbps in Auto 20/40 mode, but in Location A. So you don’t really gain a whole lot by using the bandwidth-hogging Auto 20/40 mode for single connections.
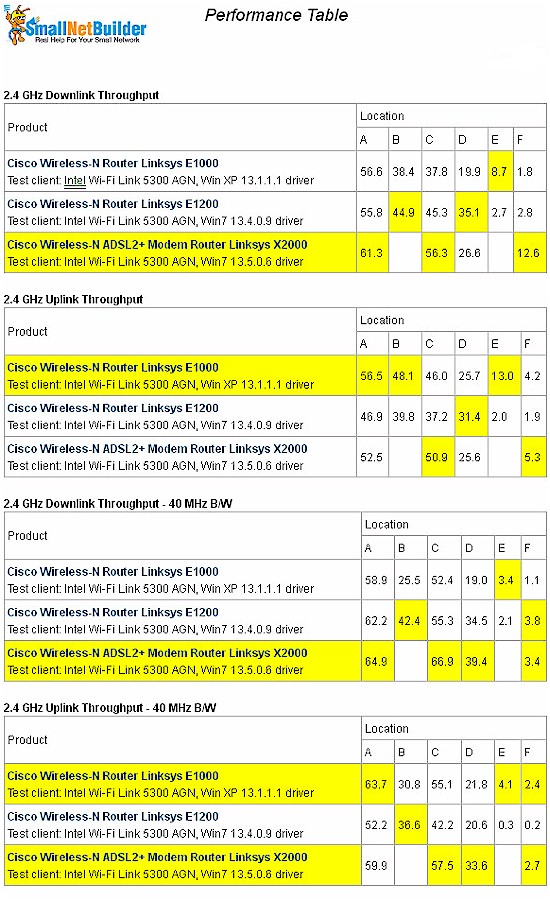
Figure 5: Linksys X2000 Wireless Performance summary – 2.4 GHz
While there are some differences shown in the table, I think you’d be hard-pressed to see any significant difference in wireless performance in the real world.
The IxChariot plot in Figure 6 shows some occasional large thoughput dropouts, which I also saw from time to time in other tests. I also saw link rate shifting and cycling during some of the testing in lower signal level locations.
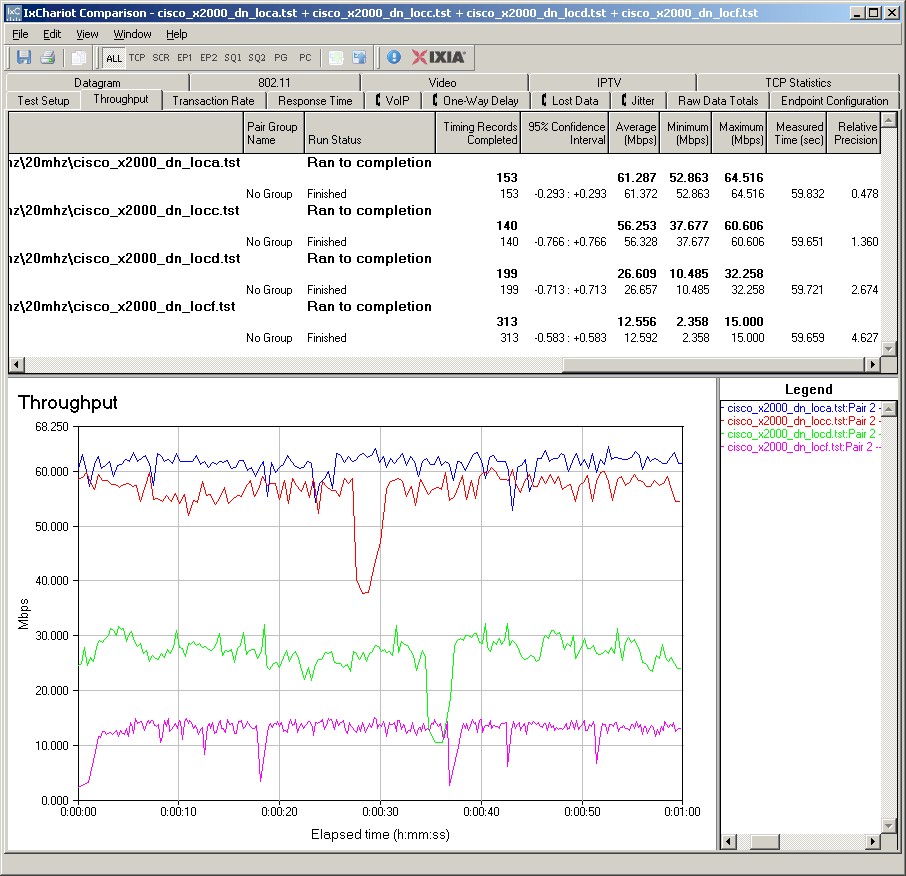
Figure 6: X2000 IxChariot plot – 2.4 GHz, 20 MHz, downlink
Here are links to the other 2.4 GHz plots for your reference:
- 2.4 GHz / 20 MHz uplink
- 2.4 GHz / 20 MHz up and downlink
- 2.4 GHz / 40 MHz downlink
- 2.4 GHz / 40 MHz uplink
- 2.4 GHz / 40 MHz up and downlink
Closing Thoughts
DSL combo routers tend to be created primarily to sell directly to service providers, so it’s interesting that Cisco is taking a direct-to-consumer route with the X2000.
This is the first DSL-inside router I’ve looked at, so had to do some checking to see if its $90 street price is a good deal. A quick check of similar products turned up the D-Link DSL-2640B for $55, but with an 802.11b/g radio, and the Actiontec GT784WN for $77, which has a b/g/n radio, but four 10/100 LAN ports. Neither of these other routers, however, also have an Ethernet WAN port.
Typical consumers, though, are unlikely to need the WAN connection type flexibility that the X2000 provides. And whether they’re willing to pay a premium for it, is even a better question. It would be useful only if you had one flavor of connection and planned to switch to another. And since the X2000 doesn’t auto-failover between WAN connection types, it can’t be used to provide more reliable Internet service for those willing to pay for two Internet links.
You can further explore and compare the X2000’s performance using the Router Chart and Router Finder.
